Are you a Mac devotee who’s been longing to experience the dark and wicked world of Blizzard Entertainment’s Diablo?
Well, I’ve got some great news for you — Parallels Desktop makes it easy for you to explore Sanctuary on your beloved Mac.
No longer do you have to be limited by compatibility issues; instead, get ready to join the countless PC gamers in this action-packed adventure that they can’t stop talking about.
I’ll guide you every step of the way to use Parallels Desktop so that your venture into Diablo is triumphant.
Smoother graphics and faster performance are guaranteed as this extraordinary program ensures that nothing stands in between you and your epic adventures!
Ready to transform your Mac into a gaming powerhouse? Get Parallels Desktop for Mac Pro Edition now and unleash your inner demon slayer!
How to play Diablo on a Mac
Ready to save Sanctuary? With Parallels Desktop Pro, you can quickly and easily install Diablo onto your Mac. Here’s how.
1. Purchase and install Parallels Desktop Pro
Get started by heading over to the official website and grabbing a copy of Parallels Desktop for Mac Pro Edition. Download it and get to installing.
2. Install Windows on your Mac
Open Parallels Desktop for Mac Pro Edition, click through instructions, then grab a valid Windows license key or installation media to finish things off.
3. Adjust the virtual machine settings
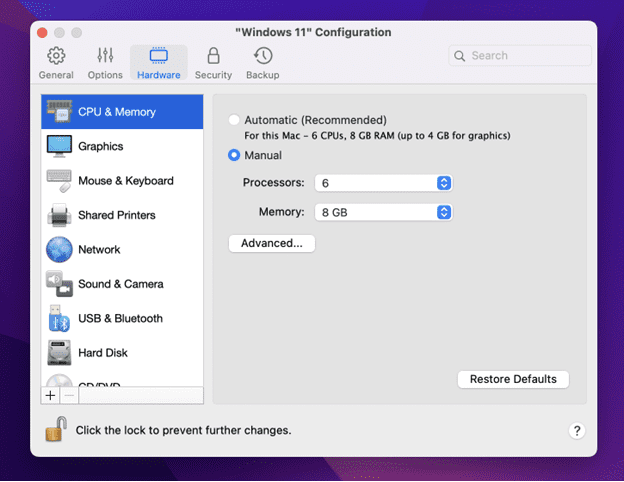
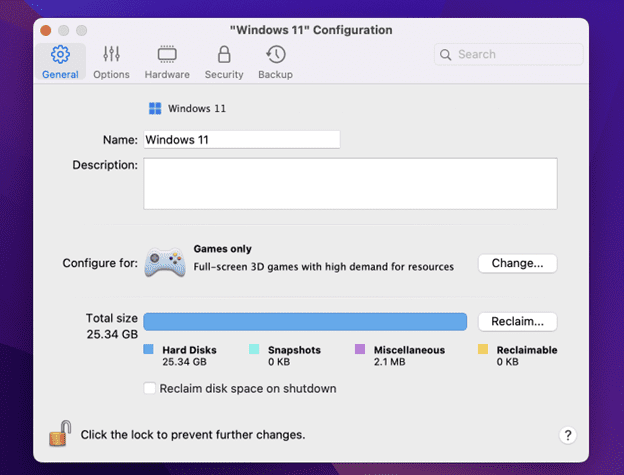
Once you’ve installed Windows, head into the Parallels Desktop Control Center under “Hardware” to allocate sufficient RAM, CPU, and GPU resources to ensure smooth gameplay.
4. Optimize Parallels Desktop for gaming
In the Control Center, select “Preferences” and choose the “Optimization” tab. Enable “Optimize for games” to further enhance your Diablo gaming experience.
5. Install Diablo
Now get your hands on the BattleNet client from Blizzard Entertainment’s website.
Follow some more instructions on-screen until you’ve downloaded and installed Diablo within your virtual machine environment
6. Configure game settings
Launch Diablo within your Windows virtual machine and head to the in-game settings menu.
Adjust the video and audio settings to your preferences and ensure that the game is running how you like.
7. Start playing Diablo on your Mac
You’re now ready to slay evil forces with ultimate precision using your favorite operating system.
Can Diablo 2: Resurrected be played on a Mac?
Diablo 2: Resurrected, similar to Diablo 3, is not natively compatible with Mac.
Simply follow the steps outlined in the section above to play the game on a Mac. You can also use these steps to play Diablo Immortal. You’ll be slaying monsters in no time!
Play Diablo on Mac with Parallels Desktop
Gearing up for an epic journey into Diablo or the vast world of PC gaming?
Parallels Desktop offers Mac users a powerful and versatile virtualization solution without compromising performance or user experience.
No more rebooting, no need to own multiple devices – this top-tier software ensures that graphics and gameplay remain smooth while you explore your favorite games.
So, if you’re ready to set out on a captivating adventure, equip yourself with the best tool available — Parallels Desktop — and get ready for full immersion!
Ready to transform your Mac into a gaming powerhouse? Get Parallels Desktop for Mac Pro Edition now and unleash your inner demon slayer!
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Parallels
Parallels® is a global leader in cross-platform solutions, enabling businesses and individuals to access and use the applications and files they need on any device or operating system. Parallels helps customers leverage the best technology available, whether it’s Windows, Linux, macOS, iOS, Android or the cloud.






)