
Previously, I wrote about the prevention steps while developing your web application. While developing, you need to test it too, and of course, after development is done and the code is merged again, the application must be tested by the QA team.
When the code is in the development stage, and you just want to test the functionality, you don’t need to set up an environment. The test would be done in your localhost. But if you want to do security tests, you will need to set up an environment. In this article, I want to show you how to set up a test environment, which will also serve as a reference point for the following articles.
Why is it good practice to set up an environment with virtual machines when testing a web application?
First, I will be focusing on testing the HTTP requests/responses as they are something the attacker will first try to compromise.
Thus, to test if HTTPs are secure, you can set up some virtual machines.
As I mentioned, our focus will be on HTTP. First, I will give a short description of HTTP.
HTTP – HyperText Transfer Protocol
HTTP request is a request made by a client to access some resource on the server.
HTTP response is a response made by a server to a client with the requested resources.
HTTP cycle
- Client makes a request to the web server
- Web servers get the request and process it
- Server returns a response to the client
- Client receives the response
To achieve these actions HTTP protocol uses HTTP methods:
- POST is used when creating a new resource
- GET is used to get some resources to read them
- PUT is used when updating resource
- PATCH is used when modifying a resource. It will contain changes to the resource.
- DELETE is used to delete the resource.
Also, it is very important to mention the structure of the request/response to create or modify them.
HTTP requests/responses share a similar structure:
- A start-line contains information about the requests to be implemented and status (successful/failed).
- A custom(optional) set of HTTP headers specifying the request or describing the body included in the message.
- An optional body contains data required for the request or the document associated with a response.
The start-line and HTTP headers are called the head of the requests, and the payload is known as the body.
Setting up the environment
First, we will need to setup two virtual machines. I will be very detailed about the setup because I want this setup to be the reference for future articles.
We will set up two machines, one with Kali and the second with Ubuntu Server. You can set up many different hypervisors such as VMware Workstation Player/Pro, Oracle VirtualBox, Hyper-V-Manager(Windows Pro/Enterprise or Education), etc.
I am going to set up the environment using VMWare Pro.
Setting up Kali
There are some prerequisites to install Kali:
- 8 GB of memory
- A quad-core CPU
- 500 GB of Hard Drive
Download the Kali ISO image from their official site. Open VMware Workstation and go to File => New Virtual Machine or use Ctrl+N. Next window will pop up:

Click next, then browse to the Kali ISO file location and click next.

Choose Linux as the Guest Operating system, then click next.

Give the name to the VM and change location if you want, and then click on next.

As it says, recommended disk size is default 20GB. I recommend that you give around 30-50GB. Then mark on Store virtual disk as a single file and click next.

Click on customize the hardware, and the following window will appear:

Choose tab Processors and give your Kali VM two cores. Then choose memory for the virtual machine and give it at least 2GB of RAM. The network adapter should be NAT which is the default setting. Click finish.
You have set up the VM and now need to install the OS. You will use the Kali ISO file you chose initially and power up your VM.

Click on Graphical install. Then choose the language.

Then continue to the next step, which is choosing your location and continue. Choose the keyboard and continue.

Create a name for the VM.

When you click on continue, you will see the field to write domain name, which is optional. When you click on continue, a new window will appear and ask you to write your name.

The next window will ask you to create your username; I chose jenny. Then click on continue to create your password.

Enter and re-enter your password. Then configure the clock.

And then leave the first option selected and continue – Guided – use the entire disk.
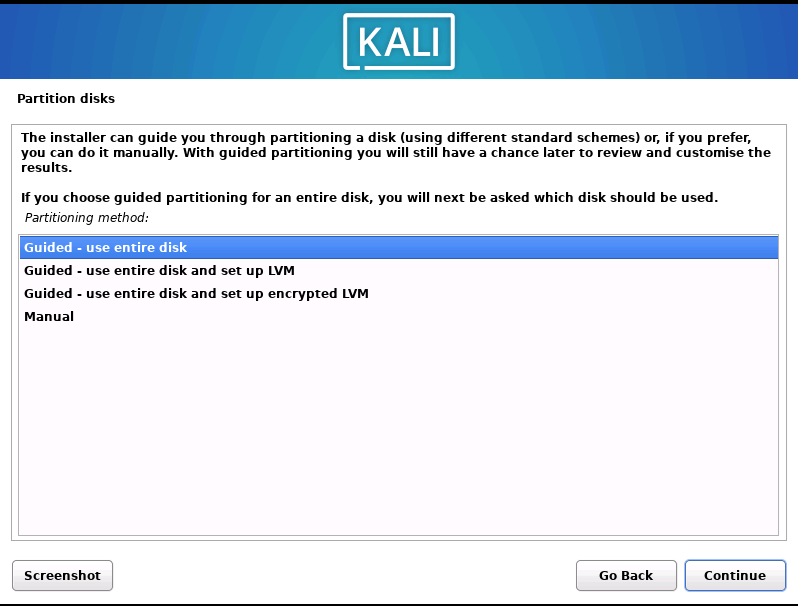
Then select the partition disk.

For our purpose, we can leave the first selected partitioning scheme. This is the simplest way.

Then make sure you leave selected finish partitioning and write changes to disk.

Then choose Yes.

For software selection, just choose the defaults as in the picture below.

Install the GRUB bootloader by clicking on yes.

Choose your virtual hard drive to install it on. It will probably be your only option to select.

Click continue and wait for the installation to complete. Great job, the installation is now complete! Don’t forget to reboot the machine after installation.
If you get prompted with the installation again, go to your VM settings – Edit Virtual Machine Settings, choose CD/DVD and uncheck and check the Use Physical Drive box. This is done so that you don’t boot off the ISO again, which would ask you to install Kali again. You already installed it, and it is on your virtual hard drive.
Now we have set up one virtual machine and are left with the second one – our Ubuntu Server.
Setting up Ubuntu
I will repeat the step by adding a new Virtual machine in VMware Workstation.
There are some prerequisites to install Ubuntu:
- GHz Dual Core Processor
- 20GB hard drive space
- 1GB RAM
Open WMware and add a new VM. Repeat the entire process in the same way as we did for Kali; just use the Ubuntu Server ISO file.
When Ubuntu VM is created, proceed with the installation of the OS.
First, power on your new Ubuntu machine. Use your keyboard to navigate through the installation process. Use Space to check boxes if you want to choose something other than defaults; use Enter to continue.

Choose language and press enter, do the same for the next step when choosing the keyboard. Then hit enter.

This looks good to me, so I move on to the next step. Then for the proxy and mirror address, press enter – I am not adding anything here, and I am choosing the default mirror as it will pick the closest server to my location, thus giving me the fastest install.

Deselect set up this disk as an LVM group. Then press enter and for the next step press enter again.

Press Continue.

Fill in all fields and click Done. No Ubuntu token is necessary for the next step, so press enter.
Select to install OpenSSH server and enter.

For the next step, leave all unmarked and press enter. Make sure you reboot the server and press enter. Voilà! Your Ubuntu machine is ready to use!
We have set up the second virtual machine and are ready to ping them, so we know they see each other.
How to ping Ubuntu from Kali in the local environment
Finally, we can now run both machines and check their connection. I am using Kali as my attacker machine and Ubuntu as the target.
I will show you in the following article how to create a basic Angular app and use Docker to deploy the app on port 8080. But until then, we will try to hit the Ubuntu machine from Kali using Ubuntu’s IP address.
But at this stage, I want to test if Kali can “see” Ubuntu. Open Ubuntu, check the IP address using command – ip a, and get the inet address under the ens3 interface. This is the network interface that was set up during installation. My IP for Ubuntu Server is: 192.168.221.129.
Open Kali, go to the terminal, and use the PING command with that IP address:

Ping was successful!
Lastly, to make your life easier, you might want to give your Ubuntu server a static IP, and you can also edit the /etc/hosts file on your attacker machine so you can SSH in with its name without using the IP address.
Conclusion
Good work! We finished setting up, and now we are ready to familiarize ourselves with OWASP ZAP (Zed Attack Proxy), which we will use to test our web application. For the upcoming article, it is very important to follow the steps in this article so you have everything set up.
In the end, secure code is the cheapest code!
#Kali #Ubuntu #Security_testing
Cover photo by Markus Winkler
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About VRX
VRX is a consolidated vulnerability management platform that protects assets in real time. Its rich, integrated features efficiently pinpoint and remediate the largest risks to your cyber infrastructure. Resolve the most pressing threats with efficient automation features and precise contextual analysis.








