
Recent years took cybersecurity to a new level — digital transformation, migration to the cloud environments, and remote work became the synonyms of technological business evolution. The new approach pushed such tech terms as VPN (Virtual Private Network), S(A)SE (Secure (Access) Service Edge), MFA (Multi-Factor Authentication), and many more that turned into essential modern cybersecurity elements.
Zero Trust is one of those most critical terms that already live rent-free in IT managers’ heads. It’s way past the emerging buzzword stage — now, Zero Trust is a security model that dictates organizational cybersecurity strategies and general security approaches.
But how influential is the Zero Trust model? What’s its role in the near future and its place in a broader picture of cybersecurity? Let’s take a look at what trends to expect in the Zero Trust department.
Password is dead; long live Zero Trust?!

The new cybersecurity era will likely be marked by another iconic moment in the digital age. Rumor has it that we will be done with the passwords in 2023. Hard to say if it’s true, but passwords as single-factor authentication are outdated in the context of the current cybersecurity landscape.
Lost or stolen credentials surge black markets imposing risk to data security. A glance at the high numbers of the latest data breaches of 2022:
Slash Next reports 255 million phishing-related attacks in 6 months — a 61% increase compared to 2021.
According to Verizon, weak or stolen passwords contributed to 81% of hacking-related data breaches. 82% of breaches were triggered by human error (including social engineering attacks).
Nvidia suffered an attack and lost the credentials (email addresses and Windows password hashes) of 71,000 employees.
Keeping in mind that 73% of employees recycle the same personal passwords for work-related accounts – NordLayer’s research about bad cybersecurity habits concluded weak passwords as one of the top vulnerabilities of organization security – the number of leaked personal credentials is a huge red flag for organizations.
Despite education and targeted reminders of password hygiene, more than half (59%) of workers tend to reuse passwords while being familiar with existing risks.
The remaining high data breach statistics only confirm the insufficiency of current actions regarding securing credentials and company data accordingly.
The Zero Trust mindset to ‘trust none; verify all’ is a straightforward change for companies to dismiss careless passwords from their systems and elevate security levels effectively.
A quick recap: ZT, ZTA, and ZTNA
Zero Trust (ZT) is a trust algorithm that ensures resources within specific networks can be accessed only by verified endpoints — devices or users. Yet when discussing cybersecurity, additional concepts of Zero Trust Architecture (ZTA) and Zero Trust Network Access (ZTNA) emerge — what’s the difference?

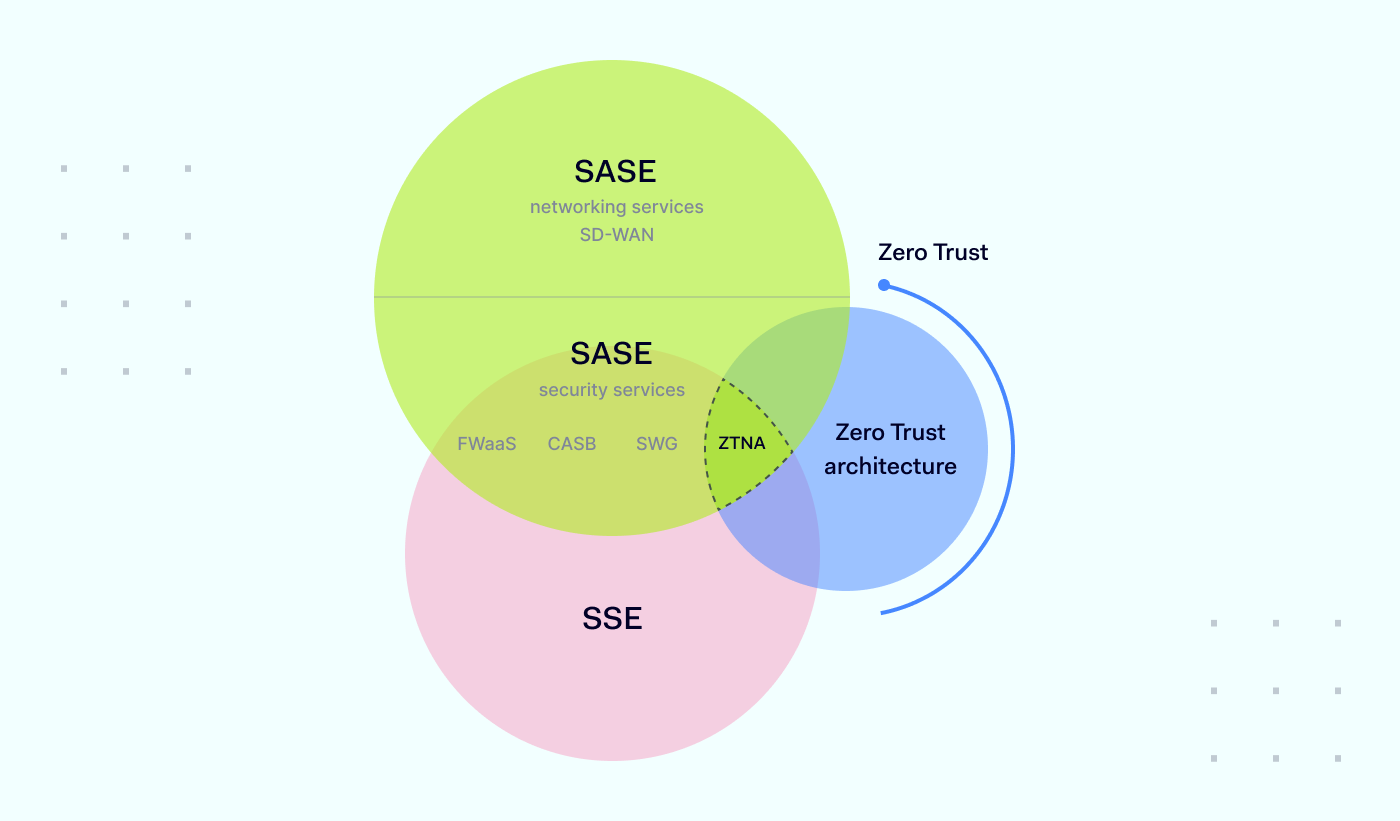
An easy way to differentiate Zero Trust, Zero Trust Architecture, and ZTNA is to define Zero Trust as the driving idea, model, or mindset that puts the theoretical foundation for the application of the method.
The Zero Trust principle turns attention to the main focus points:
Make sure to check and verify every endpoint connection request to the network.
Solely job-mandatory access rights must be granted to perform role objectives.
Plan for the maximum constraint of user movement in the network in case of a breach.
Zero Trust Architecture is a practical application of the Zero Trust approach when building security policies and IT infrastructure as if there was no traditional perimeter. ZTA combines and implements solutions for:
Endpoint verification
Network supervision.
ZTNA is a segment of Zero Trust Architecture that provides a solution to trusted-only application access. ZTNA is integral to the SASE and SSE frameworks for establishing security in remote cloud environments.
What changes does Zero Trust employ: ZTNA’s focus
Instead of discussing Zero Trust at theoretical levels, it’s beneficial to investigate ZTNA to understand what changes it suggests and how companies apply them.
According to Statista, the most common solution organizations used to enable Zero Trust segmentation in 2021 was ZTNA. Identity, Credential, and Access Management followed it.
The popularity of ZTNA comes from its adoption as a more efficient identity- and context-supported solution for controlling increasing attack surfaces in hybrid environments.

As ZK Research indicates, VPN was a go-to solution to manage and protect companies’ IT perimeters. However, VPN performance and security fallbacks brought by backhauling network traffic and open network access make it refer to VPN as a remote work solution only as a temporary one.
Therefore, to secure and connect remote workers while managing distributed endpoint, user, and application networks under the organization’s scope, companies turned to secure network access (SaaS, cloud, and edge) solutions, including ZTNA.
Shrinking the attack surface – limiting the threat actor’s activity in the network by requesting additional authentication or assigned permits to access internal applications – is the key feature of the ZTNA solution.
Prospects of Zero Trust in cybersecurity
Cyberattacks continuously challenge everyone, from consumers to federal agencies, hitting the weakest link — passwords. Attacks are disrupting business operations from intelligence businesses to manufacturers — any company with internet-connected systems and networks is vulnerable.
The Zero Trust approach can mitigate hardly controllable external and internal factors that might lead to a breach. ZTNA enables IT administrators to monitor, manage and interact with connections between endpoints and ultimately conclude whether the connection should be approved or denied.
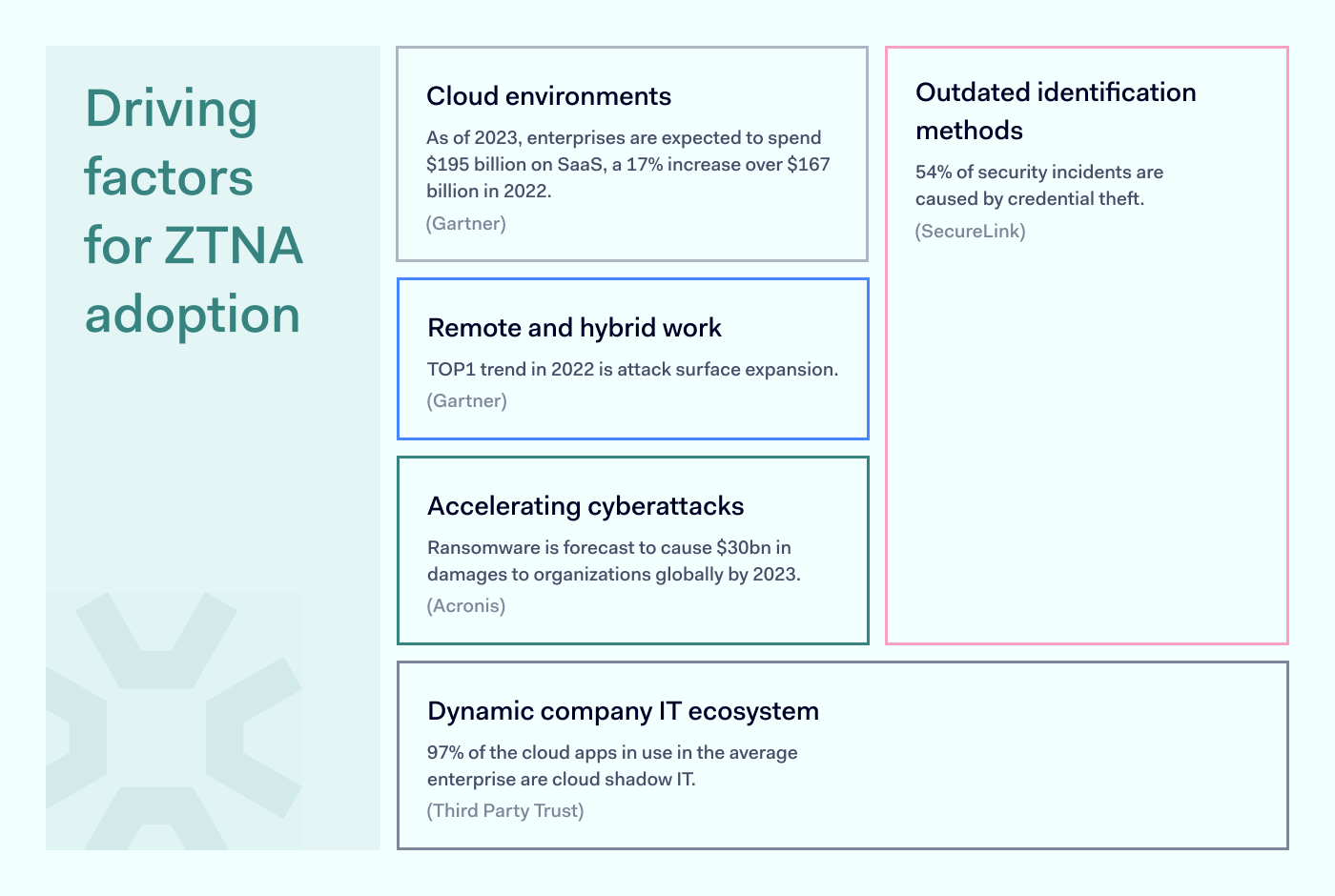
Driving factors of ZTNA adoption
The peak of ZTNA matched with hybrid and remote work developments globally introduced by the COVID-19 pandemic. Although opinions tend to clash, remote work is here to stay, and ZTNA maintains its importance to business network security.

To securely return to old ways of working – the static office-contained perimeter, which is the least challenging to maintain and control – all of the workforce should come back to their corporate desks.
Migration to the cloud is gaining momentum as it offers more flexibility and reduces the complexity of traditional IT perimeter.
The password more often causes security issues than prevents it and needs to be reconsidered and redesigned to move to more sustainable solutions.
Evolved understanding of a workplace with WFA (Work From Anywhere) quickly showed the comforts of working from home or cafe, answering work emails from a personal phone, or watching TV series on a corporate laptop after working hours. Yet these blurred lines stretch the reach of unapproved applications and devices blending into the company network.
Although the digital landscape and new modern habits might be alarming, going backward seems unrealistic. Thus ZTNA helps manage current cybersecurity challenges in this technological evolution.
State of remote work
There’s no denying that companies will have to accept the turned tables — employees now consider not how many days they will decide to work from home but how often they are willing to show up in the office.

If the workforce is not to return to the office full-time, ZTNA naturally cannot be discarded from the company’s cybersecurity strategy.

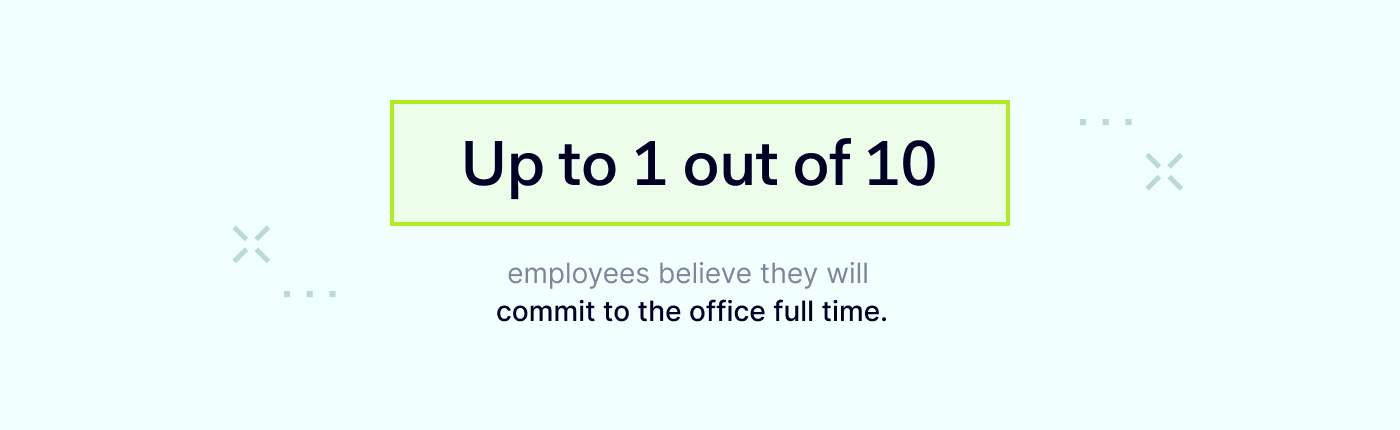
According to ZK Research 2022 Work-from-Anywhere Study, just one – or even less – out of 10 employees consider 100% work on-site, leaving most of the workforce a risk factor to data and application security.
How do companies adopt Zero Trust?
Zero Trust is dominant in creating security strategies. Statista survey revealed that one-third of polled companies, as of January 2022, already had a formal strategy actively embracing a Zero Trust policy. Only 20 percent of respondents had no Zero Trust strategy as of 2022.
Statista also concluded that almost one-fifth of respondent organizations completely discard the Zero Trust model as a cloud security strategy while the vast majority (81%) fully or partially embrace Zero Trust model guidelines for building internal security policies.

It’s safe to say that Zero Trust has been assigned an important and influential role in shaping the security infrastructure face. The mindset combines Zero Trust backed practices of accountability, consistency, dependability, and transparency to activities and processes within the organization network.
How to transition to Zero Trust?
Benefits for businesses that adopt ZTNA to enhance the security of their network. Deploying Zero Trust-based features establishes secure cloud access and allows network segmentation for least privileged access to resources.
The model reduces insider threat by protecting internal applications and lowering the potential of account breach risk. Overall, ZTNA adoption supports the company’s journey to achieving compliance requirements.
Zero Trust Network Access is a predominant framework of any setup that deals with hybrid work as an alternative to VPN. NordLayer solution makes implementation of ZTNA easy and integrable despite the existing infrastructure in your company. Reach out to learn more about securing your business network with ZTNA within minutes.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
These days, cybercrime is rampant. It’s no longer a matter of “if” you’re going to suffer an attack but “when” it will happen. All companies want to be ready for any crisis. And this is where a business continuity plan comes into play.
But what is a business continuity plan exactly? Why is it important? What should one include? Today, we’re exploring all these questions in-depth.
What is a business continuity plan?
A business continuity plan (BCP) is a document that sets guidelines for how an organization will continue its operations in the event of a disruption, whether it’s a fire, flood, other natural disaster or a cybersecurity incident. A BCP aims to help organizations resume operations without significant downtime.
Unfortunately, according to a 2020 Mercer survey, 51% of businesses across the globe don’t have a business continuity plan in place.
What’s the difference between business continuity and disaster recovery plans?
We often confuse the terms business continuity plan and disaster recovery plan. The two overlap and often work together, but the disaster recovery plan focuses on containing, examining, and restoring operations after a cyber incident. On the other hand, BCP is a broader concept that considers the whole organization. A business continuity plan helps organizations stay prepared for dealing with a potential crisis and usually encompasses a disaster recovery plan.
Importance of business continuity planning
The number of news headlines announcing data breaches has numbed us to the fact that cybercrime is very real and frequent and poses an existential risk to companies of all sizes and industries.
Consider that in 2021, approximately 37% of global organizations fell victim to a ransomware attack. Then consider that business interruption and restoration costs account for 50% of cyberattack-related losses. Finally, take into account that most cyberattacks are financially motivated and the global cost of cybercrime topped $6 trillion last year. The picture is quite clear — cybercrime is a lucrative venture for bad actors and potentially disastrous for those on the receiving end.
To thrive in these unpredictable times, organizations go beyond conventional security measures. Many companies develop a business continuity plan parallel to secure infrastructure and consider the plan a critical part of the security ecosystem. The Purpose of a business continuity plan is to significantly reduce the downtime in an emergency and, in turn, reduce the potential reputational damage and — of course — revenue losses.
Business continuity plan template
Password security for your business
Store, manage and share passwords.
30-day money-back guarantee
Business Continuity Plan Example
[Company Name]
[Date]
I. Introduction
Purpose of the Plan
Scope of the Plan
Budget
Timeline
The initial stage of developing a business continuity plan starts with a statement of the plan’s purpose, which explains the main objective of the plan, such as ensuring the organization’s ability to continue its operations during and after a disruptive event.
The Scope of the Plan outlines the areas or functions that the plan will cover, including business processes, personnel, equipment, and technology.
The Budget specifies the estimated financial resources required to implement and maintain the BCP. It includes costs related to technology, personnel, equipment, training, and other necessary expenses.
The Timeline provides a detailed schedule for developing, implementing, testing, and updating the BCP.
II. Risk Assessment
Identification of Risks
Prioritization of Risks
Mitigation Strategies
The Risk Assessment section of a Business Continuity Plan (BCP) is an essential part of the plan that identifies potential risks that could disrupt an organization’s critical functions.
The Identification of Risks involves identifying potential threats to the organization, such cybersecurity breaches, supply chain disruptions, power outages, and other potential risks. This step is critical to understand the risks and their potential impact on the organization.
Once the risks have been identified, the Prioritization of Risks follows, which helps determine which risks require the most attention and resources.
The final step in the Risk Assessment section is developing Mitigation Strategies to minimize the impact of identified risks. Mitigation strategies may include preventative measures, such as system redundancies, data backups, cybersecurity measures, as well as response and recovery measures, such as emergency protocols and employee training.
III. Emergency Response
Emergency Response Team
Communication Plan
Emergency Procedures
This section of the plan focuses on immediate actions that should be taken to ensure the safety and well-being of employees and minimize the impact of the event on the organization’s operations.
The Emergency Response Team is responsible for managing the response to an emergency or disaster situation. This team should be composed of individuals who are trained in emergency response procedures and can act quickly and decisively during an emergency. The team should also include a designated leader who is responsible for coordinating the emergency response efforts.
The Communication Plan outlines how information will be disseminated during an emergency situation. It includes contact information for employees, stakeholders, and emergency response personnel, as well as protocols for communicating with these individuals.
The Emergency Procedures detail the steps that should be taken during an emergency or disaster situation. The emergency procedures should be developed based on the potential risks identified in the Risk Assessment section and should be tested regularly to ensure that they are effective.
IV. Business Impact Analysis
The Business Impact Analysis (BIA) section of a Business Continuity Plan (BCP) is a critical step in identifying the potential impact of a disruption to an organization’s critical operations.
The Business Impact Analysis is typically conducted by a team of individuals who understand the organization’s critical functions and can assess the potential impact of a disruption to those functions. The team may include representatives from various departments, including finance, operations, IT, and human resources.
V. Recovery and Restoration
Procedures for recovery and restoration of critical processes
Prioritization of recovery efforts
Establishment of recovery time objectives
The Recovery and Restoration section of a Business Continuity Plan (BCP) outlines the procedures for recovering and restoring critical processes and functions following a disruption.
The Procedures for recovery and restoration of critical processes describe the steps required to restore critical processes and functions following a disruption. This may include steps such as relocating to alternate facilities, restoring data and systems, and re-establishing key business relationships.
The Prioritization section of the plan identifies the order in which critical processes will be restored, based on their importance to the organization’s operations and overall mission.
Recovery time objectives (RTOs) define the maximum amount of time that critical processes and functions can be unavailable following a disruption. Establishing RTOs ensures that recovery efforts are focused on restoring critical functions within a specific timeframe.
VI. Plan Activation
Plan Activation Procedures
The Plan Activation section is critical in ensuring that an organization can quickly and effectively activate the plan and respond to a potential emergency.
The Plan Activation Procedures describe the steps required to activate the BCP in response to a disruption. The procedures should be clear and concise, with specific instructions for each step to ensure a prompt and effective response.
VII. Testing and Maintenance
Testing Procedures
Maintenance Procedures
Review and Update Procedures
This section of the plan is critical to ensure that an organization can effectively respond to disruptions and quickly resume its essential functions.
Testing procedures may include scenarios such as natural disasters, cyber-attacks, and other potential risks. The testing procedures should include clear objectives, testing scenarios, roles and responsibilities, and evaluation criteria to assess the effectiveness of the plan.
The Maintenance Procedures detail the steps necessary to keep the BCP up-to-date and relevant.
The Review and Update Procedures describe how the BCP will be reviewed and updated regularly to ensure its continued effectiveness. This may involve conducting a review of the plan on a regular basis or after significant changes to the organization’s operations or threats.
What should a business continuity plan checklist include?
Organizations looking to develop a BCP have more than a few things to think through and consider. Variables such as the size of the organization, its IT infrastructure, personnel, and resources all play a significant role in developing a continuity plan. Remember, each crisis is different, and each organization will have a view on handling it according to all the variables in play. However, all business continuity plans will include a few elements in one way or another.
Clearly defined areas of responsibility
A BCP should define specific roles and responsibilities for cases of emergency. Detail who is responsible for what tasks and clarify what course of action a person in a specific position should take. Clearly defined roles and responsibilities in an emergency event allow you to act quickly and decisively and minimize potential damage.
Crisis communication plan
In an emergency, communication is vital. It is the determining factor when it comes to crisis handling. For communication to be effective, it is critical to establish clear communication pipelines. Furthermore, it is crucial to understand that alternative communication channels should not be overlooked and outlined in a business continuity plan.
Recovery teams
A recovery team is a collective of different professionals who ensure that business operations are restored as soon as possible after the organization confronts a crisis.
Alternative site of operations
Today, when we think of an incident in a business environment, we usually think of something related to cybersecurity. However, as discussed earlier, a BCP covers many possible disasters. In a natural disaster, determine potential alternate sites where the company could continue to operate.
Backup power and data backups
Whether a cyber event or a real-life physical event, ensuring that you have access to power is crucial if you wish to continue operations. In a BCP, you can often come across lists of alternative power sources such as generators, where such tools are located, and who should oversee them. The same applies to data. Regularly scheduled data backups can significantly reduce potential losses incurred by a crisis event.
Recovery guidelines
If a crisis is significant, a comprehensive business continuity plan usually includes detailed guidelines on how the recovery process will be carried out.
Business continuity planning steps
Here are some general guidelines that an organization looking to develop a BCP should consider:
Analysis
A business continuity plan should include an in-depth analysis of everything that could negatively affect the overall organizational infrastructure and operations. Assessing different levels of risk should also be a part of the analysis phase.
Design and development
Once you have a clear overview of potential risks your company could face, start developing a plan. Create a draft and reassess it to see if it takes into account even the smallest of details.
Implementation
Implement BCP within the organization by providing training sessions for the staff to get familiar with the plan. Getting everyone on the same page regarding crisis management is critical.
Testing
Rigorously test the plan. Play out a variety of scenarios in training sessions to learn the overall effectiveness of the continuity plan. By doing so, everyone on the team will be closely familiar with the business continuity plan’s guidelines.
Maintenance and updating
Because the threat landscape constantly changes and evolves, you should regularly reassess your BCP and take steps to update it. By making your continuity plan in tune with the times, you will be able to stay a step ahead of a crisis.
Level up your company’s security with NordPass Business
A comprehensive business continuity plan is vital for the entire organization’s security posture. However, in a perfect world, you wouldn’t have to use it. This is where NordPass Business can help.
Remember, weak, reused, or compromised passwords are often cited as one of the top contributing factors in data breaches. It’s not surprising, considering that an average user has around 100 passwords. Password fatigue is real and significantly affects how people treat their credentials. NordPass Business counters these issues.
With NordPass Business, your team will have a single secure place to store all work-related passwords, credit cards, and other sensitive information. Accessing all the data stored in NordPass is quick and easy, which allows your employees not to be distracted by the task of finding the correct passwords for the correct account.
In cyber incidents, NordPass Business ensures that company credentials remain secure at all times. Everything stored in the NordPass vault is secured with advanced encryption algorithms, which would take hundreds of years to brute force.
If you are interested in learning more about NordPass Business and how it can fortify corporate security, do not hesitate to book a demo with our representative.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordPass
NordPass is developed by Nord Security, a company leading the global market of cybersecurity products.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.







 Marvin Petzolt, Senior Application Security Engineer at Nord Security
Marvin Petzolt, Senior Application Security Engineer at Nord Security






