Similar to MacOS and Windows systems, securing Linux devices is paramount to ensure critical and sensitive data is safe from outside threats.
While many developers view Linux’s wide range of distribution and configuration options as desirable, the operating system (OS) presents a real challenge to IT admins. Those seeking to centrally monitor and secure Linux endpoints alongside other OS face challenges like managing root access/permissions, lack of centralized MDM while trying to stay up to date with the latest security patches across all of the different distributions.
Since there are numerous threat vectors, we recommend a simple, best practices approach to safeguarding organizational systems and data. This article highlights eight Linux System best practices worth following for better security.
8 Ways to Safeguard Linux Systems from Cybersecurity Threats
Though by no means exhaustive, the following tips lay a strong foundation for implementing a Zero Trust Security framework in a Linux environment:
1. Stay Current on Patches and Updates
Always update the software running on your devices as soon as possible to protect against vulnerabilities and/or security enhancements. This means ensuring your Linux distributions as well as other installed software are running the latest versions.
The JumpCloud Directory Platform makes it easy to set up patching policies for Ubuntu systems. You can also use JumpCloud to create your own custom scripts/commands to ensure all your devices and installed software are kept up to date.

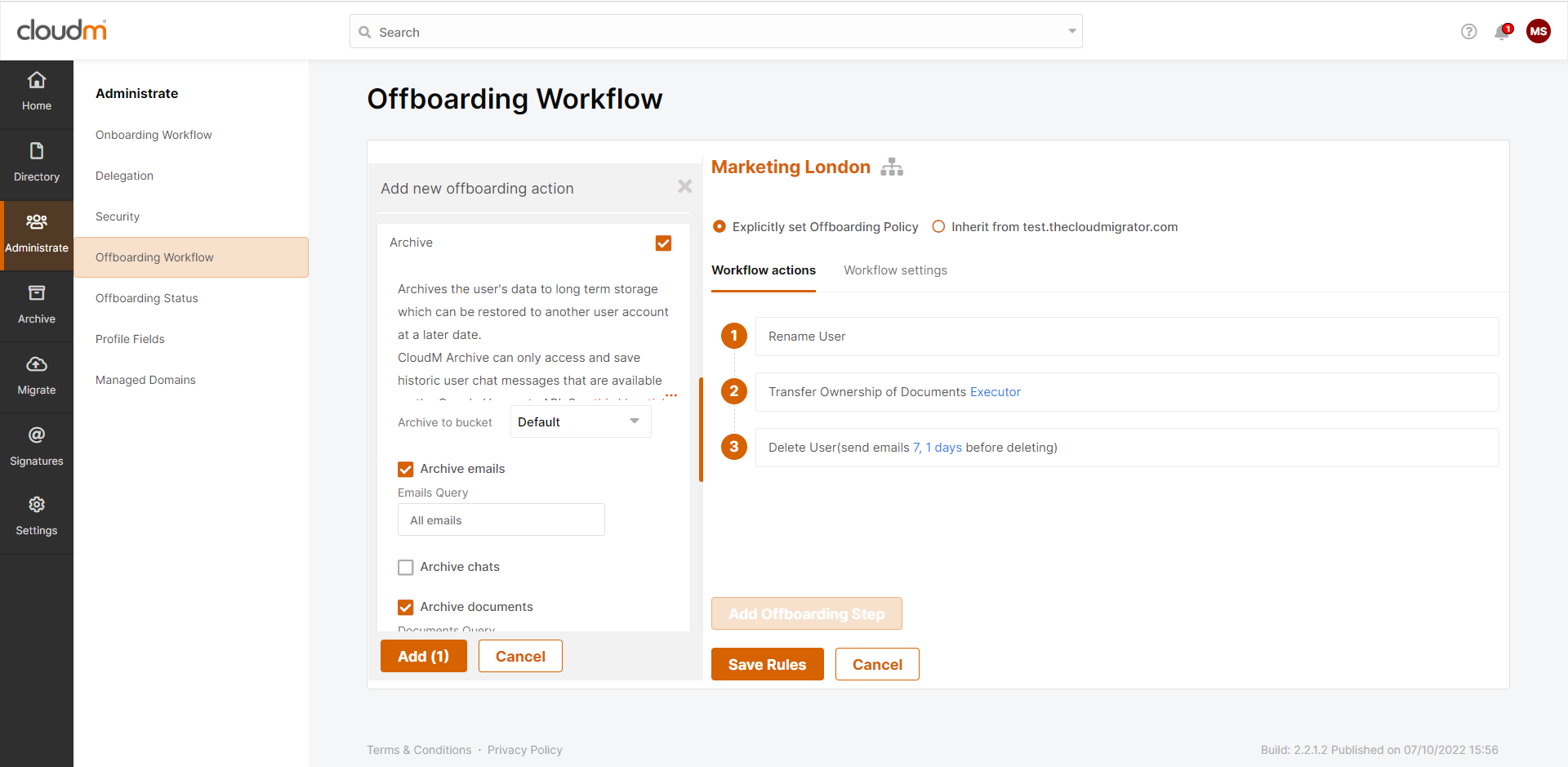
2. Practice the Principle of Least Privilege
NIST defines least privilege as follows:
The principle that a security architecture should be designed so that each entity is granted the minimum system resources and authorizations that the entity needs to perform its function.
In other words, only provide access to needed resources at any given time.
For example, the marketing department probably doesn’t need access to the same applications and data as the finance department. Use a platform like JumpCloud to manage which users have access to your Linux devices and what specific permissions and applications are available and/or accessible.
3. Utilize Data Encryption
Encrypt Linux systems data by ensuring only authorized users (with an encryption key) have access. Full-disk encryption only releases decrypted data contents after users provide proof of identity via a passphrase or key.
This extra measure provides additional security beyond existing OS security mechanisms because it continues to protect content even after breach or removal. Follow JumpCloud’s recommended Linux Encryption Best Practices along with the Linux Check Disk Encryption Policy to verify your data is protected.

4. Maintain Up-to-Date Images
Linux systems are often built or copied from “golden” images. While this hack is great scaling without building from the ground up, many admins forget to update the golden images regularly.
Ensure you’re building secure systems by maintaining your images with the latest patches and security updates. Here is a quick tutorial that walks through setting up critical policies and management practices with the JumpCloud agent.
5. Secure and Monitor Network Activity
Monitor and secure your network devices and traffic to mitigate vulnerabilities, threats, and potential for breeches. Regularly monitor your networks for abnormal activity that might indicate a new threat.
You can utilize Jumpcloud’s Network Parameters Policy to enhance your systems’ network security. This policy can disable IP and packet forwarding, prevent routed packets from being accepted, ignore ICMP broadcasts, enable path filtering and TCP SYN cookies, and log information about suspicious packets.
6. Minimize Software Footprint
Only install the software necessary for any given system. Unneeded and/or unused software increases the security risk and potential threat vectors. Further, by removing unneeded software, you also get the benefits of reduced storage space, memory allocation, any associated licensing costs while optimizing your system performance
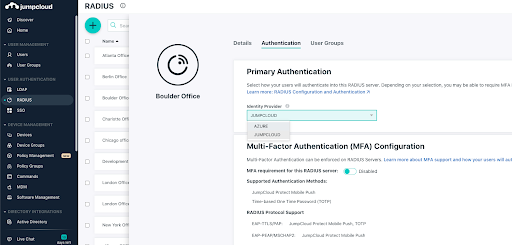
7. Enforce Strong Passwords, MFA and/or SSH keys
Protect and prevent unauthorized access to organizational systems by enforcing strong passwords, SSH keys, and multi-factor authentication.
Ensure passwords and/or SSH keys are changed regularly. Further, utilize Jumpcloud’s SSH Root Access and SSH Server Security Enforcement to help ensure only authorized access. The SSH Server securely provides remote access to devices.
The settings in this policy only apply if the SSH daemon is installed on the system. To ensure access is restricted to only authorized users, configure your server to: place sensible resource limits, disable features with high potential for abuse, and disable algorithms and ciphers known to be weak.
8. Stay Vigilant with Ongoing Training
IT Security is always changing to adapt and protect against new threats. We are all in this together to foster a safe IT environment as the backbone of our technologies.
As the saying goes, “It takes a village!” IT professionals must stay abreast of emerging security threats and openly share their knowledge with the community. We recommend monitoring the following resources for the latest security landscape happenings:
- https://learn.cisecurity.org/ms-isac-subscription
- https://www.cisa.gov/known-exploited-vulnerabilities-catalog
- https://nvd.nist.gov/
- https://cve.mitre.org/
Of course, the above list is certainly not exhaustive. Each IT admin and organization should determine which security measures to take in order to best achieve their objectives.
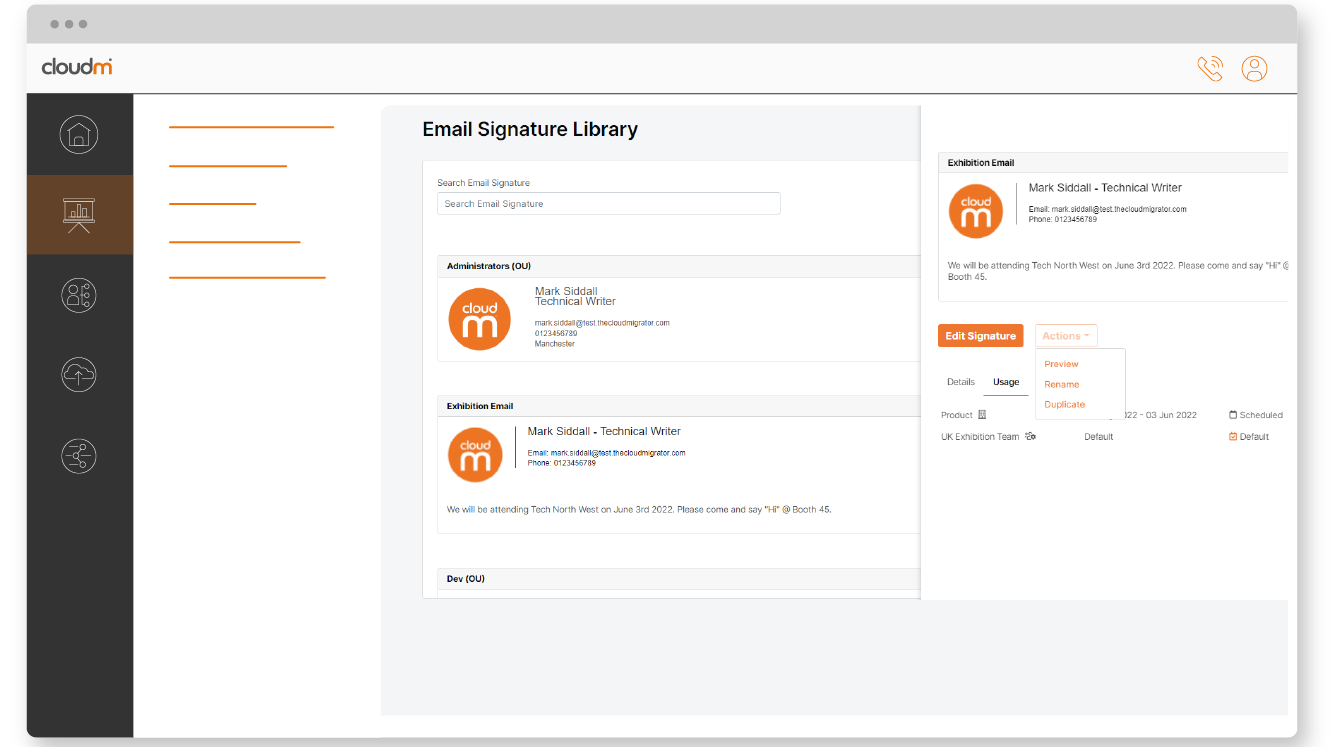
Manage Your Linux Systems With JumpCloud for Free!
At JumpCloud, we’re constantly building additional security and management measures to help meet emerging regulatory compliance requirements, security posture, and device management needs.
Please review our growing suite of Linux Security Policies and let us know how we can help provide you the tools you need to better manage your Linux systems. JumpCloud’s cross-OS platform makes it easy to manage Linux (Ubuntu) servers, Red Hat clients, Windows fleets, and macOS devices.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About JumpCloud
At JumpCloud, our mission is to build a world-class cloud directory. Not just the evolution of Active Directory to the cloud, but a reinvention of how modern IT teams get work done. The JumpCloud Directory Platform is a directory for your users, their IT resources, your fleet of devices, and the secure connections between them with full control, security, and visibility.