Intro
We all know what phishing is and how prevalent it is. This is the attack that accounted for more than 80% in 2021! More details can be found here and here.
With such scary numbers, it is an attack vector that warrants our attention. As we know, the security at our company is only as strong as our weakest link, and unfortunately, this is how threat actors leverage phishing attacks against us.
You can have all controls in the world, but you can still get phished; it is virtually impossible to implement an anti-phishing solution that will cover all the bases. Yes, you can have safe links, and a myriad of other controls, but that user interaction that’s at the core of this attack is how you get exploited and it’s just too difficult to account for. There are many tools out there that will do filtering for you (and whatever else), however these emails still can (and probably will) get through. You need to know what to do when that (inevitably) happens.
This all goes to say how important our education and cyber awareness in the organization are since we can be sure that we will eventually get targeted by one of these attacks.
My goal in this series is to look at and explain how a phishing attack works and how to analyse a phishing email. I will only explain some of the most important things briefly in this article. In the upcoming article, I will dive into the technical aspects of the attack.
Some Historical Context
Phishing and Spam are extremely common social engineering attacks, and not that new at all. First spam message dates all the way back to 1978 – you can read more about that here.
In the 4+ decades this attack has existed, threat actors have found creative ways to perfect it, and we’re all witnessing the results of that effort. As mentioned above, phishing is how 80% of breaches had started in 2021. We can’t know with certainty, but don’t expect this attack to fall out of favor. It is just too convenient for the attacker to at least try and phish the unsuspecting employee.
After obtaining those credentials, they’re off to the races.
Types of Phishing Attacks
Below are listed some of the phishing attack variants:
- Phishing – Emails sent to the target, appearing to be from a legitimate source with the goal to obtain sensitive information
- Vishing – Attack that’s based on calling the target on their mobile phone. Same logic and goal as for the regular phishing email
- Smishing – Same as vishing, with the difference being the attacker is now sending specifically crafted SMS messages to their targets
- Spear phishing – As phishing, but targeted at a specific individual or organization
- Whaling – As spear phishing but targeted at C-level executives. Also known as CEO Fraud
- Spam – Sending of unsolicited emails in bulk to a large group of people
The MO here is almost the same for every variant, even though they might leverage different methods.
Typical Phishing Email
A typical phishing email will have some (or all) of these characteristics:
- Urgency – Almost invariably, the email will be urgent in one way or the other; be it your ‘reward’ that you just got (you claiming it would be on a timer/urgent), or be it something you need to pay to avoid penalty. It will call you to action, hoping you would react immediately
- Bad grammar/spelling – This one is quite common and is oftentimes a really good indicator. Most of the phishing attacks will have small grammar/spelling errors within the email. Read through everything carefully. Of course, if an email is written perfectly, it can still be a phishing email
- Mismatched domains – Email is claiming to be from one company (domain) but it is actually sent from gmail.com or another domain. Misspelling is also sometimes use to hide the illegitimate domain by tricking you into thinking the domain’s good. Example: rnicrosoft.com, google.cm, g0ogle.com, etc. also known as Typosquatting – more on that here
- Suscpicious links/attachements – Unsolicited attachements are sent to you in an email, probably also prompting you to act on them.
- The sender email address will act and try to appear as a trusted entity – email spoofing
- The body of the email uses generic addressing such as Dear Sir/Madam, etc.
- Hyperlinks – oftentimes shortened with URL shortening services so it can hide its true purpose; don’t click on these! Hover over them to see the destination
- The body of the email is crafted in such a way that it matches a trusted entity (Google, Microsoft, for example)
This is very important to note. There are some good examples out there that illustrate the above nicely, while giving you a practical on the topic. Most companies will use similar stuff when training their employees (most likely with an internal mock phishing test). To see how you fare, you can try the quiz here.
Of course, even if we’re mindful of the above, human error can occur, so you should always pay extra attention when an unknown email pops in your inbox.
How does an Email Travel
Upon hitting SEND in your favorite email client app, there’s a lot of stuff that happens behind the curtains for your email to arrive at its destination. Three protocols are involved in this: POP3, IMAP, and SMTP.
POP3 – Post Office Protocol – receiving emails, downloading from the server
SMTP – Simple Mail Transfer Protocol – handles the sending of the emails
IMTP – Internet Message Access Protocol – stores messages on the server and syncs them across multiple devices
Slightly longer explanation can be found in this article:
IMAP:
Emails are stored on the server (meaning they can also be downloaded on multiple devices)
Sent emails are stored on the server
Messages can be synced and accessed from multiple devices
POP3:
Emails are downloaded (and stored) on a single device
Sent emails are stored on a single device, from which the email was sent
To keep messages on the server you need to enable “Keep email on server” option, because all the emails would be deleted from the server, once downloaded to the single device
Emails can only be accessed from a single device (where they were downloaded to)
SMTP:
By using SMTP, you’re sending, relaying, or forwarding messages from an email client (thinks MS Outlook) to a receiving email server
Explained here.
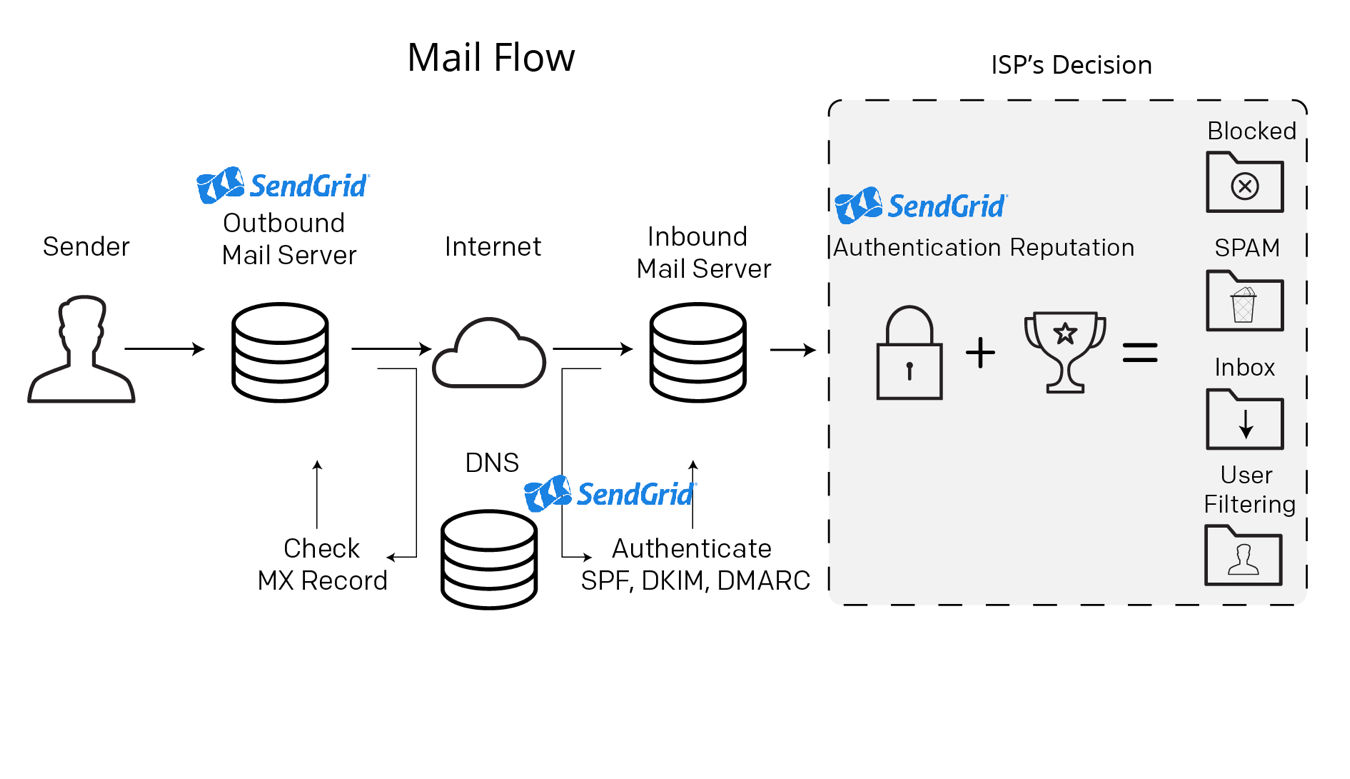
Lastly, to summarize, an email travelling would look something like this:
- You hit send within your email client after composing the message, sending it to someone@example.com
- The SMTP queries the DNS for records about example.com
- The DNS server fetches information about example.com and sends it to the SMTP server
- The SMTP server sends the email to someone’s mailbox at example.com
- The email goes through many SMTP servers before being relayed to the destination SMTP server
- Upon reaching the destination SMTP server your email is forwarded and waits in the local POP3/IMAP server waiting on someone
- Someone logs in to their email clients
- Their email client queries the local POP3/IMAP server for new emails
- Your email is copied (IMAP) or downloaded (POP3) to someone’s email client
This is nicely explained here, where you can also find the diagram shown below.
Here you can read more about these three protocols.
Default (un)encrypted ports for these protocols are:
POP3 – (110)995
IMAP – (143)993
SMTP – (25)587/465
Conclusion
Okay, so I talked a bit about phishing, how scary (real) it is, how an email travels, and I mentioned the variants of phishing attacks.
Before concluding, I’d like to emphasize again how important it is to understand/have some plan prepared against phishing as it is the best way attackers gain access, which in turn leads to some real ugly stuff. Prime example is ransomware, which is the most common way in which a ‘simple’ phishing attack evolves. (You can read more about it here, here, and here)
Finally, to let you go on a very dark note, please remember that phishing kits can be bought online quite easily, and that launching a phishing campaign can be done by someone less technical while the true danger remains; what comes after the attack i.e., what was it used for. They might be less effective, true, but it is scary to think that it can be done in that way with so little effort – in comparison to the impact the attack can have.
Stay tuned for the next piece where I’ll be talking about header and body analysis, and more!
Cover by Mohamed Hassan
#phishing #smtp #pop3 #imap #vicarius_blog
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About VRX
VRX is a consolidated vulnerability management platform that protects assets in real time. Its rich, integrated features efficiently pinpoint and remediate the largest risks to your cyber infrastructure. Resolve the most pressing threats with efficient automation features and precise contextual analysis.