Summary: Virtual private clouds and private clouds differ in cost, flexibility, and security, helping you choose the best option for your organization.
Private or public? Virtual or local? Cloud deployments come in many varieties. Choosing the right model is critical to performance, ease of use, cost, and security.
This article discusses the two main private cloud solutions: virtual private cloud and private cloud models. Each deployment type has strengths and potential drawbacks. Choosing the right type influences security, cost, and performance. It’s an important decision.
What are the two types of private cloud, and which one should you choose? This article will explain everything you need to know.
What is a virtual private cloud?
A virtual private cloud (VPC) is a virtualized multi-tenant cloud deployment hosted on public cloud infrastructure.
A cloud provider sells public cloud space, and users apply logical segmentation to create a virtual network. This separates the VPC from other resources without needing extra hardware or separate server space.
After that, the VPC functions like a private cloud domain. Users can install applications, create data storage containers, and manage cloud computing as needed.
Virtual private cloud users determine internal routing via IP address subnetting and network access control lists (NACLs). Network gateways enable secure connections from external resources. Users can also connect many VPCs via VPC peering.
Unlike private clouds, VPCs require a direct connection to the public cloud. This potentially makes it accessible to other public cloud users. However, subnetting IP addresses reduces this access risk.
Under the VPC model, users and cloud vendors share responsibility for security. Cloud vendors operate and secure the underlying infrastructure. VPC users must regulate access to resources via tools like security groups, access control lists, subnets, firewalls, and identity and access management (IAM).

Advantages of virtual private cloud architecture include:
- Flexibility. VPCs can scale rapidly as companies grow or contract.
- Cost-effectiveness. VPCs are cheap to set up and deploy because the cloud provider handles infrastructure.
- Low maintenance overheads. Companies can run cloud deployments without large IT teams.
- Sophisticated internal security. VPC users can segment deployments. It’s easy to separate financial data, sales platforms, and DevOps environments.
Virtual private clouds also have negative aspects. Most importantly, VPCs can experience outages and downtime. While VPCs are flexible, users of private cloud systems may have more customization options.
Security is another issue. VPC users must connect to gateways before accessing cloud resources, and this connection can raise security risks. Reliable access controls and multi-factor authentication (MFA) mitigate these risks. Virtual private network (VPN) protection also helps secure the VPC perimeter.
Note: Many users confuse VPC and VPN technology. The key difference is that VPNs encrypt data flows over the public internet. VPCs are virtualized cloud deployments. They complement each other, enhancing overall security.
What is a private cloud?
A private cloud is a standalone cloud solution with a single tenant. Under the private cloud model, users own and manage their cloud computing infrastructure, including data storage and networking solutions. Control is centralized, and users take responsibility for cloud security.
Typically, private clouds reside in data centers managed by the user organization. On-site hardware creates a physical network perimeter. Endpoints on the private cloud perimeter enable access control. Managers can filter inbound and outbound traffic, ensuring a high level of security.

Private clouds have many benefits:
- Support for legacy applications. Ensuring access to legacy applications that do not function well on the public cloud (if at all).
- Enhanced integration management. Managing integrations to ensure operability and maintain security.
- Granular visibility of network access and user behavior.
- Resource segregation and control. The ability to segregate resources and have full control over the underlying infrastructure.
- Robust privacy protection for sensitive information via tight access controls.
- Complete customization. Users have total freedom to design private cloud architecture.
There are also downsides. Private clouds are complex and expensive to implement and maintain. They scale poorly compared with VPCs. Users require extensive expertise and may see IT costs spiral.
Differences between virtual private clouds and private clouds
The main difference between VPCs and private clouds is that VPCs reside on public cloud infrastructure while private clouds are hosted within an organization’s own data centers or dedicated hardware.
Both technologies allow single-tenant cloud computing, ensuring greater privacy than public cloud solutions. However, users should know how they differ before making a selection. Let’s quickly run through the main points of difference.
Getting started
Private cloud
Configuring a private cloud takes time and expertise. In-house teams to manage and secure cloud deployments. This may entail recruitment or hiring short-term consultants to handle the process.
VPCs
VPCs are relatively easy to set up. The cloud provider manages infrastructure security and VPC performance. Users can also connect VPCs easily to on-premises resources or other cloud instances.
Ease of use
Private cloud
Private clouds meet organizational needs. As a result, they should meet user demands efficiently. However, ensuring consistent performance is technically challenging for in-house teams.
VPCs
VPCs score highly on usability. Cloud vendors handle demanding technical tasks and support new users. Users do not need in-house expertise to benefit from cloud computing services.
Performance
Private cloud
Private clouds deliver robust performance as they reside inside an organization’s network perimeter. Dedicated IT teams also engineer private clouds to meet operational challenges.
VPCs
Cloud-hosted VPC services often show improved performance compared to locally hosted alternatives. They also scale more easily, accommodating business growth.
Maintenance
Private cloud
In-house teams maintain private cloud infrastructure. Data centers require cooling and power systems, which require regular testing and updating.
VPCs
VPCs need minimal maintenance. Users do not maintain physical hardware, although IT teams must check security parameters and audit network traffic on virtual machines.
Cost
Private cloud
Private clouds are expensive to set up and maintain.
VPCs
VPCs tend to be more affordable. Users can also purchase the capacity needed, keeping costs as low as possible.

Availability
Private cloud
Private clouds are generally very reliable and deliver high levels of availability.
VPCs
VPCs rely on cloud providers to keep systems operational and available. Users can leverage redundancy to hedge against downtime or cyberattacks.
Security
Private cloud
The private cloud model is extremely secure. Organizations can limit external access across the network perimeter and deploy internal segmentation to regulate lateral movement.
VPCs
VPCs are more secure than public cloud solutions but less secure than private clouds. Network access controls and segmentation protect critical data. However, unsecured access points can expose data to the public cloud.
Virtual private cloud vs. private cloud vs. hybrid cloud
Before we discuss how to choose cloud solutions, we need to talk about another issue: hybrid cloud deployments.
Hybrid cloud solutions mix different technologies. The most common type combines public clouds and private cloud services.
This type of hybrid cloud suits businesses that need to cut costs, host large amounts of non-critical data, or regularly experience traffic spikes. However, hybrid cloud security is a critical factor to consider, as securing data and workloads across diverse environments requires careful planning.
For instance, space on public clouds is usually cheaper than private alternatives. You might secure confidential data in VPC containers while keeping low-risk assets public.
Another form of hybrid cloud combines private clouds and VPCs. In this scenario, users might reserve sensitive data in a private cloud service. VPCs can handle other workloads. This suits remote workforces and reduces cloud computing costs.
Choosing the right cloud for your business
Let’s return to the main question: should you choose a private cloud or a VPC-based solution? Here are some factors that influence the decision to choose private cloud vs public cloud technologies:
Complete data protection
In the comparison between private cloud vs. public cloud security, VPCs, and private clouds easily beat shared public cloud solutions.
Private clouds are slightly more secure than VPCs, as users have more control over how and where their data is stored. This makes them a better choice for organizations like healthcare bodies or financial data processors.
In general, organizations in highly regulated sectors should consider a private cloud model. They might also segregate sensitive data within private clouds and use public or VPC solutions for other assets.
Simplicity and ease of use
Virtual private cloud solutions suit smaller companies without dedicated cloud maintenance teams. Private clouds require extensive maintenance and are relatively hard to scale.
A VPC solution lets small businesses benefit from cloud computing, secure data, and adapt their deployment as their needs change. Setting up a VPC is also much easier than a private cloud.
Keeping costs low
Think about the cost of your cloud hosting solution. Private clouds have high upfront costs, while VPCs are very affordable. They lock down confidential data or workloads without needing huge capital investment.
Private clouds may have long-term advantages as the operational costs fall over time, especially for larger organizations.
Flexibility
VPCs are more flexible than private clouds. You can spin up virtual servers and storage capacity as needed. For example, you may need a temporary DevOps environment to test code before using it elsewhere.
VPCs can also reside closer to customer communities. If you serve clients on other continents, regional VPCs cut latency and may aid compliance by separating customer data sets.
Private clouds are easier to customize but less flexible. Scaling is complex, making VPCs a better option if your computing or storage needs are uncertain.
Availability
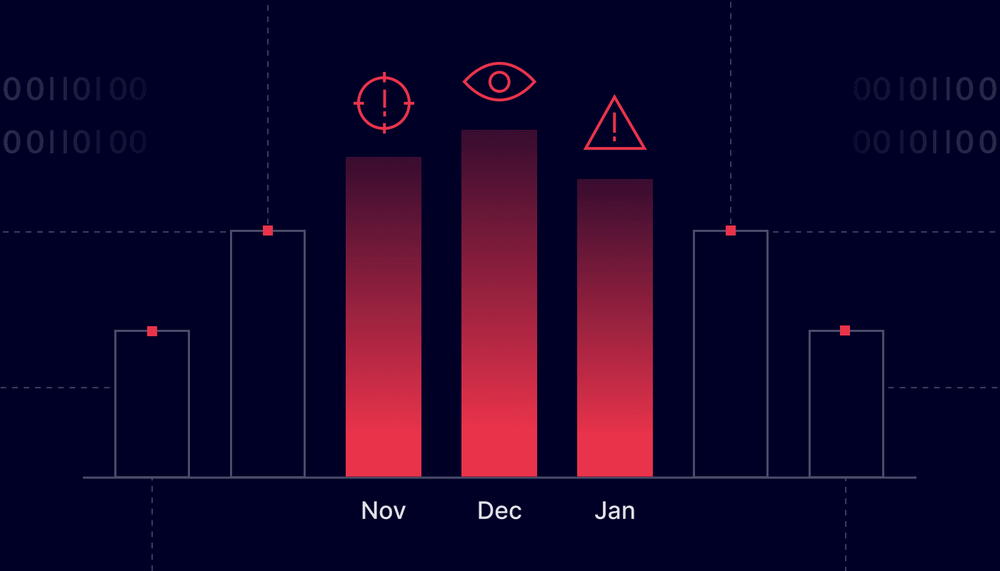
Companies using the cloud to host websites or customer data need high availability. Downtime, which disables web services and workloads, costs money.
VPCs solve the availability issue via redundancy. You can use peering or availability zones to keep systems running, even if part of your deployment fails.
Private clouds are generally reliable but present a single point of failure. Using multiple virtual servers may be a safer option.
Performance
Properly designed private cloud systems perform well because they dedicate resources to essential tasks such as processing AI data sets or video rendering.
VPCs share space with cloud provider customers, leading to variable latencies. Virtual private cloud data centers could also be distant, causing speed issues.
Virtual vs. private cloud: Securing access to both
Whether you choose a virtual private cloud or private cloud solution, security is a top priority. VPC best practices like encrypting data and applying security groups help but are not comprehensive solutions.
Secure cloud access controls are critical to minimize data breach risks. Malicious actors pounce on vulnerable devices and endpoints. There is no room for complacency, no matter what assurances your cloud provider offers.
NordLayer is compatible with the most popular VPC solutions. It can enhance your security by protecting who can access the data stored in the cloud. To secure your VPC, consider these steps:
- Secure Remote Access: Use NordLayer’s Site-to-Site VPN to create an encrypted tunnel, allowing safe access to the VPC without exposing data to public internet risks.
- Prevent unauthorized access: NordLayer’s Cloud Firewall helps you control who can access the VPC. You can limit access to authorized users, reduce the chance of data leaks, and use extra security layers like SSO and MFA to double-check identities before granting access.
- Device Posture Security: NordLayer’s Device Posture Security ensures that only approved devices that meet company security standards can connect to the VPC. It helps prevent compromised or non-compliant devices from accessing sensitive data.
To find out more, contact the NordLayer sales team and discuss your cloud security needs.
If you serve security-conscious clients, why not take a look at our MSP partner program as well? As a cybersecurity partner, you can earn revenue and secure your cloud assets with support from our experts.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.







:format(avif))



:format(avif))
:format(avif))