Not all cases of employee data theft come from bad intentions. Lukasz Krupski’s journey at Tesla began heroically. His quick action as he tackled a fire hazard at a Norway Tesla exhibition won him praise from Elon Musk.
But after finding monitoring software on his laptop and being dismissed, Krupski felt compelled to leak safety and data protection concerns, known as the ‘Tesla Files,’ to the media. These leaks, which revealed employee and customer data alongside issues with Tesla’s technology, sparked widespread discussion and legal scrutiny.
Krupski’s actions, motivated by a desire to highlight serious safety concerns, have highlighted the ethical challenges and accountability in technology.
While his case might be somewhat heroic due to his motivations, it’s essential to remember that not all instances of employee data theft are for noble reasons; sometimes, they’re purely for personal gain.
As we explore the topic of preventing data theft by employees, it’s critical to differentiate between the motivations behind such actions and implement robust security measures to safeguard sensitive information.
Key takeaways
Employee data theft involves staff taking or sharing company data without permission, posing risks to the company’s security and trust, whether done on purpose or by accident.
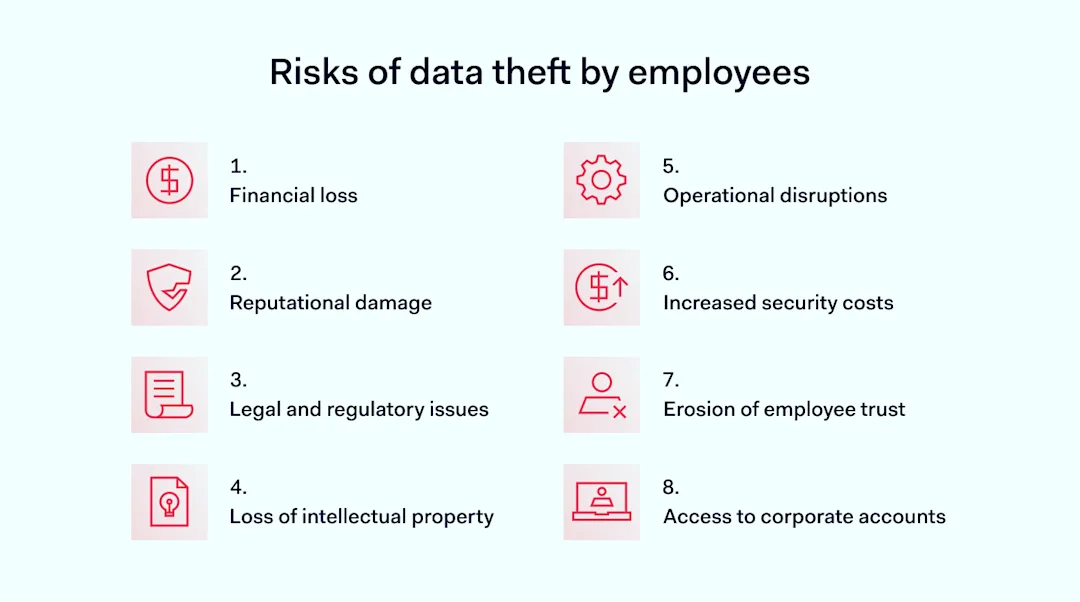
The theft of sensitive data by employees can lead to financial losses, reputational damage, legal issues, operational disruptions, erosion of trust among team members, and unauthorized access to corporate accounts.
To protect sensitive information and prevent data theft by employees, companies should implement robust access controls, use encryption for sensitive data, regularly conduct security training, and establish a clear data security policy.
Enhancing data security further involves implementing MFA, securing physical access to facilities, using updated anti-malware and anti-phishing solutions, and adopting a Zero Trust security model that requires continuous verification of all users.
NordLayer helps prevent employee data theft through advanced cybersecurity tools like Cloud Firewall and network access control solutions, which help achieve network segmentation and the Zero Trust framework.
What is employee data theft?
Employee data theft happens when an employee takes or shares a company’s data without permission.
This can be intentional, as in cases where someone decides to steal sensitive information to sell or use against the company. Sometimes, it happens by mistake, like when an employee accidentally exposes information because they weren’t careful. No matter the intent, such theft is a big problem for a company’s safety and credibility.
The risk involves all sorts of sensitive data. This includes personal details about employees and customers, financial information, strategic documents, and passwords to corporate accounts.
There are many ways someone might steal corporate data, such as copying it to a personal device, sending it through unsecured emails, or using harmful software to sneak into a company’s systems.
Another well-known case that highlights the risks of employee data theft involves Anthony Levandowski. He was an engineer at Google’s Waymo, the self-driving car project. Before leaving, Levandowski took thousands of files about Google’s technology for autonomous vehicles. He then founded a self-driving truck company named Otto, which Uber bought soon after. This led to a major legal fight between Waymo and Uber, focusing on accusations that Uber benefited from the stolen secrets. This story shows why it’s so crucial to protect sensitive data.
Risks of data theft by employees
A data breach doesn’t just stop at the act of theft; it opens up a Pandora’s box of indirect risks. Here are some consequences companies can face when employees steal data.
![]()
Financial loss. When employees steal data, companies can face direct financial losses. This is because stolen sensitive information can lead to fraud or the loss of competitive advantage.
Reputational damage. A data breach caused by employee data theft can harm a company’s reputation. Customers and partners may lose trust, which is hard to rebuild.
Legal and regulatory issues. If employees take sensitive data, this can result in legal penalties for the company. This is especially true if the stolen information includes personal data protected by laws.
Loss of intellectual property. Corporate data theft can lead to the loss of proprietary information. This is a serious risk as it can give competitors an unfair advantage.
Operational disruptions. Data theft by employees can disrupt business operations. For example, if critical data is stolen, it might halt production or service delivery.
Increased security costs. To prevent employee data theft, companies may need to invest more in data security measures. This can include adopting a Zero Trust framework, which verifies every access request.
Erosion of employee trust. When corporate data theft occurs, it can create an environment of suspicion. This might reduce collaboration and trust among team members.
Access to corporate accounts. Employees who steal data might gain access to corporate accounts. This risk is particularly high with sensitive information that includes login credentials.
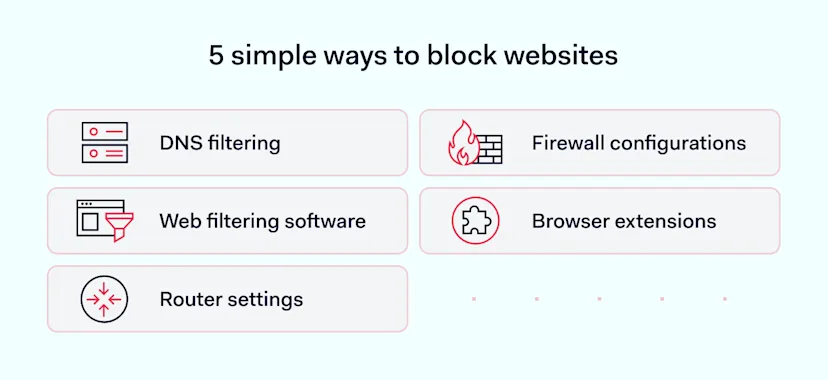
How to prevent employee data theft
The numbers tell us that sales and customer service roles are where we often find the biggest concerns for insider risks, with sales at 48% and customer service at 47%.
But really, keeping our data safe is a job for everyone in the company, not just designated roles. So, let’s explore some clever ways to protect your company.

![]()
Implement strong access controls
Setting up strong access controls, like a hardware or cloud firewall, and dividing the network into sections makes sure employees can only get to the data they need for work. This helps in preventing data theft by employees.
It’s important to remember that not everyone needs to see everything in the company. Making it clear what’s confidential can also help stop data from getting out by mistake.
A firewall helps divide the network into sections with clear permissions. This way, you limit who can see sensitive data, helping to avoid accidental sharing.
A cloud firewall (or a Firewall-as-a-Service) makes it easy to set up these divisions, giving specific access rights to certain people or groups. This is great for data security because it helps contain potential problems if something goes wrong. Thanks to how you’ve divided it, employees can only see a small part of the network. This means threat actors can’t do as much damage even if it’s an employee.
Use encryption for sensitive data
Encrypting sensitive data protects it, making the data unreadable to unauthorized users. This is effective even if data is stolen, as the thief cannot use it without the decryption key.
The downside is that managing encryption keys requires careful security measures to prevent them from being stolen as well.
Conduct regular security training
Educating employees about the importance of data security and how to prevent data theft is crucial. Regular training can make employees aware of the risks and teach them to handle data securely. But remember that training alone cannot prevent all instances of data theft, especially if malicious intent is involved.
Deploy data loss prevention (DLP) technology
Using data loss prevention, or DLP technology, is like having a smart security guard that watches over the information being shared in and out of the company. It makes sure that only the right data goes to the right places.
Think of it as having a guard who checks the passes at the door of a secure building. The guard stops people without the right pass (unauthorized data) from leaving.
But, just like any guard might sometimes stop someone by mistake (a false positive), DLP technology can accidentally block information that was okay to share. This means it’s really good at preventing data theft by employees, but it might need a little help sometimes to make sure it doesn’t stop the right information from getting through.
Establish a clear data security policy
A clear data security policy sets out rules for handling sensitive data and the consequences of data theft. This clarity helps prevent employee data theft by setting expectations. These policies must be regularly updated to remain effective and reflect new security challenges.
Implement multi-factor authentication (MFA)
Adding multi-factor authentication (MFA) to our security setup means we’re putting in place an extra step of verification, something more than just the usual password. This makes it much harder for someone to access data they shouldn’t.
If someone tries to sneak into an account or look at data they have no business seeing, MFA steps in. It sends a notification to either another employee or the person who owns the account, flagging that something out of the ordinary is happening.
This quick heads-up gives us a chance to act fast and stop any security problems before they grow, making MFA a really important tool in keeping our data safe.
Secure physical access to facilities
Make sure that only the right people can get into places where sensitive information or important servers are kept. This is especially important when you’ve got crucial servers in your office or when you’re dealing with sensitive data.
It’s essential to keep a close eye on who enters areas with critical data or infrastructure. Set up systems that check if someone is allowed in, like special locks or entry codes that only certain people have.
Use anti-malware and anti-phishing solutions
Adding anti-malware and anti-phishing software is a smart move to keep your data safe. But remember, these tools need to stay updated to fight off the latest cyber tricks. It’s also a good idea to teach your team how to spot those sneaky phishing emails. By keeping everything current and spreading a bit of know-how, you’re building a strong wall that keeps your data secure and out of the wrong hands.
Adopt a Zero Trust security model
The Zero Trust model operates on the principle that no one inside or outside the network is trusted by default. Implementing Zero Trust can significantly reduce the risk of data theft by requiring continuous verification of all users. However, moving to a Zero Trust architecture can be complex and requires significant adjustment for both IT departments and users.
No single method is foolproof, but a layered approach minimizes risks associated with employee data theft.
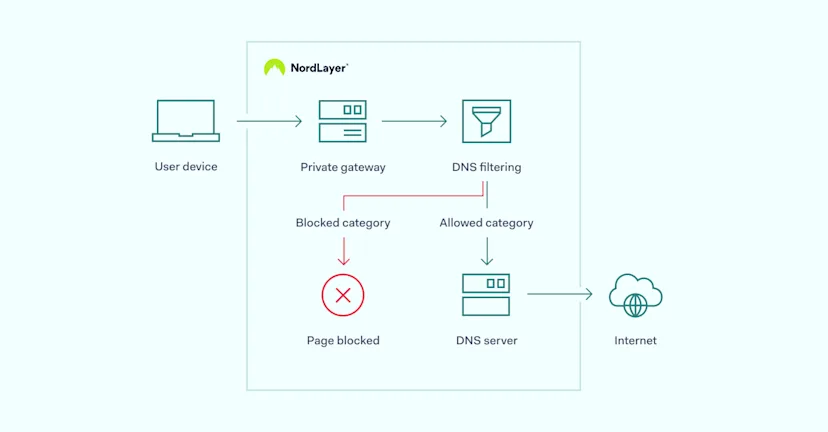
How NordLayer can protect against data theft by employees
NordLayer offers powerful cybersecurity tools, like Cloud Firewall and Network Access Control (NAC) solutions, to help your organization keep its sensitive data safe.
Network segmentation is an important part of the process. By breaking your network into smaller parts with strict access rules, you make sure only the right people can see important information. This is key to achieving the Zero Trust framework, which checks everyone’s need to access specific data, making it much harder for anyone to steal data or cause a breach. With NordLayer, setting up these secure sections in your network is straightforward and flexible.
Our Identity and Access Management (IAM) solutions add another layer of security by managing who gets access to what, beyond just passwords. The method combines Single Sign-On (SSO) with other checks to make sure every user’s sign-in is legit.
Other Network Access Control (NAC) solutions tighten security further by monitoring access based on IP addresses and device posture, allowing only compliant devices on the network. This approach offers a solid strategy on how to prevent data theft by employees.
For a tailored solution that fits your organization’s specific needs, contact our sales team. They can guide you through the offerings to find the best fit for bolstering your data security.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.