Key Takeaways for CISOs and IT Teams:
- Machine identities now outnumber humans 45 to 1—but most go unmanaged.
- SSL/TLS certificate lifespans will shrink to 47 days by 2029, making manual management unsustainable.
- 71% of breaches now start with stolen or misused credentials—including certificates and service accounts.
- Most teams fail audits due to poor machine identity visibility, ownership, and lifecycle control.
- This guide shows how to prevent outages, avoid audit risk, and automate before it’s too late.
When Microsoft Teams went dark for millions of users worldwide, the culprit wasn’t a sophisticated cyberattack or server failure. It was an expired SSL certificate. A simple piece of digital paperwork that nobody remembered to renew brought down one of the world’s most critical communication platforms.
This isn’t an isolated incident. It’s a glimpse into a massive security blind spot that’s hiding in plain sight across every enterprise network: machine identity management.
Why machine identities are the new security frontier
While your security team has spent years perfecting human identity management (multi-factor authentication, single sign-on, privileged access controls), an invisible workforce has been quietly multiplying in the background.
These are your machine identities: the digital certificates, API keys, and cryptographic tokens that authenticate servers, applications, and IoT devices.
Today, these non-human identities outnumber human employees by ratios as high as 45 to 1, and security leaders expect that number to grow by another 150% in the coming year.
When machine identities are compromised or mismanaged, the consequences range from data breaches that make headlines to outages that cost millions in lost revenue. Yet most organizations are still managing these critical credentials with the same manual processes they used a decade ago. That is, if they’re managing them at all.
What Is a Machine Identity?
Think of machine identity as the digital equivalent of a passport or driver’s license, but for software, devices, and automated systems. Just as humans prove their identity with credentials, machines authenticate themselves using digital certificates, cryptographic keys, API tokens, and other secrets.
A “machine” in this context isn’t limited to physical hardware. It encompasses any non-human entity in your digital ecosystem: servers, virtual machines, containers, microservices, APIs, databases, applications, IoT sensors, and even AI models.
Each requires some form of identifier and credential to establish trust with other systems. Common forms of machine identity include:
- X.509 certificates for establishing encrypted HTTPS connections
- API keys that authenticate applications to cloud services
- SSH keys for secure server access and file transfers
- Service account credentials that enable applications to access databases
- OAuth tokens for secure API communications
- Session-based credentials for Agentic AI acting on behalf of users across SaaS platforms or browser environments
- Access tokens used in autonomous workflows and machine-to-machine actions
When you visit a website and see the HTTPS padlock, you’re witnessing machine identity in action. The server presents a digital certificate proving its legitimacy before your browser trusts it with sensitive data. This same principle scales across your entire infrastructure. Every service-to-service connection should verify identity before exchanging information.
The challenge lies in the explosive growth of these digital credentials. The growing trend of decentralization is disrupting cybersecurity oversight, with 75% of employees expected to acquire or modify tech outside IT’s control by 2027.
Each new application, microservice, or automated process adds more machine identities to manage, creating complexity that manual processes simply cannot handle.
The Hidden Risks of Unmanaged Machine Identities
Overlooking machine identities creates serious business risks that extend far beyond IT operations. When these credentials are compromised or mismanaged, the consequences ripple through your entire organization.
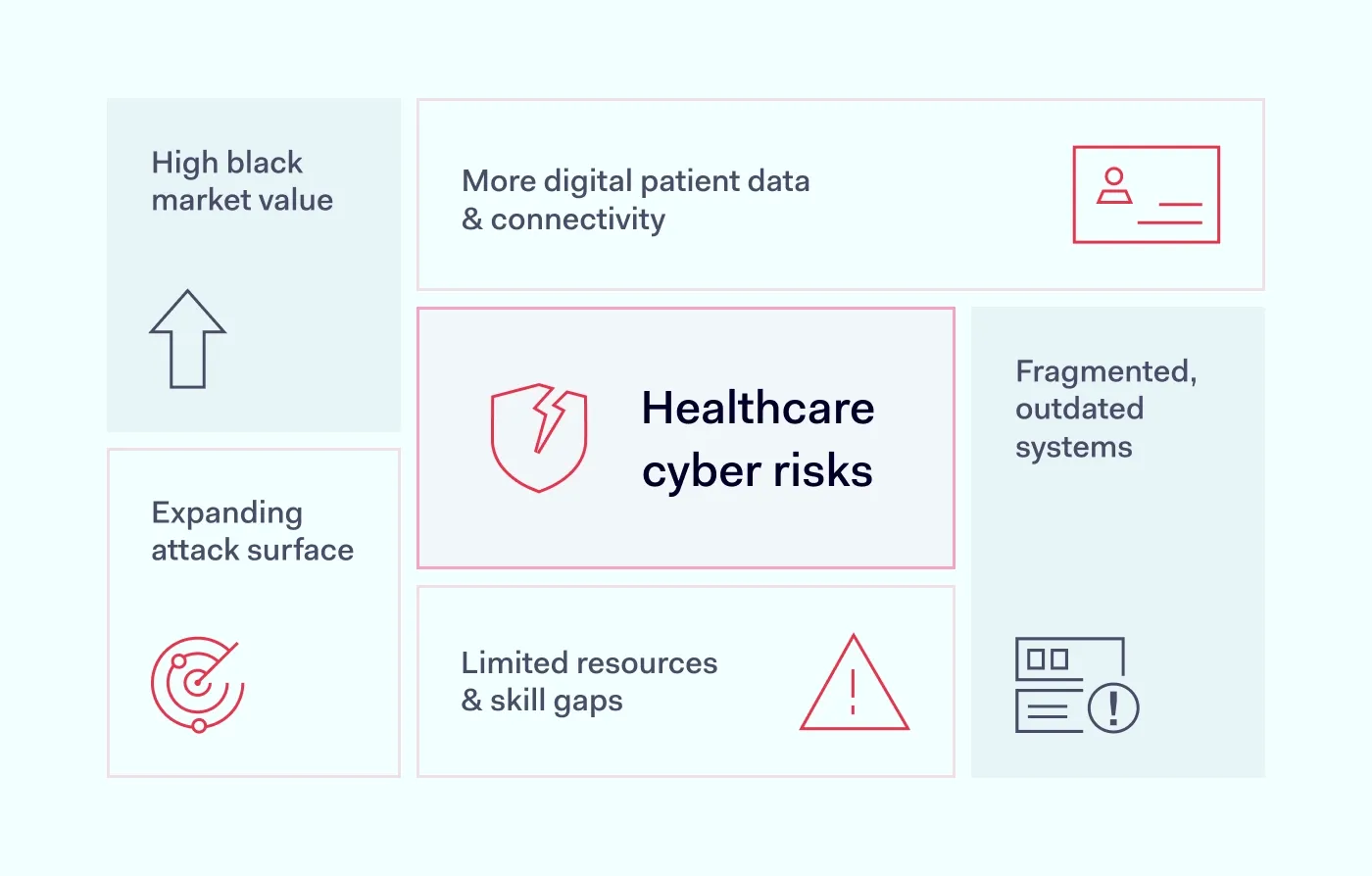
Breach Enablement Through Credential Compromise
Attackers are increasingly using machine credentials as entry points, and breaches that start with stolen or compromised credentials have seen a 71% year-over-year rise.
When attackers compromise a machine identity, they effectively “become” a trusted system within your network. This grants them the ability to move laterally, access sensitive data, and establish persistent footholds without triggering traditional security alerts.
Unlike human accounts that often show suspicious behavior, compromised machine credentials can act normally while exfiltrating data or preparing attacks unnoticed.
The SolarWinds supply chain attack is perhaps the most stark example of this threat. Hackers misused digital certificates to impersonate trusted software updates, making malware appear legitimate and bypassing security controls. As a result, they got access to over 18,000 organizations around the world.
The Washington Post described the attack as “the computer network equivalent of sneaking into the State Department and printing perfectly forged U.S. passports.”
Operational Disruptions and Revenue Loss
Certificate-related outages represent one of the most common yet preventable causes of business disruption. In addition to creating headaches for IT, they lead to lost revenue, customer frustration, and reputational damage.
Studies indicate that a single expired certificate outage can cost large organizations millions in recovery efforts and business impact.
The root cause often stems from a lack of visibility: teams simply don’t know where certificates are deployed or when they’re set to expire.
Now, the challenge is about to get harder. Starting in March 2026, the maximum validity period for public SSL/TLS certificates will drop from 398 days to 200 days, and by 2029, that window will shrink to just 47 days. This change—driven by industry mandates—will require certificates to be renewed up to 8 times a year. Manual management won’t scale. Without automation, organizations risk facing a flood of avoidable outages, compliance failures, and exposure from stale or expired credentials.
As your infrastructure grows more dynamic—with containers, microservices, and agentic AI adding complexity—automated certificate lifecycle management is no longer optional. It’s foundational.
Compliance and Governance Gaps
When organizations can’t inventory or secure their machine credentials, they risk failing audits and violating data protection requirements.
It’s particularly challenging because 88% of companies still treat “privileged user” as meaning humans only, even though about 42% of machine identities have sensitive or admin-level access. This creates a dangerous gap where powerful machine credentials operate without the oversight typically applied to privileged human accounts.
Cyber insurers and regulators are beginning to scrutinize machine identity practices more closely. Organizations that can’t demonstrate proper credential management may face higher insurance premiums, regulatory penalties, or exclusion from certain contracts requiring security certifications.
How Machine Identities Enable Modern Security Initiatives
Securing machine identities is a powerful enabler of transformative security and business initiatives. When properly managed, machine identities become the backbone of Zero Trust architectures, cloud-native development, and DevOps automation.
Zero Trust Security: “Never Trust, Always Verify” for Machines
Zero Trust security models require verification for every access request, whether from humans or machines. The principle “validate every machine’s identity irrespective of its location” ensures that malicious devices or rogue microservices can’t exploit implicit trust relationships.
Machine identity management makes Zero Trust architectures possible by ensuring every API call and service-to-service connection presents valid credentials. No machine or workload receives implicit trust based on network location. Each must prove its identity at every interaction, similar to multi-factor authentication for users.
Implementing mutual TLS, where each service possesses its own certificate, is a good example of this approach. Services only communicate after both parties prove their identities, preventing attackers from exploiting unverified connections. Even if one service is compromised, attackers can’t impersonate other trusted machines across the network.
Cloud-Native Scaling and Microservices
Modern cloud architectures depend heavily on microservices, containers, and APIs, which are essentially fleets of machines that scale dynamically based on demand. Managing identities manually in this environment becomes impossible so you need automated machine identity solutions to secure growth at scale.
Companies like Netflix show the power of this approach. Netflix uses an internal machine identity framework based on SPIFFE/SPIRE (a set of open-source standards for service identity) to authenticate thousands of microservices in real time, ensuring secure service-to-service communication across its global infrastructure. This implementation resulted in a 60% reduction in security incidents within their microservices environment.
Similar to Netflix, companies with proper machine identity management can auto-scale services without sacrificing security. Every new instance automatically receives valid credentials, and every connection maintains encryption and verification.
This eliminates the traditional trade-off between agility and security, enabling developers to deploy rapid updates and connect to third-party APIs while maintaining least privilege access controls.
DevOps and Automation: Agility with Security
DevOps environments require automation to maintain both speed and safety. Machine identity management integrated into CI/CD pipelines automates the critical tasks of issuing, configuring, and rotating credentials for applications and infrastructure.
This automation prevents human errors that cause outages while accelerating deployment cycles. When a new microservice comes online during deployment, automated machine identity services immediately issue certificates and update trust stores, enabling secure communication from the start. No helpdesk tickets, no delays, no forgotten expiring certificates.
Strong machine identities also enable advanced practices like microsegmentation and fine-grained access control in orchestration platforms. Each service maintains its own credentials and operates within defined interaction boundaries, supporting both rapid development and robust security controls.
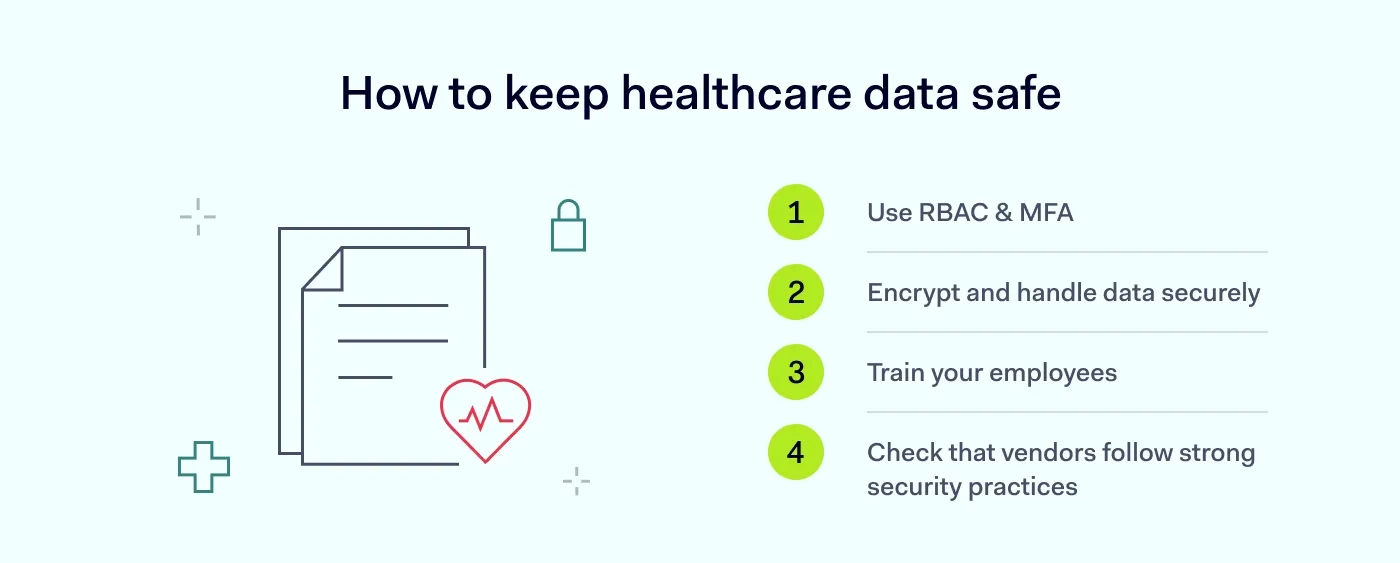
Best Practices for Securing Machine Identities
Implementing effective machine identity security requires a systematic approach that addresses discovery, automation, access control, and monitoring. These practices provide the foundation for managing machine identities at enterprise scale.
Maintain Comprehensive Inventory and Discovery
You cannot protect what you don’t know exists. Start by creating and maintaining an up-to-date inventory of all machine identities across your environment, whether it’s certificates, keys, API tokens, service accounts, and other credentials. Understand where each credential resides, which systems depend on it, and when it expires or requires renewal.
Many organizations discover hundreds or thousands of forgotten certificates and secrets scattered across cloud and on-premises systems during their first comprehensive audit. Continuous discovery tools can automatically scan networks and integrate with cloud platforms to enumerate these credentials, providing ongoing visibility as new identities are created.
Your inventory should classify privileged versus non-privileged machine accounts, helping you prioritize which credentials require enhanced security controls and monitoring.
Automate Credential Lifecycle Management
Given the volume and short lifespan of modern machine identities, manual management simply doesn’t scale. Automation becomes critical for handling issuance, renewal, and revocation of certificates and keys programmatically.
When new containers or virtual machines launch, automation tools should immediately provision appropriate credentials without human intervention. Implement regular rotation schedules for secrets and keys. Or even better, rotate after each use for highly sensitive credentials.
Automated workflows prevent outages by renewing certificates before expiration and ensure proper retirement of old credentials. These processes should integrate directly into your DevOps pipelines, creating a self-driving identity lifecycle where credentials are issued when needed, rotated frequently, and revoked instantly when suspicious activity occurs.
Enforce Least Privilege Access Controls
Apply the principle of least privilege to all machine identities with the same rigor used for human accounts. Audit the privileges of service accounts, API keys, and certificates to ensure they grant only the access each service actually needs.
If a microservice only needs to read from one database, its credentials shouldn’t allow write access to multiple systems. Too often, machine identities receive over-provisioned permissions or retain default high privileges that create attractive targets for attackers.
Bring machine identities into your Privileged Access Management (PAM) strategy. Vault their credentials, monitor their usage, and require additional verification for sensitive actions. Implement network segmentation based on machine roles, using firewall rules, service mesh policies, or cloud IAM to constrain what each identity can access.
Implement Continuous Monitoring and Response
Establish monitoring across multiple levels to detect misuse or anomalies in machine identity usage. Track certificate and key usage patterns and investigate when dormant certificates suddenly become active or API keys make calls from unusual locations.
Leverage analytics to baseline normal machine-to-machine communication patterns and generate alerts for deviations. Examples include surges in failed certificate authentications or service accounts accessing unusual resources.
Implement centralized logging for all authentication events, including mutual TLS handshakes and key usage, feeding this data into your SIEM platform. When suspicious activity occurs, have incident response playbooks ready to automatically revoke credentials or quarantine services until verification completes.
Regular testing of incident response procedures for machine identity compromise ensures your team can quickly remove or replace stolen credentials across systems, building cyber resilience through preparation and practice.
The Future: AI and Machine Identity Convergence
The relationship between AI and machine identity will evolve in two critical directions: protecting AI systems through robust machine identity controls and leveraging AI to enhance machine identity management capabilities.
Securing AI Through Machine Identity
81% of organizations now consider machine identity protection vital for safeguarding emerging AI and cloud initiatives. As AI-driven platforms become more common, they generate new types of machine identities that require protection. Sophisticated adversaries already target AI models and data, viewing machine credentials as keys to these valuable assets.
Malicious actors who can impersonate AI services or manipulate ML model API credentials could inject bad data, steal sensitive insights, or deploy rogue AI agents with elevated privileges. Protecting AI requires ensuring every automated agent, ML pipeline, and bot maintains a verifiable identity within defined access boundaries.
Future AI development frameworks will likely incorporate machine identity controls as standard practice. Things like digital signatures on AI model files, hardware-backed keys for computing environment verification, and Zero Trust principles applied to every algorithm and data feed.
AI-Enhanced Identity Management
The volume and velocity of machine identity data create perfect opportunities for AI and machine learning analytics. Next-generation identity platforms are beginning to incorporate “self-healing identity systems” that automatically adjust and repair themselves based on learned patterns.
AI engines monitoring certificates and keys could predict optimal renewal timing, automatically suspend credentials showing anomalous usage patterns, and generate replacement credentials to prevent service interruptions. These systems will optimize lifecycle management, finding ideal rotation frequencies based on risk profiles and performing predictive threat detection.
Behavioral analytics powered by AI will help differentiate normal machine behavior from malicious activity, similar to how User and Entity Behavior Analytics (UEBA) detects account takeovers.
This combination of robust machine identity practices with AI-assisted tools promises predictive, self-healing identity infrastructures that adapt at machine speed to protect against emerging threats.
Taking the First Step: Your Machine Identity Journey
The complexity of machine identity management shouldn’t prevent you from starting. Begin with an honest assessment of your current practices: How are certificates, keys, and service accounts currently handled? What visibility exists into machine credential lifecycles?
Conduct a thorough audit to uncover unknown certificates, hard-coded credentials in scripts, and legacy keys requiring rotation. This audit will make risks tangible to stakeholders while providing the foundation for improvement planning.
Create a roadmap that prioritizes quick wins like renewing near-expiry certificates, cleaning up orphaned credentials – all the while evaluating solutions for long-term automation and management. Engage cross-functional teams across security, IT, and DevOps, since success requires collaboration across these domains.
Frame this initiative as a strategic business move rather than a technical project. Emphasize positive outcomes: preventing costly breaches and downtime, enabling faster cloud deployments, and ensuring customer trust through robust security.
With leadership support, implement your machine identity management program iteratively. Start with automating certificate management in one infrastructure area, then expand coverage systematically.
Secure Your Machine Identities Today
Most teams don’t realize the risk until it’s too late. Machine identity security starts now with the right tools and a trusted partner. Segura® simplifies this transition, providing robust, ready-to-implement solutions like automated credential discovery, lifecycle management, and real-time monitoring that integrate seamlessly with your existing DevOps and cloud infrastructure.
Request a personalized demo of Segura® today.
Frequently Asked Questions About Machine Identity Management
What is a machine identity in cybersecurity?
A machine identity is any non-human credential—like a digital certificate, API key, or service account—that systems use to authenticate and communicate securely. These identities are critical for verifying trust between applications, servers, containers, and AI agents.
Why are machine identities a security risk?
Machine identities now outnumber human users by as much as 45 to 1. When they’re unmanaged or overprivileged, attackers can exploit them to move laterally, access sensitive data, and evade detection. Most breaches involving credentials start with a compromised machine identity.
What causes machine identity outages?
Most outages are caused by expired or misconfigured digital certificates. As certificate lifespans shrink to 90 days or less, manual tracking becomes nearly impossible. Without automation, teams risk system failures, compliance gaps, and reputational damage.
How do I prepare for audits involving machine credentials?
Auditors increasingly expect clear visibility, ownership, and lifecycle control of all credentials, including machine identities. You’ll need a current inventory, automated renewal policies, access controls, and logging. Solutions like Segura help teams surface risks and streamline reporting.
What’s the best way to manage machine identities at scale?
Use automated discovery and lifecycle management across certificates, keys, tokens, and service accounts. Integrate credential workflows into CI/CD pipelines. Enforce least privilege access. And continuously monitor for anomalies—especially across cloud, hybrid, and AI-enabled environments.