The OpenSSH team surfaced a security issue earlier this month that specifically affects OpenSSH server version 9.1p1 (a.k.a. version 9.1). This version contains a memory double-free vulnerability (tracked as CVE-2023-25136) that can be reached pre-authentication by a remote attacker. Researchers, including JFrog and Qualys, have been investigating and providing proof-of-concepts of a denial-of-service scenario and remote code execution for the attacker.
What is the impact?
OpenSSH is a popular open source implementation of the SSH protocol and is available on many operating systems. While the installation base for OpenSSH is quite large (Shodan currently reports ~48k public-facing instances of OpenSSH servers running version 9.1), the potential impacts of this vulnerability are not yet fully understood and are still being investigated.
The denial-of-service attack vector may be successful against a number of operating systems running OpenSSH 9.1. However, it yields limited results because it only crashes the forked daemon instance that was spun up to handle the attacker’s SSH connection (leaving the parent ssh daemon still running to handle other incoming connections).
Exploitation of this vulnerability for remote code execution (RCE) is more complex, with a current proof-of-concept that only targets OpenBSD 7.2 without memory protections in place (such as ASLR, NX, or ROP defenses) and with code execution still contained within the ssh daemon’s sandbox. As researchers continue investigating RCE exploitation, other operating systems with attacker-bypassable memory malloc and double-free protections may be discovered. So, the ability to fully execute attacker-controlled code outside of the ssh daemon sandbox -even with memory protections in place– may be achieved.
Are updates available?
OpenSSH version 9.2p1 (a.k.a version 9.2) was released earlier this month and patches this vulnerability (CVE-2023-25136). For systems currently running OpenSSH 9.1, admins are encouraged to update to OpenSSH 9.2 or later.
How do I find vulnerable OpenSSH services with runZero?
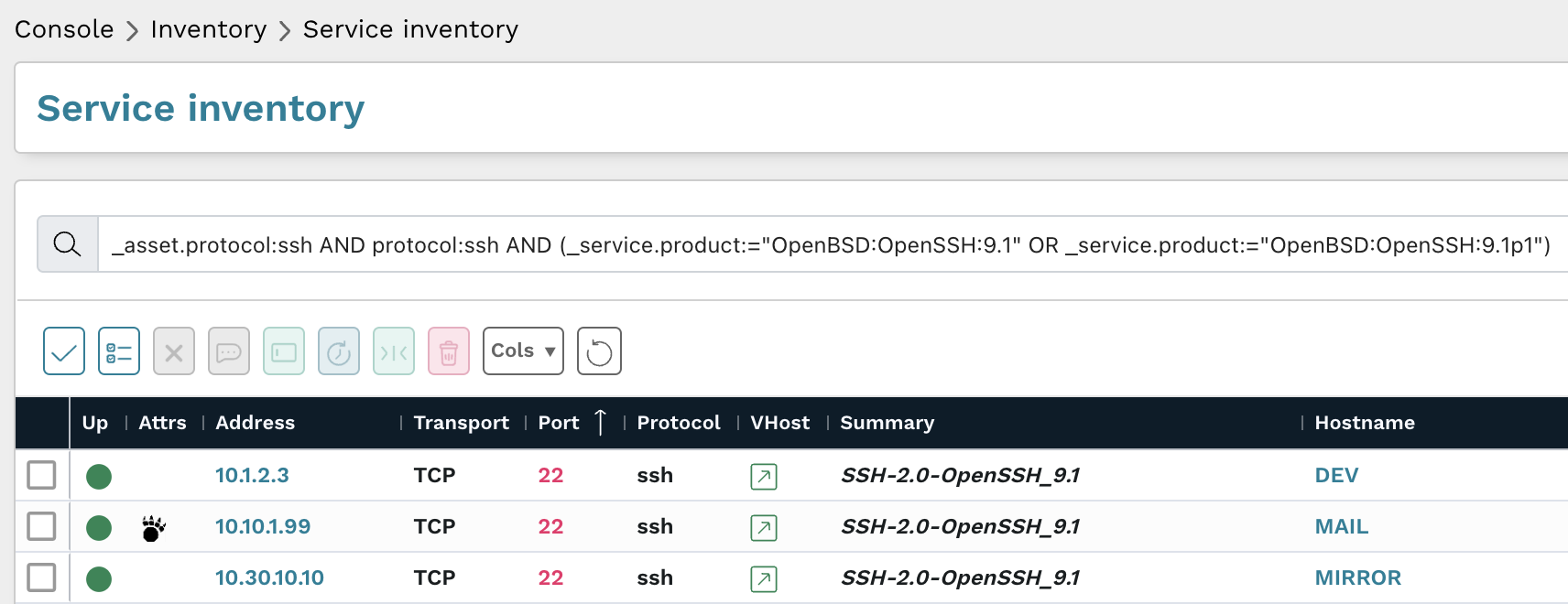
To locate OpenSSH servers running the vulnerable 9.1/9.1p1 version in your network, use the following prebuilt query in your Service Inventory:
_asset.protocol:ssh AND protocol:ssh AND (_service.product:="OpenBSD:OpenSSH:9.1" OR _service.product:="OpenBSD:OpenSSH:9.1p1")
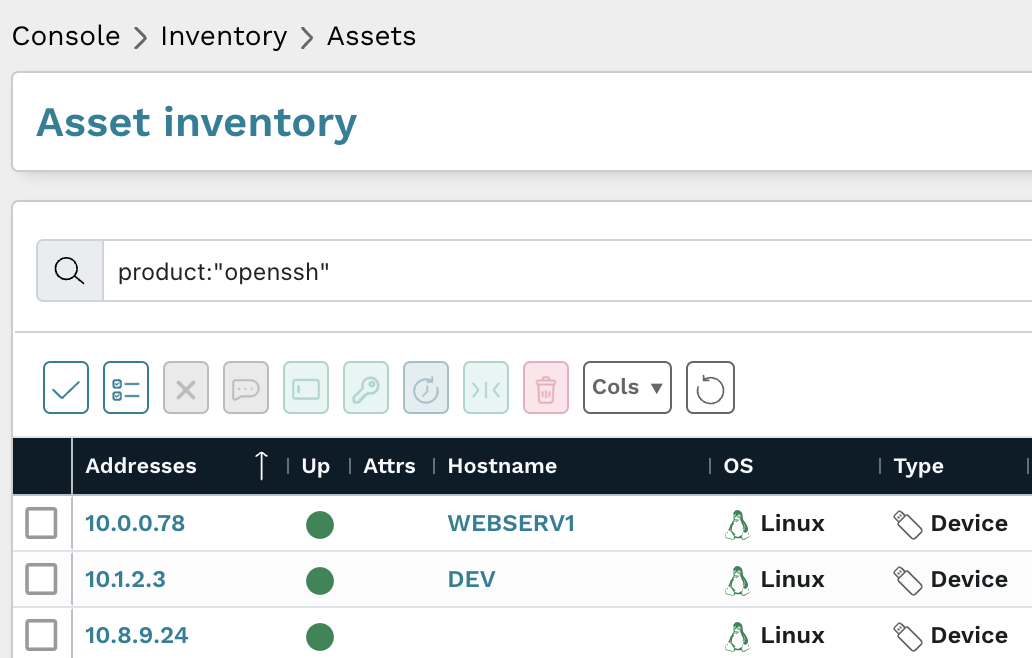
To local all OpenSSH servers in your network, use the folloing prebuilt query in your Asset Inventory:
product:”OpenSSH”
As always, any prebuilt queries are available from our Queries Library. Check out the library for other useful inventory queries.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About runZero
runZero, a network discovery and asset inventory solution, was founded in 2018 by HD Moore, the creator of Metasploit. HD envisioned a modern active discovery solution that could find and identify everything on a network–without credentials. As a security researcher and penetration tester, he often employed benign ways to get information leaks and piece them together to build device profiles. Eventually, this work led him to leverage applied research and the discovery techniques developed for security and penetration testing to create runZero.













