Imagine you’re at your favorite coffee shop, buying a latte with your credit card. In that brief moment of swiping or tapping your card, a complex web of data transfers occurs behind the scenes. Your payment information travels through various networks, all the way to the merchant’s bank, to authorize the transaction. This seamless experience relies heavily on stringent security measures to protect your sensitive cardholder data from potential cyber threats.
For businesses handling payment card data, achieving firewall PCI DSS compliance is essential to maintaining this security. Without it, the integrity of these daily transactions—and the trust customers place in using their payment cards—would be at significant risk.
This article explores the importance of PCI DSS compliance for firewall configurations, the benefits of implementing a PCI DSS-compliant firewall, and how NordLayer’s cloud firewall can help your organization achieve and maintain compliance.
What is firewall PCI DSS compliance?
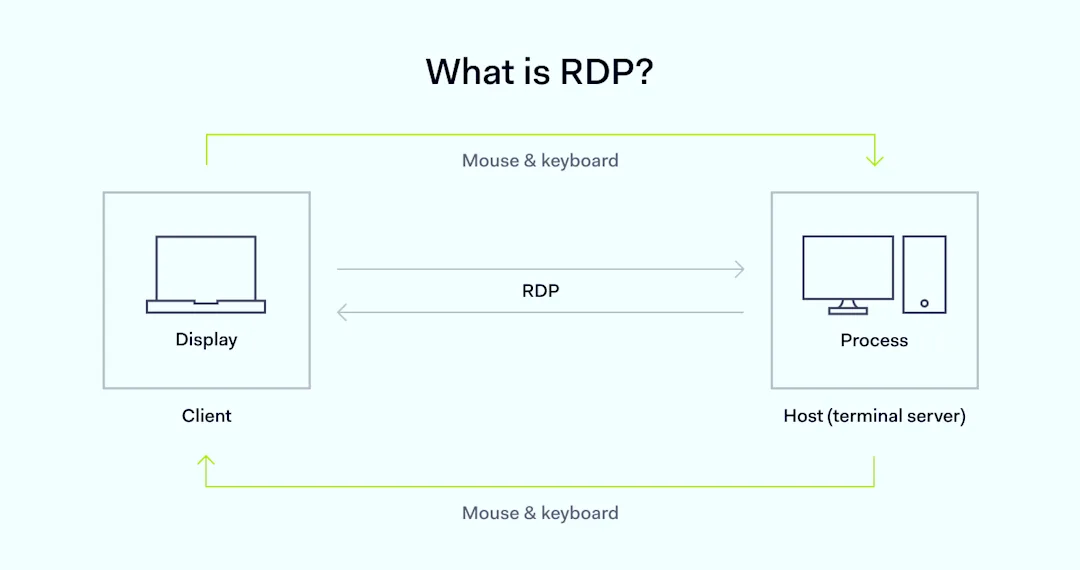
Firewall PCI DSS compliance involves meeting the security standards set by the Payment Card Industry Data Security Standard (PCI DSS) for firewall configurations. These standards offer guidelines on how cardholder data should be protected from unauthorized access and breaches by controlling and monitoring inbound and outbound traffic between trusted and untrusted networks.
A firewall is a security barrier that enforces access control lists (ACLs) and other protective measures to manage traffic. In the context of PCI DSS, a compliant firewall configuration must restrict unauthorized access to cardholder data while ensuring secure communication channels for legitimate traffic. This involves a combination of hardware and software firewalls, virtual private networks (VPNs), and other network security measures.
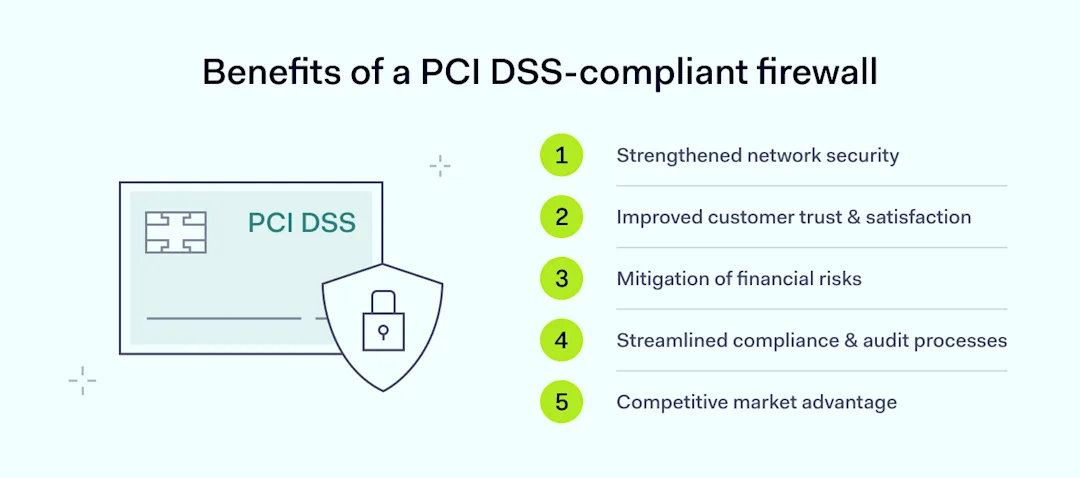
Benefits of a PCI DSS-compliant firewall
Implementing a firewall that adheres to PCI requirements offers many advantages, enhancing both security and operational efficiency for your business. By ensuring your firewall configuration is PCI DSS-compliant, you gain the following benefits:
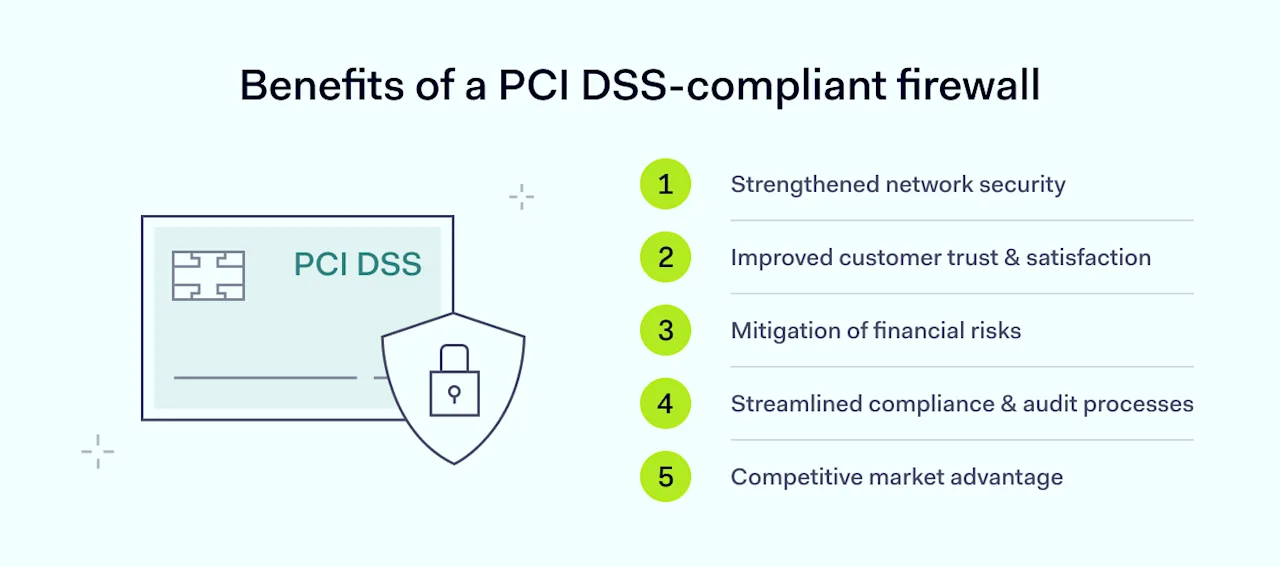
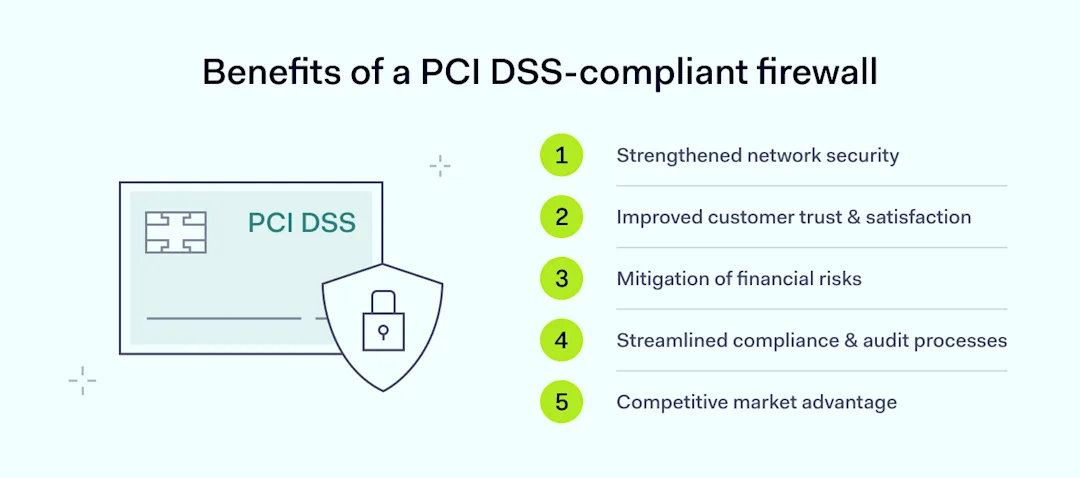
Strengthened network security: A PCI DSS-compliant firewall enforces stringent protective measures, including precise control over inbound and outbound traffic. This enhanced security posture minimizes the risk of unauthorized access and data breaches by restricting access to sensitive data.
Improved customer trust & satisfaction: Demonstrating compliance with PCI DSS builds customer confidence in your ability to safeguard their payment card data. By protecting cardholder data effectively, you foster trust and potentially increase customer loyalty and satisfaction.
Mitigation of financial risks: Non-compliance with PCI DSS can lead to significant financial penalties. A PCI DSS-compliant firewall helps avoid these fines, ranging from $5,000 to $100,000 per month. Additionally, preventing breaches protects your organization from the costs associated with data recovery, legal actions, and loss of business.
Streamlined compliance & audit processes: Meeting PCI DSS requirements simplifies compliance with other regulatory frameworks. It also streamlines audit processes by ensuring that protective measures are in place and regularly tested, reducing the burden of demonstrating compliance during audits.
Competitive market advantage: Achieving firewall compliance can serve as a differentiator in a competitive market. Businesses that prioritize security and compliance can appeal to customers and partners who value data protection, providing a competitive edge.
By leveraging these benefits, your organization not only strengthens its security posture but also positions itself to avoid the significant fines and penalties associated with non-compliance.
Avoiding fines and penalties
Failure to comply with PCI DSS can lead to severe financial and reputational consequences. Financially, non-compliance can result in substantial fines imposed by payment processors or acquiring banks. These fines vary based on the severity and duration of non-compliance.
For example, in 2019, Marriott International faced a fine of over $120 million due to a data breach, underscoring the significant financial risks involved. Beyond fines, non-compliance often leads to increased operational costs due to more frequent and stringent audits, which require additional resources and can disrupt regular business activities.
The reputational damage resulting from non-compliance can be even more detrimental. Customers expect businesses to protect their payment card data, and a breach can severely erode trust. According to a 2024 study by CivicScience, 56% of customers express a complete lack of trust in a company post-breach. Consumers aged 25-44 are more forgiving, while those aged 45-54 are least likely to trust a company again.
High-profile breaches have shown that customer confidence can erode rapidly, resulting in decreased sales and a long-term decline in market value. Based on recent Forbes research, 80% of customers in developed countries will abandon a business if their personal data is compromised in a security breach. Negative word-of-mouth and media coverage further amplify the reputational damage, making it challenging for businesses to rebuild trust and attract new customers.
Moreover, the legal ramifications of a data breach can be significant. Businesses may face lawsuits from affected customers or regulatory bodies, leading to costly legal proceedings and settlements. For instance, Target’s data breach cost the organization an $18 million settlement.
These legal battles not only strain financial resources but also contribute to ongoing negative publicity, compounding the damage to the brand’s reputation. Thus, adhering to PCI DSS requirements is crucial not only for regulatory compliance but also for maintaining financial health and customer trust.
Meeting specific PCI requirements
Businesses must comply with various PCI DSS requirements to achieve compliance. These requirements—including maintaining a secure firewall configuration and regularly updating antivirus software—are designed to protect cardholder information by establishing and maintaining robust protective measures over time. Below is an overview of key PCI DSS requirements for effective firewall setup and network security:
Install and maintain a firewall configuration
Businesses must define and enforce firewall rules that control traffic between trusted and untrusted networks. To protect cardholder information, businesses must install and maintain a PCI DSS-compliant firewall setup.
Pro tip: Configure a business firewall to block all traffic from untrusted networks except for specific IP addresses necessary for business operations.
Do not use vendor-supplied defaults for system passwords and other security parameters
Using default settings is a common vulnerability. Businesses must change default passwords and settings to secure configurations and reduce the risk of unauthorized access.
Pro tip: Change the default admin password on a firewall to a complex, unique password.
Protect stored cardholder data
This requirement emphasizes protecting payment card information stored in databases, files, and other storage systems. Businesses must use encryption and other protective measures to secure stored cardholder data.
Pro tip: Encrypt credit card numbers in a database to prevent unauthorized use of the data.
Encrypt transmission of cardholder data across open, public networks
Businesses must encrypt payment card information when transmitting it over open public networks to protect it from interception by unauthorized parties.
Pro tip: Use SSL/TLS encryption to secure the transmission of credit card information from a customer’s browser to the business’s web server.
Use and regularly update anti-virus software or programs
This requirement involves deploying anti-virus software to protect systems from malware and regularly updating these programs to defend against new threats.
Pro tip: Install anti-virus software on all systems that handle cardholder data and schedule regular updates to ensure protection against the latest malware.
Develop and maintain secure systems and applications
This involves implementing security patches, conducting vulnerability scans, and maintaining secure development practices to protect applications that handle sensitive data.
Pro tip: Regularly update PCI DSS-compliant firewall software to the latest version to protect against known vulnerabilities.
Restrict access to cardholder data by business need to know
Access to payment card information should be limited to individuals whose job responsibilities necessitate it. Implementing access control lists (ACLs) helps ensure that only authorized personnel have access to sensitive information.
Pro tip: Set firewall rules to allow only the relevant departments access to payment card data.
Identify and authenticate access to system components
Businesses must use robust authentication mechanisms, such as strong passwords and multi-factor authentication, to verify the identity of users accessing system components.
Pro tip: Require employees to use a combination of passwords and biometric authentication to access network firewalls.
Restrict physical access to cardholder data
Restricting physical access involves controlling who can physically access systems and storage areas that contain cardholder data. This includes using locks, access cards, and surveillance systems.
Pro tip: Install keycard access controls and surveillance cameras in data centers that store cardholder data.
Track & monitor all access to network resources and cardholder data
Comprehensive logging and monitoring of firewall logs and network activities are essential to track access to cardholder data and identify suspicious activities.
Pro tip: Use a logging system to monitor and analyze all access attempts to cardholder data and generate alerts when unauthorized access occurs.
Regularly test security systems & processes
Regular testing involves conducting security assessments, vulnerability scans, and penetration testing to identify and address potential weaknesses in security systems.
Pro tip: Schedule regular penetration tests to evaluate the effectiveness of firewall rules and network security measures.
Maintain a policy that addresses information security for all personnel
Businesses must develop and maintain a comprehensive information security policy that outlines security responsibilities, processes, and protocols for all personnel.
Pro tip: Create a security policy that includes guidelines for firewall management, incident response, and employee training.
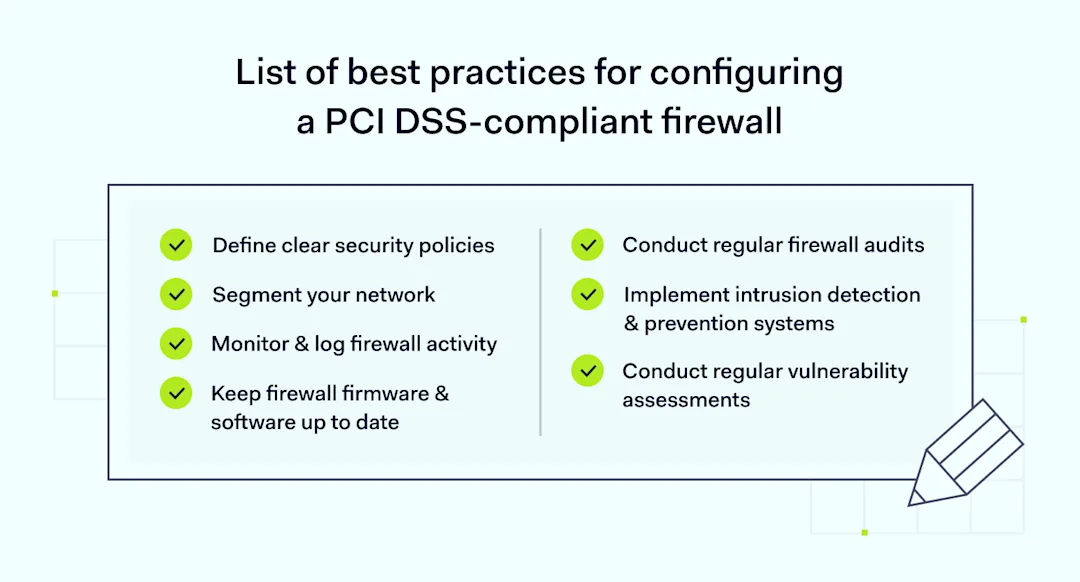
Implementing effective firewall configurations
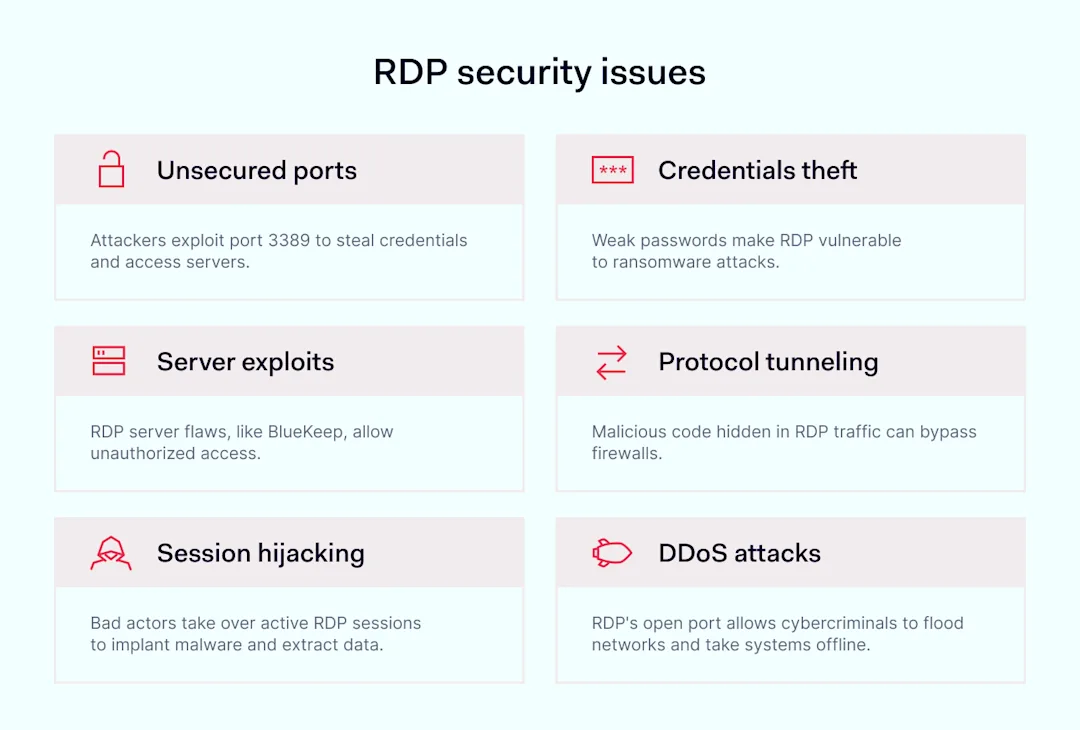
Achieving PCI DSS compliance involves installing network firewalls and configuring them effectively to protect sensitive cardholder data and mitigate potential threats. This requires a comprehensive approach that includes defining clear security policies, segmenting your network, integrating advanced detection systems, and conducting regular assessments and updates.
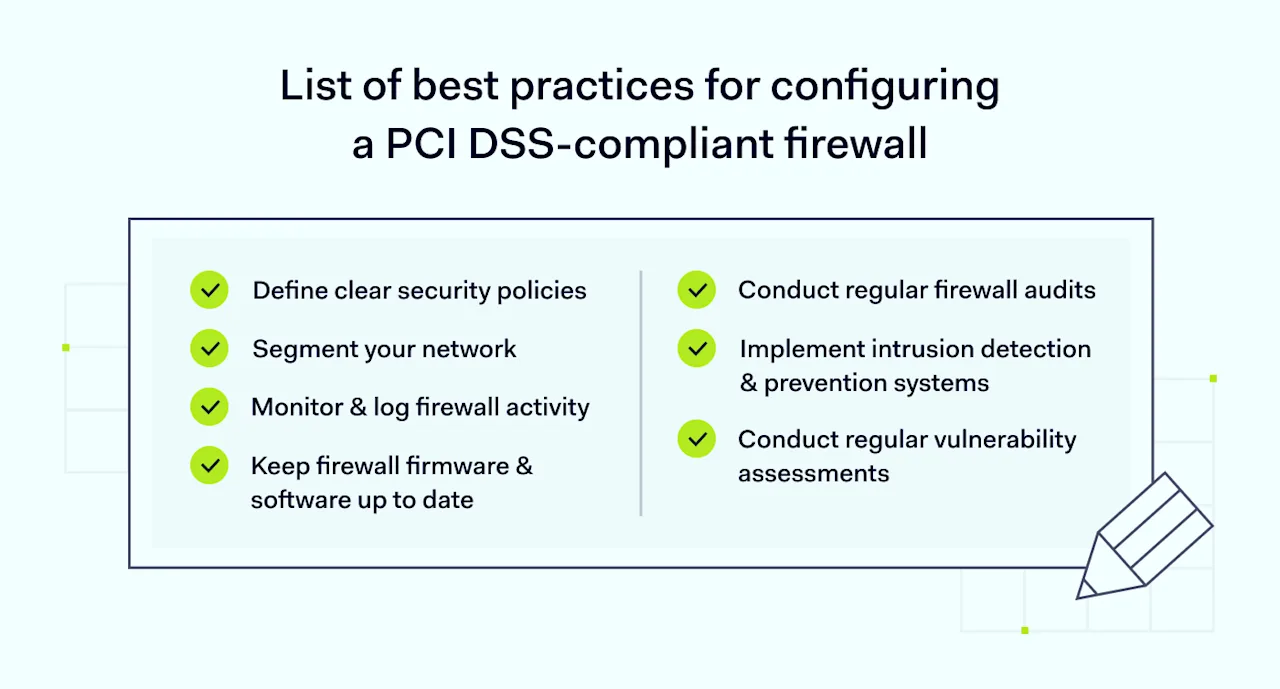
Below are the best practices for configuring a PCI DSS-compliant firewall:
1. Define clear security policies
Establish and document security policies that specify what traffic is allowed or denied. Regularly review and update these policies to reflect evolving security needs and threats.
2. Segment your network
Network segmentation involves dividing your network into smaller segments, each with its own security controls. This limits the exposure of cardholder data and helps contain potential breaches.
3. Implement intrusion detection & prevention systems
Integrate intrusion detection and prevention systems (IDPS) with your firewall to detect and respond to suspicious activities. These systems help identify unauthorized access attempts and mitigate potential threats.
4. Conduct regular vulnerability assessments
Performing regular vulnerability scans helps identify weaknesses in your firewall configuration. Address identified vulnerabilities promptly to maintain a strong security posture.
5. Keep firewall firmware & software up to date
Attackers can exploit outdated firmware and software. Regularly update your firewall to the latest versions and apply security patches to protect against known vulnerabilities.
6. Monitor & log firewall activity
Implement logging and monitoring to track firewall activities, including traffic, configuration changes, and access attempts. Use logs to investigate and respond to suspicious activities.
7. Conduct regular firewall audits
Regular audits of your firewall configuration ensure it remains compliant with PCI DSS firewall requirements. Audits should include reviewing firewall rules, testing intrusion detection capabilities, and verifying network segmentation.
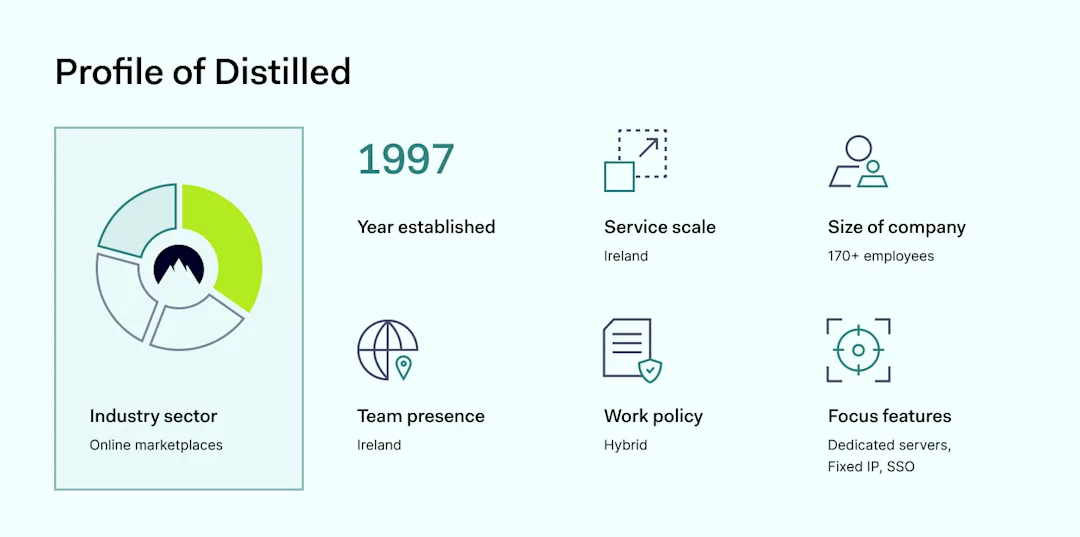
How NordLayer can help in achieving PCI DSS compliance
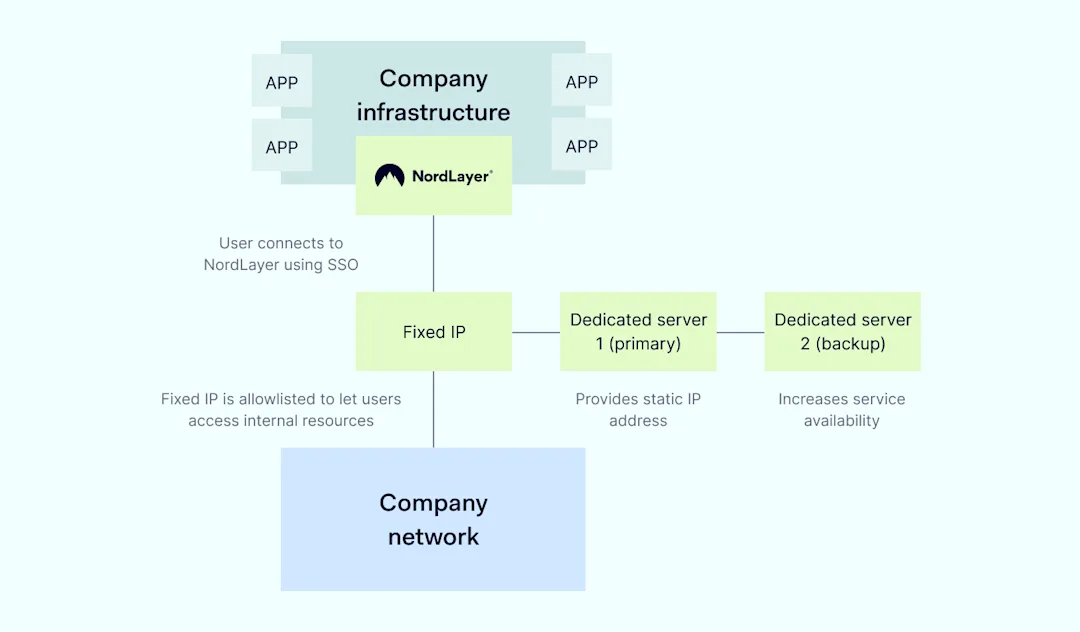
Navigating PCI DSS compliance can be complex, but NordLayer’s cloud firewall solution simplifies the process. Here’s how NordLayer can support your compliance efforts:
Simplified compliance management: NordLayer’s cloud-based firewall offers centralized control and visibility, making it easier to manage firewall configurations and demonstrate compliance with PCI DSS. You can efficiently configure firewall rules, monitor traffic, and generate compliance reports.
Enhanced security features: NordLayer’s solution includes advanced security features such as intrusion detection, virtual private networks (VPNs), and multi-factor authentication. These features help secure your network and protect cardholder data from unauthorized access.
Scalable & flexible deployment: NordLayer’s cloud-based firewall can quickly be scaled according to your business needs. Whether you require protection for a small office or a large enterprise, NordLayer adapts to your security requirements.
Comprehensive support & guidance: NordLayer provides expert support to help you navigate the complexities of PCI DSS compliance. NordLayer’s team can assist with any questions or challenges from setup to ongoing management.
Cost-effective solution: NordLayer’s subscription-based model offers predictable pricing, eliminating the need for significant upfront investments in hardware and maintenance. This makes it a cost-effective alternative to a traditional hardware firewall.
Secure Remote Access: NordLayer’s cloud-based firewall supports Secure Remote Access, allowing employees to connect safely from any location. This is particularly important for maintaining security and compliance in remote work environments.
In conclusion, firewall PCI DSS compliance is crucial for protecting sensitive data and maintaining customer trust. By implementing effective firewall configurations and leveraging solutions like NordLayer’s cloud firewall, businesses can meet PCI requirements, enhance their network security, and avoid non-compliance’s financial and reputational consequences.
For more information on how NordLayer’s cloud-based firewall can help your organization achieve PCI DSS compliance, visit NordLayer’s cloud firewall.
)








)
)