
Jira’s cloud-hosting solutions serve major corporate giants like the Coca-Cola Company, Delta Airlines, and CostCo. Every day, millions of people rely on Jira to access development apps and collaborate with colleagues. But Jira deployments require watertight security. Companies can easily fall victim to cloud data theft. This can inflict reputational damage or – in worst-case scenarios – lead to bankruptcy.
This article will explore how to secure your Jira assets. We will look at best practices for Jira security and learn how shared responsibility works. We will also explain some of the most urgent cloud security threats. The result will be a solid foundation in Jira cloud security.
Understanding the significance of Jira security
Cloud platforms are critical to the modern economy. The cloud hosts websites, customer databases, development environments, and collaboration tools. Lightweight cloud tools also dramatically lower networking costs. This makes it easier to create customized business architecture.
Operated by Atlassian, Jira is a cloud-hosting service known for supporting agile network deployments. Its development tools suit rapidly changing companies and scale smoothly. But as with all major cloud platforms, Jira is a tempting target for cyber attackers.
Jira security is shared between the cloud provider and customers. As we will see, Jira has many native security features that guard customer data. But customers retain responsibility for:
Access management
Endpoint security
Application installation and management
Protecting customer data
Jira security best practices
Jira security aims to protect sensitive data stored on the cloud platform. Users (or “tenants”) must minimize data breach risks while understanding security areas covered by Jira’s systems. This checklist covers actions required to secure Jira environments.

 Security best practices include:
Security best practices include:
Verifying your domains
Hardening your login security policies
Auditing activity logs intelligently
Managing accounts to minimize data breach risks
Training staff to use Jira securely
Making use of mobile security tools
1. Verify and claim Jira domains
The first step in improving your security setup is verifying the Jira domains you own. Domain verification allows administrators to take control of access management policies for Jira assets. Admins can claim domains via the Atlassian admin panel.
Domain verification also enables admins to use Atlassian Access. After verifying their domains, admins need to subscribe to Access. When that’s done, you can start applying security controls across your Jira-hosted assets.
2. Harden login security policies
Login portals are a critical security vulnerability. Jira tenants must exclude malicious actors while allowing legitimate requests. This is not always an easy balance to strike. Users should:
Implement two-factor authentication
2FA requires more than one authentication factor when logging on. Atlassian supports popular authentication providers like Google Authenticator and Authy. These tools integrate with Jira and deliver secure passcodes to smartphones. SMS verification is also possible, although it’s seen as a less secure option.
Enforce two-step verification
This tool supplements 2FA for Jira. Enforced verification makes it impossible to access Jira assets without supplying two authentication factors. Admins configure enforced verification via the centralized access management panel.
Create SSO portals
Single Sign On combines all Jira cloud assets via a single set of credentials. SSO integrates smoothly with identity providers. You can transfer existing directories and groups to Jira while adding authentication tools.
Prevent third-party access
Access requests from third-party cloud platforms presents a security risk. Restricting access requests from Slack, Google Cloud, or Apple platforms is a good idea. Enforce additional authentication procedures to prove user identities before granting access.
Use strong passwords
Admins must require solid passwords for all accounts. Strong passwords feature a mix of characters and numbers and are usually between 12 and 15 characters long. This makes them very difficult to guess or brute force. Admins should also set password expiry deadlines that force users to change passwords regularly.
Exclude non-human users from authentication policies
Bots and API service accounts may require access to Jira assets. But they do not require the same authentication processes. Admins should configure these users to remove SSO and two-step verification tools.
3. Audit activity logs intelligently
Product audit logs record activity across the Jira environment. This makes it possible to detect patterns of suspicious behavior and remediate network security vulnerabilities before threats emerge.
Atlassian operates separate audit processes for Confluence and Jira. In both cases, companies can track any changes made to their cloud setup. Tenants can determine which events to monitor. This includes group creation, data imports and exports, deletions, and changes to global settings.
By default, logs are kept for one year. Tenants can change this setting, reducing the audit period to as little as one month. However, retaining audit data for the maximum period is a security best practice. This will deliver more actionable insights to improve security settings.
4. Manage accounts to minimize data breach risks
Jira tenants should audit both activity and user accounts. Account audits look at the entire range of active user accounts. And they perform a couple of important security tasks:
De-escalation of administrative privileges when they are no longer needed.
Deletion of obsolete accounts. Without timely audits, user accounts may remain active after employees leave the organization. This creates a security risk and should be avoided if possible.
Carry out account audits regularly. Integrate external identity providers covered by Jira, such as SCIM or G Suite. This makes it easier to automate user provisioning and deletion tools. But do not assume that orphaned accounts have been deleted. Check thoroughly and make deletions as necessary.
5. Train staff to use Jira securely
Security teams are responsible for educating all Jira users. Solid training teaches employees to follow security best practices and should be critical to your cloud security policy. Training issues to focus on include:
The importance of strong, regularly-changed passwords.
Eliminating confidential data from Jira tickets or pages. This could include cardholder data or personal health information.
Creating access controls for any pages that contain sensitive information.
Using two step-verification to access Atlassian products.
Using API tokens to access Confluence Cloud or Jira resources.
Avoiding phishing attacks related to the Atlassian cloud environment.
Schedule regular training events and log the participation of all cloud users. Include additional security training for administrative-level account holders. Admins have extensive powers to change global settings that regular users lack. Enforce prohibitions against shared admin accounts and reinforce the need for strong password security.
6. Make use of mobile security tools
Employees may require access from home workstations, industry events, or during global travel. But mobile access carries security risks. In these situations, companies should leverage the mobile security features supplied with Jira software.
Atlassian Access allows tenants to create Mobile Application Management (MAM) policies. This is a good option if your organization relies on either work-from-home or bring-your-own-device (BYOD). MAM policies should:
Enforce multi-factor authentication for remote access to the Atlassian cloud.
Check that devices have anti-malware protection and that the operating system is up to date.
Allow only authorized BYOD devices and require registration for new devices.
Mandate encryption for all remote connections. This could include Virtual Private Network connectivity or the use of other forms of secure gateway.
If you are not an Atlassian Access member, you can integrate external MDM solutions with Jira deployments. Jira software supports Microsoft Intune, JAMF, and MobileIron. It should be possible to transfer existing MDM settings directly to the Atlassian cloud.
Understanding Jira security basics
It is important to apply the security best practices outlined above. But Jira tenants must also understand what their cloud provider secures before taking action. There is no need to duplicate security measures. Tenants should be aware of tools available within the Jira platform before sourcing external solutions.
Atlassian is vocal about its commitment to security, and the company builds both internal and client-side security features into its products. Let’s start with client-side features that tenants can control.
Client-side features:
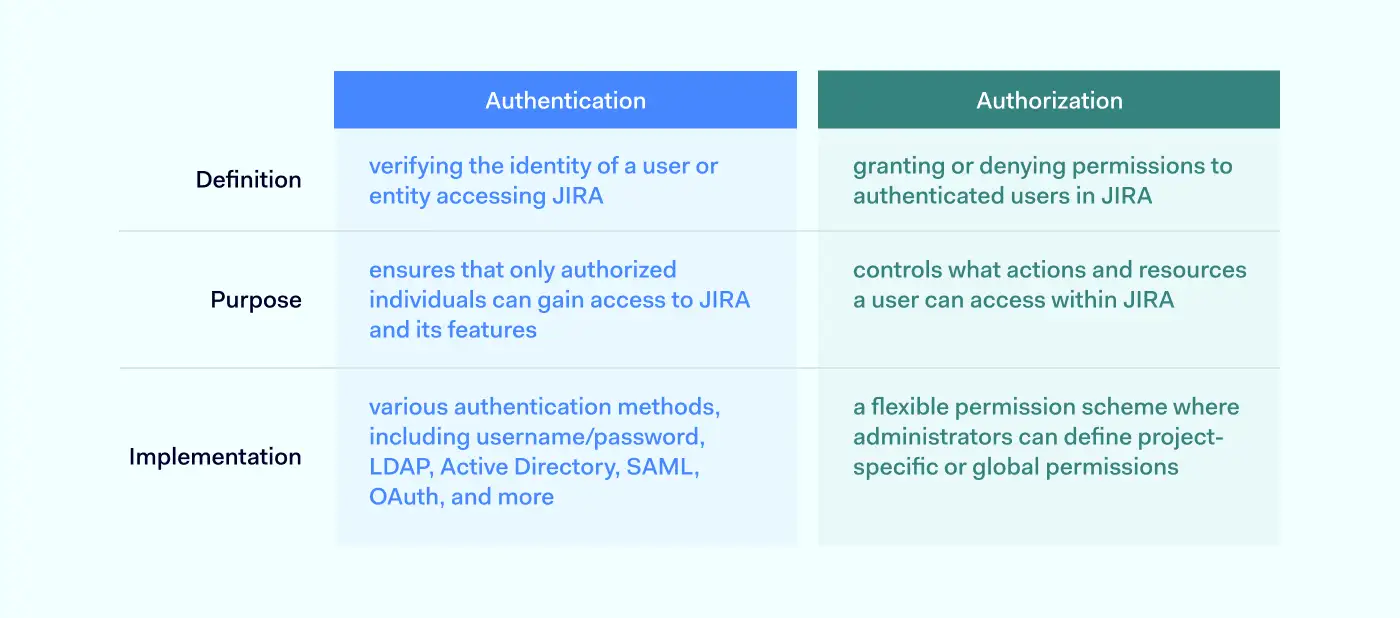
Authentication
Authentication verifies the identity of every user accessing the cloud environment. These mechanisms compare user credentials to secure directories. If supplied credentials match the database, the network grants access. Jira authentication options include Basic Authentication via Atlassian Account. However, Jira also supports OAuth tokens, which offer more security. These secure tokens add an extra layer of protection against illegitimate access.
Authorization
Authorization determines what users can do within the Jira environment. Each user receives a set of permissions. These permissions grant access to resources according to the user’s role and work requirements. Admins can create temporary groups or assign precise powers to users. For instance, the user could possess create, view, and edit privileges. But they may not be able to delete records on Jira apps.
Logging
Jira logs key activities and presents the data via the central administration console. The audit log captures project changes, user permissions, workflow changes, custom fields, data deletion, and suspicious access requests. Admins can export audit data via CSV files and amalgamate the information with other cloud platforms. Retention periods vary from one month to a year.
Incident management
Jira’s incident response systems include collaboration tools, automated alerts, incident timelines, and incident response templates. Tenants can plan to neutralize threats and restore systems as quickly as possible.
Internal security features:
Atlassian products secure hosting infrastructure with internal security controls. In keeping with the shared responsibility model, the company undertakes to ensure the “security, availability, and performance of the applications we provide, the systems they run on, and the environments within which those systems are hosted.”
Encryption
Jira encrypts data at rest and in transit. Data on the Rest API is encrypted using 256-bit AES ciphers. Data in transit is secured by TLS 1.2+ with perfect forward secrecy. Passwords are also encrypted, along with API keys. Tenants don’t need to apply encryption to data hosted on the Jira platform. But it is necessary to encrypt data passing across the network edge, for example, via remote work connections.
Zero Trust architecture
Jira’s network is constructed in line with the Zero Trust principle “never trust, always verify”. Private cloud routing, firewalls, and software-defined networking create secure zones. A three-tier access policy ensures that only authorized employees can access network resources.
Data center security
Atlassian uses Amazon Web Services (AWS) to store data. Redundancy and failover are built into a global AWS architecture. Multiple physical security controls also guard Jira’s data centers against malicious intruders.
Common security threats to Jira
Jira’s cloud hosting services face many threats. Security controls should always be designed with threats in mind. Any of these threats could result in loss of data, system downtime, and regulatory penalties:
Insider threats
Malicious individuals exploit legitimate access rights to carry out illegal actions. But insiders can also be unaware of the risks they pose. For example, employees might accidentally introduce malware via flash drives. Insiders can sabotage assets or steal data for sale. But identifying them isn’t easy. Jira tenants can leverage activity monitoring logs to detect unusual access patterns, off-board orphaned accounts, and apply MFA to make access difficult.
Social engineering
Also known as phishing. Social engineering involves persuading legitimate users to carry out risky actions. This could include opening attachments, clicking links, or even providing payment data directly. Training is the best remedy for social engineering attacks. Data Loss Prevention tools and tight access policies also help to prevent illicit data removal.
External threats
Malware can spread throughout insecure cloud deployments. Worms and Trojans leak information to outsiders. Other agents damage performance by leaching network resources for other purposes. Robust threat detection systems, network segmentation, and regular software updates are essential.
Data breaches
Data breaches require a specific strategy because the risks of suffering data loss are critical. Tenants should secure confidential data with encryption at rest and in transit. Limit access with MFA and RBAC. And track critical data via audits and threat alerts.
FAQ
How to keep my organization secure?
Follow these basic steps to secure your organization on Atlassian’s Jira platform:
Understand your Jira landscape. Inventory all apps and classify data held on Jira according to risk categories.
Ensure all assets are visible via the Atlassian admin panel.
Integrate your identity provider with Atlassian’s SSO solution.
Test configurations to balance access and security.
Create role-based access controls. Limit access to high-risk data.
Schedule regular audits and monitor activity logs.
Manage user accounts and remove users when they leave the organization.
Train your staff on security best practices.
Create a mobile device management solution for secure remote work.
What are the security features of Jira?
Jira is equipped with many security features. Use relevant features to secure cloud assets under the shared responsibility model. Tenants can configure Jira to include:
256-bit at rest encryption of sensitive data and TLS encryption for data in transit.
Flexible access controls. SSO and MFA options that integrate with identity providers.
Regular network scanning and audits of Jira infrastructure. Constant monitoring for cloud security threats.
Compliance with major standards such as GDPR and ISO 27001.
The Bug Bounty program rewards developers who find security weaknesses.
Secure development under the Peer Review/Green Build system. Testing of all new app deployments before they go live.
Atlassian has covered the most crucial security themes. But this still leaves customers with the responsibility to extend access controls to users, encrypt data outside the Jira environment, and train staff to use the cloud safely.
Key takeaways
Jira provides a wide range of security features to assist cloud tenants. This includes authentication systems that integrate easily with identity providers.
Automated user provisioning offers users the right permissions to access essential resources.
Tenants benefit from data encryption and proactive threat monitoring. Jira tools include customized audit processes and security alerts.
Cloud users must always be aware of the shared responsibility model when designing security solutions.
How can NordLayer help?
The Atlassian suite enables businesses to manage projects of varying scope and complexity effectively, but its security leaves much room for improvement. This is where NordLayer can reach out a helping hand to companies that are struggling to find the right balance between ease of use and security.
Using Virtual Private Gateways, network administrators have much better control over user access. Only gateway-connected users are allowed to reach the Jira portal. The login to NordLayer itself can be further secured by enabling Single-sign on and multi-factor authentication, ensuring that the connecting user’s identity is genuine.
With IP allow-listing (whitelisting), companies can permit access to Atlassian suite only from trusted IPs, which also shrinks the attack surface. The connections from unrecognized IP addresses are immediately blocked.
NordLayer’s suite of ZTNA and SSE-focused features allows additional layers of security and combines built-in Jira security tools with NordLayer’s solutions. This combination is a sure way to improve SaaS access control.
Get in touch with us, and discover how to reap the benefits of Atlassian suite without putting your sensitive data at risk.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.




