This is the last article in the ZAP series. In this piece, I will explain some of the main features of ZAP I didn’t cover in the previous part. Before we even start, I will remind you that this tool should be used just on the applications created for testing or the applications you would need to test.
We will divide this part of the series to cover a few topics:
- Sessions
- Generating Vulnerability Assessment Reports
- Passive Scanning
- Active Scanning
- Scan Policy Manager
Sessions
In the second part of the ZAP series, I mentioned sessions when we ran ZAP for the first time. I will summarize that.
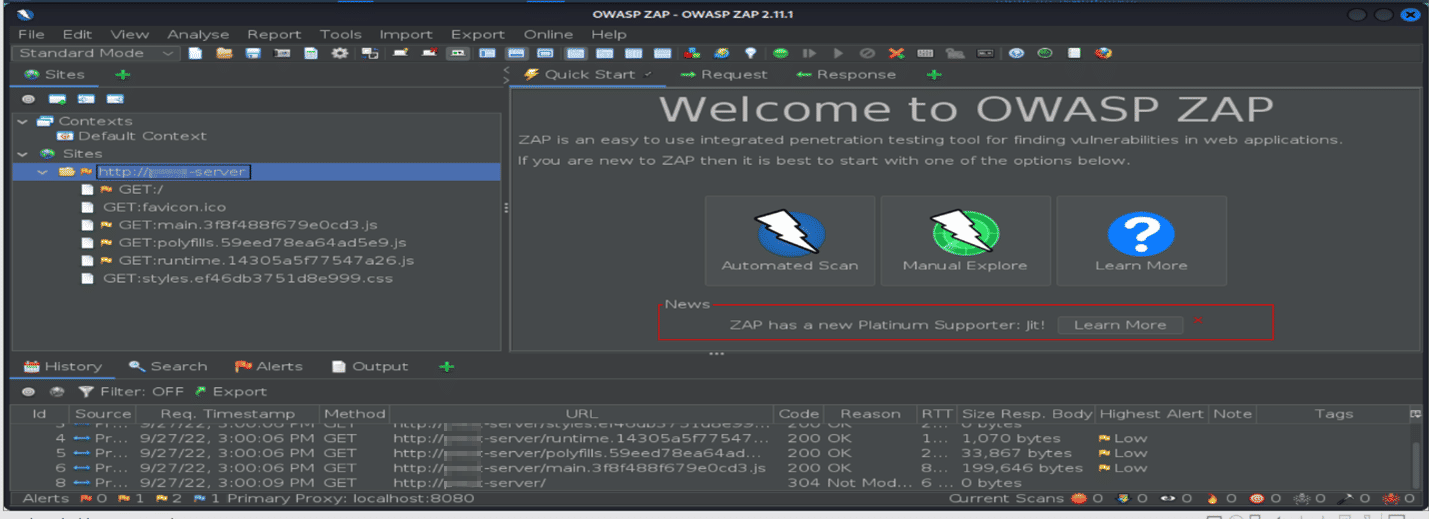
When you run the ZAP tool, this window will pop up:

I will also paste some explanation from the mentioned article about the third option when you don’t want to save the session:
We can select no, and if we want to save the session, we can do it at a later time.
If you choose to save the session, it will be saved to the disk in an HSQLDB database. The database gets a default location and name. You can access the db later. If you don’t persist a session, the files are deleted once you exit ZAP.
If we choose the first option: Yes, I want to persist this session with name based on the current timestamp the session will be stored in db folder directly and name will be based on the current timestamp. Mainly the mentioned folder where sessions will be stored is located in “%HOMEPATH%\OWASP ZAP\sessions” if you are using Windows or Kali, it is usually like in the picture below.

If we close the saved ZAP session and we want to open some other saved session, we should click on File > Open Session and find the session in its appropriate path.
If we choose the second option: Yes, I want to persist this session, but I want to specify the name and location new window will appear where you can type the desired fields. There is also a way to create a new session by clicking on the File tab > Persist Session. You can choose the location and the session’s name in the pop-up window.
There is also an option to compare two sessions. We can compare the current(opened) session with some previously saved ones by clicking on the Report tab > Compare with another session.
The other option ZAP provides is modifying the saved (current) session. That can be achieved by clicking on File > Snapshot Session As. Please don’t let the name “snapshot” fool you; imagine this option as Save As.
In pentesting, it is very important to organize your tests, so creating sessions will help you with better organization.
Next thing which is important for pentesters is making vulnerability assessment reports.
Generating Vulnerability Assessment Reports
This feature is not just important to provide for the management or the stakeholders. It is also important to collect history records of testing during the time so you can compare reports and make a conclusion about it.
When security testing is finished and you collect all results, you can start generating the report.
It is very important that we leave the sites we want to include in the report in the side tree (we can select all unnecessary sites and delete them). Then we will click on the Report tab > Generate Report, and the next window appears.
There are a few sections/tabs you can see. In the scope tab, you fill out basic information regarding the report file, but in other tabs: Template and Filter, you can specify what report will include.

The report will be saved as HTML and opened in the browser. It will be divided into sections you choose in the Template section.
There will be section Summaries, and you will be able to see, for example alert counts by alert type:

Passive Scanning
ZAP automatically performs Passive Scanning in the background thread by scanning all HTTP requests and responses. It doesn’t change the requests or the responses in any way.
Passive Scan Report Rules define what kind of vulnerabilities to check in the background.
To check out the Passive Scan Rules list, go to Tools > Options > Passive Scan Rules

Check out the list! Here you can also manage how ZAP will perform the scan – you can choose the threshold of all vulnerabilities. A Passive Scanner is also an option where you can set up the

All options can be seen in the picture, and you can manage if the scan will be performed just for some specific scope, the maximum number of alerts, etc. For more information about passive scan options, you can check out this site.
There is also a useful option called Passive Scan Tags. To read more about it you can visit this site.
Active Scanning
Active scanning attempts to find potential vulnerabilities by using known attacks against the selected targets – by OWASP.
*Note that logical vulnerabilities such as broken access control will not be found! And if you want to have better results, manual penetration testing should always be performed in addition.
Active Scan Rules define what kind of vulnerabilities to check for when attacking an application.
To check out the Active Scan Rules feature, go to Tools > Options > Active Scan.
The Active scan will include the following vulnerabilities: .htaccess information leak, Code injection, Command injection, XSS, directory browsing (can lead to directory traversal attack), SQL injection, etc. Also, you can set up a custom policy you want to use when active scanning. Policies will be explained in the next chapter.
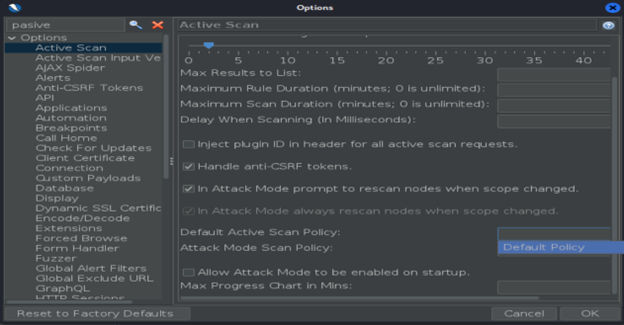
You can read more about passive scan options on this site. To determine what will ZAP attack, you can check out option Active Scan Input Vectors:

Scan Policy Manager
I have mentioned Scan Policy Manager, but what is it?
Scan Policy defines which rules will be run as part of an active scan, how many requests are to be made, and how likely potential issues will be flagged. There is no limit to defining the number of scan policies. Also, as you saw, you can define the default policy to be used for active scans and the attack mode.
To configure policies, go to Analyze tab > Scan Policy Manager, where you can Add, Modify, Remove, and Import/Export policies.

If you want to add a new policy, you can configure it easily. For example, if for your active scan you would like to perform the scan to check out CRLF Injection, you will go to Injection Section and under CRLF Injection, choose Threshold High, and for other injections, choose OFF.

When you finish with the setup, if you would like to perform an active scan with the newly created policy, you can do it like this:

Then click on the Active Scan, choose a policy, and Start Scan!

Conclusion
This is the end of the ZAP short series!
There are plenty of tutorials for using ZAP, and there is the official documentation on the OWASP site you can check out for more better understanding of this tool.
I also wanted to mention that ZAP has some free features that are not free in other security tools, such as Burp Suite. So, familiarize yourself with the pros and cons of security tools you can use before you start. You can and should always use more security tools along with manual testing if you want to get the best results.
Enjoy your ZAP ride!
#ZAP #Sessions #Pasive_scanning #Active_scanning
Cover photo by Markus Winkler
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About VRX
VRX is a consolidated vulnerability management platform that protects assets in real time. Its rich, integrated features efficiently pinpoint and remediate the largest risks to your cyber infrastructure. Resolve the most pressing threats with efficient automation features and precise contextual analysis.