As technology continues to advance, the methods of malicious actors also evolve. As a result, cybersecurity has become a critical concern for organizations of all sizes. The 2023 Verizon report highlights that 74% of all breaches involve a human element, with internal actors accounting for 19% of cybersecurity breaches. In light of these statistics, protecting your business from insider threats becomes crucial.
Insider threats can pose significant risks to your organization’s sensitive data and operations, yet they are often overlooked. In this blog post, we will explore the world of insider threats, their unique risks, and key strategies for prevention.
Organizations can take proactive steps to protect themselves from this critical cybersecurity challenge by gaining a better understanding of insider threats. We will also provide real-life examples, best practices for mitigation, and how NordLayer can assist in fortifying your defenses.
Key takeaways
Insider threats can cause harm through data theft, fraud, sabotage, or unintentional actions.
The three main types of insider threats are malicious insiders, negligent insiders, and compromised insiders. It is essential to understand the motivations and behaviors of each type to mitigate and prevent insider threats effectively.
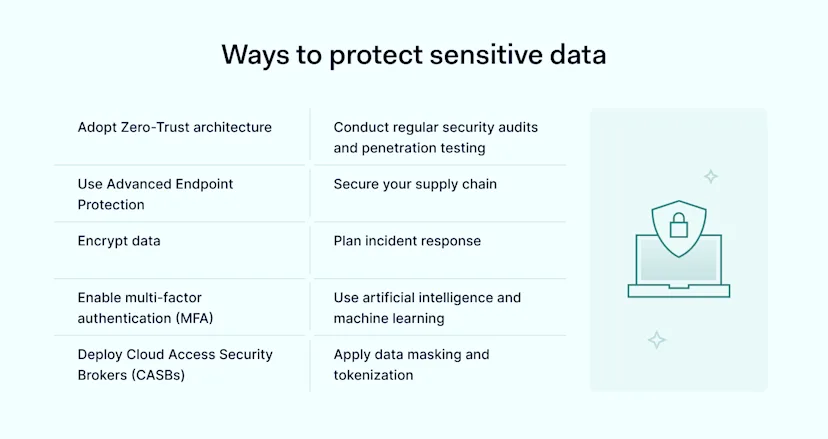
Best practices for insider threat prevention include access controls, employee training, user monitoring, multi-factor authentication, and clear policies.
Using advanced network security tools like NordLayer’s Network Access Control (NAC solution), which offers features such as Cloud Firewall and Device Posture Security, can help contain internal threats and control access.
What is an insider threat?
An insider threat is any current or former employee, contractor, or business partner who intentionally or accidentally misuses their access or insider knowledge to harm an organization’s IT systems, networks, or data. Insider threats can take many forms, including data theft, fraud, sabotage, and unintentional harm caused by careless actions or human error. Insider attacks can be divided into different types depending on the intention behind the actions.
Types of insider threats
Typically, there are three types of insider threats:
![]()
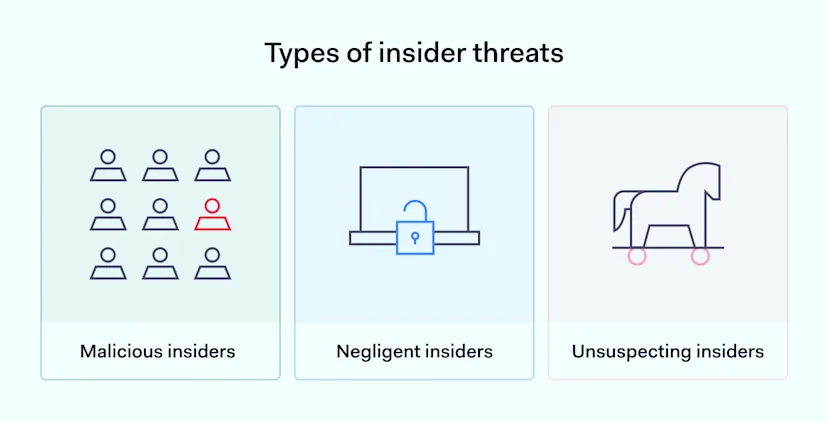
Malicious insiders who aim to cause harm deliberately through actions like data theft, sabotage, or espionage
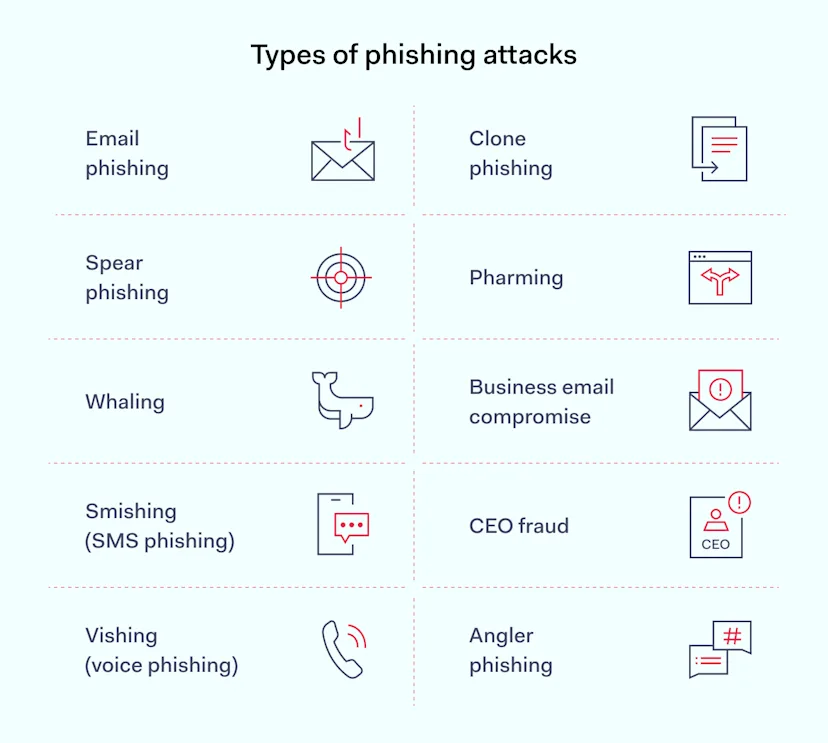
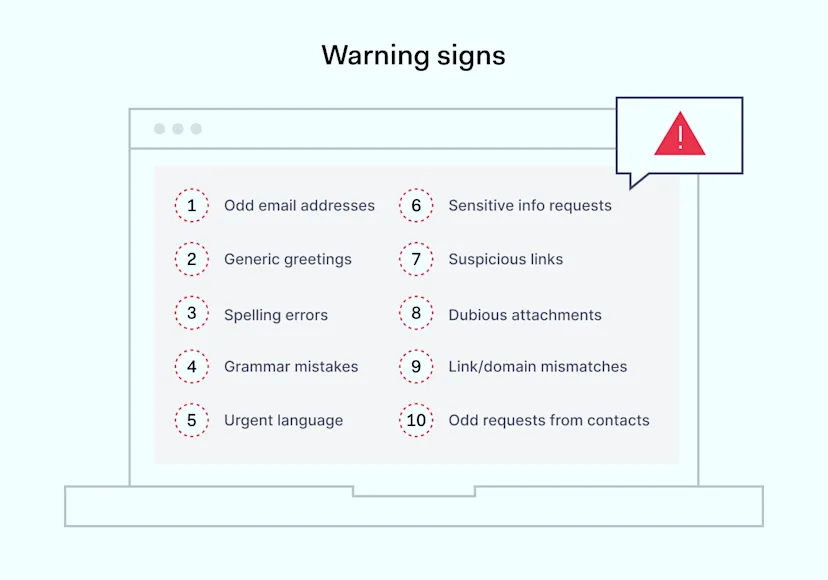
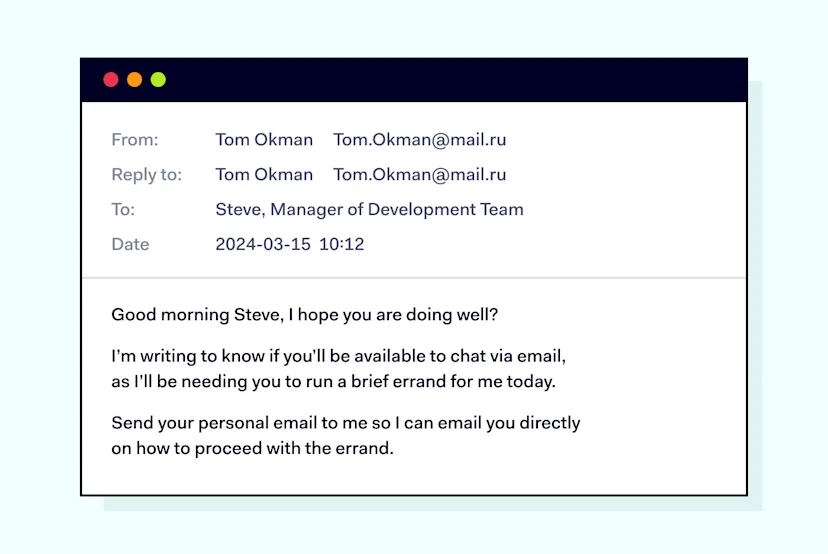
Negligent insiders whose careless actions like falling for phishing scams can unintentionally compromise security
Unsuspecting insiders whose credentials were stolen or devices were compromised by outsiders
Note that these types of insider threats can overlap or blend into each other.
Real-life examples of insider threats
Insider threats, including financial losses, reputational damage, legal liabilities, and operational disruptions, can severely affect organizations. When sensitive security information is exposed, it can be used by malicious actors to commit fraud, steal intellectual property, or launch further attacks against the company or its partners.
In some cases, the exposure of sensitive data can also lead to regulatory fines and legal penalties, particularly if it includes personally identifiable information or other confidential data.
Moreover, the loss of classified data can erode customer trust and damage the organization’s reputation, making it difficult to attract and retain customers, partners, and employees. In some cases, the impact of an insider threat can be felt for years, causing long-term damage to the organization’s bottom line and its ability to compete in the market. To illustrate the potential impact of internal threats, let’s have a look at some of the most infamous cases in recent history.
WikiLeaks in 2010
Chelsea Manning, a former US Army soldier, leaked classified military documents that included diplomatic cables, military reports, and videos of military operations in Iraq and Afghanistan. The release of the documents caused diplomatic tensions between the US and other countries, and Manning was sentenced to 35 years in prison.
The incident also led to calls for greater transparency and accountability in government operations and sparked a debate about the role of whistleblowers in exposing government misconduct.
National Security Agency (NSA) leak in 2013
Perhaps one of the most infamous cases of an insider threat, Edward Snowden leaked classified information from the NSA, exposing sensitive surveillance programs to the media. The leaked documents revealed that the NSA was collecting vast amounts of data on American citizens, including phone records and internet activity, without their knowledge or consent.
The leak sparked a global debate about privacy, surveillance, and the role of intelligence agencies in democratic societies. It also damaged the NSA’s reputation and strained its relationships with other countries, particularly those whose citizens were targeted by the agency’s surveillance programs.
Twitter compromise in 2019
An insider helped social engineer their way into compromised accounts on high-profile users like Barack Obama, Bill Gates, and Elon Musk. The cybercriminals then used these accounts to send out tweets promoting a Bitcoin scam. The fallout from the hack was significant.
The incident caused widespread confusion and concern among Twitter users, and the company’s stock price temporarily dropped as a result. The breach also raised questions about the security of social media platforms and the potential consequences of insider risks in this context.
How to prevent insider threats: best practices
As we have seen from the examples, internal threats can have serious consequences for organizations, including financial losses, reputational damage, and legal liabilities. To protect against these risks, companies need to take a proactive approach to cybersecurity.
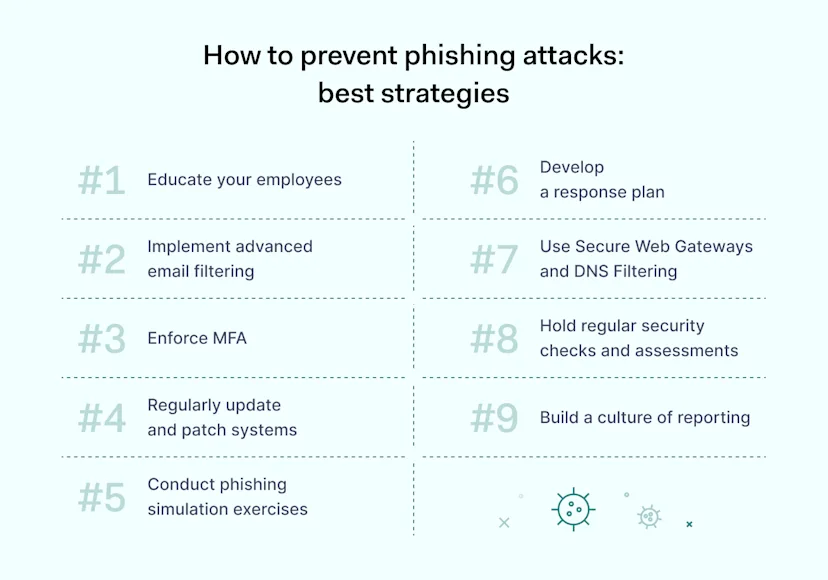
By following best practices for insider risk management, organizations can reduce the risk of data breaches, fraud, and other forms of malicious activity. Here are some of the most effective strategies that help prevent insider threats.
![]()
Implement access controls
Access controls are a critical component of insider threat detection and prevention. By limiting access to security information based on job roles and responsibilities, you can ensure that only authorized personnel can access classified data.
This approach is known as the principle of least privilege, which means that users are given only the access they need to perform their job functions. Regularly reviewing and updating permissions is also essential to ensure that access is appropriate and necessary. This process can help prevent unauthorized access, accidental or intentional data leaks, and other forms of malicious activity.
Employee training
It is essential to educate employees on cybersecurity best practices, including how to identify phishing attempts, use strong passwords, and report suspicious activities to the security teams. Providing regular training and awareness programs can help your staff stay up-to-date. Additionally, fostering a culture of security within the organization is equally important, where employees grasp the significance of safeguarding and are more likely to follow security policies and procedures.
Multi-factor authentication (MFA)
Multi-factor authentication is an additional layer of security that requires users to provide two or more forms of authentication before accessing sensitive data. Implementing MFA wherever possible can secure against illegal access and prevent breaches, even if a malicious actor has stolen a user’s password. Requiring a temporary code sent to a user’s phone in addition to a password can prevent insider attacks and make it much more difficult to gain access to private data. Based on statistics, having MFA increases protection in 50% of the cases.
Encryption
Encrypting confidential information both in transit and at rest is essential to protect against unauthorized access. Encryption scrambles data so that it is unreadable without the decryption key. This means that even if an attacker gains access to encrypted data, they will not be able to read it. Encryption can help protect data from being stolen or intercepted, and it is a key element of a comprehensive insider threat prevention strategy.
Establish clear policies
Developing and enforcing clear security policies is critical to preventing insider threats. These policies should cover data handling, acceptable technology use, and reporting procedures for security incidents. By having clear policies in place, employees understand expectations and boundaries. Regular reviews and updates are necessary to keep policies relevant and effective. Additionally, consistent enforcement ensures that the employees follow them.
Monitor user behavior
Conducting thorough background checks for new hires can help identify potential risks before they become a problem. Utilizing security tools to detect unusual or suspicious user behavior, such as accessing company resources, can also help identify potential threats.
Unusual access patterns can be a red flag, such as an employee accessing classified data outside of normal business hours or from an unusual location. Changes in user behavior, such as an employee becoming disgruntled or expressing dissatisfaction with their job or a sudden increase in downloads or transfers of private data, can also indicate an internal threat.
Once insider attacks have been detected, it is important to take immediate action to mitigate the potential damage. This may include revoking access to classified data, conducting an investigation to determine the extent of the breach, and taking steps to prevent further unauthorized access. Security teams should have a clear plan in place for responding to internal threats, including who to contact, how to contain the threat, and how to communicate with affected parties.
How NordLayer can help
NordLayer provides a multi-layered cybersecurity approach to protect your organization from insider threats. By integrating advanced encryption protocols, secure remote access capabilities, and robust network access control tools, NordLayer ensures comprehensive protection for your data and networks.
With NordLayer’s Cloud Firewall service, organizations can exercise granular control over access to internal resources and cloud tools, enhancing security with an extra layer of control. This feature allows organizations to implement advanced network segmentation strategies, dividing the network into smaller segments.
Different user groups, teams, and roles can only access the specific segments relevant to their job, preventing unnecessary lateral movement across the wider network. Through tailored access controls, it minimizes the risk of data leaks from unauthorized access within the system.
Moreover, NordLayer’s Network Access Control (NAC) solution offers adaptive security features—such as Single sign-on (SSO), Devise Posture Security, Virtual Private Gateway with fixed IP address, and MFA—that authenticate users and devices, enabling secure access across various platforms.
The key to insider threat protection is a combination of technology, policies, and people. While technology provides the tools to establish safeguards and enforce access controls, policies provide guidelines for secure usage. Moreover, engaged employees trained to recognize and report potential risks can help prevent threats from occurring in the first place.
Thus, with product managers and engineers constantly monitoring the threat landscape and responding by strengthening NordLayer’s solutions, we can help security teams create a more secure environment for their organizations.
Don’t let insider threats compromise your business. Start your journey towards a more secure future with NordLayer today.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.