Summary: Learn how Traceloop locked down AWS access, passed SOC 2 compliance, and saved hours with NordLayer’s dedicated IP.
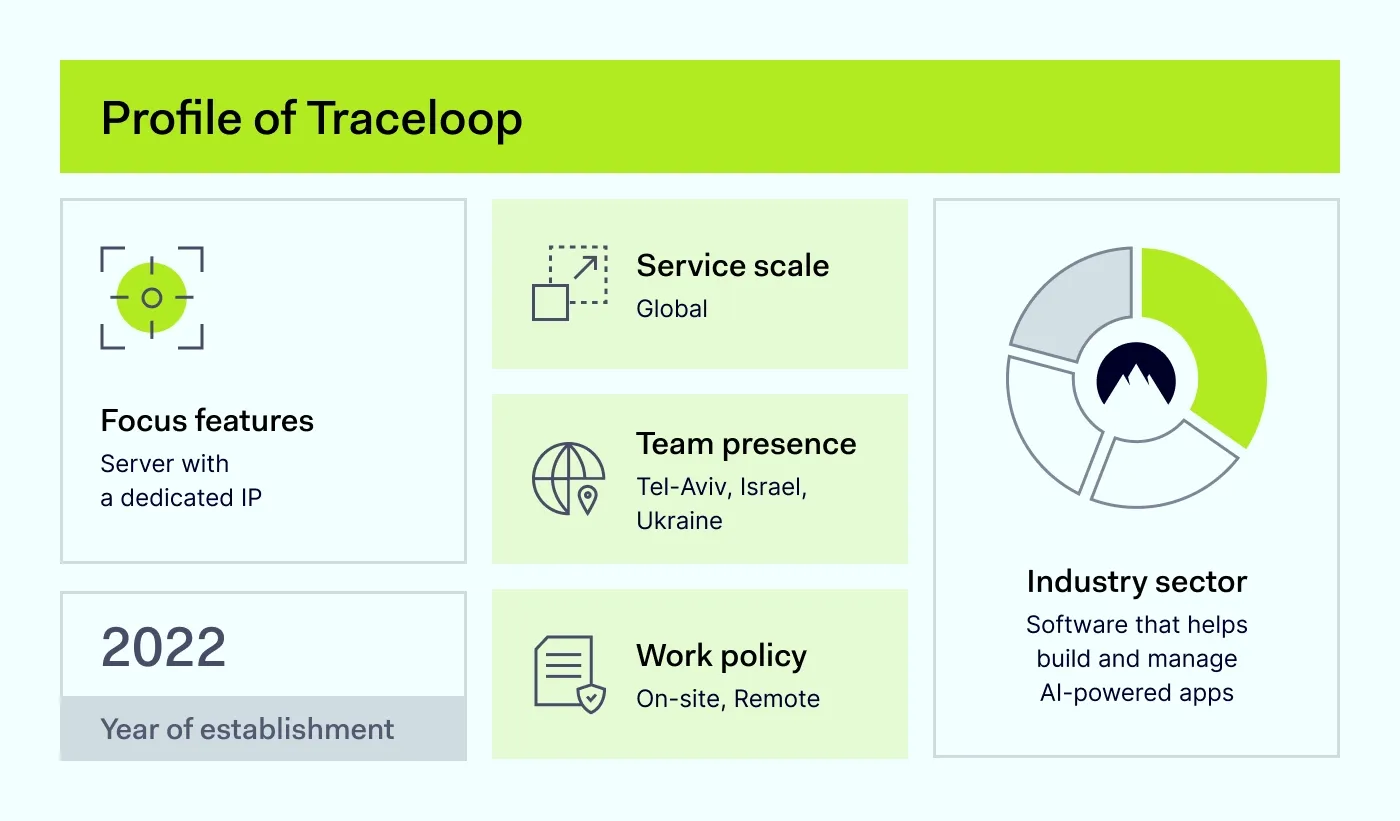
Established in 2022, Traceloop is a seed-stage startup based in Israel. It creates platforms that help companies worldwide build and improve their large language model (LLM) apps. The team consists of eight on-site employees and one remote worker based in Ukraine.
Before NordLayer, Traceloop didn’t have any security solution in place. And like many early-stage startups, its team focused exclusively on building products.
Knowing that their SOC 2 compliance audit was fast approaching, they needed a reliable and scalable solution that:
- Helps secure access to their AWS-managed Kubernetes clusters
- Supports SOC 2 compliance
The challenge: Securing access to DevOps environments
We spoke with Gal Kleinman, CTO and co-founder of Traceloop, about when security became a priority.
“We’ve always cared about security, but SOC 2 made us realize we needed tighter access controls to our cloud environments.”
The biggest issue was that their Kubernetes clusters were accessible from anywhere using AWS Command Line Interface (CLI), with no IP restrictions. Manually restricting access would’ve slowed down the team and introduced bottlenecks for developers.
They needed a solution that offers a server with a dedicated IP, works seamlessly with AWS, and could be set up in minutes, not days.
How NordLayer helped Traceloop
Traceloop needed a fast, reliable way to secure access to its cloud environments without adding unnecessary cost or complexity. As Gal Kleinman explains:
“With NordLayer, our team can now securely access our cloud resources, and I don’t have to spend much time managing it.”
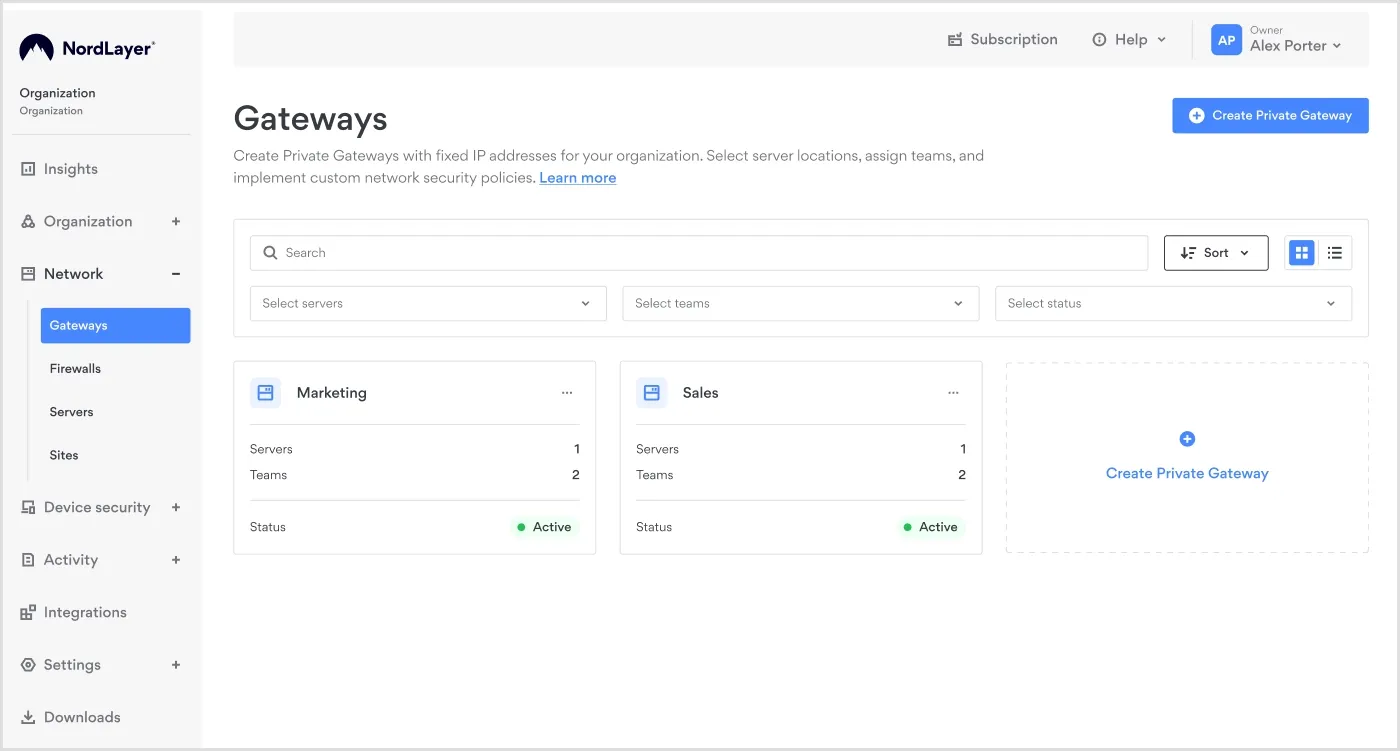
Traceloop deployed NordLayer’s server with a dedicated IP, which was assigned to the company through a Virtual Private Gateway.
Benefit 1: Fast NordLayer’s deployment
Traceloop was looking for a solution that was easy to use and set up. NordLayer’s deployment was simple:
- Log in to NordLayer.
- Invite the team members.
- They click the link, download the app, and it installs automatically.
- Within minutes, they’re securely connected.
“Everything took four or five minutes—start to finish.”
Benefit 2: Secure cloud access with a dedicated IP
To secure AWS access and meet SOC 2 compliance, Traceloop assigned a server with a dedicated IP to the Virtual Private Gateway. This ensured the whole team could connect through the same IP address, regardless of where they were.
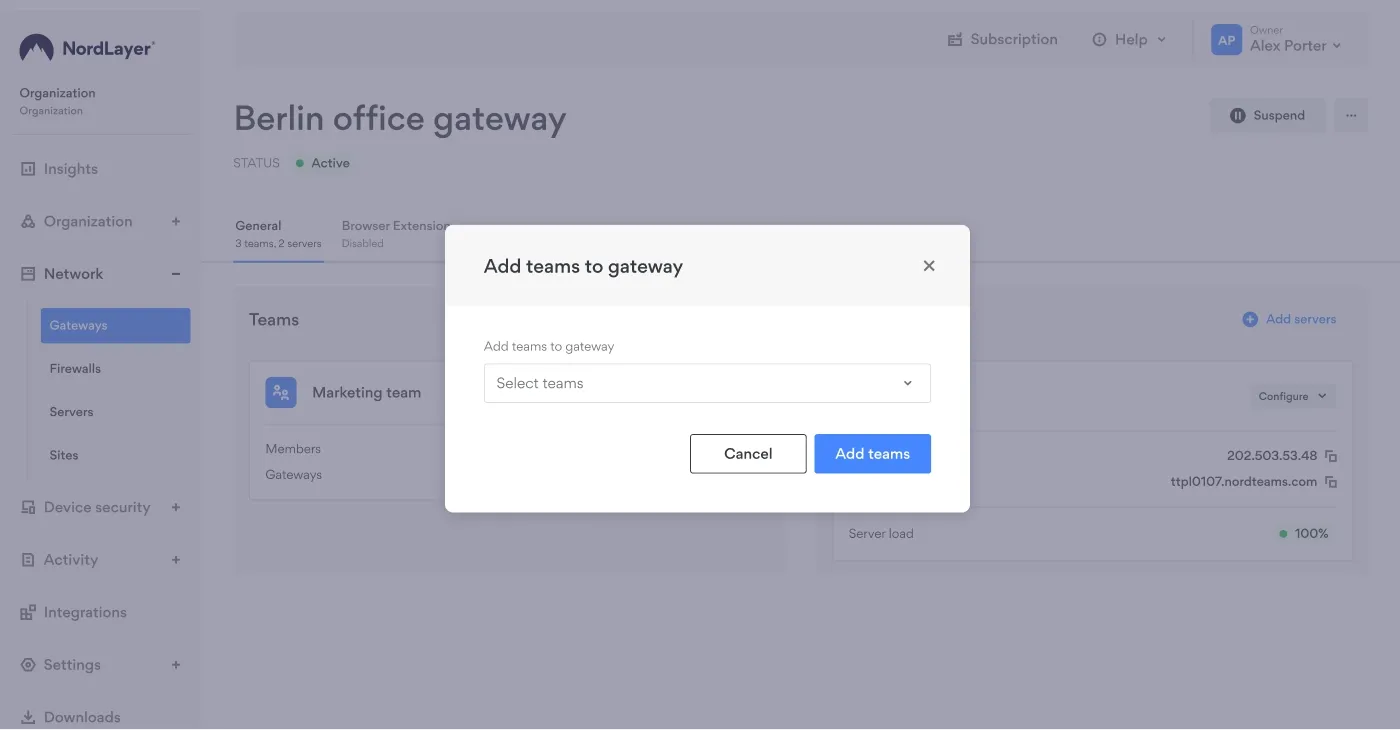
For a small team managing security themselves, this simplicity was a huge benefit. Setup was fast and straightforward. And they met all SOC 2 requirements without disrupting workflows or slowing down product development.
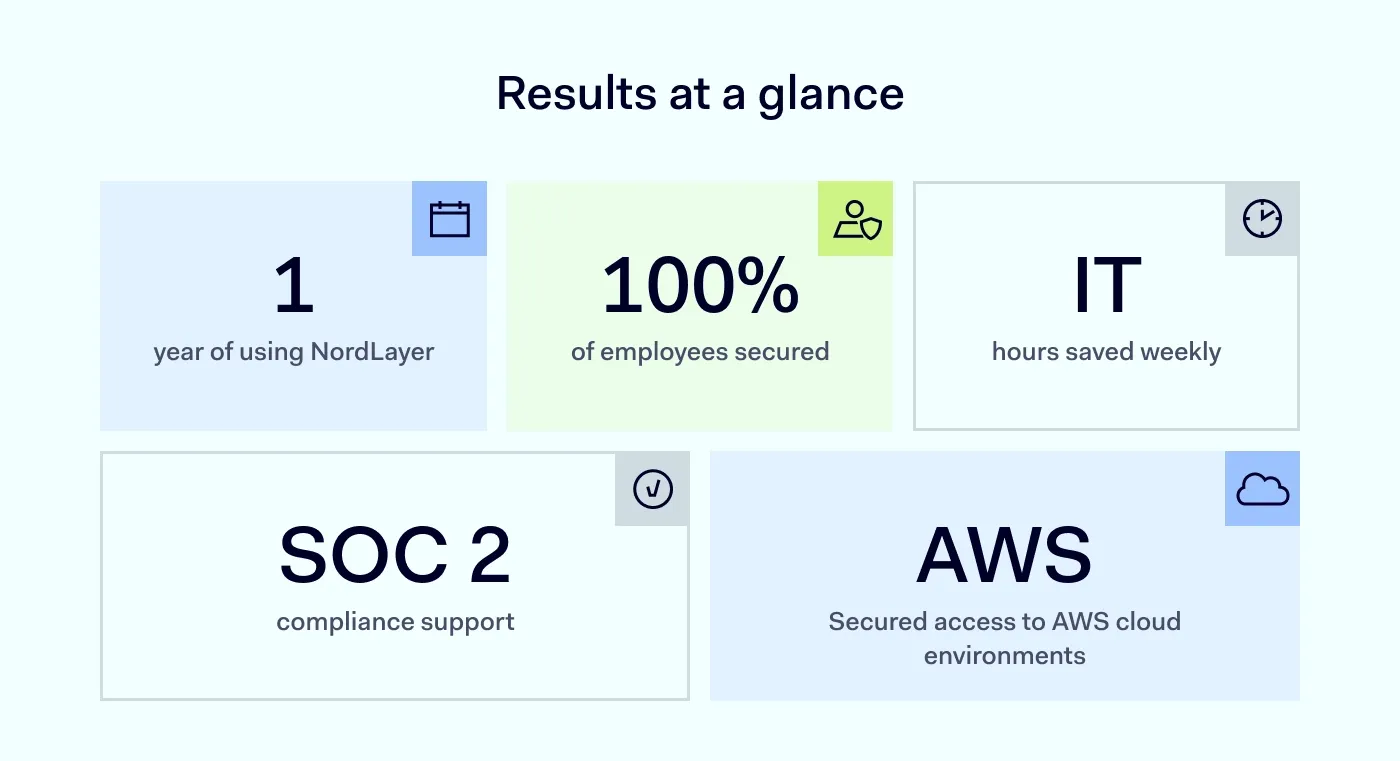
Results
After one year of using NordLayer, Traceloop achieved the following results:
- Locked-down cloud access: Secure access to staging and production environments.
- SOC 2 compliance support: Fast, compliant access controls for audit readiness.
- Scales with the team: 8 out of 9 team members use NordLayer daily, and the setup is quick and effortless.
- Many IT hours saved: NordLayer is easy to use and streamlines Traceloop’s workflows.
“NordLayer gave us a simple way to secure AWS access with a dedicated IP. The whole team connects through the gateway, and I can control access without touching our workflows.”
Why NordLayer works for Traceloop
NordLayer was the perfect fit for Traceloop because it delivered exactly what the team needed: simplicity, security, and zero disruption to developer workflows.
As a small startup without a dedicated IT team, Traceloop needed a solution that just worked, right out of the box:
- Secure access with a dedicated IP. Locked down staging and production, eliminating open endpoints.
- Set-up in minutes. NordLayer was fully deployed in under five minutes.
- Works with existing tools. Integrated seamlessly with AWS Command Line Interface (CLI), so the team didn’t have to change how they work.
Pro cybersecurity tips
Gal Kleinman, CTO and co-founder of Traceloop, shared a few cybersecurity tips with us:
- Keep it simple. Choose security tools that are easy to implement and use. Avoid overcomplicated setups that drain time and energy.
- Protect without disrupting. Security measures should work quietly in the background, not block workflows or frustrate developers.
- Balance security and speed. The best tools protect your systems and let your team move fast.
Conclusion
Traceloop chose NordLayer to secure its AWS access and streamline SOC 2 compliance without disrupting the team’s daily work.
“NordLayer gave me exactly what I needed—a dedicated IP, fast setup, and no disruption to how our team works.”
With NordLayer, Traceloop gained secure cloud access and an easy way to scale security as the team grows.
Need to secure your cloud workflows without slowing your team down? Learn how NordLayer can help you with that.
Talk to our sales team to find the right plan for your team.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.