- ESET Research discovered two previously unknown backdoors — which we named LunarWeb and LunarMail — compromising a European ministry of foreign affairs and its diplomatic missions abroad, primarily in the Middle East.
- ESET researchers attribute these compromises with medium confidence to the infamous Russia-aligned cyberespionage group Turla. The aim of the campaign is cyberespionage.
- Turla, also known as Snake, has been active since at least 2004, possibly even dating back to the late 1990s. It is believed to be part of the Russian FSB.
- ESET believes that the Lunar toolset has been in use since at least 2020.
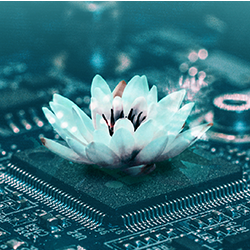
- Both backdoors employ steganography, a technique in which commands are hidden in images to avoid detection.
Illustration of an exfiltration email with data hidden in the image
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About ESET
For 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give individuals and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D facilities worldwide, ESET became the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single “in-the-wild” malware without interruption since 2003.