)
Moving beyond passwords
Passwords have been the go-to method for securing access to online accounts and data from the early days of the Internet. However, as cyberattacks grow increasingly sophisticated, relying solely on passwords may no longer suffice.
Hacker-controlled machines are now too good at cracking them, particularly because many people use weak or reused passwords across multiple accounts, unaware that this practice makes the attackers’ job effortless.
And so, the time has come to move beyond passwords and adopt more modern standards to safeguard digital assets. In other words, it’s time to go passwordless.
What is passwordless authentication?
Passwordless authentication is a cybersecurity method where users can access a service or application without entering a password. How does passwordless authentication work then? It allows users to utilize alternative authentication factors such as fingerprints or face IDs to verify their identity while logging into a service.
The goal of passwordless authentication is to provide a more convenient alternative to traditional passwords that can not only maintain but also enhance the level of protection against cyberattacks.
Types of passwordless authentication
Passwordless authentication can take many forms; however, some are now more popular than others. Let’s now go through a few of the commonly used authentication techniques that do not require passwords.
Biometric authentication
Probably the most popular passwordless authentication method available today, biometrics involves using built-in scanning tools on devices to verify unique biological characteristics such as fingerprints or facial features to confirm a user’s identity. This method has become highly popular because most modern mobile phones support it. Also, fingerprints can’t be as easily stolen as James Bond movies might suggest, which makes biometric authentication a more secure option than passwords.
Authentication apps
This popular password-free authentication technique uses a dedicated app to generate time-limited codes for accessing accounts, ensuring high security. It works well because most people have their mobile phones with them, making it easier to check the app for a code than to remember all their passwords for different online accounts.
Hardware Tokens
Generally speaking, hardware tokens are physical devices that generate authentication codes or utilize cryptographic keys to grant access to systems. They are quite popular due to their reliability in providing a second factor of authentication, which significantly enhances security. Also, hardware tokens do not rely on internet connectivity or software, making them more resilient against many forms of cyber threats.
Magic Links
With this method, users receive a link via email that, when clicked, allows them to log in to their account without entering a password. This approach simplifies the login process while ensuring security, as the link is usually valid for a limited time and can only be used once.
Passkeys
Compared to other types of passwordless authentication described in this section, passkeys are the new kid on the block, though already quite popular. Passkeys typically involve using a pair of cryptographic keys: a private key stored on the user’s device and a corresponding public key on the website’s server. Access is granted when these keys are successfully matched in a process often initiated through biometrics. This approach enhances convenience and significantly boosts security because attackers must acquire both keys to gain unauthorized access. Stealing the private key from the user’s device is extremely difficult.
The benefits of passwordless authentication
As we’ve already covered in this article, the benefits of passwordless authentication are plenty. These advantages become even clearer when compared to what passwords can provide. So, let’s delve into each major benefit in detail, starting with…
1. Enhanced security
The first, and arguably the most important, benefit of passwordless authentication is that it provides much more protection than traditional passwords. This is because it eliminates vulnerabilities commonly associated with password-based systems, such as phishing, brute-force attacks, and password reuse. With passwordless methods like biometrics or passkeys, authentication relies on unique and difficult-to-replicate factors, significantly reducing the risk of unauthorized access. As a result, adopting passwordless authentication strengthens overall security posture and helps keep outsiders at bay.
2. Ease of use
When it comes to user convenience, passwordless authentication delivers a knockout blow to passwords, preventing them from getting back up. Firstly, the passwordless approach is much faster as it allows users to log in to a service or application with one click, whereas with passwords… well, you know the drill. Secondly, with passwordless authentication, users don’t have to remember anything, freeing their minds and preventing the frustration of repeatedly entering incorrect passwords. And thirdly, this ease of use extends to business as well, preventing account lockouts and shopping cart abandonments, and keeping customers happier and more willing to use a given service.
3. Reduced password-related support
Unlike traditional authentication methods that frequently lead to forgotten passwords and subsequent support requests, passwordless authentication effectively eliminates these issues. This significantly reduces the need for password-related support, saving time and resources while enhancing user satisfaction with a seamless login experience.
4. Enhanced regulatory compliance
Embracing passwordless authentication is a strategic way for businesses to boost their compliance with regulations on data privacy. How so? By adopting secure methods like biometrics or passkeys, organizations can meet diverse data protection requirements without compromising user convenience. This proactive approach not only helps mitigate financial and reputational risks associated with non-compliance but also builds trust among customers and stakeholders.
Passwordless authentication use cases
With the support of organizations such as the FIDO Alliance, which helps develop authentication standards to reduce the world’s reliance on passwords, passwordless authentication methods have become highly popular among key players across all industries.
This should come as no surprise, especially considering that, according to a study by Secret Double Octopus and the Ponemon Institute called “State of Workforce Passwordless Authentication,” organizations can save up to $1.9 million by implementing passwordless authentication methods.
This explains why Microsoft has been promoting passwordless authentication through Windows Hello; why Amazon, Apple, and Google have introduced support for passkeys in their services; why Twitter offers password-free login options through third-party authentication apps and security keys; and so on — almost everywhere you look, a password-free login option is available. As a result, passwordless authentication is used today by millions of users worldwide and is gradually pushing passwords out of the picture.
How to enable passwordless authentication on your service
If your website or application requires customers to log in but doesn’t offer passwordless options, consider adding this feature to your to-do list. The answer to whether your company and your customers will benefit from that is undoubtedly yes. The real question is: how can you integrate a password-free login option effectively?
Well, although you can hire a team of IT professionals and ask them to write passwordless logins into your code, this approach requires significant upfront investment and is rather time-consuming.
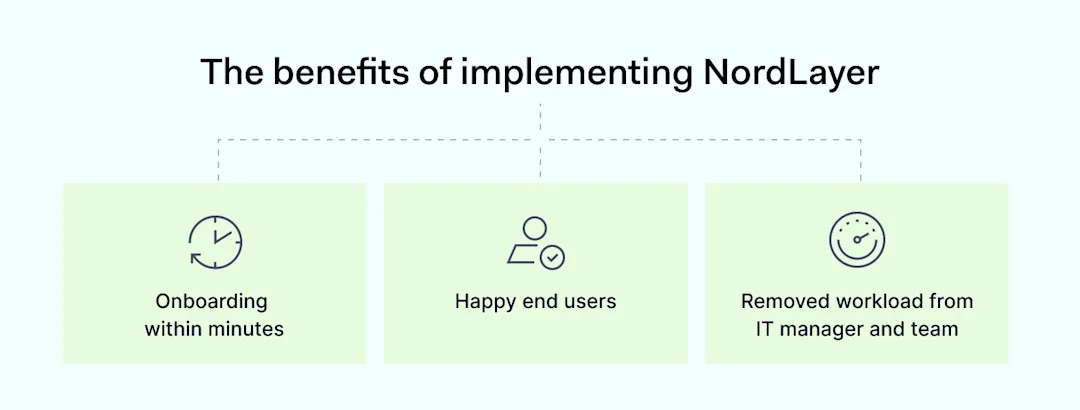
Fortunately, there are alternatives. For example, you can use Authopia by NordPass, a free tool that allows you to easily add a passkeys widget to the login form on your website or service. Here’s how it works: you receive pre-written code that even those with basic IT skills can implement, you activate the widget by registering with Authopia, and voilà — you have a password-free login option up and running!
As already mentioned, Authopia is free to use, which means you can quickly integrate passkey logins into your service and observe improvements in sign-ups and conversions today. So, don’t miss out on this opportunity!
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordPass
NordPass is developed by Nord Security, a company leading the global market of cybersecurity products.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.





)



)
)