In today’s digital landscape, organizations are increasingly adopting multi-cloud strategies to harness the benefits of multiple cloud service providers. However, with this approach comes the crucial need for robust security measures to protect valuable digital assets across diverse cloud environments.
This article provides readers with a deep understanding of multi-cloud security, shedding light on its importance and exploring the essential measures to ensure comprehensive protection.
What is multi-cloud security?
Multi-cloud security refers to the practices, technologies, and policies employed to secure data, applications, and infrastructure deployed across multiple cloud environments. It involves safeguarding digital assets against various threats and ensuring data confidentiality, integrity, and availability while complying with industry regulations.
Organizations adopt a multiple-cloud approach, utilizing various service providers simultaneously, including public, private, or hybrid clouds in a multi-cloud setup. The flexibility, scalability, and resilience offered by multi-cloud architectures are attractive, but they also introduce unique security challenges that demand specialized security strategies and controls.
A quick check on definitions
☁️ Multi-cloud security refers to the protection and safeguarding of data, applications, and infrastructure across multiple cloud service providers. It involves implementing security measures and practices to ensure the confidentiality, integrity, and availability of digital assets in a multi-cloud environment.
☁️ The aim of multi-cloud security is to safeguard data confidentiality, integrity, and availability while maintaining compliance with regulatory requirements.
Multi-cloud security challenges
Operating in a multi-cloud environment introduces safety challenges that organizations must address effectively. Some common security risks in multi-cloud environments include:
Data breaches and unauthorized access
Multiple entry points across various cloud platforms increase the risk of data breaches and unauthorized access attempts, which can lead to significant financial losses, reputational damage, and legal consequences.

![]()
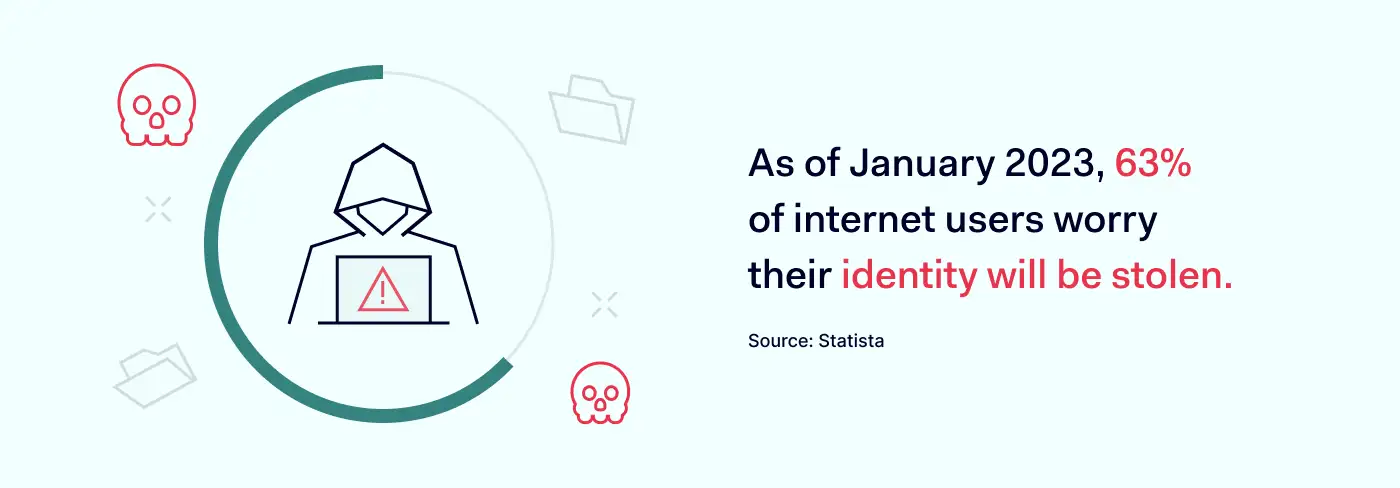
Account hijacking and identity theft
Attackers may target user credentials, exploiting vulnerabilities in authentication mechanisms to gain unauthorized access to sensitive information. Account hijacking and identity theft pose serious threats to the confidentiality and privacy of organizational data.
DDoS attacks and network vulnerabilities
Distributed Denial of Service (DDoS) attacks can disrupt cloud services and cause downtime, impacting business operations. Network vulnerabilities within cloud environments can also be exploited to compromise critical systems and infrastructure.

Data loss and corruption
Multi-cloud setups involve data replication and synchronization across multiple platforms, increasing the risk of data loss or corruption. Technical issues, human errors, or malicious activities can result in permanent data loss or compromise integrity of data security.

![]()
Compliance and regulatory concerns
Organizations operating in regulated industries must ensure compliance with industry-specific regulations and standards across multiple cloud environments. This becomes complex when dealing with different cloud providers and their specific security requirements.

![]()
Multi-cloud security best practices
To mitigate the risks associated with a multi-cloud environment, organizations should adopt the following best practices:
1. Implement a comprehensive security multi-cloud architecture. Develop a robust security architecture that spans across all cloud environments, including network security, access controls, encryption, and threat detection mechanisms.
2. Adopt a defense-in-depth approach. Implement multiple layers of security controls, such as firewalls, intrusion detection and prevention systems (IDPS), and security information and event management (SIEM) solutions. Security monitoring strategy is helpful for securing public cloud and private cloud data.
3. Leverage automation and orchestration. Automate security processes and leverage orchestration tools to ensure consistent, scalable, and efficient management of security controls across diverse cloud platforms. Using compatible Identity and Access Management (IAM) providers for access management and controls facilitates automation processes.
4. Monitor and detect anomalies. Implement real-time monitoring and threat detection mechanisms to promptly identify and respond to security incidents. Continuous monitoring helps detect unauthorized activities, data breaches, and potential vulnerabilities to lower the likelihood of multi-cloud security challenges.
5. Encrypt data and implement key management. Encrypt sensitive data at rest and in transit to ensure its confidentiality. Establish secure key management practices to safeguard encryption keys and control access to the encrypted data.
6. Regularly update and patch systems. Deploy a security monitoring strategy to ensure timely updates and patches for cloud infrastructure components, applications, and security tools and address known vulnerabilities.
7. Educate and train employees. To onboard a multi-cloud security solution is half-job done. Conduct regular security awareness training to emphasize the importance of secure cloud usage and best practices. Promote a culture of security consciousness to empower employees to identify and report security threats.
By implementing these best practices, organizations can enhance their multi-cloud security posture, minimize vulnerabilities, and protect their digital assets from evolving cyber threats in the complex multi-cloud landscape.
Benefits of a multi-cloud strategy
While multi-cloud security presents its own set of challenges, adopting a multi-cloud strategy offers several benefits to organizations. Some of the key advantages include:
Flexibility and vendor independence
By leveraging multiple cloud service providers, organizations have the flexibility to choose the best services and features from each provider. This reduces vendor lock-in and enables companies to customize their cloud infrastructure based on specific requirements.
Improved performance and reliability
Distributing workloads across multiple cloud platforms helps enhance performance and reliability. Organizations can optimize their infrastructure by selecting cloud providers that offer the best geographical coverage, network capabilities, and service-level agreements (SLAs) for their specific needs.
Scalability and elasticity
Multi-cloud environments provide scalability and elasticity, allowing organizations to scale resources up or down based on demand easily. By leveraging the resources of multiple cloud providers, organizations can ensure they have the necessary capacity to meet fluctuating workloads without service disruptions.
Disaster recovery and business continuity
Adopting a multi-cloud strategy strengthen disaster recovery and business continuity capabilities. Organizations can replicate data and applications across different cloud platforms, ensuring redundancy and resilience in the event of a cloud service outage or disaster.
Cost optimization
Multi-cloud strategies help organizations optimize costs by selecting the most cost-effective cloud services for different workloads. Organizations can efficiently manage their cloud expenditures by leveraging competitive pricing models, discounts or promotions from various cloud providers.
How to choose the right multi-cloud vendor?
Selecting an appropriate multi-cloud vendor is a critical decision that impacts an organization’s security and overall cloud strategy. Consider the following factors when evaluating potential multi-cloud vendors:
Security capabilities: Assess the vendor’s security measures, including data encryption, access controls, threat detection, and incident response capabilities. Ensure alignment with your organization’s security requirements and compliance standards.
Integration and interoperability: Evaluate how well the vendor’s services integrate with your existing systems and applications. Consider the vendor’s compatibility with industry-standard APIs, tools, and technologies for smooth interoperability.
Scalability and performance: Examine the vendor’s ability to scale resources and handle increasing workloads. Evaluate their network capabilities, geographical coverage, and SLAs to ensure they can meet your organization’s performance and scalability requirements.
Cost structure: Compare pricing models, including pay-as-you-go, subscription-based, and reserved instances, to find the most cost-effective option. Evaluate the vendor’s pricing transparency, potential hidden costs, and the availability of cost optimization features.
Vendor reputation and support: Research the vendor’s reputation, reliability, and customer support services. Read reviews, seek recommendations, and evaluate the vendor’s responsiveness to customer inquiries and support requests.
How can NordLayer help?
NordLayer, a leading provider of cloud network security solutions, offers comprehensive features to address the security challenges of multi-cloud environments. NordLayer’s solutions include
Secure network connectivity: NordLayer provides secure and encrypted network connections between cloud environments, ensuring data integrity and confidentiality.
Centralized security management: with NordLayer’s centralized management console, organizations can efficiently monitor and manage security policies across multiple cloud platforms, simplifying the security administration process.
Zero Trust Network Access (ZTNA): NordLayer’s ZTNA, based on the Zero Trust approach, enables organizations to implement precise access controls and authenticate users and devices before granting network access, reducing the risk of unauthorized entry.
Threat detection and response: NordLayer employs advanced threat detection and response mechanisms, using machine learning to identify and mitigate potential security incidents in real-time.
Compliance and regulatory support: NordLayer assists organizations in meeting compliance requirements by offering features like data encryption, secure access controls, and audit logging to ensure regulatory adherence.
By leveraging NordLayer’s robust multi-cloud security solutions, organizations can enhance their security posture and protect their digital assets across diverse cloud environments effectively.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.




