Active Directory (AD) is a directory service introduced by Microsoft that runs on a Windows server to centrally manage user access to resources on the LAN. The server role in Active Directory is run by Active Directory Domain Services (AD DS), and the server running AD DS is called a domain controller. The domain controller performs two important functions:
- Authenticates and authorizes all users and systems in a Windows-based network
- Assigns and enforces all security policies for Windows systems
That is why Active Directory remains an important system of record for many small and medium-sized enterprises (SMEs), even though it can only reside on servers within a network. However, IT infrastructure and workplace trends have changed dramatically since its introduction over two decades ago. It’s common to have a heterogeneous mix of devices with employees working remotely at least some of the time (or even indefinitely). Microsoft has responded by extending AD to the WAN, but devices and users can now be managed without AD, or Microsoft.
Identity has become the new perimeter and IT teams must look beyond standalone AD to manage identities and all corresponding devices, wherever they exist. Devices are the gateway to your IT assets and shouldn’t go unmanaged because they’re not Windows. Cloud directories are filling the gap by providing the access control, device management, portability, and security that AD cannot. This has brought forward the option for a new paradigm: the domainless enterprise.
This article examines AD’s benefits, and when it’s necessary to look beyond it. That’s accomplished by integrating with cloud directory services to extend it, or even a domainless enterprise.
What Does Active Directory Do?
AD DC manages local network elements, such as systems and users, by organizing them into a structured hierarchy. The domain controller is then responsible for authorizing user authentication requests within the network. The next section outlines its core capabilities.
Manages Devices, Services, and Users
Active Directory Users and Computers manages local contacts, devices, and users in your fleet: from PCs to printers. Admins create and organize groups within organizational units (OUs) to logically separate resources. OUs reside within a “forest,” which is the highest level of organization in AD. It may include service accounts for network services, apps that run on your servers, and integrations with SaaS apps. Service accounts can run locally on machines or across the domain. This tool also configures permissions for objects within your directory.
Global Catalog of Domains
Global catalog is an AD feature that stores replicas of the attributes of an object within a forest (or domain tree), even if the object (such as a user) resides within a separate domain. This enables organizations to centralize IT even if they have multiple locations and data centers, but users and devices must either exist within the confines of those facilities or utilize a VPN.
Querying and Indexing Directory Objects
There are two built-in options to query AD attributes. The Active Directory schema snap-in enables admins to index attributes. PowerShell is another option to specify a query string to retrieve AD objects. Many organizations purchase third-party reporting tools for compliance purposes and to gain visibility into their AD environment, but it’s vital to trust all software that’s installed on a DC. Attackers may gain entry into networks through the supply chain, and DCs hold the “keys to the kingdom.”
High Availability
Every domain controller is a server object in AD DS. High availability is automatic whenever there’s more than one DC. This makes it possible to shut down a server for maintenance without impacting your end users. Objects are automatically replicated throughout the server cluster. Administration is more complex: e.g., add-on apps must be installed and updated on each DC. Adding servers may increase licensing, management, server infrastructure costs.
Schemas and Templates
Admins have deep control over how AD operates. Schemas can be customized to control (through rules) objects that can be stored within the directory and their related attributes. Templates can be configured to automate the creation of objections and associated policies. Admins use the Group Policy Editor to create and edit ADMX and ADML template files. Templates may also be imported into Microsoft’s Endpoint Manager, a new subscription cloud service.
Now, let’s explore what AD isn’t capable of doing.
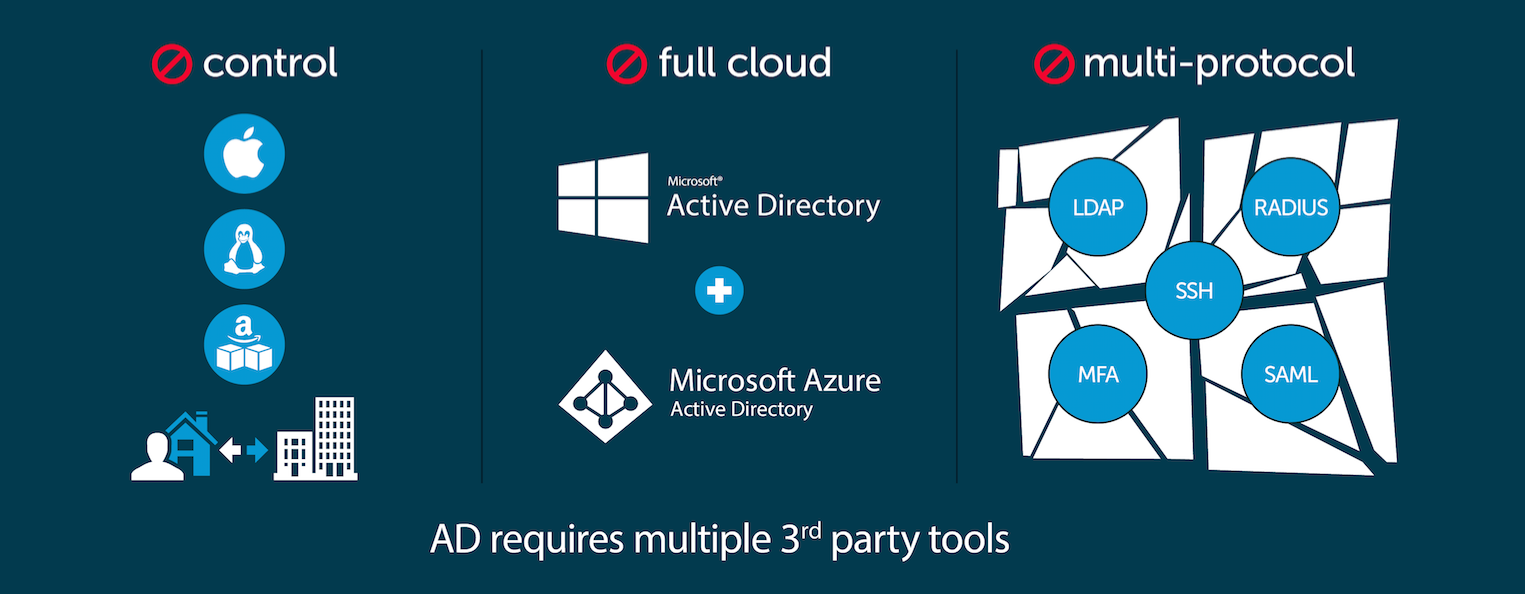
What Doesn’t Active Directory Do?
The domain controller serves an important role, but the modern workplace has shifted to the cloud. Legacy management solutions like the domain controller struggle to manage the disparate, non-Windows-based identities that have become commonplace in the IT landscape. Managing identities also entails managing devices and access to SaaS apps external to the Microsoft ecosystem. The next section examines those constraints in further detail.
Single Sign-On (SSO) and Multi-factor Authentication (MFA)
The widespread shift toward web applications means that end users can no longer leverage single sign-on (SSO) through AD for all resources. Twenty years ago, when the IT landscape consisted entirely of Windows applications and desktops, AD connected every user to just about every resource they required. AD no longer grants that level of authorization, forcing admins to adopt additional tooling to manage authentication and authorization for all of their IT assets.
Microsoft introduced an Identity-as-a-Service (IDaaS) solution with Azure Active Directory (AAD), but AAD can make identity management complex, time-consuming, and costly for IT admins by forcing them to keep on-prem AD in conjunction with it. There’s a free tier of AAD that makes it possible to access apps such as Microsoft 365 (M365), but a Premium 1 (P1) or greater subscription to AAD is necessary to have SSO for domain-bound apps and the cloud.
Additionally, if IT professionals wanted to leverage SSO for their users without AAD, they would have to add Active Directory Federation Services (AD FS) to their on-prem AD. That would need to be housed on-prem. AD FS has high management overhead and can be difficult to implement. Microsoft requires the NPS server role to be installed, configured, and managed to access network devices. There are multiple options for SSO within the Microsoft portfolio, but extending AD for roles it wasn’t designed for dramatically increases complexity and overhead.
Multi-factor authentication (MFA) isn’t built into AD. SMEs must purchase solutions that integrate with it. Microsoft offers MFA to access Windows apps, but only through its AAD P1, P2 SKUs. Additionally, conditional access (CA) policies aren’t available without those integrations.
Securing and Managing External Identities
The domain controller struggles with providing access to IT resources outside of the on-prem Windows networks, so AWS and GCP infrastructures can be difficult to integrate, such as Google Workspace.
Third-party solutions, such as JumpCloud’s open directory, manage identities from other identity providers (IdPs) such as Google or Okta. Microsoft has introduced the capacity to manage external identities through Entra, for an additional monthly fee per user. It also charges for every single instance of an MFA authentication for those external IDs.
Strong Security Defaults
Substantial work is required to harden Active Directory through specialized configurations. It’s not secure by default, and attackers have cultivated a strong understanding of AD’s default settings. Hardening AD is mandatory to secure your infrastructure.
IT teams should always follow best practices to limit how they run as domain administrators. It’s advisable to use Microsoft’s ATA (Advanced Threat Analytics) or Defender for Identity to detect anomalous user behaviors. Security best practices for AD can take several full days of work to implement.
Automation of Identity Lifecycle and Entitlements
User identity lifecycle and entitlement management is a manual process in AD. Serious and costly breaches, including the Colonial Pipeline ransomware attack, have occurred when domain users were “forgotten.” Forgotten accounts are still able to access assets. It’s important to actively manage users and privileges to safeguard against insider and external threats.
Integrated Reporting
Third-party tools/services are necessary for reporting, especially when your users are accessing confidential and protected information or your industry is subject to compliance or regulatory requirements.
Cross-OS Device Management
Systems must be directly bound to the AD to deploy Group Policy Objects (GPOs) which are registry settings, configurations, or tasks that need to be executed. Mac and Linux systems’ commands and scripts (i.e., no GPOs) cannot be managed from the Windows domain controller, meaning that IT admins must manually configure each system if they choose not to implement add-ons. Even Windows systems must be connected to a VPN to receive policy updates from AD or PowerShell commands, complicating your capacity to effectively manage remote users.
Microsoft’s paid subscription Intune service fills this gap, but Microsoft services aren’t mandatory. An open directory platform, such as JumpCloud integrates with AD to perform this function, but could also manage devices without a domain controller being present.
Patching
There have been over 1,000 patches released from Microsoft to date this year alone. Patch Tuesday has now become “Zero Day Tuesday.” However, it’s possible to deploy software using AD Group Policy, but it doesn’t handle patching Windows systems throughout a domain (or even third-party applications) without a patching solution.
Patching services may be cloud-based, such as JumpCloud, or on-premise servers. Patching OSs and apps (such as browsers) is vital to prevent Zero Day attacks from being exploited.
AD DS runs on Windows Server, which must be maintained and supported. Domain controllers contain data that determine access to an established network, making it a primary target for cyberattackers looking to corrupt or steal confidential information. It’s even possible for attackers to elevate domain standard users accounts to become domain admins without using malware on unpatched systems. Security tools such as BloodHound and Mimikatz are all that’s required for the AD attack path.
Standard endpoint detection and response (EDR) won’t detect these intruders, and firewalls won’t stop them. Given these risks, cybersecurity should be a paramount priority for all SMEs. Industry experts routinely recommend a Zero Trust posture.
Active Directory isn’t Zero Trust.
Active Directory and Zero Trust Security
Microsoft has responded to these threats by updating AD’s capabilities for better security, but the requisite setups and changes can be resource intensive or require its premium cloud services. Active Directory works best with on-prem networks and Windows-based environments. AD natively operates by establishing a network of trusted assets, known as a domain, which are protected by an AD domain controller, VPN, firewalls, and other controls.
The objective is to create a strong perimeter to protect trusted resources from the open internet. As a result, external sources of network traffic (e.g., users) must first authenticate and ultimately be authorized to access internal domain resources such as systems and applications.
Zero Trust security, on the other hand, is a security model that effectively eliminates the separation between an internal domain that’s safe and the open internet that’s dangerous. Rather, all sources of network traffic are viewed as potential attack vectors that must generate trust before they are authorized for user access — and with good reason too. Bad actors are now attacking traditional networks from inside and out, often bypassing perimeter-based security by targeting trusted assets. Thus, Zero Trust security is effective because it basically eliminates the concept of trusted assets (i.e., the domain) altogether. Users must prove who they are.
The next-generation Active Directory alternative has been reimagined AD for the cloud era. Cloud directories connect users to their IT resources regardless of their platform, provider, protocol, and location. They’ll also manage all your devices. Additionally, as an identity and access management (IAM) platform, cloud directories forgo the concept of the traditional domain. This provides users with True Single Sign-On™ access to virtually all of their IT resources. SMEs can leverage JumpCloud’s open directory platform to manage identities wherever they reside with the assurance that it will help to deliver Zero Trust security.
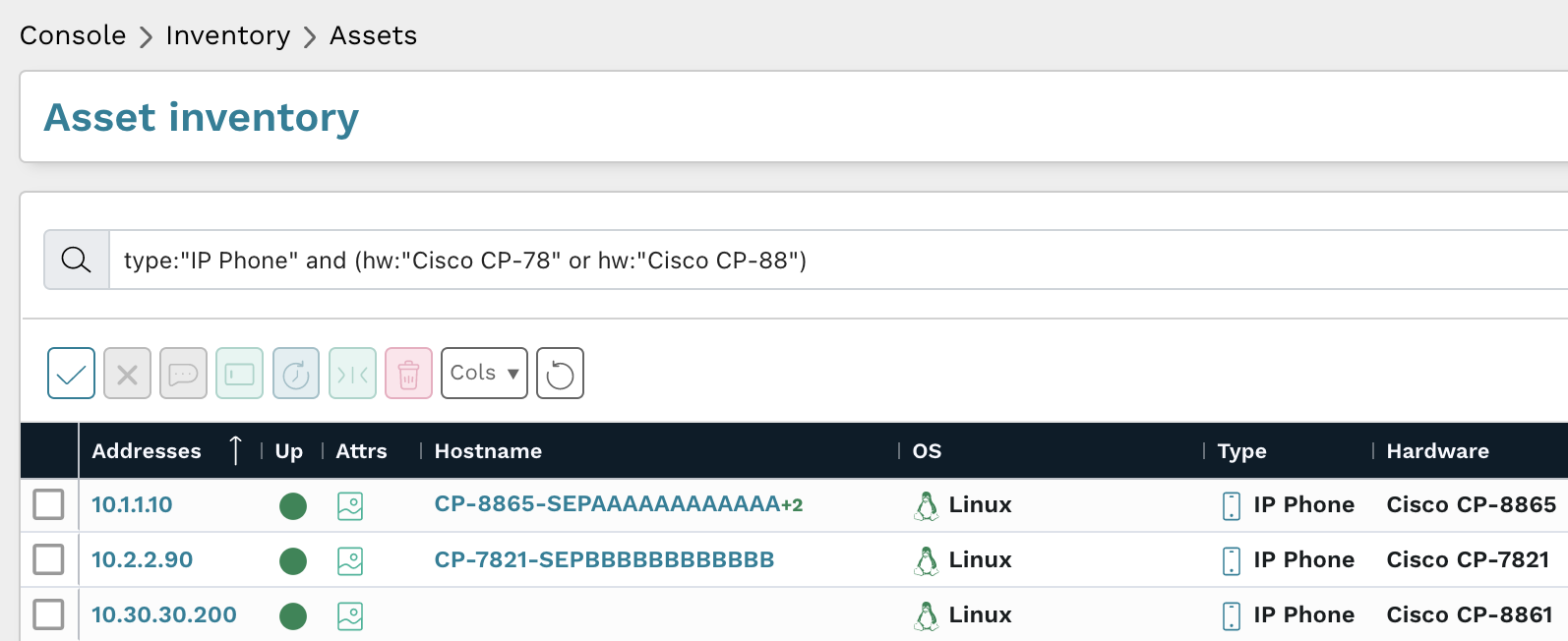
Cloud Integration with IT Resources
The cloud directory integrates with the external identities and devices that AD doesn’t support in addition to AD itself. This is made possible through the combination of modern IAM and SSO protocols, automated entitlements management, using MFA to verify users, and CA for privileged user management. You can manage your entire device fleet through JumpCloud.
Centrally Control Identities and Systems
JumpCloud can extend AD and AAD identities and agent-based control (or MDM) to all systems in a fleet, whether they’re Apple, Android, Linux, or Windows devices. Unlike Microsoft, there’s no additional cost to manage your non-Windows devices or Windows without a DC. JumpCloud can also serve as a standalone cloud directory or import identities from Google and Okta.
End users access their machines with their identity provider’s credentials, and admins can enforce pre-built GPO-like policies on those machines, such as full disk encryption or managing patches. No complex templates are required. SUDO-level permissions and a PowerShell module enable administrators to perform commands on any device, from CRUD operations to benchmark policies. A commands queue offers admins an easy-to-use dashboard for admins to see what commands they have awaiting execution on all their assigned devices and their status.
Other key features include:
- Automatic high availability and redundancy. There’s no need to license multiple servers or to create a service account that has access to a privileged AD group.
- Telemetry aggregated from devices, events, users, and cloud services with pre-built reports and reporting tools. You’ll even know which users are accessing SSO apps.
- Opt-in Remote Assist, without the complexity of RDP or need to license a solution from a third party. This feature works across multiple operating systems.
- An optional decentralized password manager and vault for your users.
- Zero-touch Mac enrollment is available and Windows Out of the Box Experience (OOBE) is upcoming to onboard remote workers.
- PowerShell command templates to bind Windows PCs to your office printers without a print server.
- PKI as a service (coming soon), eliminating the need for a separate CA (certificate authority) Windows server role.
- The benefit of potentially lowering your TCO.
Manage Wi-Fi and VPN Access
You don’t need AD to access your network. Admins can achieve Cloud RADIUS functionality without additional on-prem infrastructure, and they can ensure users log into Wi-Fi networks (with VLAN tagging) and VPN clients using the same core credentials they use to access their other resources. Delegated authentication includes AAD credentials. Admins can enable Push or TOTP MFA, which is especially useful to secure VPN access to internal network and on-prem resources from switches to servers.
SSO to Everything
The open directory platform builds the stack that you want. A web-based portal is used to access all the apps employees need to do their jobs with best-of-breed solutions. The portal serves as a security control to help eliminate phishing. Pre-built connectors are freely available for common apps. Supported protocols include:
- LDAP
- OIDC
- SAML/SCIM
- RADIUS
Long-standing workflows don’t have to be scrapped in favor of cloud apps. Even Windows file sharing is possible without a domain controller.
Like AD, groups are used to manage access to your apps and resources. The difference is that they are automated with HRIS provisioning included. Attribute-based access control (ABAC) reduces the risk of human error and eliminates the heavy administrative overhead that’s necessary to keep AD privileges and users up to date.
Boundaries matter less.
This setup also eliminates the need for complex server management and AD’s global catalog. For instance, specifying an office location could be as simple as creating a directory group assignment.
Integrated MFA and Conditional Access
AD is reliant upon a single factor. MFA is environment wide in the open directory platform. Optional conditional access policies can further restrict access to trusted devices, by geolocation, and more for privileged users. JumpCloud doesn’t charge for MFA for external identities; Microsoft’s AAD does. Microsoft limits CA to AAD P1, P2, and requires integrations for AD. AD doesn’t have these capabilities and must be morphed into something it’s not in order to satisfy modern requirements.
In contrast, there’s far less complexity, labor, and cost when the domain controller is left out of the equation. In addition, there’s a greater opportunity to protect identities. JumpCloud secures identities (and aligned devices) even further with extended detection and response (XDR) integrations from the security vendors of your choosing. Microsoft only makes its security services first-class citizens.
Utilizing an Open Directory Platform
Organizations have already been moving their operations to managed services in the cloud to save the cost and time of maintaining an on-prem domain controller and server rooms. The journey begins by integrating JumpCloud with AD. An open directory platform frees up time and money for IT admins looking to manage a variety of systems and applications from one built-in service. Budget can be allocated toward higher priorities, such as Zero Trust, especially during leaner economic times. JumpCloud is free for your first 10 users or devices with 10 days of chat support up front.
Sometimes self-service doesn’t get you everything you need. If that’s how you’re feeling, schedule a 30-minute consultation to discuss options for implementation assistance, migration services, custom scripting, and more.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About JumpCloud
At JumpCloud, our mission is to build a world-class cloud directory. Not just the evolution of Active Directory to the cloud, but a reinvention of how modern IT teams get work done. The JumpCloud Directory Platform is a directory for your users, their IT resources, your fleet of devices, and the secure connections between them with full control, security, and visibility.