In today’s economy, choosing the right cybersecurity security tools can make or break a company’s finances.
Ransomware cost global companies around $1 billion in 2023. Data breaches cost companies $4.45 million on average, while DDoS attack victims lose around $500,000 each.
The thing is, robust firewalls and antivirus coverage can protect companies against most malware attacks. Filtering traffic and efficiently getting rid of malware agents deters attackers and renders them harmless.
Despite this, many companies rely on ineffective and outdated security solutions. Don’t be like them. Act now to avoid becoming part of next year’s cybersecurity statistics.
This blog will explain the functions of firewalls and antivirus software and help you choose the right security tools. We will dive a little deeper, too, exploring how to update your cloud security posture. Let’s start at the network edge with an introduction to firewall technology.
What is a firewall?
Firewall devices protect network security by filtering incoming and outgoing traffic.
Firewalls inspect data and apply rules to determine whether data is legitimate or malicious. If packets pass security rules, data is allowed to enter or leave. If not, data is denied or discarded and cannot compromise security.
Traditional firewalls come in software and hardware forms. Hardware firewalls operate as separate devices between external networks and local devices. On the other hand, firewall software uses agents or modules on network endpoints.
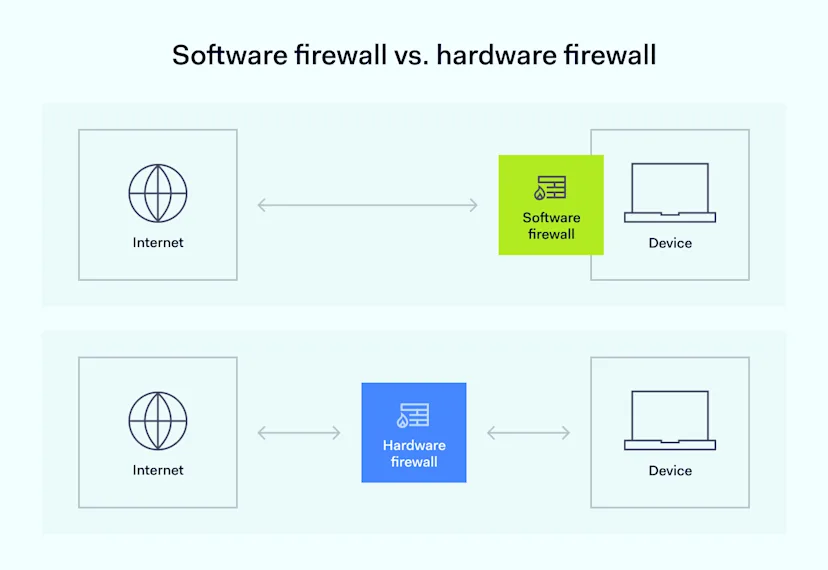
![]()
Hardware firewalls tend to handle large amounts of traffic efficiently, but coverage is limited to nearby devices. Software firewalls move with devices. They suit remote workers but may compromise device performance.
Traditional firewalls employ two main inspection techniques:
Packet filtering—assesses surface packet data, including source and destination IP addresses, protocol types, and ports.
A stateful inspection—evaluates the state of active connections to determine whether they meet network rules.
Next-generation firewall services go beyond traditional features.
NGFWs include deep packet inspection and Intrusion Prevention Systems (IPS). These features enable NGFWs to analyze the contents of data packets, something not possible in traditional packet filtering.
These extra features guard against complex threats like DDoS attacks, extending firewall capabilities from simple filtering to active threat prevention.
Recently, Cloud firewall services have also emerged. These firewalls reside in the cloud and operate on a firewall-as-a-service (FWaaS) model.
Cloud firewalls protect cloud deployments and scale as companies add new cloud applications or data capacity. They also ensure consistent access control and data filtering across hybrid and multi-cloud environments.
What are antivirus tools?
Companies install antivirus software on network endpoints, where it analyzes traffic to identify and block cyber threats. When it identifies malware or other suspicious agents, antivirus software quarantines and neutralizes threats, keeping network assets safe.
Antivirus solutions typically use signature analysis to detect known threats.
Researchers identify new worms, viruses, or malware. They extract a unique identifier from each agent based on file attributes, byte sequences, or malware behavior. They then send information about this signature to antivirus tools.
Antivirus software compares traffic signatures to threat databases. Software blocks signatures that match. Security tools may quarantine or delete malware, depending on local security settings and the severity of the threat.
Some antivirus software also uses heuristic methods to identify threats.
Heuristic systems track file or user behavior and flag suspicious activity that does not match known profiles. More advanced antivirus software uses machine learning to understand network environments, tailoring detection to specific contexts.
As with firewalls, antivirus software has also entered the cloud. Cloud-native antivirus tools scan virtual machines and cloud-hosted data. They integrate with popular cloud platforms and scale with deployments – complementing on-premises security tools.
Key differences between firewall and antivirus software
When comparing firewalls vs antivirus software, the main difference is simple: firewalls filter traffic at the network edge. Antivirus software identifies and neutralizes threats on network endpoints.
![]()
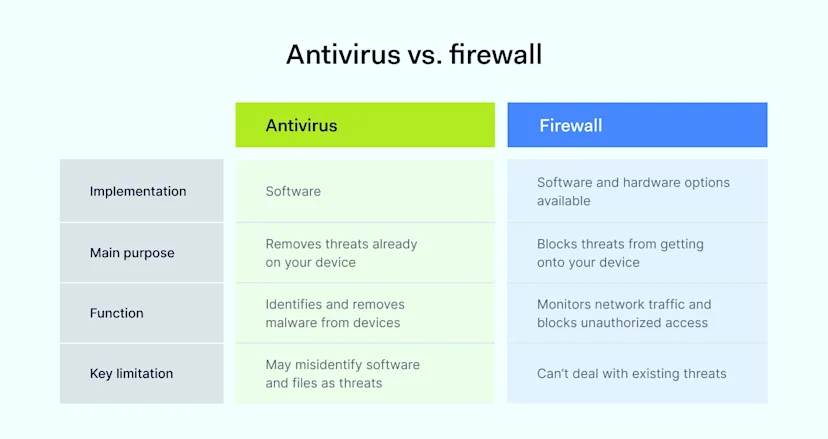
However, the two security technologies have many other differences. Understanding where they differ is important when building functional security systems. Below is a handy summary.
Functionality
Firewalls: Scan traffic entering and leaving networks to block harmful traffic.
Antivirus: Scan files on network endpoints. They protect against internal threats, including malware or worms.
Scope
Firewalls: Operate at the network level via packet filtering and protocol analysis. Can extend Saas or IaaS deployments via cloud firewalls.
Antivirus: Works at the application or system level. It scans files and communications between devices.
Threat detection
Firewalls: Rules define what traffic is permitted. Uses packet filtering and stateful inspection to block external threats and malicious traffic.
Antivirus: Analyzes files on devices to find malicious programs. Identifies threats via malware signatures and heuristic analysis.
Implementation
Firewalls: Implemented at the network edge to filter incoming and outgoing traffic.
Antivirus: Installed on computer systems and other endpoints connected to the network.
Performance impact
Firewalls: Minimal impact on system performance. Minor effects on network latency.
Antivirus: Real-time and scheduled system scans can impact device performance.
Cost
Firewalls: Tend to be cost-effective, especially basic firewalls included with operating systems. Costs rise for high-maintenance enterprise-level implementations.
Antivirus: Subscription costs rise with protection requirements. Add-ons like VPNs and identity theft measures raise costs further.
Updates and maintenance
Firewalls: Companies must update rules to reflect security needs. Security teams must monitor traffic, test rules, and ensure compatibility with network applications.
Antivirus: Less burdensome as automated updates deliver virus definitions and patches. Security teams may need to schedule scans and manage quarantined files.
Compatibility with other security tools
Firewalls: Must integrate with the local Intrusion Prevention System and Virtual Private Network tools.
Antivirus: Sometimes, antivirus conflicts with existing endpoint security tools. These conflicts may lead to false positives or consume more system resources.
Effectiveness
Firewalls: Good at blocking cyber threats at the network edge, including cloud deployments. Ineffective at dealing with malware within the network.
Antivirus: Detects, identifies, and neutralizes malicious software. Scans must cover all endpoints to work effectively.
Similarities between firewalls and antivirus tools
Despite the differences listed above, firewalls and antivirus software are closely related. Understanding their similarities helps when choosing the correct security solution. Similarities include:
Fundamental goal. Both tools protect networks against external threats. They filter or block malicious agents, ensuring smooth performance and protecting critical data.
Changing techniques. Antivirus software and firewalls are evolving to meet new challenges. For instance, both come in cloud-native versions to defend virtualized assets.
Network monitoring. Firewalls monitor network traffic to prevent unauthorized entry or exit, and antivirus programs actively monitor internal threats.
Customization. Companies can set firewall rules to suit their operations, and users can customize antivirus coverage with scheduling, alerts, and exclusion lists.
Compliance roles. Firewalls and antivirus software are critical tools to ensure compliance with data security regulations.
Should your business choose a firewall or antivirus?
Until recently, answering this question was simple. Companies needed both, as traditional antivirus tools and firewalls performed complementary network security functions.
However, the choice is not as simple as it once was. Security solutions featuring both firewall and antivirus protection are becoming ever more popular.
In the past, firewalls operated as a barrier between untrusted external networks and local assets. Antivirus software operated locally, scanning for malicious software. Firewalls deal with network-level attacks, while antivirus systems operate at the application or system level.
Firewalls created a first line of defense. Antivirus software allowed layered defense, dealing with malware that crossed the network edge. In that situation, it often made sense for companies to source separate firewall and antivirus protection.
Things have changed. Next-generation firewall systems have narrowed the differences between the two technologies. The familiar firewall vs antivirus comparison is unhelpful when antivirus firewalls offer a single solution.
Cloud coverage is also something to consider. Next-generation cloud firewalls deliver flexible security in cloud environments. Access control is a critical challenge when securing cloud assets, potentially making cloud firewalls more attractive than cloud-hosted antivirus software.
How NordLayer can enhance your network security
Robust cybersecurity is a must for any business. Cyber threats can expose confidential data and take systems offline in seconds, with catastrophic consequences.
Firewalls and antivirus software are two of the most effective cybersecurity tools. Even so, choosing the wrong tools will leave systems exposed. Outdated protection is almost as risky as no protection at all.
NordLayer’s Cloud Firewall (FWaaS) is the perfect solution.
Our cloud-hosted security tools create a watertight barrier around your cloud infrastructure. Our firewall lets you control who accesses assets by defining teams and members. You can also determine how users connect by granting access to various end-points.
NordLayer’s cloud firewall adds control and security that complements our virtual private gateways—bringing hybrid cloud networks under your security framework.
Update your firewall technology today.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.







)
)