With the rise of remote working came a surge in cybercrime. Business Email Compromise (BEC) attacks have seen a 150% year-over-year increase, so the odds are not in any business’s favor. However, staying vigilant and educated can protect your company and avoid such attacks. Keep reading to find out the main dangers business email accounts face and get 10 business email security tips.
What is Business Email Compromise (BEC)?
BEC is a type of cybercrime that involves impersonating a trusted business contact, such as a CEO or supplier, in order to trick employees into transferring money or sensitive information to the criminal’s account. These schemes often involve careful research and social engineering to create a convincing ruse.
According to the FBI, BEC fraud has cost companies over $26 billion globally since 2016, and the threat continues to grow. Small businesses are particularly vulnerable, as they may not have the resources or expertise to detect and prevent these attacks.
One example of a BEC scam involved the director of Puerto Rico’s Industrial Development Company, Ruben Rivera, who mistakenly made the transaction of $2.6 million to a fake bank account. In another case, Ubiquiti Networks Inc., the San Jose-based manufacturer of high-performance networking technologies, fell victim to a BEC attack that resulted in a loss of $46.7 million.
As the use of email continues to be an essential aspect of business communication, it is crucial for companies to remain vigilant and take proactive measures to defend against the threat of BEC.
Phishing is the number one email security threat
Phishing is a type of digital scam that is especially common in emails. It’s a form of social engineering where a hacker tries to deceive an employee into believing the email is coming from a credible source. Phishing emails usually have some sort of CTA: it’s like a form of marketing, if you will. Except that phishing CTAs usually involve clicking on a malicious link or revealing sensitive company data to outsiders.
Well, just like any other marketer, hackers employ creative techniques to improve the conversion rates of their scams. The more deceitful the email, the higher the conversion rate. That’s why phishing emails can be difficult to spot at times. Examples of phishing emails include:
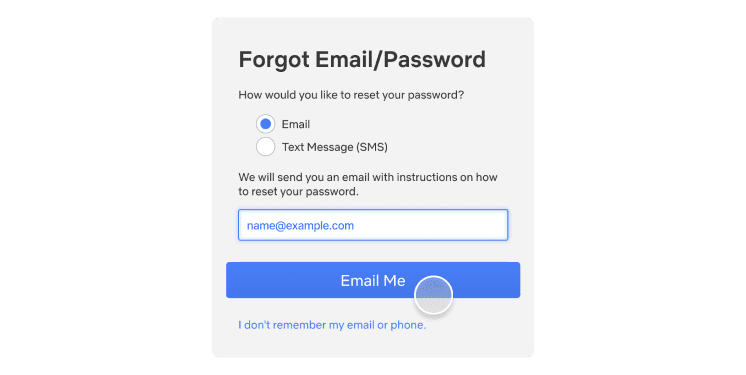
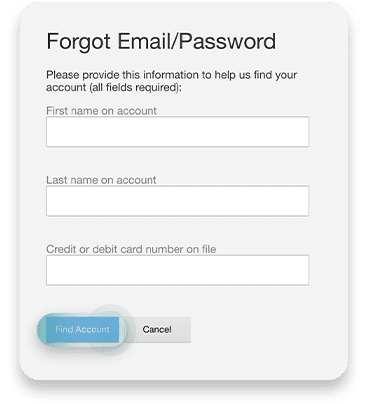
Account verification scam. You may receive a phishing email that looks something like this: “Due to a recent security threat, we would like to ask you to verify your account by signing in through the link below. Failing to do so will result in the permanent deactivation of your account.”
Fake invoice scam. Hackers may send out emails saying, “We still haven’t received your payment for our services. Please use the link below to complete the transaction.”
Spear phishing. This is a more advanced and tailored form of phishing that requires hackers to do some research on your company. For instance, an employee may receive an email that looks like it’s coming from a specific coworker, instructing them to visit a website or disclose information.
Password security for your business
Store, manage and share passwords.
30-day money-back guarantee
Best practices for business email security
Falling for phishing scams can expose your company to data breaches and malware. Taking steps to appropriately ensure the security of your email will help protect your business from phishing and other forms of cybercrime:
1. Conduct phishing awareness training
Emails usually get breached through employee negligence and lack of knowledge. So the first way to increase email cybersecurity is to raise awareness about the main threat: phishing. All employees should receive in-depth training on recognizing and avoiding attempted phishing schemes. The main points to cover here are:
Becoming familiar with the main phishing schemes
Being suspicious about unusual requests
Never clicking on random links received through email
Once employees are familiar with these precautions, your company’s susceptibility to phishing emails will significantly decrease and your business email security will improve in general.
2. Train employees on how to deal with email attachments and suspicious email links
Email attachments and suspicious links are the most common methods cybercrooks use to spread malicious software. Ensure that your employees are well aware of these devious practices and are trained to spot them in real-life situations. With time and a lot of practice, your team will develop a sense for suspicious email links and attachments, which should considerably lower the potential attack vector and significantly improve your overall security posture.
3. Enable multi-factor authentication
You can make your account safer from hackers by connecting your smartphone to your email. Even if the passwords to your email accounts are leaked, no outsiders will be able to access them without having access to the device it’s connected to. All vital business accounts, not just email accounts, should have multi-factor authentication enabled.
4. Avoid using email when on public Wi-Fi
Public Wi-Fi poses massive risks to email security. If it’s unencrypted (which it often is), anybody can connect to the same network. You never know when a hacker will be that someone.
If a hacker intercepts your connection with unencrypted public Wi-Fi and catches you logging into your email, they can steal your email password. It’s best to steer clear of public Wi-Fi altogether, but if connecting to it is necessary, never transmit important data while on it.
5. Avoid using business emails for private purposes and vice versa
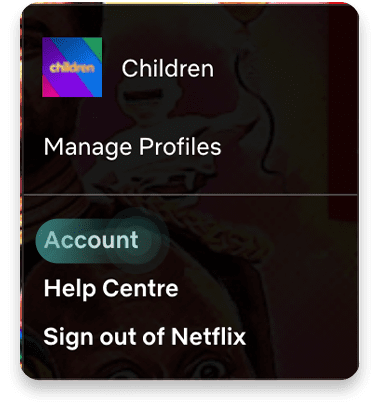
Most office jobs these days come with an email address. Some people get the temptation to use the new email address for all sign-ins. Need to sign up for a new streaming service? Well, why not use your brand new business email for that? Everybody else does it, anyway, right?
At first, it might sound like a great idea. Yet using your enterprise email for private purposes and vice versa could cause significant security concerns for you as an individual and the company.
First, using a company email for your personal online activities allows for easier and simpler profiling. Consequently, that could lead to spear-phishing — a targeted phishing campaign or other targeted cyberattacks.
6. Encrypt company email
Encrypting company email using special email security software is a great way to steer hackers away. Encryption ensures that the only people able to view the emails are the sender and recipient. If a hacker intercepts an employee’s Wi-Fi connection or email account, they will not see any sensitive data.
7. Set up email security protocols
Email security protocols are immensely important because they provide an extra layer of security to your digital communications. The protocols are designed to ensure the safety of your communications as they pass through webmail services over the internet. Without the aid of email security protocols, bad actors can intercept communication in a relatively easy manner. Please familiarize yourself with different email security protocols and enable them to ensure secure communications.
8. Improve endpoint security
To further fortify your security stance, take action to improve your endpoint security. Often the easiest and most effective way to boost endpoint security is by implementing security tools for company-wide use.
Consider deploying a VPN like NordLayer — a tool that encrypts the internet connection and data transferred over your business network. Antivirus software is another tool that should be used on all business workstations to ensure a proactive defense.
9. Don’t change passwords too often
Password fatigue is a fact of life — today, the average user has about 100 passwords on their hands. Keeping track of all the passwords is a challenge.
The conventional wisdom regarding password security is that you should change your passwords every 90 days. While that might sound like a reasonable security practice, it could lead to simpler and easy-to-crack passwords being used.
If you know that your employees take password hygiene seriously and craft hard-to-guess passwords and that none of their passwords were ever leaked, then they should stick to the passwords they already use. If any password (no matter how strong it is) is leaked or breached — the change should be immediate.
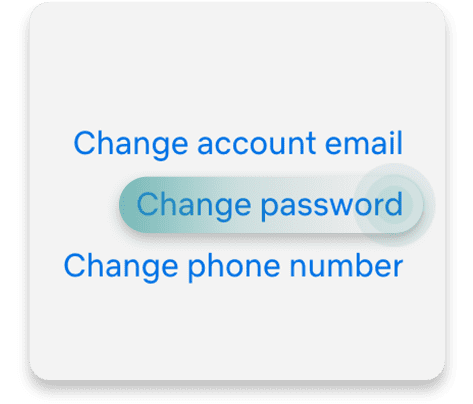
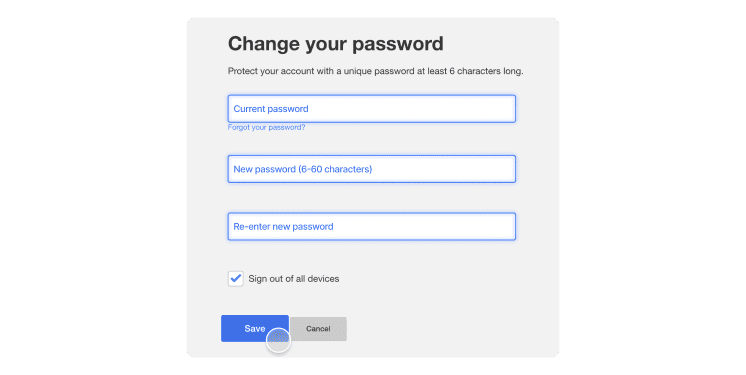
10. Use strong passwords for email accounts
Strong passwords are the backbone of account safety. Yet businesses often fail to secure their emails with strong passwords. If your business is like this, you should know that the easier the password, the easier it is to hack, especially through brute-force attacks. Brute-force attacks are when hackers try to guess a password by flooding your account with thousands of attempts.
To protect your business email from such attacks, ensure everyone in your organization secures their passwords. Secure email passwords are:
Long
Complicated
Contain different types of characters
Unique (never reused from other accounts)
These points are crucial if you want to ensure the safety of your business. However, passwords that are difficult to hack are also difficult to remember. The last thing anyone would want is to secure their account so well that they couldn’t even access it themselves.
Luckily, the business password manager by NordPass can come to the rescue. If all members of your company use it for their accounts, their emails will be safe, and they won’t need to scratch their heads trying to remember their passwords.
Bottom line
Business email security is never a given. Even though platforms like Gmail or Outlook do their best to ensure the safety of their users, you can easily fall victim to hackers if you don’t actively protect your account. By following these five email security best practices, the chances of getting your business emails hacked will be much slimmer because hackers will likely prefer more vulnerable prey.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordPass
NordPass is developed by Nord Security, a company leading the global market of cybersecurity products.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.