Navigating the landscape of remote work can be a complex task for businesses. A solid plan, grounded in real-world data and insights, is the cornerstone of a successful remote work strategy.
That’s where resources like the Global Remote Work Index (GRWI) come into play. This powerful tool compiles extensive data to provide a comprehensive view of remote work trends around the world. Gathering the insights helps companies craft effective and informed remote work policies.
In this article, we’ll guide you through using the index to develop a remote work policy that is both efficient and employee-friendly, ensuring that your team stays productive, connected, and content, no matter where they are working from.
Benefits and challenges of remote work—the need for a remote work strategy
Harnessing the benefits
Remote work, a transformative approach to traditional work environments, offers a wealth of benefits. It opens doors to a global talent pool, allowing companies to tap into diverse skills and perspectives. This approach fosters innovation and enhances the company’s adaptability in a rapidly evolving business landscape.
Flexibility is another remarkable advantage. It allows employees to create a work schedule that aligns with their most productive hours, improving overall work quality and output. Businesses can also reduce expenses, saving on office space and other associated costs, allowing for redistributing resources towards growth and development initiatives.
Facing the challenges
Despite its numerous benefits, remote work also presents challenges that businesses must navigate diligently. One of the primary concerns is maintaining consistent communication and collaboration among team members. The absence of a physical office can sometimes lead to feelings of isolation and disconnection, potentially impacting team synergy and morale.
Data security is also paramount. Protecting sensitive information becomes more complex when employees work from various locations, requiring robust cybersecurity measures and policies to prevent unauthorized access and data breaches.
The crucial role of a remote work strategy
Considering these factors, the need for a well-rounded remote work strategy becomes clear. Such a strategy should optimize the benefits while effectively addressing the challenges. Utilizing comprehensive resources like the Global Remote Work Index can be instrumental in this regard, offering critical insights for informed policy-making.
A successful strategy should encompass clear communication guidelines, ensuring that team members can collaborate seamlessly and maintain a sense of community. Implementing reliable tech tools and platforms to facilitate communication and project management is crucial.
Moreover, it’s essential to establish cybersecurity protocols to safeguard company data, including secure access systems and regular employee training on cybersecurity best practices.
By adopting a thoughtful and strategic approach, businesses can create a remote work policy that maximizes productivity and innovation while fostering a supportive and secure virtual work environment.
Setting clear objectives for a remote work strategy with GRWI
The GRWI is an invaluable tool that offers insights to refine and optimize remote work policies. Here’s a look at how leveraging the index can guide businesses in setting clear and impactful objectives.
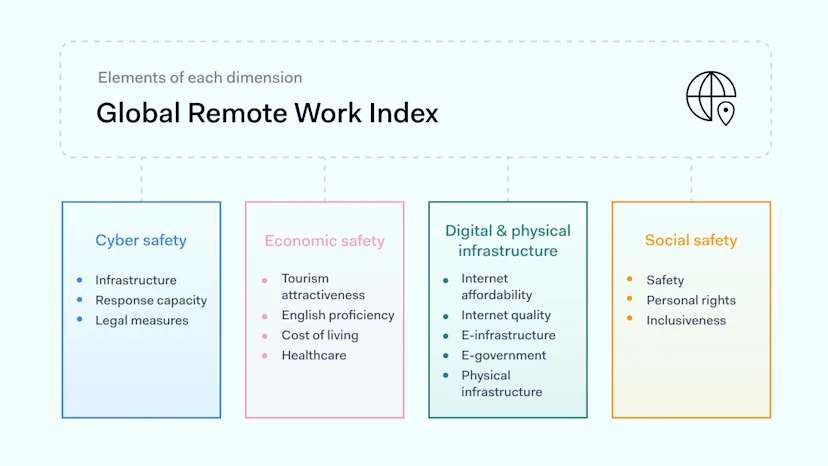
The full methodology and data sources guide through the layers of the GRWI tool, explicitly showcasing the criteria to consider.
Accessing a broader talent pool
The GRWI presents a nuanced perspective that helps organizations tap into a broader talent pool, which is vital for cultivating innovation and global competitiveness.
The index evaluates the prevalence of individuals using the internet. Categorically, it’s placed under the e-infrastructure rank that is part of the digital and physical infrastructure dimension. This data is paramount as it provides insights into digital connectivity and accessibility in society in various regions, a necessity for remote work.
Another significant component integrated within the GRWI is English proficiency within the economic safety dimension. English, often called the global business language, is vital for widening the talent acquisition spectrum. Proficiency in English allows organizations to communicate seamlessly, ensuring that language barriers do not restrict collaborative productivity and innovation.
The GRWI also includes the e-government ranking from the digital and physical infrastructure dimension. It emphasizes the significance of digital public services in facilitating remote work. This provides insight into the digital advancement of governmental operations, reflecting a region’s overall digital maturity, which is important for foreign business integration.
By analyzing these crucial elements, organizations can strategically expand their workforce, ensuring access to diverse talents and skills essential for driving organizational success in a digitally connected global landscape.
Boosting productivity
In crafting a policy that optimizes productivity in a remote work setting, the GRWI offers essential insights by analyzing various crucial metrics.
One key area is the quality of the internet, nestled within the digital and physical infrastructure dimension. A reliable and robust internet connection is the backbone of effective remote work, enabling seamless communication, access to information, and use of productivity tools and applications, ultimately reducing downtime and frustration caused by connectivity issues.
GRWI’s focus on cyber incident response, categorized under the cyber safety dimension, helps assess the right country for remote work. A strong stance on cyber safety, reflected by a region’s ability to swiftly and effectively respond to cyber incidents, ensures uninterrupted workflow by safeguarding organizational and employee data.
Including the ICT (Information and Communication Technology) adoption index as part of the e-infrastructure score (the digital and physical infrastructure dimension) embraces the technology that bolsters productivity. This metric sheds light on how deeply integrated technology is within a region, pointing to the availability and use of tech tools that facilitate smoother and more efficient remote working experiences.
Blending these elements provides an instrumental viewpoint for organizations aiming to amplify productivity in a remote work environment. Companies can use this data to design policies that mitigate challenges, using technological infrastructure and cybersecurity measures to cultivate a productive, resilient, and secure remote workforce.
Reducing costs
Harnessing the data provided by the GRWI, organizations can strategically navigate towards cost-efficiency in their remote work policies. The index integrates several key elements crucial in this aspect.
A prime component is internet affordability, located within the digital and physical infrastructure dimension. This metric is essential because it allows organizations to assess the financial feasibility of remote operations in various regions, ensuring that employees can access stable internet connections without excessive costs, thus maintaining organizational expenditure at reasonable levels.
Next in line is the co-working space density per capita rank, also encapsulated within the digital and physical infrastructure dimension. A higher density indicates more options and potentially lower costs for securing suitable, professional working environments for remote employees, especially those lacking a conducive home office setup.
The cost of living, placed under the economic safety dimension, is another fundamental component. This data helps organizations gauge the general affordability aspect of different locations, enabling a clearer view for determining compensations and other allowances, ensuring that employees can maintain a decent standard of living without causing organizational costs to skyrocket
With these elements, organizations can compose a pragmatic perspective for shaping remote work policies that are both effective and economically sound. By using the GRWI data, organizations are better equipped to steer their remote work strategies towards enhanced cost-efficiency, making informed decisions that align with both organizational and employee financial well-being.
Improving work-life balance
Using the GRWI can be a game-changer in cultivating a remote work policy that enhances work-life balance. The index combines various indicators that can be instrumental in fostering a more balanced and enriching remote work experience.
Consideration of the tourist attractiveness of a location as part of the economic safety dimension provides insights into the livability and allure of different regions. For remote workers, residing in a location with a high tourist attractiveness score can enhance the quality of life outside of work, providing multiple options for leisure, exploration, and relaxation, contributing positively to work-life balance.
The healthcare rank, another data point under the economic safety dimension, contributes significantly to determining the suitability of a location for remote work. A robust healthcare system is crucial in ensuring the well-being of remote workers, providing accessibility to quality medical services, and promoting a healthy lifestyle, which is essential for productivity and job satisfaction.
Inclusiveness, found in the social safety dimension, focuses on social cohesion and equality within a region. An inclusive environment helps facilitate a sense of belonging and community among remote workers, mitigating feelings of isolation and enhancing overall life satisfaction.
By prioritizing these aspects, organizations can facilitate a remote work experience that is not only productive but also conducive to their workforce’s overall well-being and happiness.
Putting the GRWI tool into action: a how-to guide
The index has a number of layers that can be used to gain reliable insights and develop an effective remote work strategy.
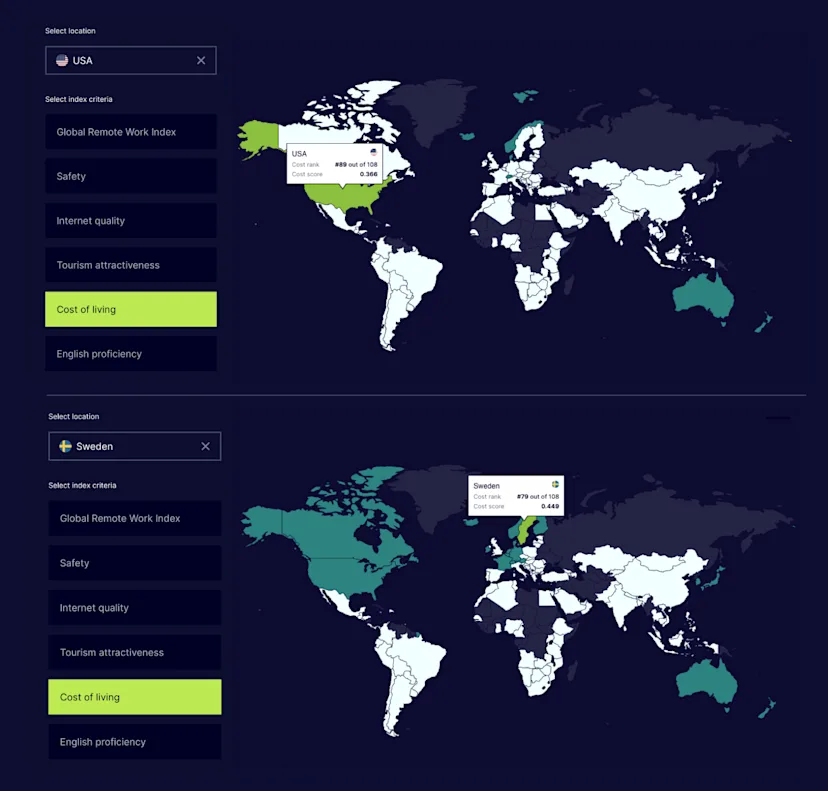
Let’s say a company wants to hire people from another country to help maintain the organization’s low expenses. We established that looking at internet affordability, co-working space availability, and the cost of living is beneficial to keep costs down.
All these elements derive from economic safety and physical and digital safety dimensions, so this is where we need to focus:
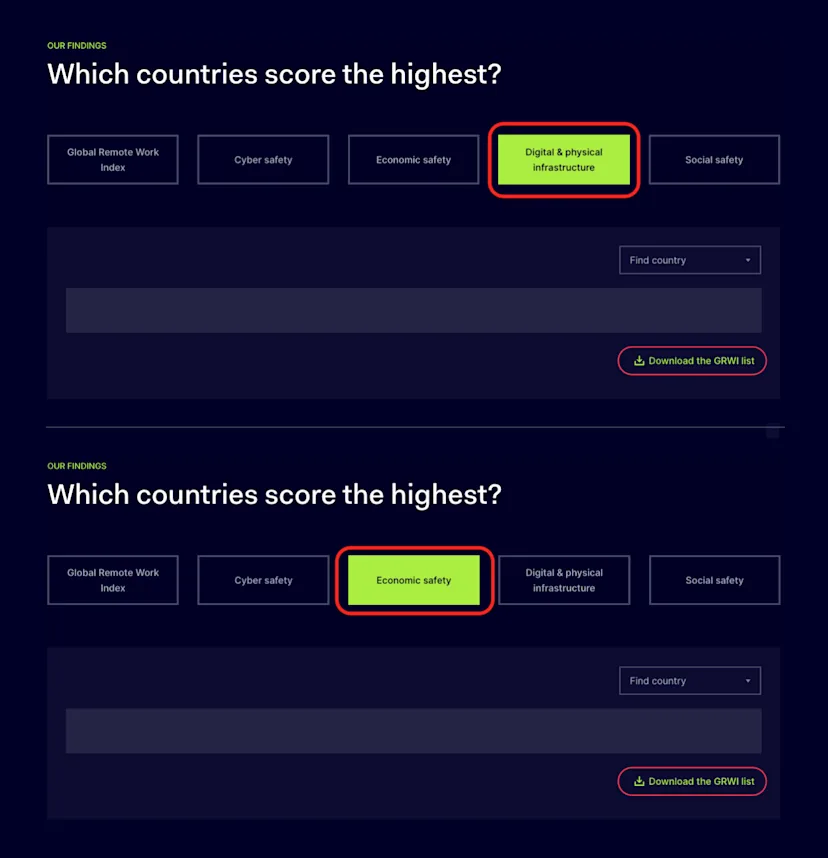
Since GRWI incorporates data from 108 countries, consolidating the Top 10 countries of each dimension will reduce the scope:
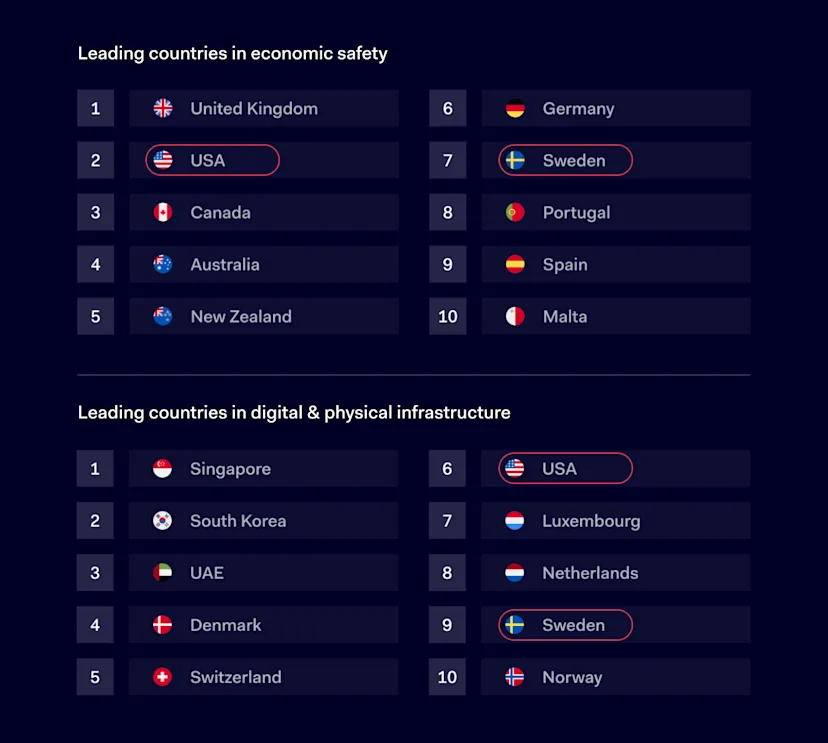
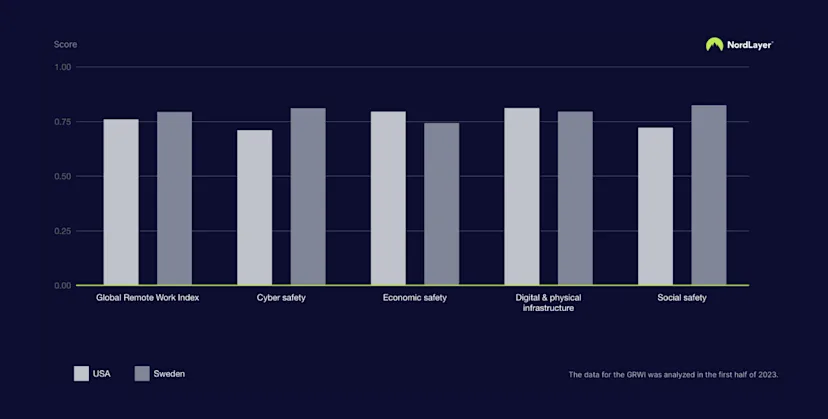
We get two perfect matches on these lists—the United States and Sweden. To select the final candidate by evaluating its overall score, we need to compare them on all different dimensions:
To make a more detailed decision, you can browse additional criteria to gather in-depth insights, for example, such as the country’s English proficiency or safety rankings:
Now you’re able to create insights from gathered information. The GRWI tool provides users with options to explore data from different perspectives, so take your time using it.
Make GRWI your insights asset
The Global Remote Work Index acts as a compass, guiding businesses in crafting remote work policies that are both efficient and empathetic. By setting clear objectives focused on work-life balance, cost reduction, talent acquisition, and productivity enhancement, organizations can unlock the full potential of remote work for success and sustainability.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.