How should you set up your security policies for your employees working from home? What are the potential culprits of a remote workforce? And is BYOD putting your organization at unnecessary risk of a data breach? Some love it, and some hate it, but there’s no use turning a blind eye to the massive surge in the number of employees working from home.
Ever since covid turned the world upside down in 2020, working remotely became the norm… and a new threat to data security. Covid-19 sent employees packing (to their home offices). Across the globe, workers have been working from home, but not every company has managed to keep up with the security policy department.
Based on the 2022 Verizon Data Breach Investigations Report, 82% of all data breaches involve the human element. You probably know all too well by now how hard it is to keep those humans in check (security-wise), even if they’re all in the same building. But making sure everyone is being safe when they’re out of sight? Are you sure your work-from-home guidelines for employees are up to date?
With 8 in 10 people working either in a fully remote or hybrid environment (and the numbers are expected to rise, based on a 2022 AT&T study), figuring out and maintaining a work-from-home policy is not just important; it’s critical to any organization’s security.

These are the top things to keep in mind if your organization employs remote workers:
What are the security risks of working from home?
First of all, let’s be clear about one thing: It’s called “work from home”, but unless you are specifically restricting your employees from working outside of their residence, they could be all over the place: from a cafe downtown to a beach on the other side of the world.

That requires smarter planning, stronger policies, and better communication with employees on your part.
Remote work poses a wide variety of cybersecurity risks due to all the potential scenarios and versions of remote work. Some potential considerations:
- Without an IT department in the office next door, your remote worker may struggle with their limited IT skills.
- What type of networks are your employees connecting to? Are they using public wifi?
- Are you providing hardware for remote workers, or are they using their own devices?
- Is your infrastructure cloud-based to allow for a more functional work-from-home solution?
- What are your employees’ work habits? Could they be endangering your data with their behavior?
The question is: How can you protect my organization from external cyber-attacks and the negligence of employees without making it difficult for your employees?
Because if it’s difficult, hard to understand, and tedious, your employees won’t adhere to your security policies.
The most important work-from-home security policies
Which security you set up for your organization will depend on your specific circumstances. But you don’t need to reinvent the wheel.
There are numerous regulations already in existence that your organization may or may not need to comply with that already specify the most important remote work policies.
You can also use ISO 27001, a major guideline for the establishment of an effective information security management system, to set up the best possible data security policy for your organization. Learn more about ISO 27001

Some areas that will always need to be addressed are:
Securing networks
It can be as simple as making sure that your employees’ home wifi router isn’t still on the default password and insisting they never use public wifi when connecting to your organization’s systems unless they use your organization’s VPN (a virtual private network).
A VPN will encrypt data being sent and received, preventing data leaks. It’s like a disguise for your employees’ online identity and your sensitive data.
Multi-factor authentication
Enforce a strong password policy and require changing passwords periodically, but don’t stop there. Have your employees use two-factor authentication to log onto your organization’s systems as an extra layer of protection.
This can be anything from utilizing single-use passwords to using biometrics.
Two-factor authentication can dramatically reduce the success of phishing and malware attacks since they often rely on stealing information such as passwords to infiltrate a system.
Have you heard of Zero Trust? The Zero Trust Approach is an evolving data loss protection model based on the need to authenticate and authorize any access to the network because trust is not assumed even if it has already been granted. It’s a great tool that can help you set up your authentication requirements.
Encryption
Encryption means that data from emails and documents is encoded, and only authorized parties can access and decipher it.
Sure, every device has an encryption option (but is it turned on?), but you can also implement data encryption software to protect your organization. Encryption is also used to protect sensitive data that is transferred between employee devices and company servers.
Using a VPN will encrypt data going to and from your remote worker through the internet.
Up-to-date software and security systems
Make sure all of your employees working from home have up-to-date firewalls, software, and security systems on all of their devices. You want all security patches to be activated as soon as they come out so that any vulnerabilities in the system are managed.
This can be harder to achieve in the BYOD (bring your own device) model. More on that is below.
Communication and support
Provide clear channels of communication. Educate your employees on how to report any suspicious online activity. Instruct them on how to spot a phishing attempt or security breach. Do your work-from-home employees know who to talk to in case a security issue comes up? Have someone within each team act as the go-to contact and provide guidelines for what types of issues should be reported.
Safe behavior
Talk to your employees about safe behavior – Are they working in an environment where people can easily see their screens? Do they know not to share sensitive information over messaging systems or on social media? Are they doing enough to prevent hardware theft?
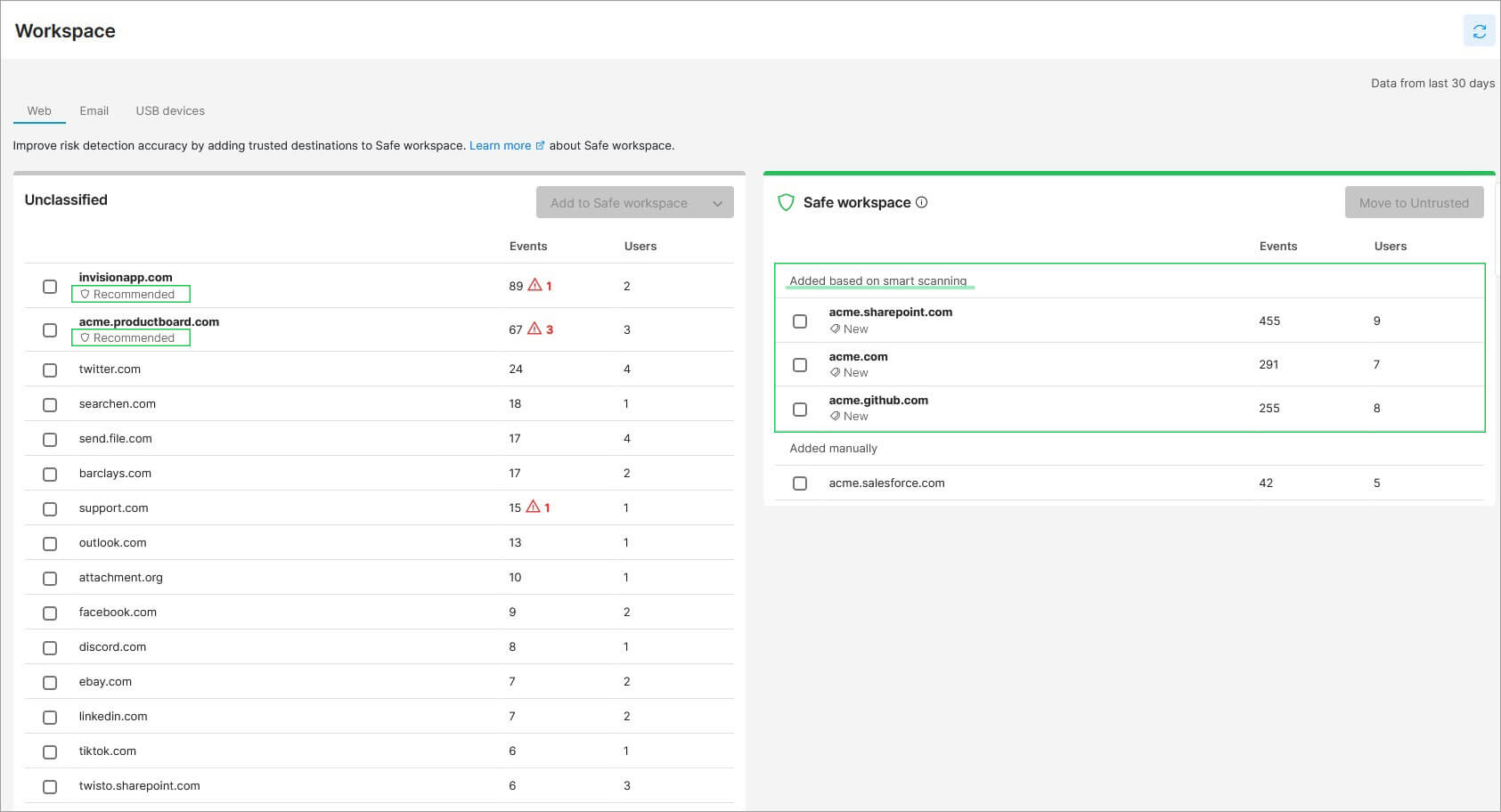
Dedicated DLP Systems
Dedicated DLP (data loss prevention) systems such as Safetica’s solutions use a centralized and automated system to monitor and report on everything happening in an organization’s cybersecurity landscape – on-site or off. You will feel more secure knowing that no matter where your employees are, your organization’s sensitive data will remain safe.
Dedicated DLP vs Integrated DLP: Which one makes sense for your organization?
How to explain and enforce security guidelines
For in-house employees, you can use things like posters and LED visuals to spread security messages around the office. You’re also more likely to see questionable behavior or notice the need to distribute that new security brochure you spent too long putting together.

For work-from-home employees, out of sight and literally off-site equals fewer possibilities to have any physical effect on the people you work with. You’ll need to think out of the box and remember that it’s much easier to forget about policies (even if it’s by accident) when you aren’t in the office.
Learn more about educating your employees about data security.
school
Simply put, in order to maintain awareness, you need to keep your policies easy to understand, easy to implement, and easy to remember. And for remote workers also easy to find in the first place.
Since practice makes perfect, everyone in the organization can benefit from a friendly reminder from time to time. Can you plan an email campaign to explain one security rule every two weeks simply? Have team leaders lead by example (that means higher management, too!), and make data security a topic in regular meetings.
To get the word out, get personal and KISS! Emails and passive messages are great as refreshers, but your employees to really hear you and not just scan the security checklist you send them; they need to hear it from the horse’s mouth.
All policies look great on paper (even the digital kind), but they make a much bigger impact during a live video presentation by the IT Director or even CEO – you are letting your work-from-home employees attend important meetings online, right? If it’s just George, the IT guy hounding them in yet another Slack message, he’ll barely be heard.
So keep it short and simple (KISS!), but make it count.
Specifics of BYOD when working from home
If your remote employees use computers and other devices that your organization provides to them, you are able to make sure that all equipment and software comply with company standards and policies.

But what about BYOD? If employees use their own devices, your work-from-home guidelines for employees will need to:
- Specify approved devices
- Separate personal and company data
- Plan for ongoing maintenance and updates of all devices
- Set restrictions on what can and cannot be installed on the device
- Consider potential legal issues/difficult data retrieval
- Explain ownership expectations and procedures upon an employee’s termination
While BYOD has obvious advantages, such as reduced costs and potentially greater mobility, it also poses a greater security risk for your organization.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Safetica
Safetica is to provide small and mid-sized companies with the same quality data protection that corporations have – affordably, and without any additional IT administration or disruptions in operation.