The IBM Cost of a Data Breach 2022 report brought a lot of information that shows the importance of choosing a good cybersecurity project for your organization.
According to information extracted from this document which included interviews with more than 3,600 people working in companies that had their data violated, it was possible to find alarming conclusions.
First, 83% of the organizations surveyed suffered some kind of breach between March 2021 and March 2022. Also, 60% of these attacks increased prices for customers.
It has also been identified that 79% of critical infrastructure organizations have not implemented a zero-trust plan to prevent cyber threats, and 19% of violations occur due to a compromised business partner.
Faced with so many digital security gaps, it can be difficult to know where to start deploying a cybersecurity project. Therefore, we address this issue here. To facilitate your reading, we divided our text into topics. These are:
- About Cybersecurity
- Importance of Cybersecurity
- Cybersecurity Project: What Is It, and What Is Its Importance?
- What Are the Five Types of Cybersecurity?
- People, Processes, and Technologies: Crucial Elements for the Success of Every Cybersecurity Project
- Guidelines for Prioritizing Cybersecurity Projects within a Company
- Key Cyber Threats Faced by Companies
- About senhasegura
- Conclusion
Enjoy the read!
About Cybersecurity
When we talk about cybersecurity, we refer to a set of technologies, procedures, and methods used to prevent attacks on devices, programs, data, and networks, avoiding the activity of hackers and ensuring the privacy of a company’s data, which must be protected from insider and external threats and natural disasters.
However, accelerated by the Covid-19 pandemic, digital transformation has brought several vulnerabilities, such as those related to remote work. As a result, there was a significant increase in data leaks, phishing emails, and account invasions.
Importance of Cybersecurity
Currently, processes in companies are migrating to the online world due to digital transformation, which can “facilitate” the loss of information of great importance to a business.
Thus, organizations need to invest in cybersecurity in order to ensure their operations and prevent threats, such as malware, viruses, and phishing.
One should also be aware that malicious attackers have been improving their techniques over time, so it is increasingly challenging to maintain data security and avoid compromised business.
Another novelty is data protection laws, which have been holding organizations accountable for the exposure of sensitive information from their customers, employees, and business partners, generating million-dollar sanctions.
In practice, these legislations have several requirements to be respected in order to avoid accidental or intentional data loss.
That is, investing in a good cybersecurity project is the recommended measure to avoid inconvenience, financial losses, loss of credibility, and closure of companies.
Cybersecurity Project: What Is It, and What Is Its Importance?
Cybersecurity projects are aimed at promoting digital security within any company. Its importance lies in the possibility of avoiding cyber threats, such as hacker invasions. It also contributes to the fact that errors -whether deliberate or not, of employees or third parties – have fewer impacts on the organization and reduce the possibility of losses, such as: loss of data, credibility, millionaire sanctions imposed by data protection laws, which can even cause the end of a business. And in small companies, this is even more crucial: according to a Cisco study, 60% of organizations affected by a cyberattack shut down operations within 6 months of the incident.
What Are the Five Types of Cybersecurity?
There are five types of cybersecurity. These are:
- Critical Infrastructure Security;
- Application Security;
- Network Security;
- Cloud Security; and
- Internet of Things (IoT) Security.
Check out each of them in detail below:
Critical Infrastructure Security
What Is It?
When talking about critical infrastructure security, we refer to the area that contemplates the security of systems, networks, and assets in industries that are essential to ensure the security of a country’s economy, health, and public services. These sectors include the chemical, communications, utilities, energy, and financial industries.
What Are the Challenges?
A major challenge for critical infrastructure is the security issues its systems present versus the limited protection features.
Application Security
What Is It?
Application security is essential as these programs have increasingly become targets for hackers. It consists of practices adopted to make them more secure, which occurs during their development and then after their implementation.
What Are the Challenges?
Ensuring application security requires tracking all the tools developed for these applications. It is also important to be aware of the future needs of a company, which may require software aimed at a more complex infrastructure.
Network Security
What Is It?
Network security is a term that refers to hardware and software solutions, as well as procedures aimed at protecting the network and data against cyberattacks. In practice, this concept includes network analysis, application security, access control, and antivirus software, among other factors.
What Are the Challenges?
The main challenge of network security is to maintain protection in increasingly complex structures, with a large volume of cyber threats and several functionalities used in corporations, which also represent new problems.
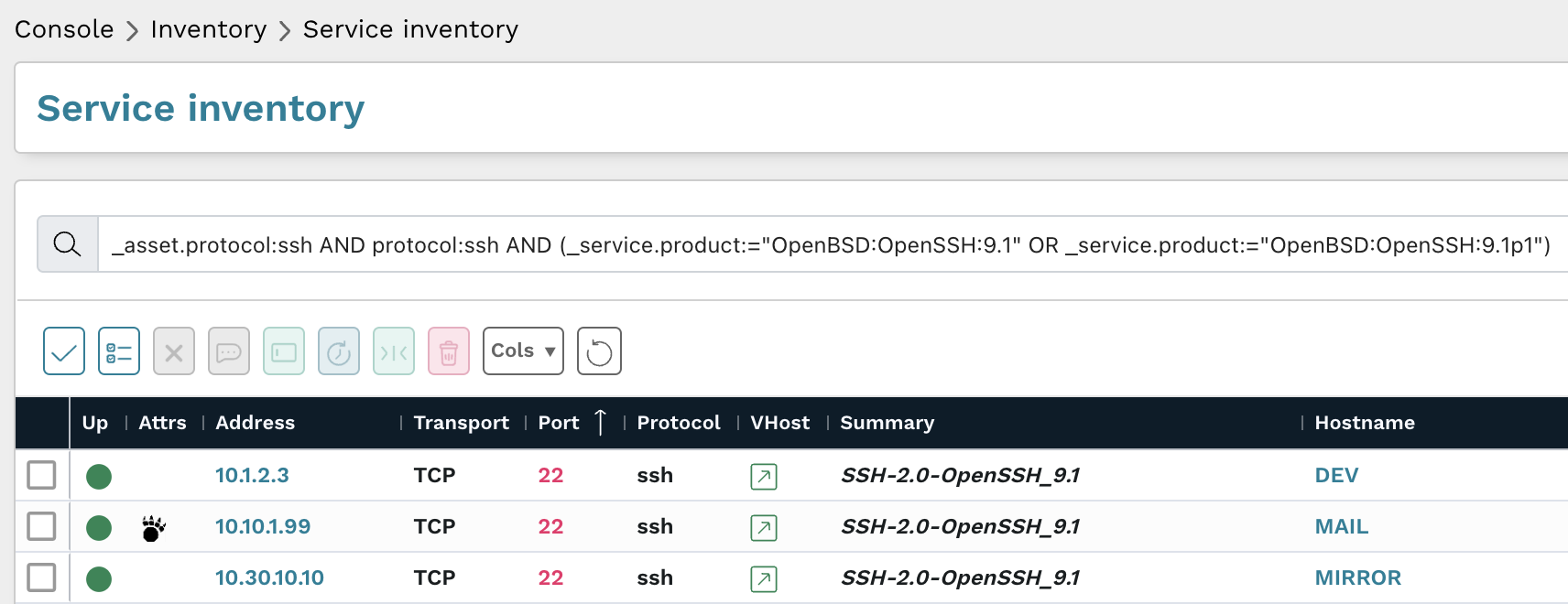
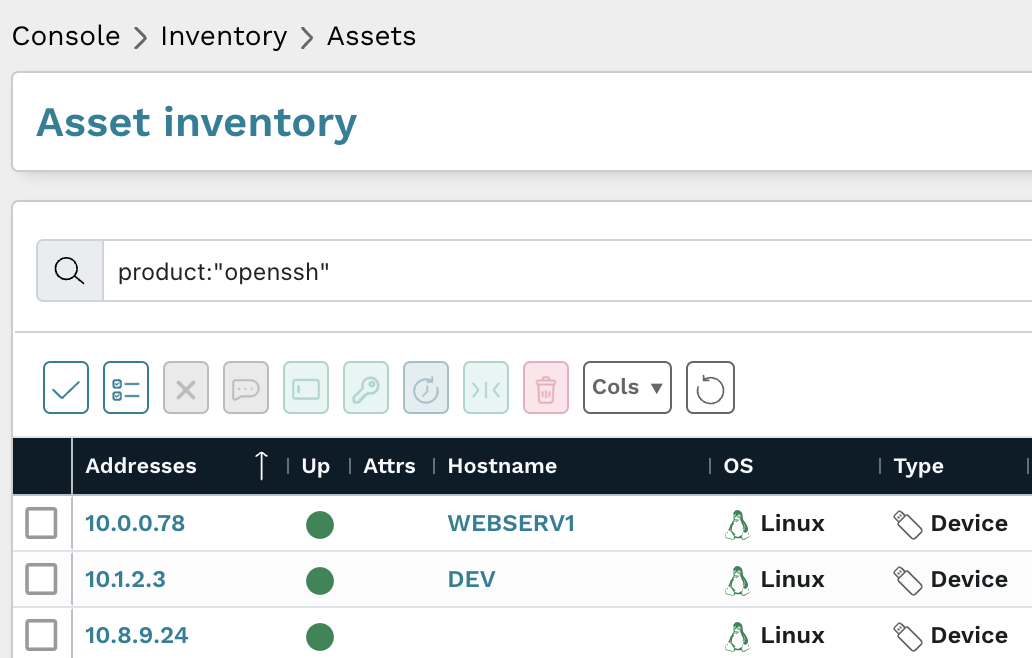
Cloud Security
What Is It?
As companies suffer the impact of digital transformation, they become more dependent on cloud solutions and need to adopt measures that ensure digital security in this context.
This is because outsourced providers may even be responsible for infrastructure management, but the accountability for any exposed data remains with the organization as well.
What Are the Challenges?
The challenges of companies adopting cloud solutions are related to the ability to meet security criteria in a dynamic environment, which can generate a lack of visibility in accessing and using data.
Internet of Things (IoT) Security
What Is It?
Internet of things security is associated with protecting devices connected directly to the cloud in gadgets, such as surveillance cameras. Its function is to protect designed devices, without taking into account aspects of cybersecurity and data protection.
What Are the Challenges?
The greatest challenge associated with the internet of things security refers to human activity. In practice, with the increased connectivity of these devices, it is necessary to instruct users on the change of default passwords and the need for updates, for example.
On the other hand, many users do not see these devices as targets of attacks and end up ignoring best security practices during their development and use.
People, Processes, and Technologies: Crucial Elements for the Success of Every Cybersecurity Project
An efficient cybersecurity project does not only involve the five types of digital security covered in the previous topic. It is also important to take other essential elements into account. They are: people, processes, and technology.
Here’s what you need to know about these aspects:
People
When it comes to cybersecurity projects, investing in cutting-edge technology is not enough. It is essential to train users to respect security protocols and ensure the protection of company data.
In practice, your employees increase security risks in a variety of ways.
Among them, we can highlight:
Clicking on URLs and Opening Suspicious Emails
It is necessary to make your employees aware of the risks involved in this practice and encourage the exclusion of emails from fake addresses to protect sensitive data.
Keeping the Same Password for a Long Period
To ensure the security of your company, employees’ passwords must be changed regularly. In addition, strong combinations should be used, and it is not recommended to reuse the same password in different services.
Due to the difficulty in memorizing so many passwords, we also recommend the use of a password vault, which will only require the memorization of a single code.
Personal Browsing
Many people use the devices of their companies for personal purposes, such as accessing social media, shopping, or paying bills. The big problem is that this behavior facilitates the work of malicious agents who want to collect information. Therefore, ask your employees to use their own devices, not corporate ones, for personal browsing.
Lack of Backups
Many people still fail to perform backups when finishing their tasks. Nevertheless, it is of paramount importance to back up the system files. So, employees should understand they need the help of the IT team with these functions.
Unattended Devices
Leaving devices on desks unattended and without blocking them is a fairly common practice, which can also cause damage to the security of a company. For this reason, it is essential to make employees aware of the importance of preserving data contained in these devices and maintaining their control.
Processes
Information security professionals use numerous processes to protect sensitive data. In practice, they need to identify and combat cyber threats, protecting information and responding to incidents.
Besides being implemented, these processes must be documented to save time and financial resources, and preserve customer confidence in cases of cyberattacks.
To counter cybersecurity-related risks, we recommend using the Cybersecurity Framework, developed by the National Institute of Standards and Technology (NIST) of the U.S. Department of Commerce, after former U.S. President Barack Obama signed an executive order in 2014.
Technology
After the deployment of security processes, it is indispensable to assess the tools available to avoid cyber threats.
For this, you must consider two types of technology: those that will help you prevent and combat attacks, such as antivirus, DNS filtering, and malware protection; and those that need protection, including computers, routers, and the cloud.
Previously, we could rely on security perimeters. Now, migration to cloud environments, remote work, and policies like Bring Your Own Device (BYOD) have made it easier for hackers to work.
Guidelines for Prioritizing Cybersecurity Projects within a Company
A cybersecurity project is essential to not overwhelm IT staff with unnecessary work and to ensure the company’s ability to deal with a cyberattack.
However, to create and run your cybersecurity project, you must take some action. They are as follows:
Understanding Your Company’s Goals
Each organization has its strategic goals, which should guide the creation of the cybersecurity project. Therefore, it is important to evaluate the company’s vision and its business and cybersecurity strategies.
This information will provide a basis for the development of the project and will be a guide to gradually know if it is, in fact, efficient.
To understand the strategic goals of the company, read documents related to the subject and talk to top management to know their priorities.
Discovering the Reason Behind the Project
Cybersecurity projects can be motivated by several reasons, although all of them need to prevent and combat cyber incidents in common.
In practice, the project can be an awareness and training campaign on cybersecurity, the implementation or updating of a security system, compliance with new laws and regulations, etc.
Understanding what the project’s motivation is will certainly contribute to establishing priorities, directly impacting the company’s operations.
Determining the Value of the Project
Here, when we talk about value, we are referring to the importance of a cybersecurity project for an organization. That is, it is convenient to analyze how it will impact stakeholders and what its real importance is to the business. A project that adds great value must necessarily be prioritized.
Analyzing the Urgency
It is important to assess the urgency of the cybersecurity project to determine whether it should be prioritized or can wait. But remember that priorities can and should be modified as changes occur.
Detailing the Aspects that Affect the Project’s Success
A successful cybersecurity project depends on a number of factors, including budgets, deadlines, and return on investment (ROI), among other things.
On the other hand, it is often impossible to execute a project due to unfavorable circumstances. Therefore, it is advisable to know what can affect the project’s success in advance.
Ranking the Cybersecurity Project According to the Priority
With the information on goals, objectives, and possibilities of success in hand, it is time to establish an order of priorities through an overall classification, which can be score-based.
Defining How Many Projects Can Be Executed at a Time
Probably, the organization will not be able to assume all priority projects at once. Thus, the solution is to work on them in a phased manner, creating a queue of plans to execute.
Another recommendation is to run the fastest ones first and then the ones that require more time and effort.
Sharing Findings with Top Management
Before starting the cybersecurity project, it is essential to meet with leaders and share the information gathered. This is because the findings can serve as insights to change the order of priorities of the projects, requiring top management to be on board.
Working Flexibly
Working with cybersecurity projects requires flexibility, after all, priorities can be modified according to context. By the way, this occurred in most companies after the beginning of Covid-19, which accelerated the mass adoption of remote work and brought new demands to security teams.
Key Cyber Threats Faced by Companies
The following are the main cyber threats that should be considered by a cybersecurity project:
- Ransomware;
- Phishing;
- Attacks on Mobile Devices;
- Attacks Using QR Codes;
- Denial-of-Service (DDoS) Attacks; and
- LotL and AVT Attacks.
See the detailed explanation of each of them below:
Ransomware
This type of cybercrime works like this: the attacker blocks a network or system and asks for millionaire amounts in exchange for the release of information, which may not be returned, but sold to other criminals. Due to the lack of efficient cybersecurity mechanisms in companies, this tactic is very common.
Phishing
Another common crime in the virtual environment is phishing, which consists of sending counterfeit emails, and pretending to be a legitimate organization. With this, malicious agents convince their victims to share personal information or take action to their benefit.
There are also some types of very sophisticated phishing attacks, such as very realistic audio recordings produced through artificial intelligence.
Attacks on Mobile Devices
With many people working remotely, the use of personal devices for corporate purposes and the use of corporate devices for personal purposes tend to occur more frequently.
This increases security vulnerabilities, especially in the face of malware attacks on devices.
Attacks Using QR Codes
Currently, cybercriminals use QR Codes to deploy malware applications, infecting their victims’ phones and stealing their bank details.
For this reason, it is advisable to check the code provided by the company before accessing it.
Denial-of-Service (DDoS) Attacks
This type of attack occurs when the hacker overloads a machine with traffic, disrupting its normal operation and making a service unavailable to users. In practice, the attack is performed through a single computer.
LotL and AVT Attacks
Less known, Living off the Land (LotL) attacks do not need to create malicious files to access a company’s systems because they use gateways that already exist.
Advanced Volatile Threat (AVT) attacks allow access to an organization’s data as quickly as possible.
About senhasegura
We, from senhasegura, are part of MT4 Tecnologia, a group of companies specializing in digital security, founded in 2001 and operating in more than 50 countries.
Our main objective is to ensure digital sovereignty and security for our clients, granting control over privileged actions and data and avoiding theft and leaks of information.
For this, we follow the lifecycle of privileged access management through machine automation, before, during, and after accesses.
These are also our commitments:
- Avoid interruptions in the activities of companies, which may impair their performance;
- Automatically audit the use of privileges;
- Automatically audit privileged changes to identify privilege abuses;
- Provide advanced PAM solutions;
- Reduce cyber risks;
- Bring organizations into compliance with audit criteria and standards such as HIPAA, PCI DSS,
- ISO 27001, and Sarbanes-Oxley.
Conclusion
In this article, you saw that:
- Cybersecurity is a set of technologies, procedures, and methods used to prevent cyberattacks;
- Digital transformation has brought new vulnerabilities to IT structures;
- Companies should invest in cybersecurity to prevent threats, such as malware, viruses, and phishing;
- Data protection laws hold organizations accountable for the exposure of sensitive information of their customers, employees, and business partners;
- Cybersecurity projects are aimed at promoting digital security within any company;
- There are five types of cybersecurity: critical infrastructure security, application security, network security, cloud security, and Internet of Things (IoT) security;
- People, processes, and technology stand out among the crucial elements for the success of a cybersecurity project;
- To define the priorities of cybersecurity projects within a company, one needs to understand the organization’s objectives, find out the reason for each project, determine its value, assess its urgency, detail aspects that interfere with its success, rank projects in order of priority, define how many projects it is possible to execute at a time, share the findings with top management, and work flexibly;
- The main threats faced by companies are ransomware, phishing, mobile device attacks, attacks using QR Codes, denial-of-service (DDoS) attacks, and LotL and AVT attacks.