Imagine a school facing problems with students accessing inappropriate websites during class. Teachers feel frustrated, and IT admins try to find a solution. This situation is common in many places that need secure and controlled internet access through URL filtering.
Finding the best internet filtering software can seem hard, but the right choice protects against malicious content and data loss. Web content filtering software creates a safe online environment by reducing cyber threats. This guide highlights the top 10 web content filtering solutions that, in our opinion, based on the public sources we analyzed, offer strong features and ease of use. Each solution is evaluated based on user feedback and cost. Explore these options to improve your business’s online security and productivity with URL filtering and a secure web gateway.
How we chose the best content filtering solutions (in our opinion)
We reviewed the websites of various content filtering solutions and read user reviews on platforms like Gartner, G2, and Capterra. We focused on what users mentioned most about value, speed, performance, and cost.
Here are the seven most important characteristics we used to pick the best content filtering solutions.
Key features. Does the DNS layer security providers offer enough capabilities, like specific URL filtering to implement Secure Web Gateway strategies?
User feedback. We paid attention to what users generally liked and disliked. We focused on ease of use, customer support, effectiveness, and reliability.
Cost and business type. We analyzed cost and overall value for different organization types by considering user comments on pricing models and expenses.
Deployment and management. We examined user comments on how easy it was to deploy and manage each solution. We prioritized solutions that users found simple to set up and manage.
Security and compliance features. We reviewed the security features based on user experiences. We looked at threat detection, DNS filtering, deep packet inspection, and compliance with industry standards.
Scalability and flexibility. We evaluated how well each solution scaled to meet the needs of different-sized businesses. We considered user reviews about flexible deployment options and support for various devices.
Performance and reliability. Based on user feedback, we considered performance and reliability and prioritized solutions with robust infrastructure, high uptime, and fast response times.
Top 10 web content filtering solutions
Different solutions suit different business types. Here’s a detailed look at our top web content filtering solutions available today, listed in no particular order.
NordLayer
DNSFilter
ScoutDNS
SafeDNS
Twingate
GoodAccess
Cloudflare
Zscaler
Cato Networks
Netskope
NordLayer
![]()
NordLayer provides advanced DNS filtering, which helps businesses control employee web traffic and protect against unwanted content through URL filtering. This is crucial because unrestricted internet access can endanger the entire network.
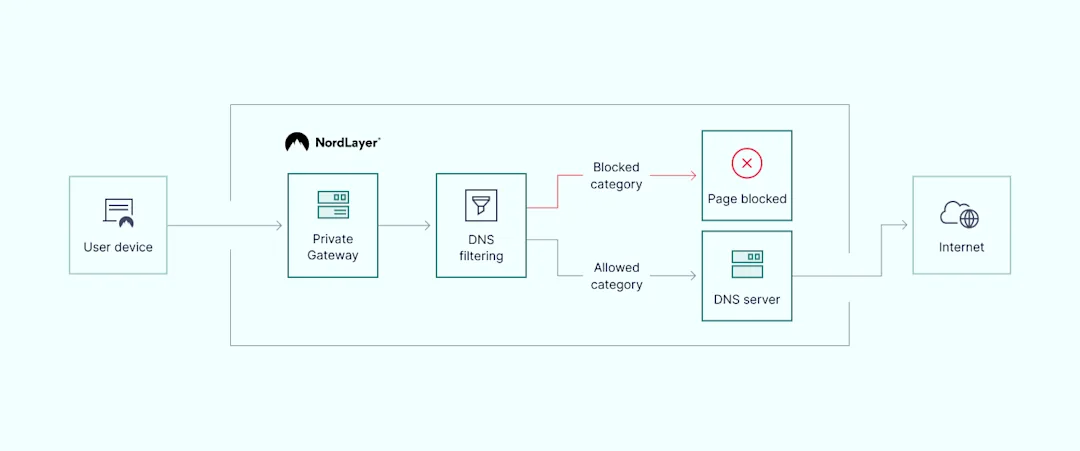
DNS filtering by category acts as a gatekeeper, preventing access to inappropriate websites. A specially configured DNS resolver checks requests against a blocklist of unsafe domains. When a domain is flagged, the resolver blocks the request and stops potential cyber threats before they reach the network. This customized filtering allows businesses to block specific categories, such as violence or adult content. It also helps increase employee productivity, maintain business reputation, and boost network performance.
![]()

With NordLayer, businesses can easily manage and customize security policies from a single central point, regardless of location. NordLayer’s unique, patented DNS filtering technology ensures reliable and effective categorization and blocking of unwanted content, enhancing compliance capabilities. Multiple DNS filtering options allow the blocking of over 50 inappropriate, distracting, or malicious content categories, helping to maintain a clean, more compliant digital environment.
The ThreatBlock solution extends DNS filtering by blocking malicious domains. Using various malware libraries and deny lists, ThreatBlock continuously updates to recognize and block new threats. Even if an employee clicks on a malicious link, ThreatBlock intercepts the request and displays an error message.
Most mentioned product strengths:
Granular control over categories
Over 50 content categories available
Broad range of topics for restriction
Most mentioned overall product benefits:
Multiple platform support
User-friendly interface
24/7 support team response
Reasonable pricing
Regular updates
Compatible with various infrastructures
Integrates with popular IAM platforms
Scalability
Low latency
Free trial or money-back guarantee
Some complaints:
Need to request DNS filtering by category manually
NordLayer stands out as a solid choice due to its strong filtering software, including DNS security and secure web gateway features.
DNSFilter
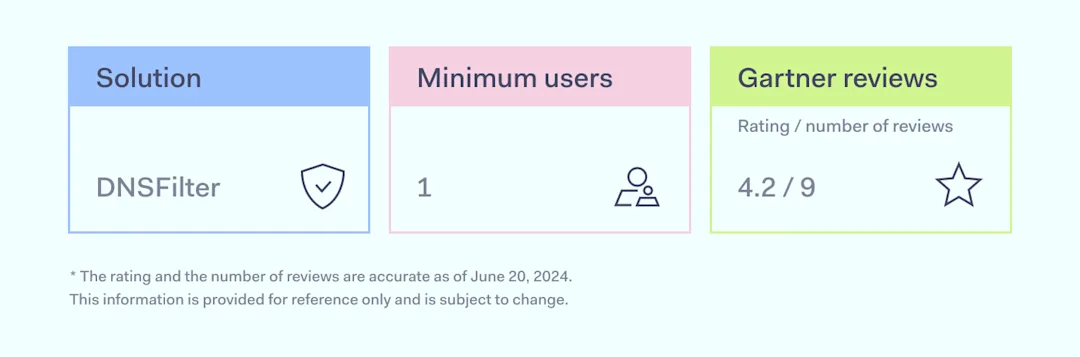
DNSFilter helps organizations filter internet content and protect against online threats like malware and phishing through URL filtering. Founded in 2015, the company now supports thousands of brands worldwide.
DNSFilter performs content filtering at the DNS level with its machine-learning engine, Webshrinker. This technology categorizes new and unknown sites, ensuring accurate content filtering. Users can choose from over 35 content categories and 7 threat categories to customize what they block or allow.
![]()
Most mentioned product strengths:
Flexible filtering options
Fast logging and reporting
Possibility to import domain names in CSV format
Domain whitelisting
Detailed reports, intuitive layout
Most mentioned overall product benefits:
Multiple platform support
User-friendly interface
Reasonable pricing
Regular product updates
Integration with Active Directory
Simple client setup
Free trial
Some complaints:
Failing auto-updates
Deployment challenges
Blocking legitimate sites
VPN compatibility
Disclaimer: This review is based on information from the DNSFilter website, VPN review sites such as Gartner and G2, and user feedback from Reddit, accessed on June 20, 2024.
ScoutDNS
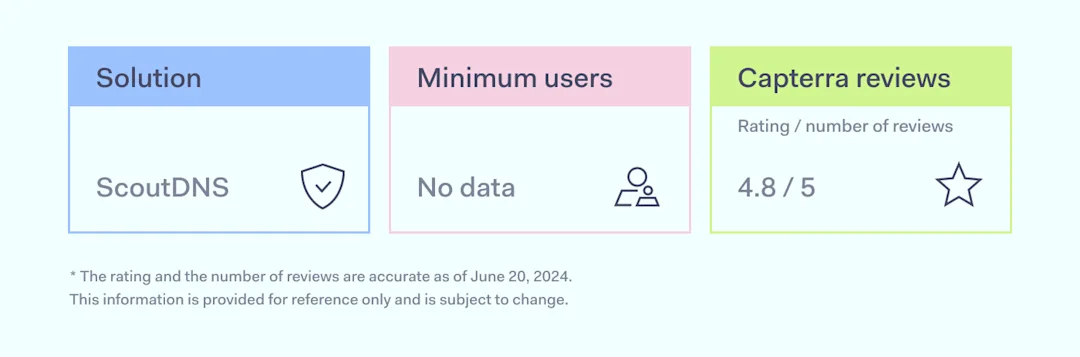
ScoutDNS is a tool that provides DNS security and URL filtering for organizations. It offers a simple way to manage and protect internet access by controlling which sites can be visited.
ScoutDNS helps organizations with content filtering, DNS layer security, and network visibility. It manages over 67 content categories and allows custom allow/block lists for different needs. Users can add items from logs, block harmful sites like those with phishing and malware, and manage suspicious domains. It provides real-time logs for 30 days, shows detailed activity, and inspects DNS messages for more control.
![]()
Most mentioned product strengths:
Whitelist/Blacklist management
Reporting and analytics
Roaming client available
SSL certificate integration
Most mentioned overall product benefits:
Responsive support team
User-friendly interface
Reasonable pricing
Quick issue resolution
Free trial
Some complaints:
Lack of real-time alerts for blocked pages
DNS rerouting can slow down browsing
Disclaimer: This review is based on information from VPN review sites such as Capterra and G2, accessed on June 20, 2024.
SafeDNS
Since 2010, SafeDNS has provided content filtering for thousands of businesses. It helps organizations keep their data safe with reliable web filtering and DNS security services.
SafeDNS offers features that enhance online security and control, such as DNS layer security, content filtering, and app blocking. The AI-powered categorization filters inappropriate content across a vast database and provides detailed reports and analytics for monitoring internet usage. The Anycast network ensures fast and stable performance worldwide, and the solution supports roaming clients and scheduling for flexible management. SafeDNS focuses on content filtering, which makes it ideal for businesses that need to manage web access and online safety, but it is not a comprehensive cybersecurity solution.

Most mentioned product strengths:
Comprehensive category options
Whitelist/Blacklist management
Monthly stats
Wi-Fi network integration
Most mentioned overall product benefits:
Scalability
User-friendly interface
Reasonable pricing
Integration with other tools
Ease of maintenance
Some complaints:
Blocks good websites
Issues with detailed reporting
Inconsistent performance
Support issues
License starting from 15 seats
Disclaimer: This review is based on information from the SafeDNS website and VPN review sites such as Gartner and Capterra, accessed on June 20, 2024.
Twingate
Twingate provides a secure remote access solution designed to meet modern security challenges. Developed in 2019, Twingate aims to address the limitations of traditional VPNs by offering a Zero Trust Network Access model that is both user-friendly and easy to deploy.
Twingate automatically flags, detects, and blocks malicious web threats, protecting users from malware, phishing, and other online dangers. It blocks malicious websites and thwarts phishing attempts while keeping users’ internet traffic safe with customizable filters for both managed and BYOD items. The platform consolidates tools into a single agent, centralizing management for internet security and remote access without the need for multiple solution-specific agents.

![]()
Most mentioned product strengths:
Granular control over categories
Reporting and analytics
Most mentioned overall product benefits:
User-friendly interface
Scalability
Integration with other tools
Great documentation
Lightweight and efficient
Some complaints:
Frequent disruptions
Not cost-effective
Lack of Linux VPN client
Disclaimer: This review is based on information from VPN review sites such as Gartner and G2 and user feedback from Reddit, accessed on June 20, 2024.
GoodAccess
GoodAccess is a startup founded in 2020 and has since developed an affordable Zero Trust Network Access solution.
GoodAccess’ DNS filter, Threat Blocker, prevents ransomware attacks. GoodAccess uses its own DNS system to handle all DNS resolutions for every connected client. Threat Blocker, part of the larger Secure Shield package, combines open-source and commercial lists of malicious domains. It checks every DNS request against these lists. When it finds a match, Threat Blocker redirects the user to a safe website that informs them that an attempt to access a malicious domain was blocked.

![]()
Most mentioned product strengths:
Real-time data monitoring
Most mentioned overall product benefits:
Stable and reliable
Multiple platform support
Responsive support team
Reasonable pricing
Some complaints:
Newer versions cause service issues, and updates need manual intervention
High costs when adding more gateways
Limited connections per user
Hard to use for less tech-savvy people
Disclaimer: This review is based on information from VPN review sites such as Capterra, Gartner, and G2, accessed on June 20, 2024.
Cloudflare
Cloudflare One is a web filter and security solution with a secure web gateway. It is from Cloudflare, a well-known and long-standing provider, which has a global presence and higher cost.
Cloudflare One provides an authoritative DNS service, a public DNS resolver, and DNS filtering. It includes Cloudflare Gateway, a secure web gateway that offers DNS filtering, browser isolation, and other technologies. This web filter helps protect internal users and keep data secure. Cloudflare Gateway improves network security and restricts what employees access on the internet.
![]()

Most mentioned product strengths:
Customizable filtering options
Whitelist/Blacklist management
Bypass methods control
Most mentioned overall product benefits:
User-friendly interface
Responsive support team
Free trial
Some complaints:
Blocks the right websites and users
Complex setup
Interrupts communication
Customer support issues
Disclaimer: This review is based on information from the Cloudflare website and VPN review sites such G2 as Gartner, accessed on July 3, 2024.
Zscaler
Zscaler Internet Access (ZIA) has a web filter designed to improve organizations’ internet security. The tool includes many advanced features to protect users from online threats.
Zscaler offers powerful URL filtering as part of Zscaler Internet Access. It also includes a secure web gateway, data loss prevention, cloud-gen firewall, and more. Zscaler Internet Access is part of the Zscaler Zero Trust Exchange platform, which allows fast, secure connections for employees working from anywhere. This filtering software uses dynamic content categorization, integrated browser isolation, and safe search enforcement to control web traffic effectively.
![]()
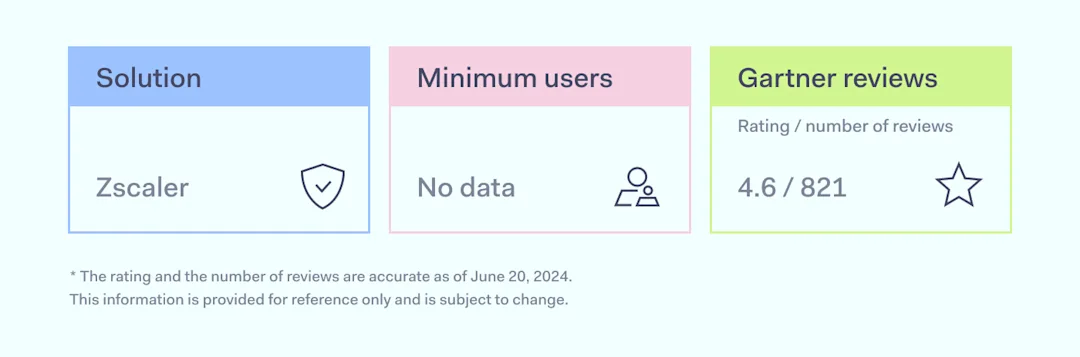
Most mentioned product strengths:
Granular control features
Real-time threat protection
Whitelist/Blacklist management
Reporting and analytics
Most mentioned overall product benefits:
Multiple platform support
Responsive support team
Some complaints:
Complex and time-consuming setup
Managing security policies is complex
Logging for different modules isn’t separate, making troubleshooting hard
Sometimes blocks essential sites
Disclaimer: This review is based on information from the Zscaler website and VPN review sites such as Gartner, G2, and Trustradius, accessed on July 4, 2024.
Cato Networks
Cato SASE Cloud is a comprehensive solution that also provides businesses with web content filtering. It offers a cloud-based service that integrates various features to ensure safe and efficient network management.
Cato’s DNS Security inspects all DNS traffic and blocks requests to malicious destinations before a connection occurs. AI-based DNS inspection delivers in-line phishing protection by analyzing webpage components, domain age, and other factors. This solution blocks malicious domains and command-and-control sites using updated threat intelligence.
![]()
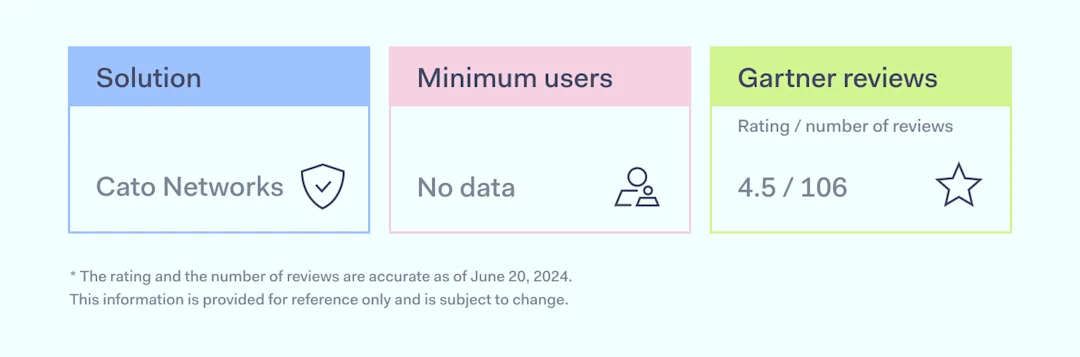
Most mentioned product strengths:
Reporting and analytics
Most mentioned overall product benefits:
Multiple platform support
Responsive support team
Integrations with other products
Some complaints:
Few technical documents available for troubleshooting
Need for careful implementation planning
Complex cloud management console navigation
Login issues with the app
Disclaimer: This review is based on information from the Cato Networks website, and VPN review sites such as Gartner and G2, accessed on June 20, 2024.
Netskope
Netskope One SASE provides a web filtering solution for enforcing acceptable use policies (AUPs) in various locations, including headquarters, remote offices, and mobile workers using company-managed devices. Netskope’s NewEdge private cloud network spans over 70 regions.
Netskope’s web filtering software helps organizations enforce AUPs using predefined and custom categories for apps, security risks, YouTube, and silent ad blocking. It covers over 120 categories and supports 200+ countries. The solution includes dynamic web page categorization, custom categories, and API-enabled updates. Netskope uses machine learning to rate new and unknown web content. Netskope Intelligent SSE, built on the Netskope Security Cloud, offers real-time data and threat protection for cloud services, websites, and private apps.
![]()
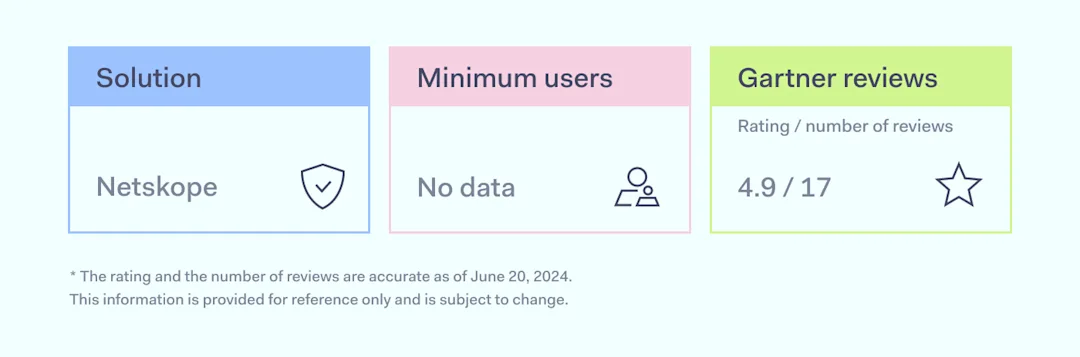
Most mentioned product strengths:
Granular policy controls
Reporting and analytics
Most mentioned overall product benefits:
Responsive support team
Integrations with other products
Low system impact
Some complaints:
Lack of granular threat protection and packet analysis
Syncing issues
Pricing structure
Lack of integration with certain tools
Limited help articles
Regular outages
Disclaimer: This review is based on information from the Netskope website and VPN review sites such as Gartner and G2, accessed on June 20, 2024.
How to choose the best content filtering solution for your business
Choosing the best web content filtering solution involves looking at your specific needs, budget, and the size of your organization. Here are seven steps to help IT admins make the best choice.
Identify your business needs. Assess what your organization requires. A small business with 20 employees might need basic web filtering software to block malicious content, while a large enterprise with over 1,000 employees may need a secure web gateway to manage complex threats and ensure compliance.
Evaluate security features. Look for solutions that provide strong security features. DNS filtering helps protect against malware and ransomware, as well as improves productivity and network performance. Real-time protection against new online threats is also helpful for high security.
Consider ease of use and management. The content filtering software should be easy to set up and manage. Simple deployment and a user-friendly interface are important, especially for businesses with limited IT resources.
Check scalability and future-proofing. Ensure the solution can grow with your business. Choose a tool that is good for scaling: the one that supports flexible deployment and integration with more Security Service Edge (SSE) frameworks like Zero Trust Network Access (ZTNA) and Firewall-as-a-Service (FWaaS).
Evaluate customization options. Your content filtering solution should allow customization to meet specific business needs. Flexibility is essential for organizations that need tailored filtering policies based on their industry, such as schools needing to block adult content while allowing educational resources.
Consider cost-effectiveness. Budget is a key factor. Look for solutions that provide comprehensive security features at a competitive price. Small businesses with tight budgets can start with minimal filtering capabilities and upgrade to more advanced solutions as they grow.
Assess support and reliability. Reliable customer support and high uptime are crucial, especially during setup and troubleshooting. Responsive support teams and detailed dashboards and analytics help IT admins manage their networks effectively.
Check provider credibility. Choose a trustworthy solution with a good track record. Look at customer reviews and brand awareness to ensure reliability and effectiveness.
Conclusion
Filtering is crucial for many reasons. Security is a major one, but it’s not the only benefit. Even if internet threats aren’t a concern, these tools boost employee productivity, protect business reputation, and improve network performance.
Whether you need comprehensive security, ease of implementation, or scalable solutions, the options listed here offer reliable and effective ways to filter content and ensure secure internet access. Evaluating your specific needs and the features of each solution helps you make an informed decision that enhances your organization’s web security and productivity.
Disclaimer: The information in this article is provided for informational purposes only and is based on publicly available third-party reviews, user feedback, and online sources as of July 5, 2024. While we strive for accuracy and completeness, Nord Security Inc. and its affiliates make no guarantees regarding the information’s accuracy, completeness, or suitability. The product rankings and comparisons are our opinions, based on our analysis of public sources and publicly described product features, and should not be considered definitive or permanent. We do not warrant or represent that any product is or will remain the best, top, or highest-ranked in any list or rating for any period of time. Product features, pricing, and other details may change, and we advise readers to verify these directly with vendors. We disclaim liability for any errors, omissions, or actions taken based on this information. The inclusion of competitor products does not imply endorsement, and all trademarks mentioned are the property of their respective owners. Readers should conduct their own research and seek independent advice before making purchasing decisions.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.






)



)
) As the digital world continues to expand and evolve, the need for secure authentication is more critical than ever. Enter passkeys – a modern solution for secure authentication that provides a safer and more convenient way to access apps and websites without ever having to remember or type out a password. Today, we’re looking into the world of passkeys, explaining what they are, how they work, and why they’re considered the future of authentication.
As the digital world continues to expand and evolve, the need for secure authentication is more critical than ever. Enter passkeys – a modern solution for secure authentication that provides a safer and more convenient way to access apps and websites without ever having to remember or type out a password. Today, we’re looking into the world of passkeys, explaining what they are, how they work, and why they’re considered the future of authentication.