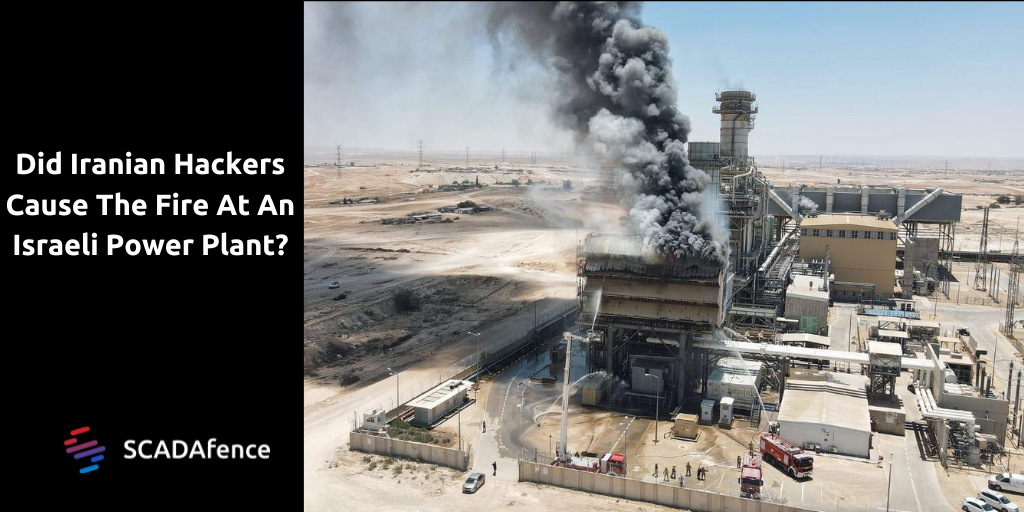
Almost immediately after a fire broke out in an active power plant in southern Israel on July 14, 2022, an Iranian hacking group claimed responsibility. While it’s understandable why the group, which goes by the name #Altahrea, would want to boost their hacker profile by saying they caused the fire, there is ample evidence that they actually had nothing to do with it.
The Orot Yosef power plant, part of the Edeltech group, is located in Ramat Hovav, Israel and has been in operation since 1989.
To understand why we believe this fire was not the work of hackers, let’s take a look at how this plant operates and what might have happened to cause the fire. (SCADAfence’s security team research lead Yossi Reuven also spoke about the attack to Techmonitor.ai)
Gas turbines can be used in conjunction with steam boilers by passing hot gasses from the boiler through a gas turbine to produce mechanical drive for electricity generation. This combined arrangement is commonly referred to as “cogeneration.” Cogeneration is thermodynamically the most efficient method for generating electrical power, and it is the method used by the Orot Yosef facility.
Why is this important? Understanding the process used by a facility is crucial to determining what event took place. Gas turbines require a correctly ratioed air-to-fuel mixture to operate. Running a turbine too rich or too lean, (too much air or too little air, respectively) can cause significant damage to the turbine. This means that if someone with malicious intent were able to compromise the air handling and run the turbine at maximum output with a lean mixture there is a good chance of detonation, overheating, loss of power, and damage to the turbine. These issues would all relate to the turbine housing and be far more catastrophic of an event.
We know that GE turbines were purchased and installed in the plant in 1989 as you can see in the image below from the Global Energy Observatory. (The GEO is a publicly available database of global energy information)
The Power Plant Fire
Shortly after the fire began, the Iranian hacker group #Altahrea posted a photo on Telegram of a fire that looks to have started in the building known as the, “Air Filter House”.
Most of the technology that resides inside the filter house is there to detect if the system is clogged. When a clog happens, it triggers the shutdown of the turbine to protect it from too much debris passing through the filter system, which can shorten the lifespan of the turbine.
Fire is a major risk for filter houses that have poor maintenance cycles. If filters are not replaced routinely, particulates and debris build up and all it takes for the filter cartridge pairs to go up in flames is a single spark.
Based on open-source intel, it is likely that this facility is running an Electrostatic Precipitator.
An Electrostatic Precipitator is typically used for pollution control to remove dirt from flue gasses in exhaust systems. Due to the fact that this facility has the ability to use Diesel as a secondary source of power generation, it is possible that an ESP could be present.
Another detail that provides relevant information is a redacted picture of Shodan.io’s Industrial Webcrawler revealing a Phoenix Contact EMpro PLC running a Webserver exposed to the internet as shown below.
The EMpro is used to measure voltages and current in a power supply system. The measure is used primarily to manage critical load balancing across a system and not for any critical process control of the filter house. If the device were to be compromised it would only allow an individual to carry out relatively small actions, and this is only in the event that the device had the Digital Output wired up.
This all begs the question, is it possible that a remote monitoring device was compromised in a way that allowed an adversary to trigger a discharge inside the filter house which then ultimately triggered a fire. Possibly. However it would require ideal conditions for this to happen and would also require a lapse in maintenance with a buildup of debris etc. I would expect that the same level of probability would occur if someone discarded a cigarette that was still lit and the filter house consumed it into the filter cartridge stage. In this case, that is a more likely cause of the fire, and not the Iranian hackers who claimed credit.
To learn more about how the SCADAfence Platform can protect your OT network request a demo today.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About SCADAfence
SCADAfence helps companies with large-scale operational technology (OT) networks embrace the benefits of industrial IoT by reducing cyber risks and mitigating operational threats. Our non-intrusive platform provides full coverage of large-scale networks, offering best-in-class detection accuracy, asset discovery and user experience. The platform seamlessly integrates OT security within existing security operations, bridging the IT/OT convergence gap. SCADAfence secures OT networks in manufacturing, building management and critical infrastructure industries. We deliver security and visibility for some of world’s most complex OT networks, including Europe’s largest manufacturing facility. With SCADAfence, companies can operate securely, reliably and efficiently as they go through the digital transformation journey.




