Some forms of malware are more sophisticated than others, using varying methods of compromise or evasion. Examples include ransomware, wipers, viruses, worms…designed to intrude upon unsuspecting digital victims to steal, damage, or destroy their data.
Fileless malware is one of those types that is highly evasive – only working within a computer’s memory, leaving no physical footprint on its hard drive.
With such a method of execution, does it mean that our devices are left vulnerable? Not quite.
What is fileless malware?
A common way many types of malware families work is that by opening a malicious attachment, you inadvertently enable the code to execute its dark magic, acting without the user’s knowledge.
Consequently, the code can infest different parts of the system, install other payloads such as keyloggers or other spyware, block access to files or apps, display malicious ads, and more. Think of it as a regular program that’s installed on your PC, just acting against your interests.
Fileless malware is a bit different. Instead of being stored on your computer’s drive, it acts maliciously exclusively after being loaded into a computer’s random-access memory (RAM) – except being less visible as it uses legitimate programs to compromise the computer, as opposed to regular malware, which leverages executable files to run itself (needs to be installed). This means that fileless malware is harder to detect since it has no footprint to speak of – it exists entirely in memory.
Essentially, fileless malware manipulates existing processes/tools for its agenda, as opposed to running a separate standalone ‘campaign’, also making it more persistent due to its ability to manipulate system features, abusing and hiding within them.
Did you know? The fileless beginning of viruses
The first computer virus for the PC, the Brain virus, infected floppy diskette boot sectors only, not files. Dating back to 1986, it was followed by many other floppy diskette (and hard disk drive) boot sector infectors like Form, and hard disk drive master boot record infectors like Stoned and Michelangelo. All of these were never contained in any file on the file system of the disk volume, just in system areas of the disk that were normally inaccessible to users, and subsequently in memory, once a system booted from infected media.
But you might ask, “Alright, but I still need to download it somewhere, no?” and you’d be right: in-memory ‘fileless’ malware is still delivered via malicious links or attachments; it’s just that the execution is different – fileless malware wants to evade detection as much as it can.
Examples of fileless malware
A well-known example of the use of fileless malware was within the Astaroth malware campaign (detected by ESET as Guildma), which had been using a fileless method (process injection) to operate an infostealer, originally delivered through a malicious email link. Upon interaction, the malware used legitimate Windows tools such as BITSAdmin, the Alternate Data Streams file attribute, and a utility of Internet Explorer (ExtExport.exe) for defense evasion (through DLL Side-loading).
In essence, it leveraged legitimate system processes and tools to run its code becoming detectable after being run in memory (by ESET as Win32/Spy.Guildma).
Similarly, the Kovter malware family, first detected by ESET Research in 2014, stored its malicious payload encrypted in the Windows registry, considered as fileless persistence. Likewise, GreyEnergy also made sure that some of its modules only ran in memory, hindering detection.
Such malware techniques are problematic for simple endpoint security software that works by scanning files on a system, lacking process or memory scanning capabilities. But this doesn’t mean that they cannot be detected.
Protecting against fileless threats
ESET Endpoint Security’s multilayered product features an Advanced Memory Scanner module, which, combined with our Exploit Blocker, protects against malware designed with evasiveness in mind. Additionally, thanks to different forms of Advanced Machine Learning employed within, detections are fine-tuned to offer the best detection rates.
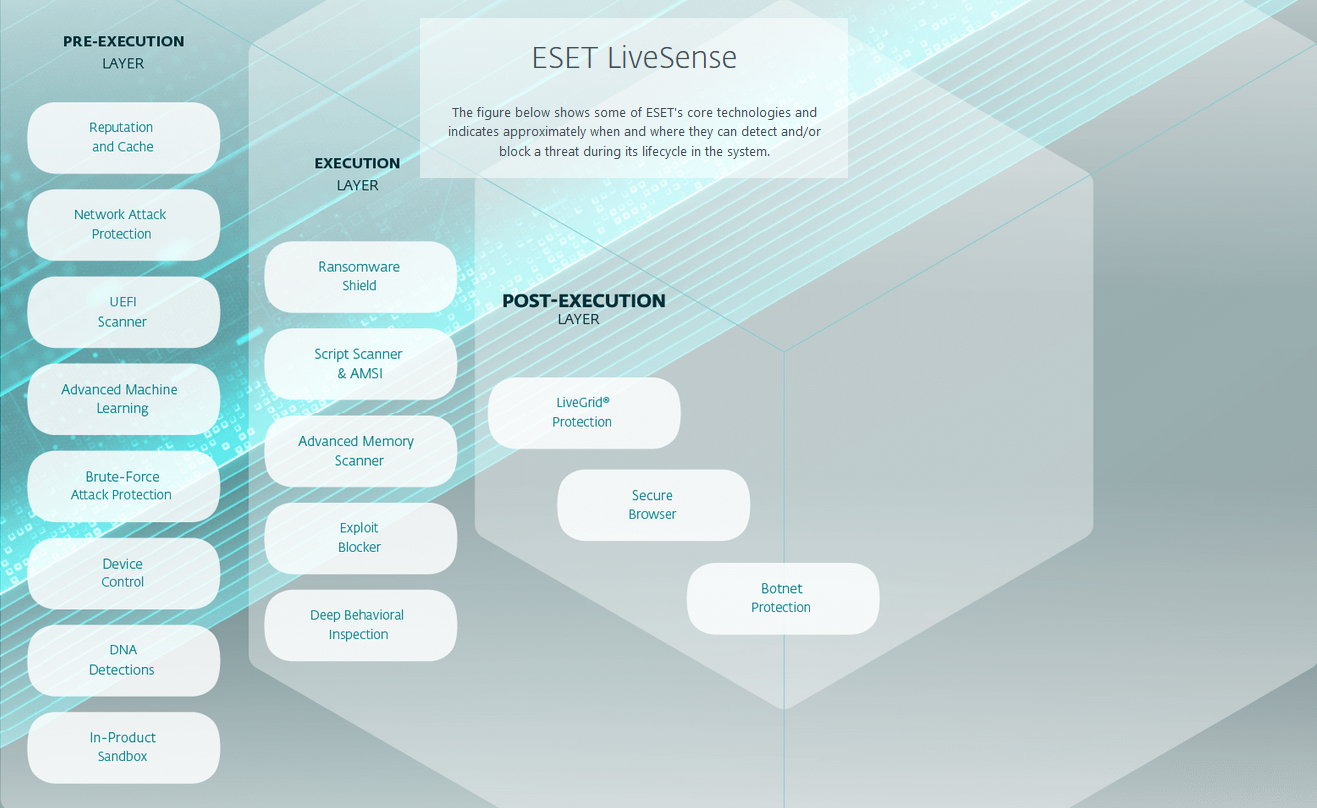
Only memory scanning can successfully discover active in-memory fileless attacks that lack persistent components in the file system, such as was the case with Astaroth (Guildma) and its use of the Windows toolset.
Furthermore, the ESET Host-based Intrusion Prevention System (HIPS) and its Deep Behavioral Inspection (DBI) use predefined rules to scan for and monitor suspicious behavior related to running processes, files, and registry keys, targeting methods often used by fileless malware to obfuscate its activities. Hence, malware families like Kovter find it hard to hide from ESET Endpoint Security in the Windows registry, since the memory scanner also deals with encrypted threats.
Issue-less
With cybersecurity protections stepping up to protect people against advanced threats such as fileless malware, one thing still needs to be said: Never click on any malicious links or attachments in suspicious emails – even if they are from someone you know and trust.
First, via a different communications medium (e.g., text, phone, or in person for something received in email, etc.), reach out to the apparent sender and verify whether it’s really them who had sent the message, as well as their intent. While this might seem like a bit too much, social engineering has gotten rather complex, and can fool anyone quite easily.
As always, exploiting human error is the best avenue for a compromise, so stay informed by reading our ESET Blogs, WeLiveSecurity, and ESET Research on Twitter (now known as X) to keep ahead of the cyber threat game.
In addition, try our free ESET Cybersecurity Awareness Training to learn how to stay secure at all times.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About ESET
For 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give individuals and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D facilities worldwide, ESET became the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single “in-the-wild” malware without interruption since 2003.