Cybersecurity teams stand as the unsung heroes of every organization. These dedicated professionals are at the forefront of defending their company’s digital infrastructure, tirelessly monitoring security alerts to prevent and mitigate potential threats. However, with the ever-expanding landscape of cyber threats, these defenders are facing a new adversary: security alert fatigue. As the sheer volume of security alerts escalates, experts are rallying to find innovative ways to reduce alert fatigue and ensure that no genuine threat goes unnoticed.
The Peril of Security Alert Fatigue
Picture this: a cybersecurity analyst staring at a wall of screens, each flashing with a seemingly endless stream of security alerts. In an environment where the number of alerts can easily number in the thousands per day, it’s no wonder that many analysts experience alert fatigue. This phenomenon occurs when the sheer volume of alerts overwhelms the human ability to respond effectively. As a result, fatigue sets in, causing analysts to become desensitized and potentially miss critical indicators of a breach (not to mention generally burned out).
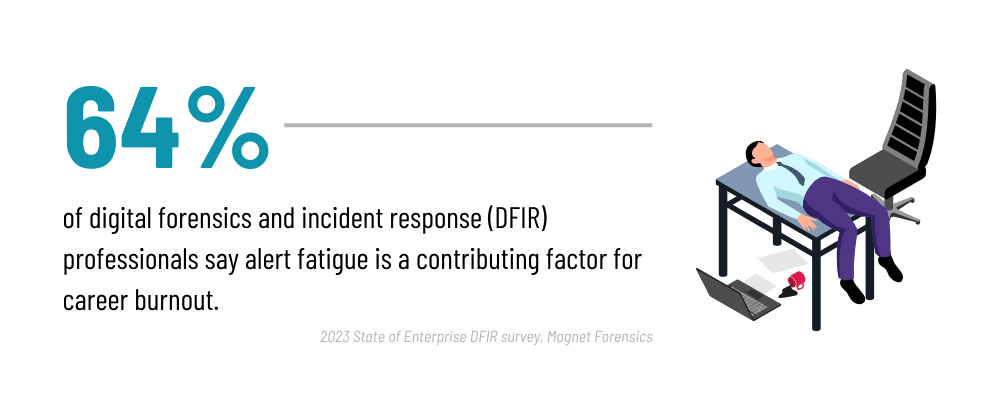
Alert fatigue can have dire consequences. Missed alerts mean that potential threats might go unchecked, giving cybercriminals a window of opportunity to exploit vulnerabilities and cause significant damage. In the worst-case scenario, it can lead to massive data breaches, financial losses, and irreparable reputational damage.
The Deluge of Alerts: A Growing Challenge
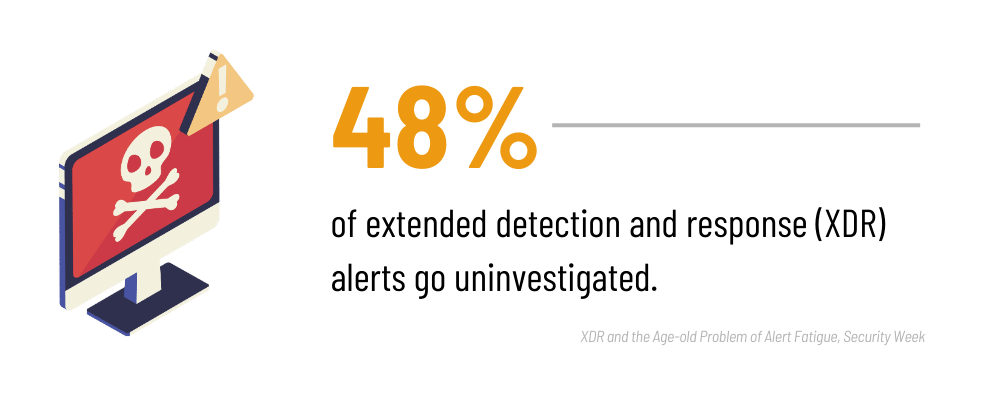
The information technology landscape has evolved significantly in recent years, giving rise to increasingly complex cyber threats. As organizations adopt more sophisticated security measures, cybercriminals respond by devising more intricate and subtle attacks. This arms race has led to a surge in the number of security tools and systems deployed, generating a corresponding flood of alerts.
From intrusion detection systems to firewalls, each layer of defense generates its own set of alerts. Multiply this by the various devices and applications within an organization, and it becomes clear why cybersecurity teams are grappling with alert overload. This not only strains human resources but also taxes the efficiency of the entire cybersecurity apparatus.
A Multi-Faceted Approach to Tackling Alert Fatigue
Addressing security alert fatigue requires a multi-faceted approach that combines technological advancements, process optimizations, and human-centered strategies.
I. Automation and AI
Leveraging automation and artificial intelligence (AI) is crucial in filtering out noise and identifying patterns in the deluge of alerts. Machine learning algorithms can be trained to differentiate between routine events and potential threats, reducing the number of false positives that analysts need to sift through.
II. Contextualization
Providing analysts with contextual information about alerts can significantly enhance their ability to prioritize and respond effectively. Integrating threat intelligence feeds, historical data, and asset inventory details can help analysts understand the potential impact of an alert and its relevance to the organization.
III. Consolidation and Integration
Rather than relying on a plethora of disparate security tools, organizations are adopting unified security platforms (*cough* like the Portnox Cloud *cough*) that centralize data and streamline alert management. This not only reduces the number of tools analysts need to monitor but also facilitates a more holistic view of the organization’s security posture.
IV. Tuning and Refinement
Regularly tuning and refining alerting thresholds can minimize false positives. This iterative process involves fine-tuning tools to align with the organization’s specific network and application behaviors, ensuring that only meaningful alerts are escalated.
V. Human Factors
Recognizing the pivotal role of human analysts, organizations are taking steps to alleviate the mental strain of constant alert monitoring. Implementing shift rotations, providing opportunities for skill development, and fostering a supportive work environment can help combat burnout and maintain analysts’ vigilance.
VI. Incident Response Plans
Having well-defined incident response plans in place can help analysts navigate high-stress situations with clarity and confidence. Knowing the precise steps to take when a threat is confirmed reduces uncertainty and facilitates a more coordinated and efficient response.
A Brighter Horizon
The battle against alert fatigue is an ongoing one, but with a concerted effort from cybersecurity professionals, organizations can reclaim their edge in the fight against cyber threats. By embracing a combination of technological advancements, procedural refinements, and a deep understanding of human factors, the cybersecurity community is paving the way for a more effective and resilient defense.
As cyber threats continue to evolve, cybersecurity teams must evolve with them. This includes not only staying updated on the latest attack vectors but also ensuring that the mechanisms in place to detect and respond to these threats are as robust as possible. By addressing alert fatigue, organizations can fortify their digital defenses, protect sensitive data, and ensure a safer digital future for all.
In a world where a single missed alert can have far-reaching consequences, the efforts to reduce alert fatigue are not just about technology—they’re about safeguarding the very foundations of our interconnected world. As cybersecurity teams rise to this challenge, their triumph over alert fatigue will undoubtedly be a beacon of security and resilience for years to come.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Portnox
Portnox provides simple-to-deploy, operate and maintain network access control, security and visibility solutions. Portnox software can be deployed on-premises, as a cloud-delivered service, or in hybrid mode. It is agentless and vendor-agnostic, allowing organizations to maximize their existing network and cybersecurity investments. Hundreds of enterprises around the world rely on Portnox for network visibility, cybersecurity policy enforcement and regulatory compliance. The company has been recognized for its innovations by Info Security Products Guide, Cyber Security Excellence Awards, IoT Innovator Awards, Computing Security Awards, Best of Interop ITX and Cyber Defense Magazine. Portnox has offices in the U.S., Europe and Asia. For information visit http://www.portnox.com, and follow us on Twitter and LinkedIn.。




