
Making Security Operations Simpler
We deliver an easy-to-use Open XDR platform built to meet the needs of lean security teams, providing security functionality anyone can use.
Our Mission:
Deliver world-class
security products for the 99%
Our Open XDR Platform
Ingests security alerts, logs, and telemetry from any product
Uses AI to analyze and correlate collected data to identify cyber threats
Enables your security team to complete effective investigations fast
The Stellar Cyber Open XDR Platform Delivers
Nex Gen SecOps
Unified, simplified, automated security operations platform.

Next Gen SIEM
Fulfill empty promises of legacy SIEMs.

NDR
Simplify attack detection and react quickly.
Bring Your Own EDR
Immediately turn any EDR into an XDR.
With Stellar Cyber You Can…

Protect Your Entire Attack Surface
Identify threats against your on-prem, cloud, and IT/OT environments with our out-of-the-box threat detections.

Increase SecOps Performance
Improve MTTD by >8x and MTTR by >20x. Let your people do what they do best, let AI-driven automation do the rest.

Reduce Costs While Simplifying SecOps
Flexible deployment options coupled with our open approach mean you control your investment strategy, not us.
How Stellar Cyber Works
Stellar Cyber empowers lean security teams to successfully secure their cloud, on-premises, and OT environments from a single platform.
Ingest And Normalize Data
Stellar Cyber can ingest data from any security, IT, system, or productivity product you have deployed.
Centralized Threat Detection
Stellar Cyber automatically finds threats using a mix of detection capabilities.
Sensor-Driven Threat Detection
Stellar Cyber Sensors can be deployed to the far reaches of your environments with embedded threat detection capabilities.
AI-Enabled Investigation
Stellar Cyber eliminates the manual steps typically required to complete an investigation.
Automated Response
Create playbooks that run automatically when a specific threat is detected.
Ingest and Normalize Data
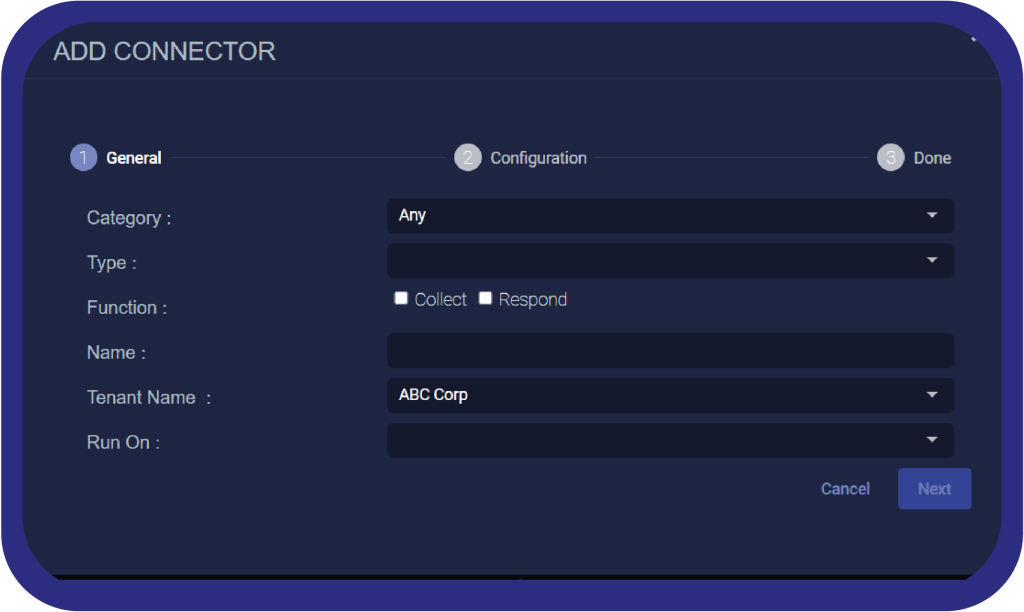
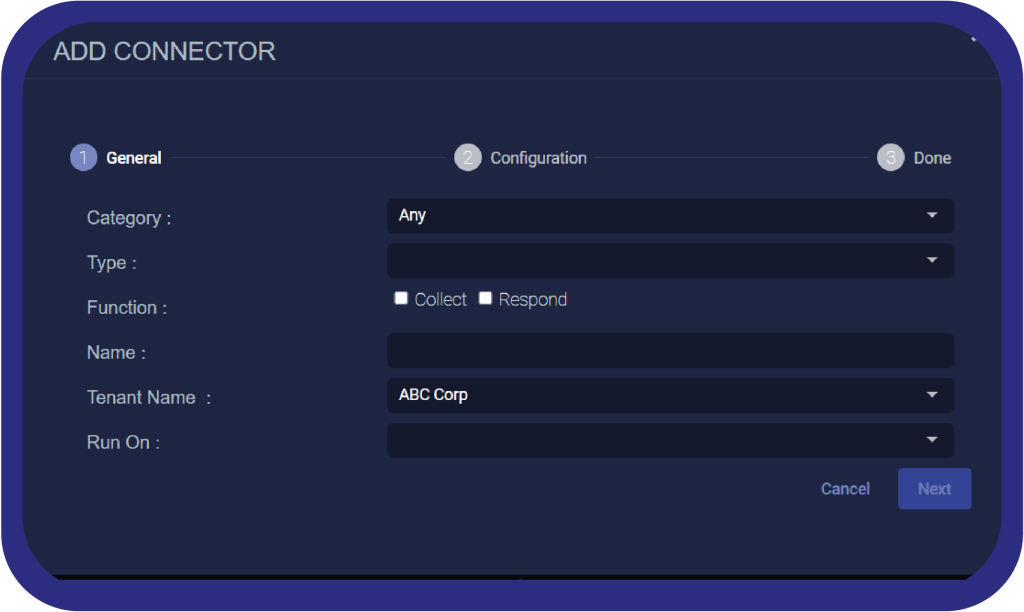
Stellar Cyber ingests data from API based connectors (cloud or on prem), or from streaming log sources via protocols like Syslog. On prem data sources can be captured because of Stellar Cyber’s Sensors which can be deployed physically or virtually to hook into those environments. Data, regardless of its origin, gets normalized into a standard data model. Common fields like source IP, timestamp, or logon type are always standardized when possible to make workflows easy. Third party specific data is kept in a vendor data namespace. Data is also enriched with geolocation and asset context to increase the value of all telemetry.
Centralized Threat Detection
Stellar Cyber uses several methods to root out potential threats:
- Easy-to-find sources of known bad are found through rules in Stellar Cyber, with new and updated rules being shipped continuously to all customers, sourced from our internal detection team as well as open communities like SigmaHQ.
- Unknown and zero-day threats are uncovered using unsupervised machine learning techniques. These models look for anomalous behavior indicative of a threat. These models baseline over several weeks on a per-customer/per-tenant basis.
- Harder-to-find sources of known bad are identified using supervised machine learning detection. Stellar Cyber’s security research team develops models based on publically available or internally generated datasets and continuously monitors model performance across the fleet.
Sensor Driven Threat Detection
Stellar Cyber’s sensors not only collect logs from cloud and on-prem sources, they also create visibility and deploy network based detections to the edge. Sensors package together Deep Packet Inspection (DPI), Intrusion Detection System (IDS), and Malware Sandbox into a single configurable software package.
AI Enabled Investigations
Correlation across detections and other data signals occurs through a Graph ML based AI that aids analysts by automatically assembling related data points. The AI determines connection strength between discrete events that can be sourced from any data source, based on property, temporal, and behavioral similarities. This AI is trained on real world data generated by Stellar Cyber and is continuously improved with its operational exposure.
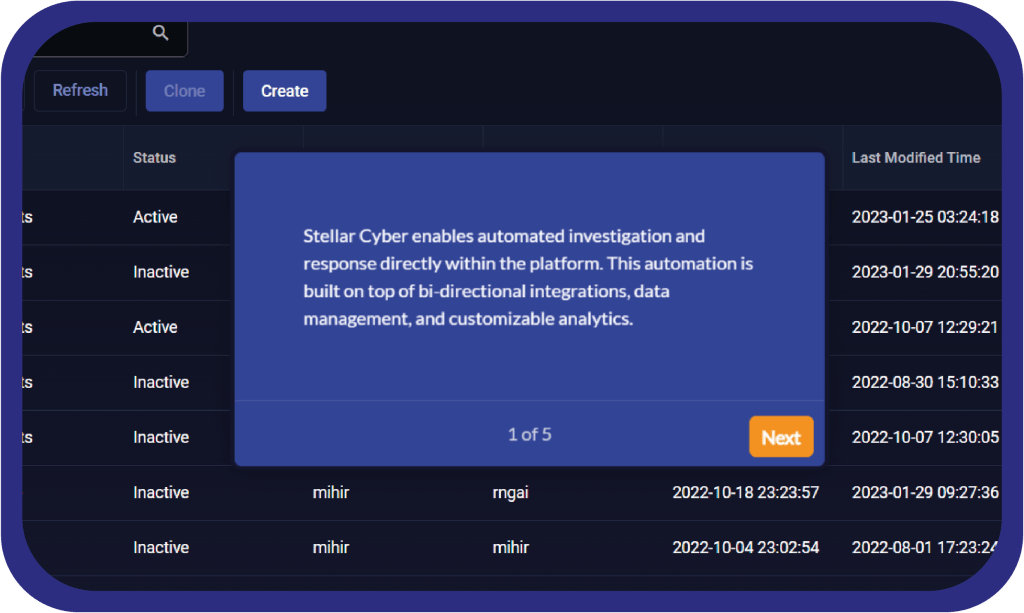
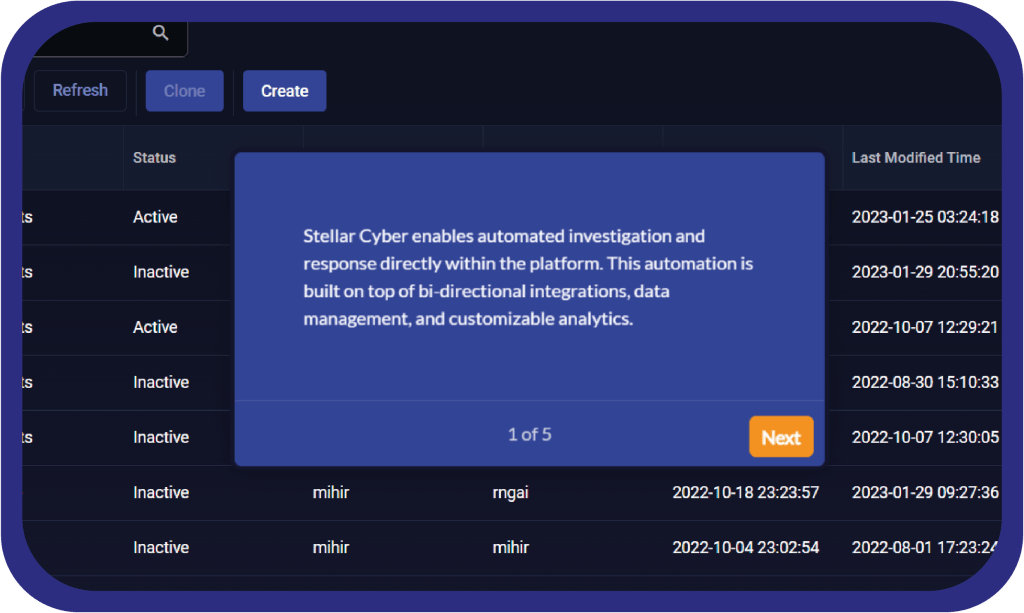
Automated Response
Users have complete customizability over the context, conditions, and output of playbooks. Playbooks can be deployed globally or on a per tenant basis. Use any out-of-the box playbook for a standard response, or create a custom playbook for taking action back into an EDR, calling a web-hook, or simply sending an email.
Explore our Open XDR Platform
Data Onboarding and Management Made Easy
Ensuring you have the data you need to identify threats is the first step in any successful security program. See how we make it easy.

Working with Alerts and Incidents
Investigating alerts manually is no longer feasible. See how Stellar Cyber makes working with alerts and incidents faster than ever before.
Automated Threat Hunting and Response
The threats you do not see are the ones that hurt the most. See How Stellar Cyber automates Threat Hunting and Incident Response.
Next Gen SIEM
Open XDR
關於 Stellar Cyber
主要功能
產品介紹
資源中心
品牌新訊
Making Security Operations Simpler
We deliver an easy-to-use Open XDR platform built to meet the needs of lean security teams, providing security functionality anyone can use.
Our Mission:
Deliver world-class
security products for the 99%
Our Open XDR Platform
Ingests security alerts, logs, and telemetry from any product
Uses AI to analyze and correlate collected data to identify cyber threats
Enables your security team to complete effective investigations fast
The Stellar Cyber Open XDR Platform Delivers
Nex Gen SecOps
Unified, simplified, automated security operations platform.

Next Gen SIEM
Fulfill empty promises of legacy SIEMs.

NDR
Simplify attack detection and react quickly.
Bring Your Own EDR
Immediately turn any EDR into an XDR.
With Stellar Cyber You Can…

Protect Your Entire Attack Surface
Identify threats against your on-prem, cloud, and IT/OT environments with our out-of-the-box threat detections.

Increase SecOps Performance
Improve MTTD by >8x and MTTR by >20x. Let your people do what they do best, let AI-driven automation do the rest.

Reduce Costs While Simplifying SecOps
Flexible deployment options coupled with our open approach mean you control your investment strategy, not us.
How Stellar Cyber Works
Stellar Cyber empowers lean security teams to successfully secure their cloud, on-premises, and OT environments from a single platform.
Ingest And Normalize Data
Stellar Cyber can ingest data from any security, IT, system, or productivity product you have deployed.
Centralized Threat Detection
Stellar Cyber automatically finds threats using a mix of detection capabilities.
Sensor-Driven Threat Detection
Stellar Cyber Sensors can be deployed to the far reaches of your environments with embedded threat detection capabilities.
AI-Enabled Investigation
Stellar Cyber eliminates the manual steps typically required to complete an investigation.
Automated Response
Create playbooks that run automatically when a specific threat is detected.
Ingest and Normalize Data
Stellar Cyber ingests data from API based connectors (cloud or on prem), or from streaming log sources via protocols like Syslog. On prem data sources can be captured because of Stellar Cyber’s Sensors which can be deployed physically or virtually to hook into those environments. Data, regardless of its origin, gets normalized into a standard data model. Common fields like source IP, timestamp, or logon type are always standardized when possible to make workflows easy. Third party specific data is kept in a vendor data namespace. Data is also enriched with geolocation and asset context to increase the value of all telemetry.
Centralized Threat Detection
Stellar Cyber uses several methods to root out potential threats:
- Easy-to-find sources of known bad are found through rules in Stellar Cyber, with new and updated rules being shipped continuously to all customers, sourced from our internal detection team as well as open communities like SigmaHQ.
- Unknown and zero-day threats are uncovered using unsupervised machine learning techniques. These models look for anomalous behavior indicative of a threat. These models baseline over several weeks on a per-customer/per-tenant basis.
- Harder-to-find sources of known bad are identified using supervised machine learning detection. Stellar Cyber’s security research team develops models based on publically available or internally generated datasets and continuously monitors model performance across the fleet.
Sensor Driven Threat Detection
Stellar Cyber’s sensors not only collect logs from cloud and on-prem sources, they also create visibility and deploy network based detections to the edge. Sensors package together Deep Packet Inspection (DPI), Intrusion Detection System (IDS), and Malware Sandbox into a single configurable software package.
AI Enabled Investigations
Correlation across detections and other data signals occurs through a Graph ML based AI that aids analysts by automatically assembling related data points. The AI determines connection strength between discrete events that can be sourced from any data source, based on property, temporal, and behavioral similarities. This AI is trained on real world data generated by Stellar Cyber and is continuously improved with its operational exposure.
Automated Response
Users have complete customizability over the context, conditions, and output of playbooks. Playbooks can be deployed globally or on a per tenant basis. Use any out-of-the box playbook for a standard response, or create a custom playbook for taking action back into an EDR, calling a web-hook, or simply sending an email.
Explore our Open XDR Platform
Data Onboarding and Management Made Easy
Ensuring you have the data you need to identify threats is the first step in any successful security program. See how we make it easy.

Working with Alerts and Incidents
Investigating alerts manually is no longer feasible. See how Stellar Cyber makes working with alerts and incidents faster than ever before.
Automated Threat Hunting and Response
The threats you do not see are the ones that hurt the most. See How Stellar Cyber automates Threat Hunting and Incident Response.
Next Gen SIEM
Open XDR
產品查詢
電話:(852) 2893 8860
電郵:sales@version-2.com.hk
產品查詢
電話:(852) 2893 8860
電郵:sales@version-2.com.hk






