In 2024, increased attacks on serverless technologies, predicted by Google Cloud’s Security report, became a reality. Misconfigured cloud environments contributed to 30% of incidents in the first half of the year. That’s why it’s important not only to choose a robust Secure Access Service Edge (SASE) cybersecurity solution but also to ensure it is properly configured to protect your company.
In this article, we’ll compare Check Point alternatives, including NordLayer, Fortinet, and Zscaler, to help organizations find the best solutions for enhanced security and protection.
In brief,
Check Point, Fortinet, and Zscaler are enterprise-level providers with effective but costly and complex solutions.
While NordLayer doesn’t cover all SASE features, it offers a highly-rated solution with some SSE features (part of SASE). It also stands out for its proactive configuration assistance and 24/7 support.
Let’s explore these solutions and see which one might best suit your organization’s protection and security needs.
Check Point software overview
Check Point Software is a long-standing player in the cybersecurity market. It was founded in 1993 and has offices around the world, including in sanctioned countries such as Russia and Belarus.
Check Point offers a wide array of cybersecurity software solutions, but here are the main five areas.
Cloud (Check Point CloudGuard): Provides cloud security services to protect public, private, and hybrid environments. It includes firewall, threat prevention, and posture management software.
Security for remote users (Harmony): Protects remote users with endpoint security tools. Harmony secures devices, web browsing, email, and collaboration software solutions.
Security ops (Horizon): Supports security operations by providing services for threat detection, incident response, and automation.
Network security (Quantum): Delivers advanced firewall and intrusion prevention services to protect networks.
All (Infinity Platform): Integrates multiple security products into one platform. This product covers network, cloud, and endpoint security.
As you can see, Check Point offers a wide range of products that can address various security needs from a product standpoint.
Most mentioned product strengths
Check Point Software offers features that help to secure various network infrastructure and cyber security aspects. Here are some mentioned by users:
Secure network access for businesses
Advanced threat prevention and real-time threat detection
Zero Trust Network Access (ZTNA) features
Deep packet inspection and SSL inspection
Firewall with VPN access management for remote users
Geo-location filtering and detailed URL filtering
Zero-day attack protection with quick patch updates for vulnerabilities
Network mapping and compliance testing across environments
Environment-specific reports generated for better oversight
Most mentioned overall product benefits of Check Point
Here are some things users often mentioned about Check Point products overall:
Well-known and respected in the industry
Reliable and effective
Unified security management system
Centralized firewall management with easy server integration
User-friendly interface
Minimal need for daily adjustments after the setup
Limitations of Check Point
Despite its strengths, Check Point Software may have some limitations that might not align with the needs of every organization. They might include:
Complicated and costly pricing
Complex setup and configuration
Slowing down during heavy traffic
Difficult advanced features and services
Slow, upgrade-focused support
Overwhelming product range
Lacks competitive SD-WAN alternatives
VPN client issues on MacOS
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as Gartner, G2, and Reddit. It also assessed customer feedback shared on these platforms, accessed on August 13, 2024.
Let’s look at Check Point alternatives.
1. NordLayer
Overview of NordLayer
NordLayer is a network security solution designed to provide safe access to company resources from any location. It provides protection for networks, facilitates remote work, and aids in meeting compliance requirements. Developed by Nord Security, the creators of the popular NordVPN service, NordLayer offers a multi-layered defense for your network.
NordLayer assists organizations in implementing Firewall as a Service (FWaaS), Zero Trust Network Access (ZTNA), and Secure Web Gateway (SWG) principles, with a focus on the Secure Service Edge (SSE). It delivers SaaS security features to control access to the internet, resources, and networks.
NordLayer’s flexibility makes it a good fit for businesses of all sizes that need scalable protection.
Product strengths
![]()
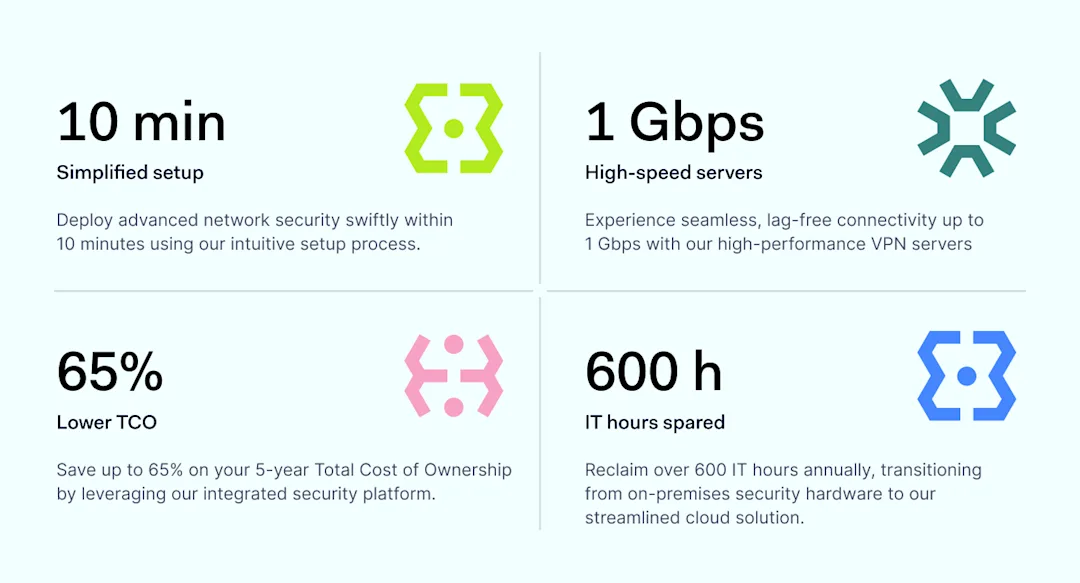
NordLayer addresses three key business needs. First, it helps enable secure internet access, including for remote employees, and protection while browsing. Second, it segments and controls access to company resources. Third, it helps companies ensure compliance with key cybersecurity regulatory frameworks through easy-to-use visibility dashboards and straightforward identity and access management.
NordLayer primarily focuses on network protection and provides key SSE features, including:
Shared gateways and virtual private gateways
Quantum safe encryption
Dedicated servers with Fixed IP
Cloud Firewall
Device Posture Security
IP allowlisting
Web protection (formerly Threatblock)
DNS Filtering capabilities
NordLynx VPN protocol
Browser Extension that enhances performance while ensuring secure browsing
Overall product benefits of NordLayer
Compared to larger solutions discussed in this article, NordLayer offers several key advantages:
Transparent pricing, with plans starting at $7 per user per month
Proactive setup support to minimize misconfiguration risks
24/7 live support, dedicated account managers, and personalized assistance
Direct influence on product development and growth
Limitations of NordLayer
Despite its many strengths, NordLayer has some limitations:
Less established brand and not as widely recognized
Fewer features and capabilities
Slows down the internet connection when using the VPN
Can’t adjust team size online; need to contact support to downgrade
Sometimes, NordVPN and NordLayer are confused
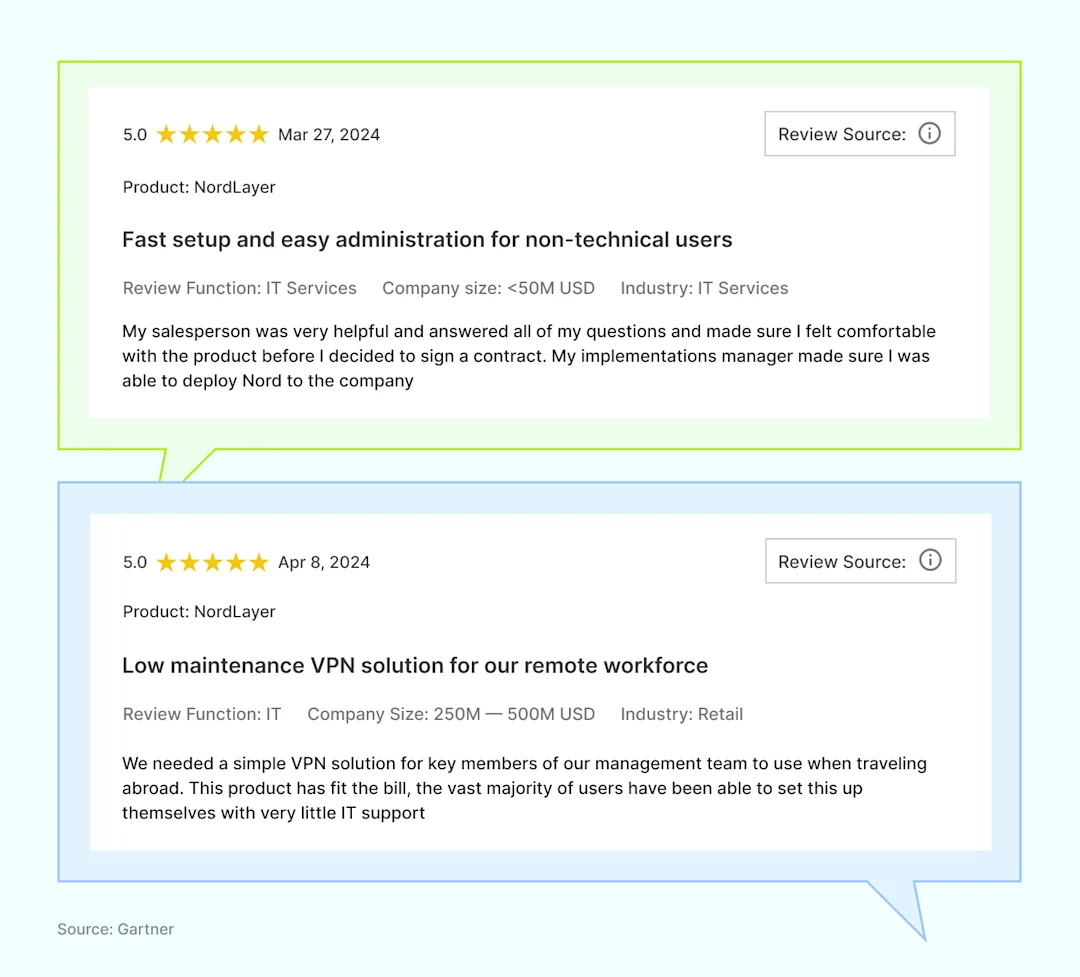
NordLayer reviews
Users frequently praise NordLayer for its ease of use, even for those without extensive IT knowledge. They also appreciate the helpful support provided at every stage.
Disclaimer: This product review is based on information provided on our website, VPN review sites and social networking forums such as Gartner, G2, and TechRadar. It also assessed customer feedback shared on these platforms, accessed on August 13, 2024.
2. Fortinet
Overview of Fortinet
Fortinet is a well-known cybersecurity provider, established over 20 years ago in California. Overall, Fortinet is a versatile option for medium to large enterprises protection.
The company specializes in network security, unified SASE, and cloud security for enterprises. While Fortinet does offer solutions for small and midsize businesses, user reviews suggest that it is particularly well-suited for large companies that can benefit from using multiple Fortinet products together.
Most mentioned product strengths
Fortinet’s products are designed to offer comprehensive security services with a focus on performance and scalability.
Well-built, stable hardware, particularly for perimeter firewalls
Next-Generation Firewall featuring AV, IPS, web filtering, application control, and VPN
Advanced Threat Protection
Functions as a wireless controller at no additional cost
FortiGuard Labs threat intelligence
FortiGuard services, including antivirus, data loss prevention, and anti-spam
SecureFabric for isolated communications
Most mentioned overall product benefits of Fortinet
Fortinet stands out due to its strong performance capabilities and broad security features that cater to various business needs.
Intuitive and easy-to-use GUI
Full-stack, single-pane integration
SSL VPN with no extra licensing
Easy firewall configuration
Centralized control and visibility
Cost-effective
Simple management and customization
Easy implementation across platforms
Consistent OS across all devices
Limitations of Fortinet
While Fortinet offers extensive features, it may also have some drawbacks, depending on an organization’s specific needs.
Limited technical support for security products
Logging lacks real-time information and is hard to navigate
Complex configuration and firewall software syntax
VPNs frequently drop, affecting customer experience
Documentation is complex and lacks vital information
The learning curve for rich security features
High license costs, challenging for small-scale organizations
Frequent bugs impact product reliability
Manual firmware updates hinder customer experience
Needs flexible pricing and service options to protect smaller organizations
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as Gartner, G2, and Reddit. It also assessed customer feedback shared on these platforms, accessed on August 13, 2024.
3. ZScaler
Overview of ZScaler
ZScaler, founded in 2007 and based in California, specializes in a cloud-native Zero Trust Exchange platform designed to protect customers from cyber-attacks and data loss. As a cloud-based security service provider, ZScaler focuses on securing internet traffic and managing user access to applications.
Most mentioned product strengths
ZScaler provides a range of capabilities designed to enhance security and manageability for organizations that operate in distributed and cloud environments.
Wide array of security features
Numerous customizable options
Granular control in creating security policies
Easy-to-generate reports
Most mentioned overall product benefits of ZScaler
ZScaler’s cloud-native approach and focus on zero trust make it a strong contender in the cybersecurity market.
High performance
Reliable connectivity
Stable cloud-native architecture
Centralized access management and security visibility
User-friendly interface
Scalable at any time
Limitations of ZScaler
Although ZScaler is innovative, it has drawbacks that might not suit every organization.
Complex migration from legacy VPN to cloud-based Zero Trust Network Access
The steep learning curve for users
Incorrect URL classifications affecting security
Disconnection during brief internet fluctuations
Lacking detailed API documentation
Poor customer support and response
Time-consuming setup process
Confusing pricing information for services and products
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as Gartner and G2, and it assesses customer feedback shared on these platforms, accessed on August 20, 2024.
Choosing the right network security solution
Finding the right network security solution is crucial for your organization’s protection and growth. Here’s what to focus on:
Ensure the software integrates well with your current systems
Assess firewall capabilities that match your organization’s needs
Review each option’s ability to scale with your organization
Prioritize ease of use for smooth implementation and management
Evaluate the provider’s support and customer service
Start by considering these factors to secure your organization effectively.
Disclaimer: The information in this article is provided for informational purposes only. It is based on publicly available third-party reviews, user feedback, and online sources accessed between August 13, 2024, and August 20, 2024, and should not be considered definitive or permanent. While we strive for accuracy and completeness, Nord Security Inc. and its affiliates make no guarantees regarding the information’s accuracy, completeness, or suitability. We do not undertake, warrant, or represent that any product, or its feature, is or will remain publicly regarded as better or worse than other alternatives, serve any purpose, has mentioned features, benefits, strengths, and limitations for any period of time. Product features, pricing, and other details may change, and we advise readers to verify these directly with vendors. We disclaim any liability to any party for any errors, omissions, or actions taken based on this information. The inclusion of competitor products does not imply affiliation or endorsement, and all trademarks mentioned are the property of their respective owners. Readers should conduct their research and seek independent advice before making purchasing decisions.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.






)
)
)
)
)
)
)
)
)