Navigating the world of IT support and cybersecurity services can feel like exploring a maze. Two terms that often come up are MSP and MSSP. Though they sound similar, their roles in the IT ecosystem are distinct.
Let’s dive in to clarify these differences, helping you identify which service aligns best with your IT and cybersecurity needs.
What is an MSP?
An MSP, or Managed Service Provider, acts as your IT department’s extension or sometimes its entirety.
They manage a spectrum of IT services, from network and infrastructure to software management and support. MSPs aim to ensure your IT operations run smoothly, efficiently, and without interruption, focusing on maintenance and optimization.
What is an MSSP?
MSSP stands for Managed Security Service Provider. While MSPs cover the broader IT landscape, MSSPs focus on cybersecurity.
They monitor and manage your security devices and systems and offer threat intelligence, incident response, and more. Essentially, they’re your cybersecurity guardians, proactively defending your digital assets against threats.
Key differences between MSP and MSSP
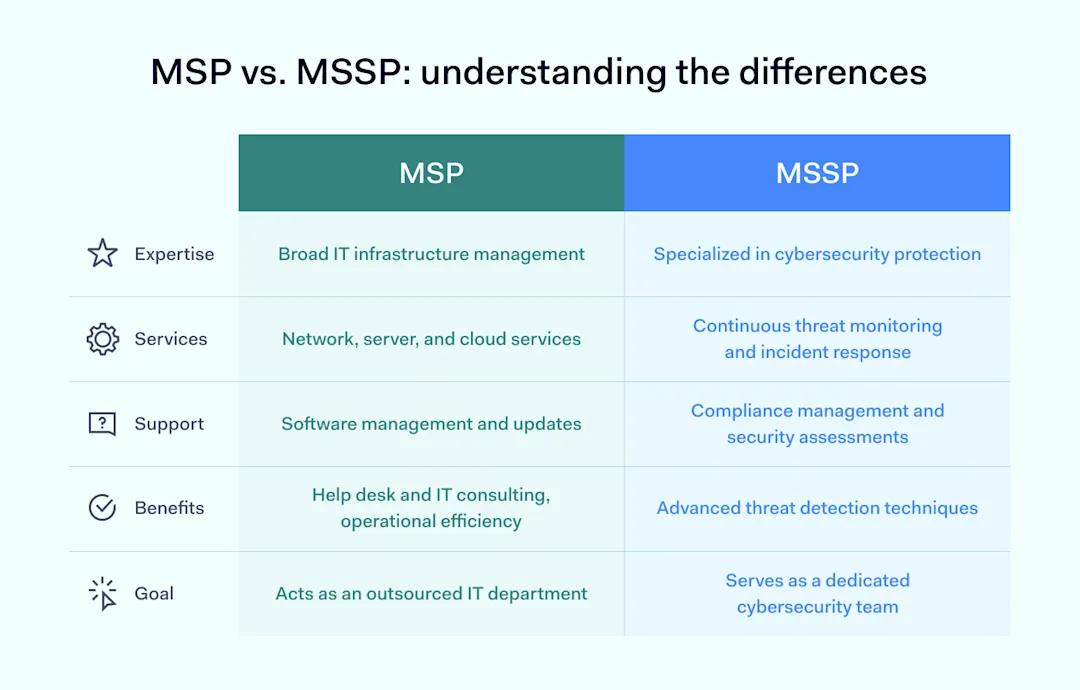
MSPs serve as a full IT department, offering various services like network management and software updates. Their primary goal is to ensure the seamless operation and reliability of your IT infrastructure. MSPs are the technology stewards, ensuring your systems are efficient, up-to-date, and scalable to support your business objectives.
MSSPs focus narrowly yet deeply on cybersecurity, acting as vigilant protectors against cyber threats. They specialize in monitoring, managing, and responding to security risks, employing a suite of services designed to protect businesses from digital dangers. Their services range from real-time threat monitoring to incident response and compliance management, all aimed at fortifying your organization’s cybersecurity posture.
To neatly summarize the distinctions, let’s lay MSP vs. MSSP out in a table:
![]() Here’s a breakdown of their primary differences:
Here’s a breakdown of their primary differences:
MSPs focus on the broader spectrum of managing and optimizing IT infrastructure and operations. They offer a wide range of services, including:
Managing networks, servers, and cloud services
Providing software management and updates
Help desk support and IT consulting.
The core objective of MSPs is to enhance operational efficiency and support business growth, acting essentially as an outsourced IT department.
MSSPs, on the other hand, specialize in protecting businesses from cyber threats and ensuring data security. Their services are centered around:
Incident response
Compliance management
Security assessments.
They use advanced methods to detect and prevent cyber threats, acting as a dedicated cybersecurity team for their clients.
While MSPs are all about ensuring that the IT infrastructure is running smoothly to support and enhance business operations. MSSPs, on the other hand, dive deeper into the cybersecurity aspect, ensuring that businesses are safeguarded against the increasing number of cyber threats.
Whether a business opts for an MSP or an MSSP depends on its primary needs: comprehensive IT management or specialized cybersecurity protection.
In many cases, businesses benefit from the combined strengths of both types of providers to ensure both operational excellence and robust security.
What is the difference between MSSP and MDR?
While MSSPs focus on managing and monitoring security services, MDR (Managed Detection and Response) providers take a more hands-on approach to actively hunting, detecting, and responding to threats. Think of MSSPs as your cybersecurity watchdogs, while MDR services are the special forces that detect and neutralize threats.
MSP and MSSP: the market growth
The global managed services market has seen consistent growth, driven by businesses’ increasing reliance on IT infrastructure and the need for efficient, scalable solutions.
According to projections, this market could grow significantly, reaching a substantial valuation by 2028. This growth is fueled by the ongoing digital transformation in various sectors, necessitating managed IT services to support operations, data management, cloud services, and customer relations.
The managed security services market is also on a robust growth trajectory, with a specific focus on cybersecurity services.
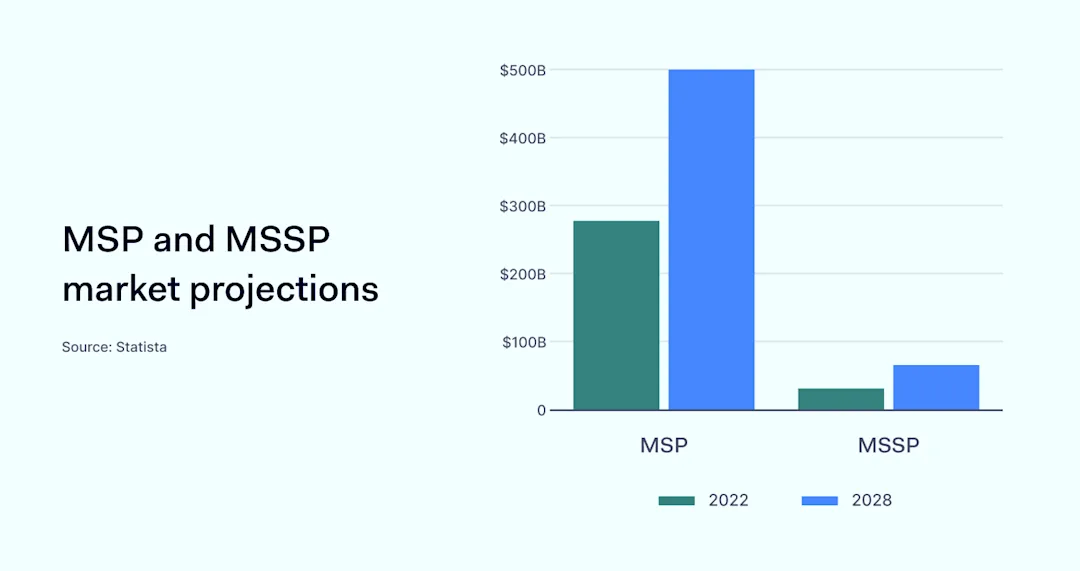
The escalating threat landscape propels this market’s expansion, regulatory compliance requirements, and the complexity of cybersecurity solutions. Businesses are increasingly outsourcing their cybersecurity needs to MSSPs to protect against data breaches and cyber-attacks and to ensure data privacy and compliance with regulations.
Factors defining MSP market growth
Digital transformation: as businesses continue to digitize operations, the demand for comprehensive IT services, including cloud management, data analytics, and network infrastructure, grows.
Cost efficiency: MSPs offer a cost-effective solution for businesses to manage their IT needs without the overhead of an in-house IT department.
Scalability and flexibility: the ability of MSPs to scale services according to business needs is a key driver, allowing companies to adjust their IT services based on growth and seasonal demands.
Factors responsible for MSSP market growth
Cybersecurity challenges: the increasing sophistication of cyber threats drives demand for MSSPs as businesses seek specialized expertise to navigate the complex cybersecurity landscape.
Regulatory compliance: With growing regulatory pressures around data protection, businesses turn to MSSPs for compliance assurance and to avoid potential fines.
Advanced threat detection and response: the need for 24/7 monitoring and quick response to security incidents has become critical, making MSSPs an essential partner for businesses.
Market differences
While both MSPs and MSSPs are integral to the IT and cybersecurity ecosystem, their markets differ primarily in focus and expertise.
MSPs are broad, covering all aspects of IT management and support, catering to businesses’ operational and efficiency needs. In contrast, MSSPs are specialized, focusing solely on cybersecurity services to protect businesses from digital threats and ensure compliance with data protection laws.
The MSP market is defined by its operational support and infrastructure management role, appealing to businesses looking for end-to-end IT services. The MSSP market, however, is driven by the need for specialized cybersecurity services, attracting businesses focused on enhancing their security posture in the face of increasing cyber threats.
Can an MSP be an MSSP?
Yes, the line between MSPs and MSSPs can blur. Some MSPs evolve to include MSSP functions, offering a hybrid model that covers both IT management and security services. This evolution reflects the growing importance of cybersecurity across all IT operations.
The managed service provider can indeed evolve into a Managed Security Service Provider. Still, this transformation requires a strategic approach, significant investment in skills and technology, and a commitment to adopting a security-first mindset.
Why make the transition?
The move from MSP to MSSP is often motivated by the growing demand for cybersecurity services. Businesses are increasingly aware of the risks posed by cyber threats and are seeking providers that can offer both IT management and robust security measures. By transitioning to an MSSP, providers can meet this demand, offering a one-stop shop for IT and security needs.
Moreover, this evolution allows providers to differentiate themselves in a crowded market, offering added value to clients through specialized security solutions. It also opens up new revenue streams, as businesses are willing to invest significantly in cybersecurity to protect their assets and reputation.
What are the deciding factors when choosing between an MSP and an MSSP for your business?
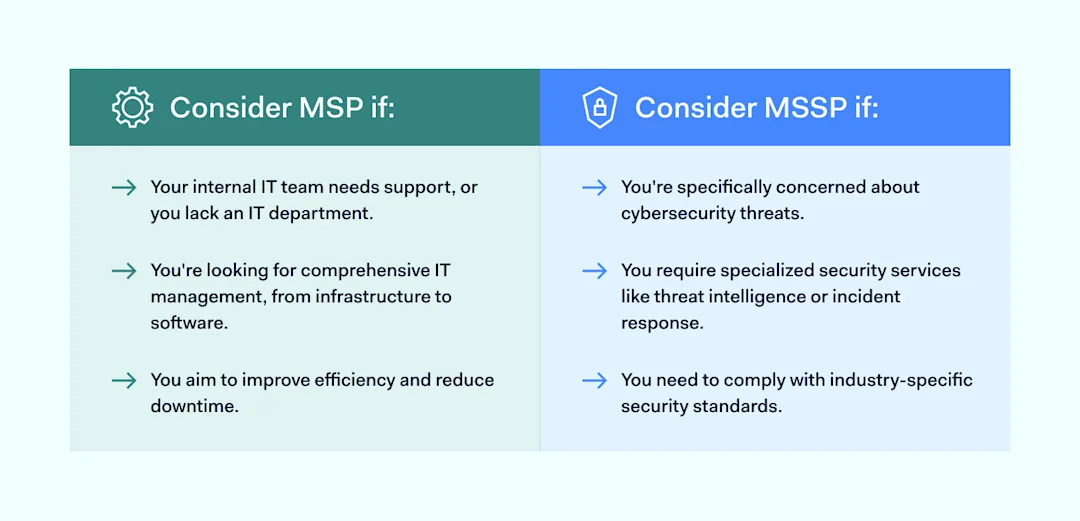
Comparing MSP vs. MSSP for your business comes down to understanding your core IT infrastructure management and cybersecurity needs. Here’s a streamlined approach to making that decision:
Assess business IT capabilities: if a business lacks a dedicated IT department or needs to augment its existing IT capabilities, an MSP might be the right fit. MSPs provide comprehensive IT services, ensuring your infrastructure is robust and up-to-date, with increased efficiency supporting your business operations.
Evaluate security requirements: if you’re particularly concerned about cybersecurity, face stringent regulatory compliance requirements, or handle sensitive data, leaning towards an MSSP makes sense. MSSPs specialize in protecting businesses from cyber threats with services like real-time monitoring, incident response, and compliance management.
Consider business size and sector: small to medium-sized businesses often find MSPs suitable for their broader IT needs, while larger organizations or those in high-risk sectors (e.g., finance, healthcare) may prioritize the specialized security services of an MSSP.
Budget and investment: determine the budget for IT and cybersecurity services. MSPs can offer more predictable costs for a range of IT services, while MSSPs might represent a higher investment focused on advanced security measures.
Future growth and scalability: think about business future needs. An MSP can help scale the IT infrastructure as your business grows, whereas an MSSP will ensure your cybersecurity posture scales in tandem with your risk exposure.
Selecting either an MSP or an MSSP boils down to understanding your specific needs:
![]()
How NordLayer boosts MSP capabilities
Third-party providers like NordLayer step in as a powerful solution for MSPs, enhancing their capabilities to manage and secure networks with comprehensive security solutions. It offers features like Secure Remote Access, Zero Trust network architecture, and advanced threat protection.
Security monitoring. NordLayer amplifies MSPs’ ability to offer continuous security monitoring, which is crucial for early threat detection and maintaining a vigilant cybersecurity posture. This ensures clients are protected around the clock from a broad spectrum of cyber threats.
Security operations. With NordLayer’s security solutions, MSPs can enhance their security operations through automation and advanced analytics, speeding up incident response and bolstering defenses against evolving cyber threats, thereby elevating the level of service to clients.
Endpoint protection. NordLayer supports MSPs in implementing robust endpoint protection and safeguarding client devices against malware and other attacks, which is essential for the integrity and security of client networks.
Data protection. By offering encryption and secure access controls, NordLayer assists MSPs in protecting clients’ sensitive data against unauthorized access, aligning with information security regulations, and enhancing clients’ trust.
Cloud services. NordLayer enables secure access to cloud services, protecting data in transit to and from the cloud, an essential feature for businesses leveraging cloud-based solutions and security operations in today’s digital environment.
Providing cybersecurity services. Integrating NordLayer allows MSPs to expand their cybersecurity services, covering everything from security monitoring to data protection, meeting the increasing demand for comprehensive cybersecurity solutions.
These tools bolster an MSP’s service offering and ensure clients’ networks are both accessible and secure. By performing risk assessment and integrating NordLayer, MSPs can provide a more robust IT and security infrastructure, reflecting the synergy between comprehensive IT support and dedicated cybersecurity measures.
Are you looking for a trusted partner to secure your clients’ networks? NordLayer offers a Partner Program with a focus on tangible benefits for its partners and simple yet effective solutions to protect businesses in the hectic cybersecurity landscape.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.







)





