Tor
You can say that Tor is an open-source, anonymizing, encrypted, volunteer-operated proxy network. It distributes your traffic over several layers (or relays) so that no single point can link you with your destination. Basically, you go through these relays before reaching that destination.
This helps you reduce the risk from both simple and more complex network analysis.
For example, installing the Tor browser on your client (Windows) machine will place a Socks5 proxy on it. You can configure it to push all the Internet traffic you want through that proxy – taking the same path.
Packets sent are encrypted and enter the Tor network encrypted; after that, they get bounced from node to node until they reach the exit node, where the packets get decrypted, and you arrive at your final destination – like Facebook. We call this a Tor circuit.
The example above takes the clear web into consideration. To access Tor’s hidden services, you need a .onion URL, a special URL required to access the Tor Darknet. Note that the exit node is not really required in this case, as you’re not leaving the Tor network; you’re going to a server that’s within the network.
This also means that your traffic will stay encrypted (end-to-end). The main idea about Tor here is that no individual relay (node) will know the complete path you’ve taken. In fact, the client negotiates a different set of keys for each hop within the Tor circuit. Thus, no hop can trace these connections as they are passing through.
There’s 10 minutes or so window for circuits (Tor uses the same circuit) where it will use the same circuit, but the later requests will be given a new circuit, keeping people from linking your previous actions to your later ones.
It’s important to note that Tor is not solving all the privacy and anonymity problems! Tor does not cover everything and is not a silver bullet, but it can be an extremely useful tool to help you protect your privacy and anonymity when configured correctly and when used in conjunction with other tools/layers that will keep your privacy and anonymity unscathed.
Tor utilizes the Diffie-Hellman handshake, which is used to establish the session keys (I mentioned above that the client negotiates different keys for each node); Diffie-Hellman basically lets your client negotiate the session keys in such a way that even if the negotiation was listened to by a MiTM (Man in The Middle), they wouldn’t be able to establish what the mutually agreed session key was.
Another thing that Tor uses is something called Perfect Forward Secrecy, which means the session keys are used briefly and later replaced. This means that if one of the nodes were to get compromised, data that already passed through it can’t be decrypted with the private keys because the keys have changed since then.
Tor is both a piece of software and an anonymizing network. A live representation of the Tor network can be seen here. The Tor browser (software) is what lets you access the Tor network.
Most of the Tor relays are to be found in Central Europe. From the link above, you can see the network’s historical development. You might experience more (or less) latency depending on your proximity to the nodes. The Tor network is generally known to not be blazing fast.
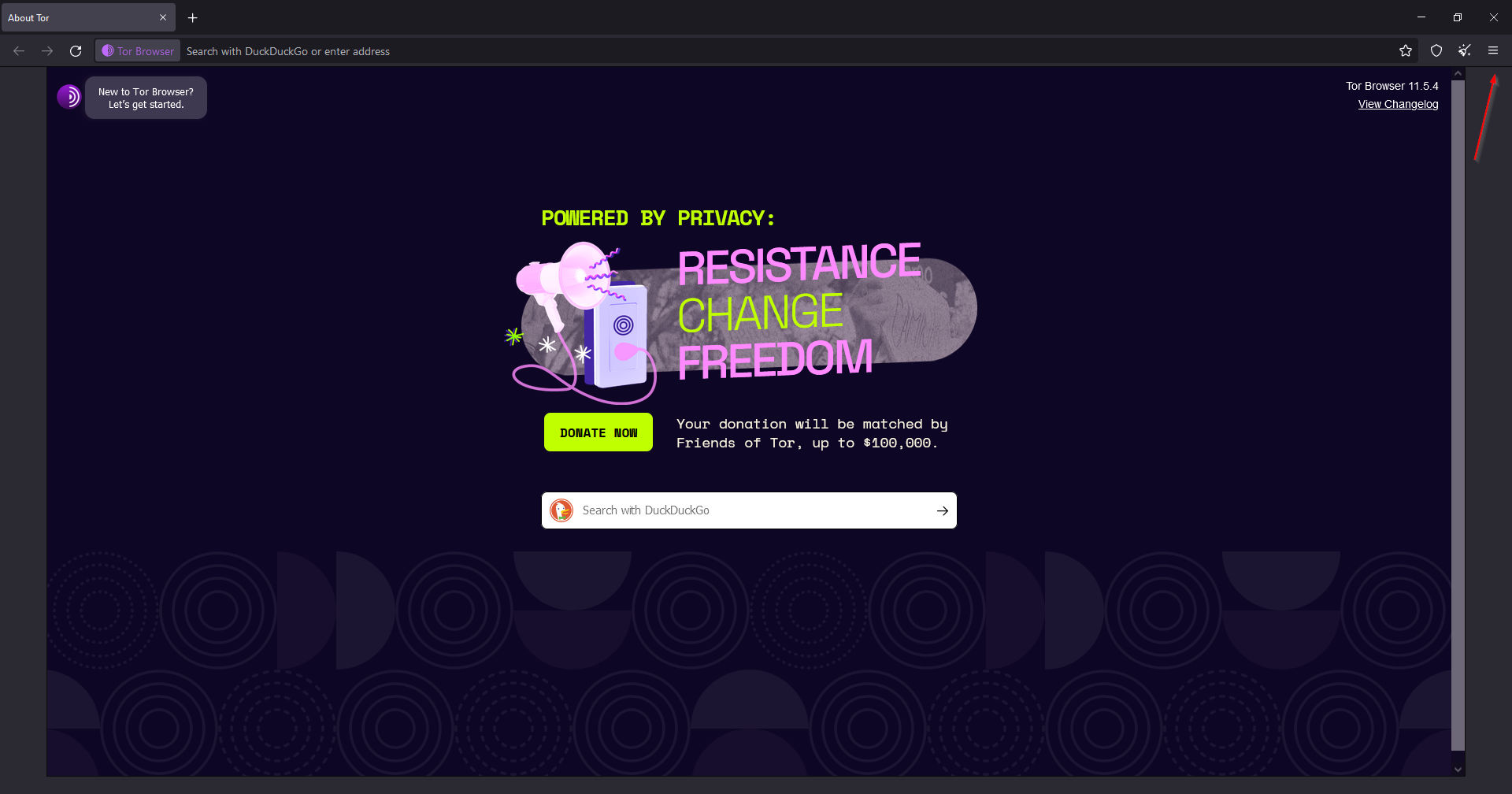
The Tor browser itself is a hardened Mozilla Firefox ESR (it has NoScript, HTTPS Everywhere, and Tor proxy browser addons). It can be also run from a removable media (standalone) and is cross-platform – available on Windows, Mac, GNU/Linux.
You can verify and download it from https://www.torproject.org/.
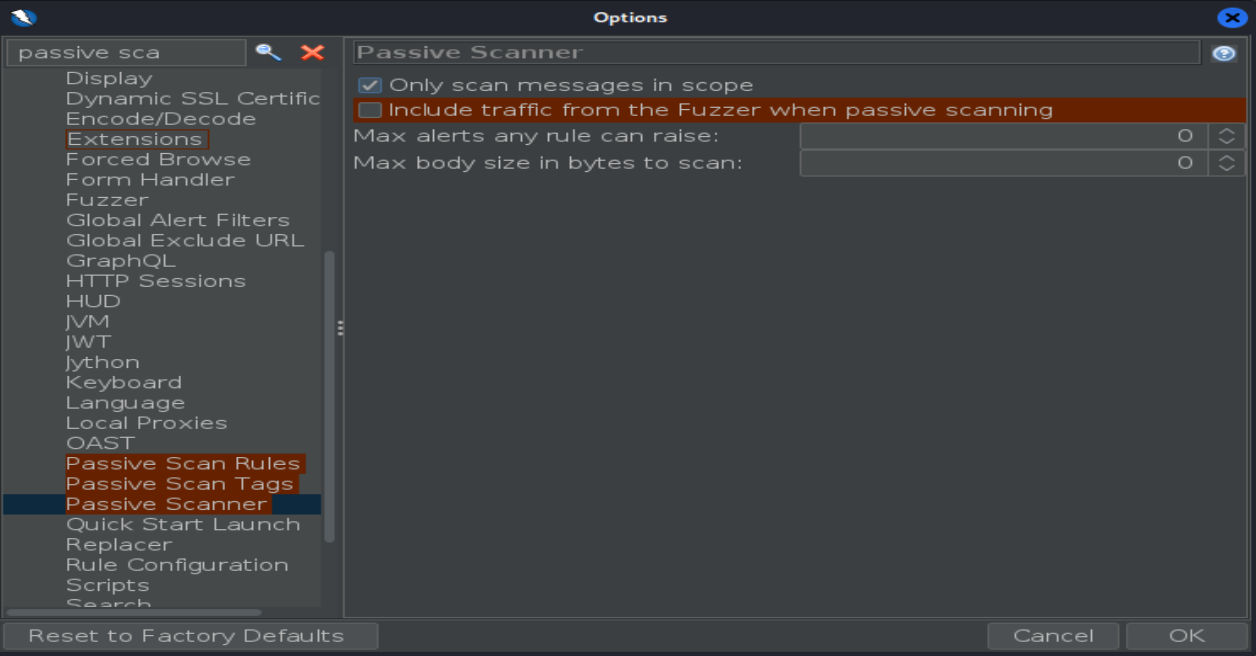
Once installed, and started, you will see a Firefox-like UI, and will be greeted with a welcome message for the first time. I will not cover how you can configure these, for the most part, its almost the same as for your Firefox broswer, so if you’re a Firefox user, you’ll feel at home. I will just share some thoughts below (check the third screenshot); This is more to give you an idea on what approach we need to have here, but the more technical aspects is something I will gradually build up to as we go through the series.

Note the two options from the second screenshot. The New Circuit option will make you go through a different exit node, and will basically present a new IP address but you can still have trackable items in your browser (even though the browser tries to fight that anyway, its still possible), but the New Identity option will restart the browser itself. This is the big difference between the two options, the New Identity will attempt to wipe everything that is contained within the browser and could be linked/used for tracking, which is why it restarts.

For an attempt at anonimity, you want the security settings set at the Safest option, even though it might break some websites. But, if that’s not chosen, deanonymizing is much easier, and it kinda defeats the purpose of using Tor in the first place. You obviously want to restrict 3pp cookies, disable browser plugins (Flash), never record browsing history or website data, and change details that distinguish you from other Tor Browser users.
Resources
https://support.torproject.org/ – Check out the Most Frequently Asked Questions section
https://tor.stackexchange.com/ – A stackoverflaw-like Tor messageboard where you can find answers to your Tor-related questions
https://blog.torproject.org/ – A blog by the Torproject
https://gitlab.torproject.org/tpo/team – This used to be the Tor wiki, a lot of useful information here
https://www.reddit.com/r/tor – Tor subreddit which can be very useful to you
https://2019.www.torproject.org/projects/torbrowser/design/ – If you want to really jump down the rabbit hole that is Tor, this might be the best place to be, as these are basically the design documents for Tor
Conclusion
I hope you liked this article, and that I’ve managed to shed some light on Tor! There’s way more to unpack here, and I hope to gradually help you familiarize yourself with this enormous topic, by building upon what was written in previous articles, so, stay tuned for the next one!
Cover image – taken from https://torflow.uncharted.software/
#tor #tor-circuit #nodes #onion
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About VRX
VRX is a consolidated vulnerability management platform that protects assets in real time. Its rich, integrated features efficiently pinpoint and remediate the largest risks to your cyber infrastructure. Resolve the most pressing threats with efficient automation features and precise contextual analysis.