Network management is pivotal and complex in the increasingly connected world. The task is enormous, whether it’s understanding the intricate user activity patterns, keeping a keen eye on data traffic, or monitoring device activity within the network.
Enter the analytics territory, where data doesn’t just speak; it roars volumes. By harnessing tools such as activity logs, server usage analytics, and Device Posture Monitoring, network visibility reaches a new height into a new dimension.
Different challenges require diverse solutions
A company network is a complicated organizational ecosystem. Various aspects, like the load of data traffic and employee connections, require specific attention. These targeted approaches help in decision-making, identifying problems, and streamlining network performance.
The use of data analytics in network management is transformative in addressing different issues:
Security concerns
Behavior analysis – continuous monitoring and analyzing data traffic, unusual patterns, or anomalies can help detect signs of a security breach or threats.
Compliance monitoring – regular scans and assessments ensure that network configurations meet the industry’s compliance regulations.
Network performance optimization
Bottleneck identification – real-time analysis of network traffic data helps identify potential bottlenecks or overloaded devices, allowing proactive action to prevent slowdowns.
Capacity planning – historical data analysis allows organizations to predict future network needs, making planning for expansion or upgrades easier.
Troubleshooting and maintenance
Root cause analysis – analytics can provide deep insights into the root causes of network issues, allowing for quicker and more accurate resolutions.
Predictive maintenance – by analyzing trends and historical data, predictive algorithms can forecast potential hardware failures or performance degradation, enabling preventative maintenance.
User experience and behavior understanding
Application performance monitoring – insights into how applications perform on the network can lead to optimizations that enhance user experience.
User behavior tracking – understanding how users interact with the network provides valuable security and performance-tuning insights.
Cost Management
Resource allocation – data-driven insights help efficiently allocate resources, ensuring no part of the network is over- or underutilized.
Cost prediction – analyzing trends helps forecast bandwidth usage, hardware upgrades, and maintenance costs, aiding budget planning.
Strategic planning and decision-making
Trend analysis – long-term data analysis can uncover emerging trends and potential opportunities for innovation or improvement.
Decision support – data-driven insights support informed strategic decisions, aligning network management with business goals.
Device monitoring in network management
Device Posture Monitoring – understanding the state and security of all connected devices is crucial for a robust network environment, including:
Real-time assessment – monitoring device states in real-time, tracking factors like software versions, security patch levels, and endpoint configurations to determine their compliance with security policies.
Threat detection – identifying potential vulnerabilities through continuous device behavior surveillance and comparing them against established baselines. This allows for an immediate response to unusual activities.
Integration with security protocols – Ensuring devices connecting to the network meet specific compliance and security standards is crucial. This is achieved by integrating posture assessments with existing network access controls.
Automated remediation – to prevent potential security breaches, execute automatic actions to correct non-compliant devices, such as quarantining or patching.
Visibility and reporting – providing comprehensive visibility into the devices connected to the network and generating detailed reports for compliance tracking and security auditing.
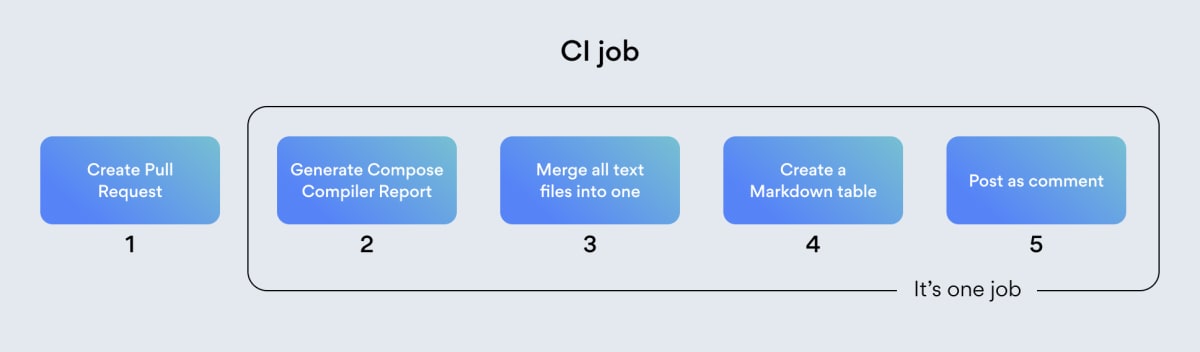
How NordLayer incorporates analytics for network visibility
NordLayer’s approach is all about simplicity. We offer a unified platform to manage your organization’s network from one central place. Different pieces of information give insights into varying elements monitored from a data perspective.
Here are the scenarios where NordLayer can come in handy when looking for an analytical angle of network performance.
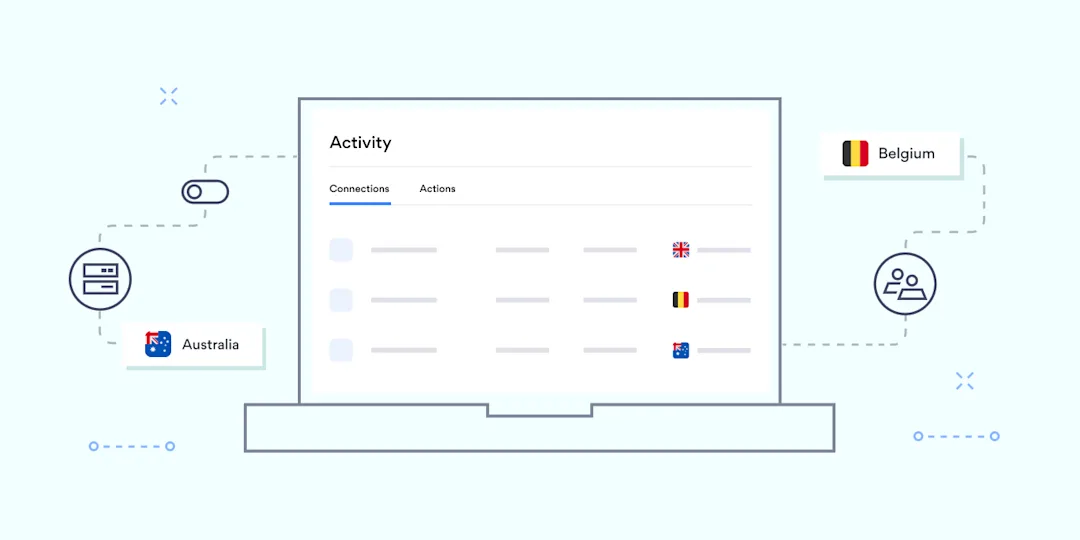
An overview of connections and actions: Activity monitoring
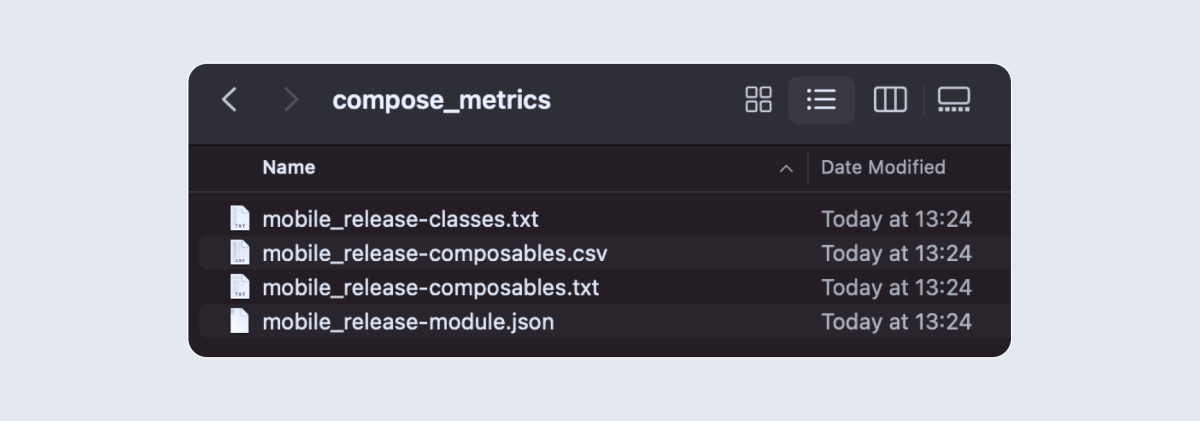
![]()
The network of a small company and a large enterprise needs to record every organization member to identify who has access to connect. It’s like a window into what’s happening within the network and how each element behaves at a surface level.
NordLayer’s Activity monitoring is a helpful functionality for admins. It allows organizations to not only identify a connected member but also have their details and session time to evaluate the tool’s usage.
From a user activity perspective, information like member name, device name, given ID number, and email helps spot any deviations in created user profiles. You can also track when members connect and disconnect from the network in a provided table, ensuring compliance with security policies.
The Activity monitoring also shows a list of admin’s actions, from creating gateways and logging in to enabling or enforcing specific features. It’s practical to track down what actions were performed retrospectively in case of an audit, procedure revision, or simply to avoid accidentally duplicate actions. The functionality supports troubleshooting, helping to find if single errors have affected the team level.
Admins can use an export capability to have all concise data in one place and use it for generating insights. The export capability allows downloading encrypted connection reports, often used for compliance audits and internal process reviews.
Track service performance: server usage analytics
Connection statistics help better understand bottlenecks and overloads of the company network. From the number of members to what servers they are connected to, it provides visibility to network managers to distribute teams more effectively.
Cramped servers lead to performance issues that impact your workforce’s productivity. Therefore, the data about service usage is crucial in future decision-making and establishing processes. NordLayer’s Insights tab in the Control Panel has interactive dashboards for server usage visibility.
The Insights tab provides a detailed data summary to analyze protocol connectivity patterns and see active sessions in a given time. The information available for protocol usage displays the company’s dedicated server metrics.
The active sessions dashboard lists data about the number of users connected to specific dedicated servers. It makes it easy for admins to analyze the distribution of connections and plan for potential future needs, such as additional dedicated servers.
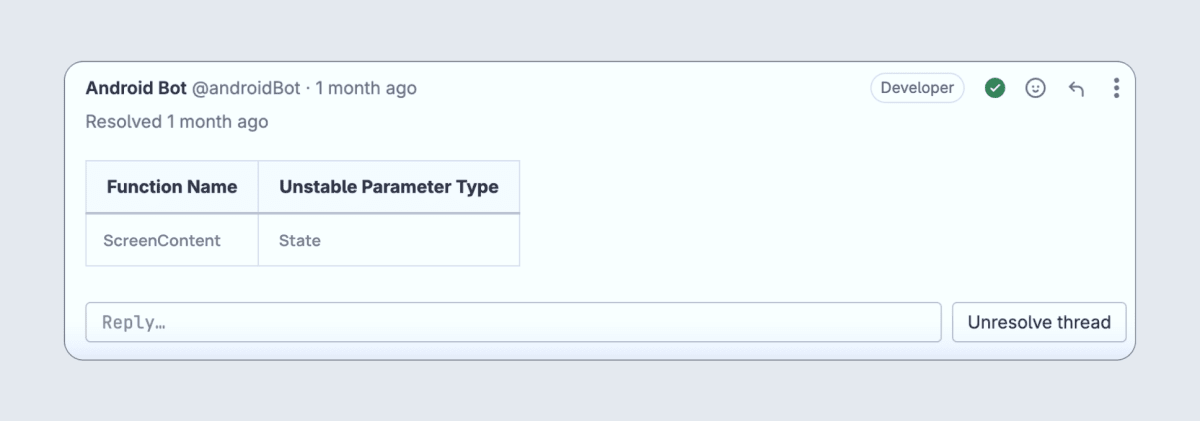
Maintaining a record of network activity: Device Posture Monitoring
Hybrid work and bring-your-own-device (BYOD) policies increase the risk of malicious connections.
Managing and gaining visibility into the devices within the network is challenging. You need to verify the identity of connecting individuals and ensure their connecting devices aren’t infected and don’t threaten the organization’s network.
NordLayer’s Device Posture Monitoring functionality addresses this challenge by accurately monitoring who connects to the company network based on predefined rules. The feature is convenient for registering deviations from established norms.
Device Posture Security allows admins to define periodical device check rules listed below.
Enabling a list of organization admin-trusted devices.
Defining a preferred OS and its version.
Specifying the supported NordLayer app version.
Enforcing checks if the device is jailbroken or rooted.
Confirming that the device contains a specific file.
Checking for an allowlisted IP address on the device.
The functionality improves the admin’s visibility of a device’s compliance with internal policies and its up-to-date status. To increase actions based on the Zero Trust framework, the functionality provides information about access, device health, and activity data for devices in the organization.
Benefits of network visibility features
Having data and knowing what to do with it offers substantial benefits for organizations. By offering a panoramic view into the complex labyrinth of connections, server usage, connected devices, and their security posture, network visibility features not only enhance the control and management of the network but open doors to numerous advantages.
Additional security
Network visibility allows organizations to monitor and analyze network traffic effectively. By observing network behavior, IT admins can detect and respond to security threats. This approach helps identify suspicious activities or unauthorized access attempts.
Network performance
Insights into the network enable understanding and optimization. It assists with the identification of bottlenecks, congestion, latency issues, and network failures. Better network management enables a landscape where data informs and empowers, leading to a smarter, safer, and more efficient work environment.
Troubleshooting
Detailed insights provide information to make troubleshooting and resolving issues easier, thus saving time. When problems occur, IT admin can use all of these capabilities to analyze traffic patterns and pinpoint the source of the problem.
Embracing the future with advanced network visibility
As the digital landscape expands, the importance of a transparent, secure, and efficient network cannot be emphasized enough. With tools like NordLayer, organizations can confidently navigate this evolving terrain.
NordLayer showcases the future of network management, where data doesn’t just inform but empowers growing businesses that face increasingly complex network challenges. Embracing advanced analytics and visibility tools is not just a luxury—it’s a necessity.
Share article
Copied
Copy failed
Genetic data leak, 23andMe point to credential stuffing
Hackers are selling genetic data stolen from users of the company 23andMe. The company itself says they weren’t breached, although their users’ data was used by what seems to be a single threat actor stealing personal details and genetic data. This data was then published or advertised online. 23andMe suggested that the threat actor(s) gained unauthorized access with “recycled login credentials”, a technique known as credential stuffing.
The logic is simple: Keep trying stolen username/password combinations, and eventually, they’ll work on another site. An easy solution to credential stuffing attacks? You guessed it: Multi-factor authentication (MFA). While 23andMe has offered an MFA feature since 2019, it was not made mandatory for users. With genetic and personal data at stake and up to 7 million users affected by these recent breaches, it might be time for a change in policy.
The Bleach Breach: Clorox revenue and supply chain hit
Clorox, the household cleaning giant, predicts a more than 20% drop in quarterly sales due to a cyberattack (thought to be ransomware) that caused product shortages and operational disruptions. Manufacturing, often kept running by legacy systems and sprawling workforces, suffers more cyberattacks than any other industry.
The Clorox incident is being linked to the same group responsible for the MGM and Caesars Palace hacks, discussed in our previous episode, which occurred around the same time in August 2023. “Scattered Spider” is notorious for using social engineering methods to gain access to internal systems. The Clorox Company’s share price has dropped by over 7 percent in the last month.
Wearable AI: Trendy or just trending?
Tech companies are rushing to secure the lead in wearable AI products. Meta has collaborated with Ray-Ban on a pair of high-tech glasses, enabling wearers to live stream directly from the glasses to Facebook or Instagram and voice activate Meta AI, “an advanced conversational assistant”. Jony Ive, Apple’s legendary former design lead, and OpenAI are reportedly teaming up to design the “iPhone of AI”.
Rewind.ai unveiled a neck-worn pendant that records conversations to your smartphone and creates a searchable database of life moments. Humane, imagining “a world where you can take AI everywhere”, have developed a smart device that resembles a badge or lapel pin.
The common goal here seems to be for technology to rely less on screens, to fade from view, and become all but invisible.
Stay tuned for the next episode of Cyberview.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.