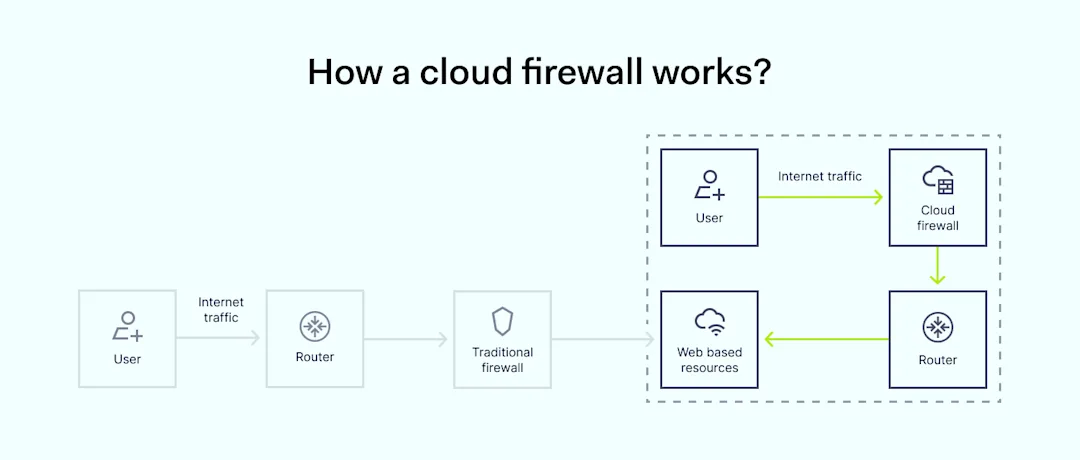
Since the first commercial firewall in 1991, network security needs and technology have evolved significantly. While many businesses still use hardware firewalls, the rise of virtual network firewalls has made it easier to achieve the same functionality without the maintenance and complexity of physical firewalls.
Software firewalls offer effective network protection in a simpler, easier-to-manage way compared to hardware options. This article reviews our top 10 picks for software network firewalls to help you choose the best one for your business.
How we chose the best network firewall solutions (in our opinion)
We selected a range of network firewall options, including large enterprise solutions, mid-size businesses with similar features, and smaller companies that may not be as developed but still provide strong functionality. We didn’t go into too many details, but we focused on how well the firewall strengthens network security and how easy it is to set rules relating to the user interface. We also looked at the overall benefits of each firewall vendor and what types of clients they suit. We also considered cost-effectiveness and how comprehensive these solutions are.
We checked reviews and user feedback on sites like Gartner, G2, Reddit, and Capterra. We focused on what users said about cost, performance, next-generation firewalls, feature reliability, and how helpful the support teams were. If we found unusual feedback about a specific firewall provider that users often mention, we included it as well.
Top 10 network firewall solutions, in our opinion
Different solutions suit different business types. Here’s a detailed look at our favorite network firewall solutions available today, listed in no particular order:
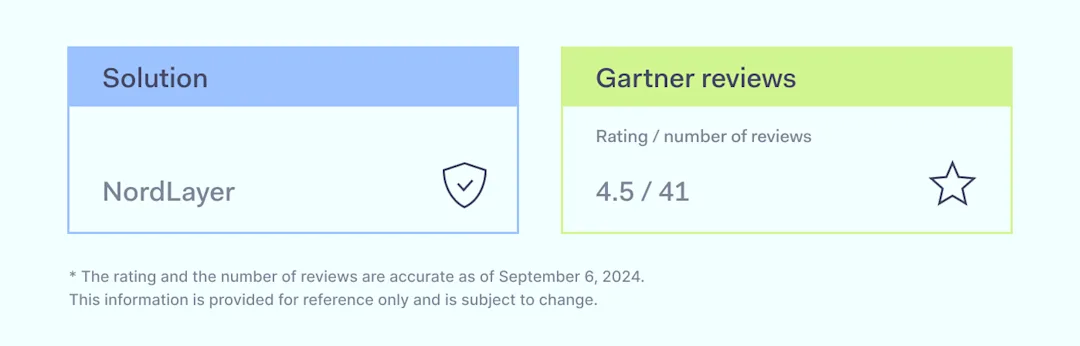
NordLayer
Cato SASE Cloud
Fortinet: FortiGate VM
Palo Alto VM Series
Cloudflare WAF
Zscaler Internet Access
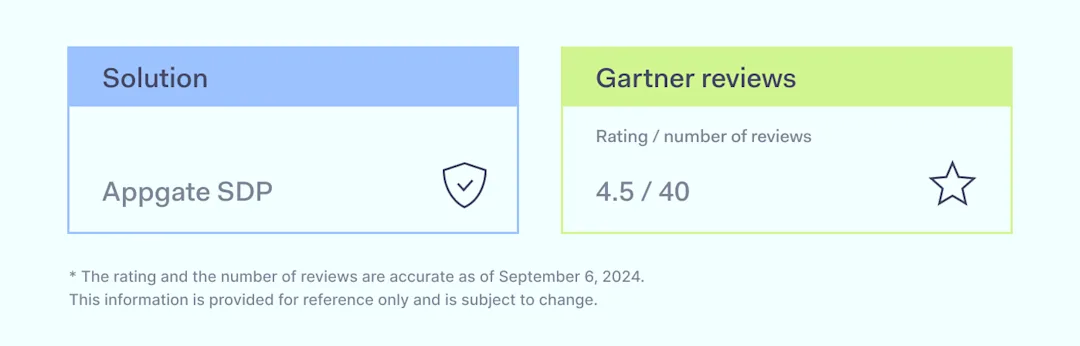
Appgate SDP
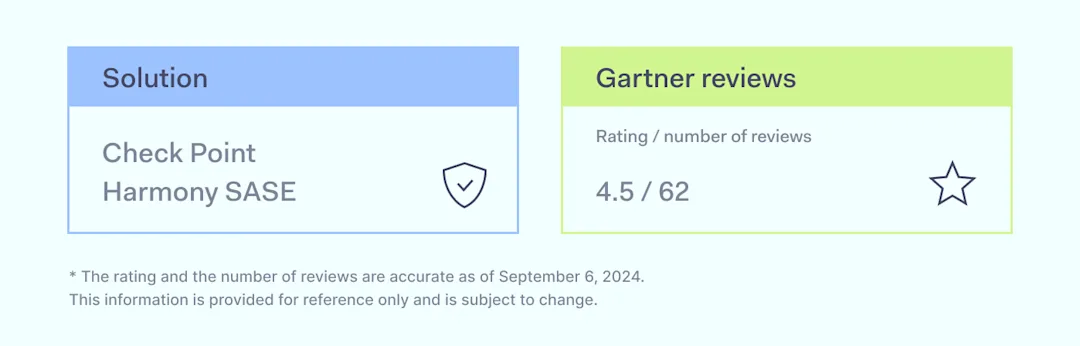
Perimeter 81 (Check Point Harmony SASE)
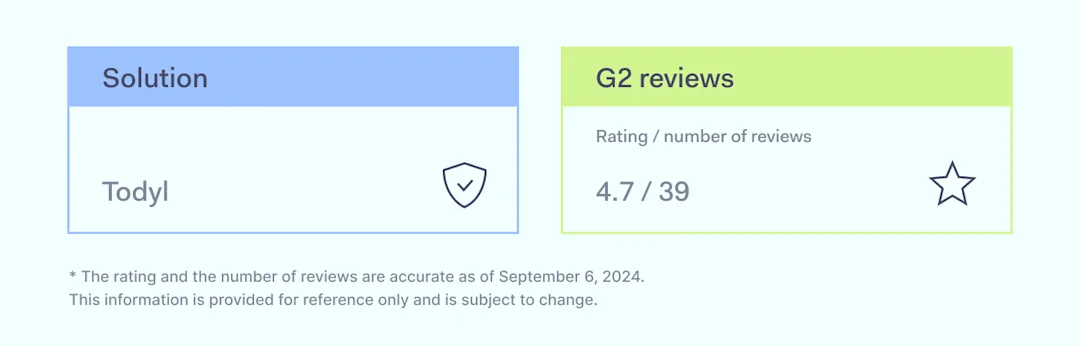
Todyl
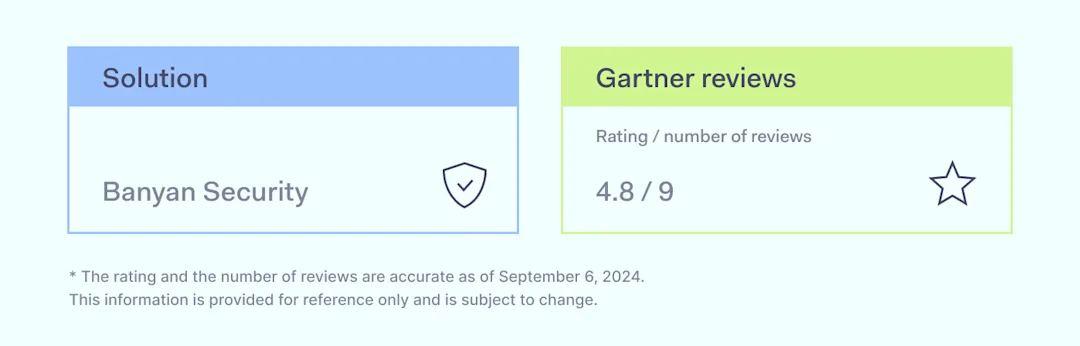
Banyan Security
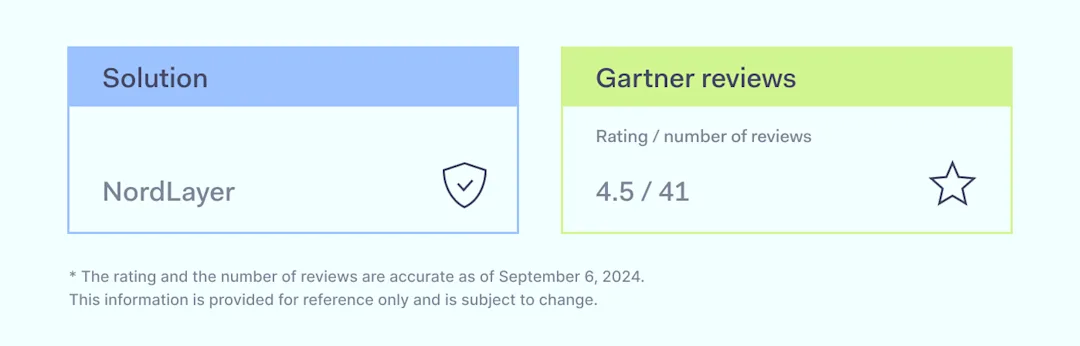
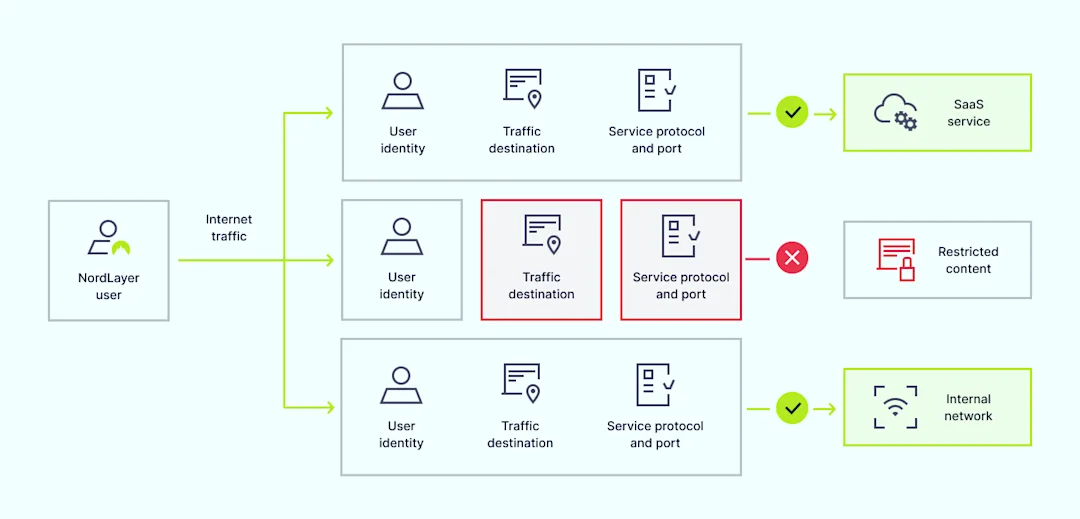
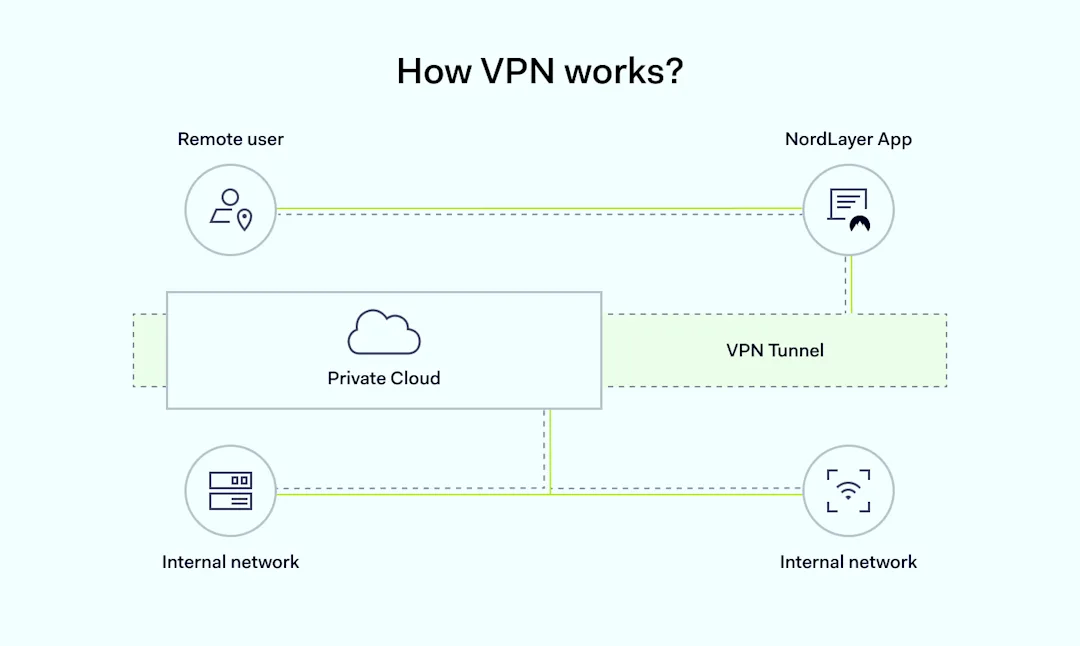
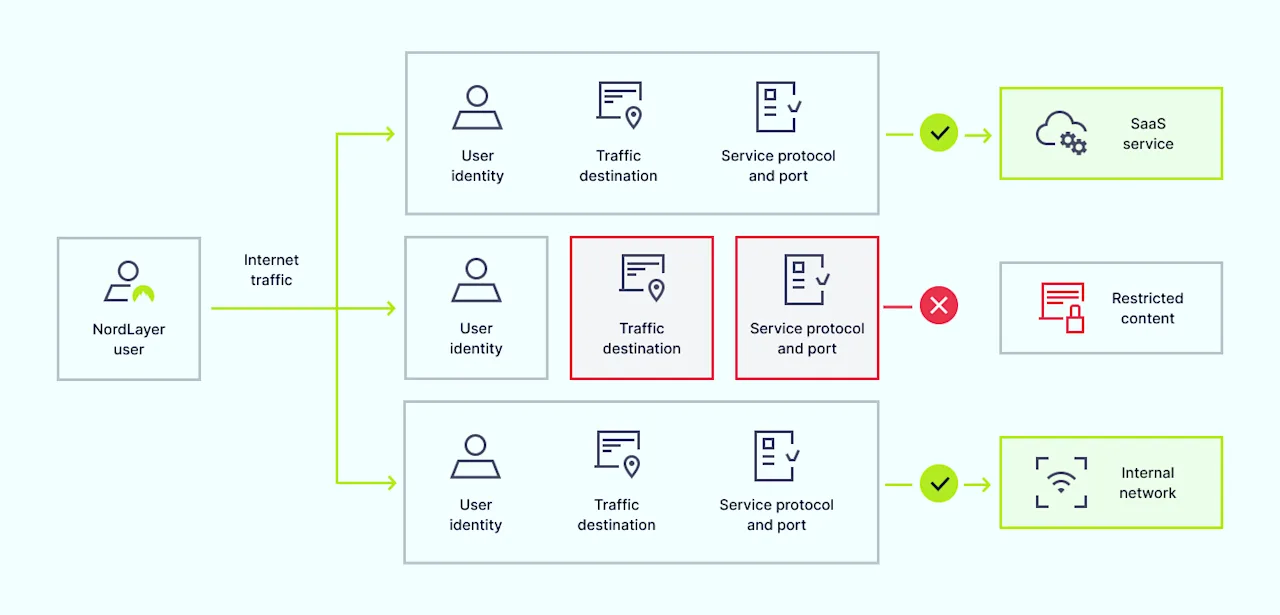
NordLayer is a network security solution that offers secure access to company resources from any location. It helps protect networks, enables remote work, and provides the tools necessary to comply with key regulatory frameworks. Developed by Nord Security, the creators of NordVPN, NordLayer offers a multi-layered defense and features typical of next-generation firewalls (NGFW).
NordLayer enables organizations to implement Firewall as a Service (FWaaS) along with Zero Trust Network Access (ZTNA), and Secure Web Gateway (SWG) principles.
Five ways NordLayer Cloud Firewall can help:
Prevent data leaks. Network segmentation is key in access control. Without it, data leaks are more likely.
Achieve compliance. Many standards focus on network access control and protection of network and encrypted traffic.
Implement security strategy. Best practices include secure access service edge (SASE), FWaaS, SWG, and ZTNA.
Unify security across hybrid setups. Securing a mix of data centers, cloud, and on-premise systems can be challenging, but NordLayer helps simplify this.
Support hybrid work models. NordLayer strengthens security for remote teams while managing network firewalls across locations.
NordLayer’s flexibility makes it ideal for businesses of all sizes that need scalable network protection. It provides secure internet access, resource protection, and compliance with major cybersecurity regulations.
Apart from Cloud Firewall, NordLayer offers other security features like:
Quantum-safe encryption
Dedicated servers with Fixed IP
Device Posture Security
IP allowlisting
Web protection (formerly ThreatBlock)
DNS filtering
NordLynx VPN protocol
Browser extension for secure browsing
Benefits:
Transparent pricing, starting at $7 per user per month
Proactive setup support
24/7 live support with dedicated account managers
Direct user feedback influences product development
Drawbacks:
Less known compared to other competitors
Fewer security features than large enterprise firewall vendors
Possible slowdowns with the use of VPN
Reducing team size requires reaching out to support
Occasional confusion between NordVPN and NordLayer
Disclaimer: This product review is based on information provided on our website, VPN review sites and social networking forums such as Gartner, G2, and TechRadar, as well as customer feedback shared on these platforms, accessed on September 6, 2024.
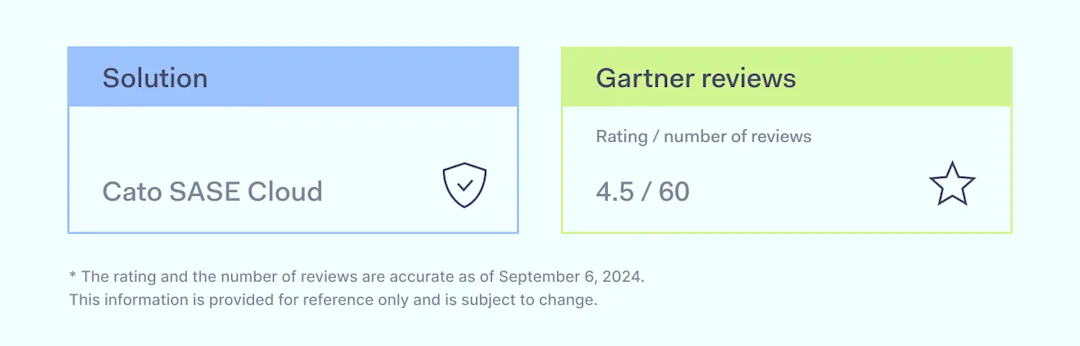
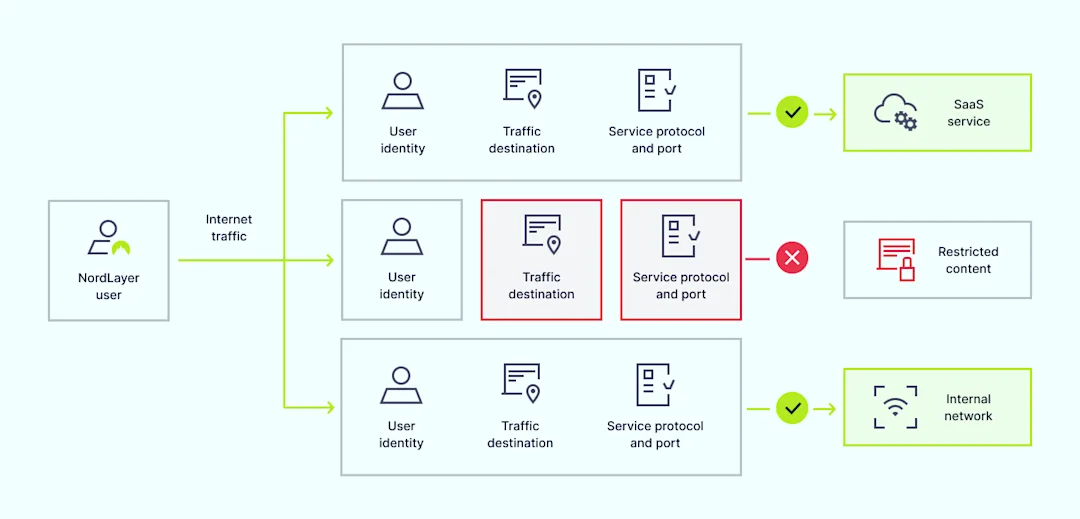
2. Cato SASE Cloud
Cato Networks is an Israeli company that offers Secure Access Service Edge (SASE) technology. The platform combines communication and security in a cloud-based solution. Founded in 2015, Cato Networks now employs over 900 people globally. When it comes to the firewall, users frequently mention that the solution is easy to set up, with straightforward firewall rule management and affordability. It simplifies firewall management and offers features typical of NGFW.
Most mentioned overall product benefits:
Comprehensive security features
Complete management panel for easy user control
Low-latency performance through numerous points of presence (PoPs)
Reliable, with no impact on internet speed or application performance
Automatic firewall updates
Agile and scalable solution
Drawbacks:
Can be difficult to implement
License costs are high
Logs and reports are hard to interpret
VPN licenses must be purchased in packs of 10
Sometimes the app fails to log in
Upgrading bandwidth capacity for a site can be costly
Disclaimer: This product review is based on information provided on the company’s website, VPN review sites and social networking forums such as Gartner and G2, and it assesses customer feedback shared on these platforms, accessed on September 6, 2024.
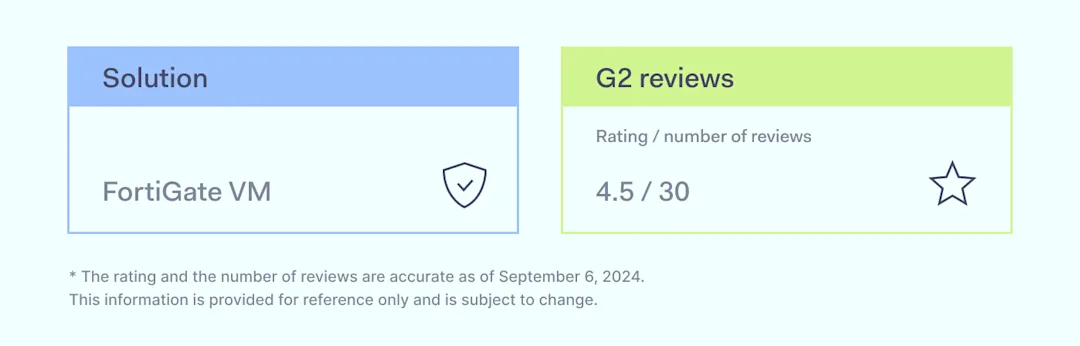
3. Fortinet: FortiGate VM
Fortinet, founded over 20 years ago in Sunnyvale, California, provides cybersecurity solutions for a wide range of users. FortiGate VM—a virtual firewall—offers network protection in private, public, and telco cloud environments. Running on the same OS as FortiGate hardware, it enforces consistent security policies across hybrid setups.
Most mentioned overall product benefits:
User-friendly interface
Straightforward setup and management of virtual machines
Easy integration in virtual environments
Works well with multivendor environments, including IaaS and public clouds
Drawbacks:
More advanced tutorials or documentation needed
Complex configurations
Some interface complexities
High entry pricing
Logging and reporting issues
Problems integrating with certain XDR solutions
Sizing virtual environments could be clearer
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as G2, and it assesses customer feedback shared on these platforms, accessed on September 6, 2024.
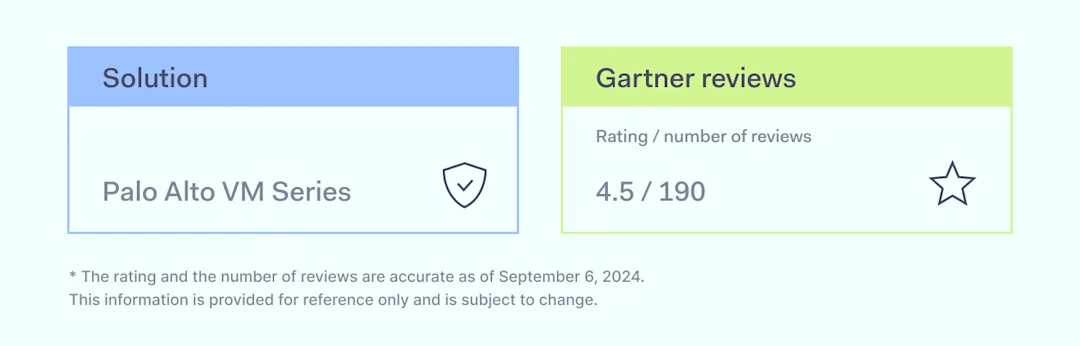
4. Palo Alto VM Series
Palo Alto Networks is a multinational cybersecurity company based in Santa Clara, California. Its platform includes advanced network firewalls and cloud-based solutions that cover various aspects of security. The company serves over 70,000 organizations worldwide. Users praise the firewall’s strong security features, ease of use, and flexibility, which are on par with those of on-premises network firewalls.
Most mentioned overall product benefits:
Easy deployment
Flexible and scalable
Effective for disaster recovery
Centralized management
User-friendly interface
Drawbacks:
High pricing
Licensing complexity
Long upgrade and restart times
Documentation could be improved
Occasional performance slowdowns
Limited integrations with some cloud platforms
Resource-intensive solution
Disclaimer: This product review is based on information provided on the company’s website, VPN review sites and social networking forums such as Gartner and G2, as well as customer feedback shared on these platforms, accessed on September 6, 2024.
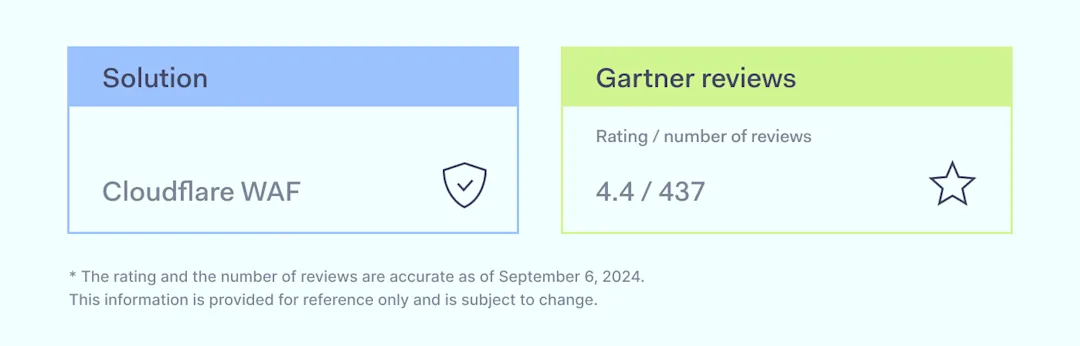
5. Cloudflare WAF
Cloudflare is an American company that offers content delivery networks, cloud cybersecurity, DDoS mitigation, and domain services. As of 2024, over 19% of the internet uses it for web security. Its Web Application Firewall (WAF) features managed rulesets that are frequently updated, geolocation blocking, and proxy detection, making it highly effective in preventing man-in-the-middle attacks. Users also note its useful integrations, such as with Azure AD and Google Cloud.
Most mentioned overall product benefits:
Easy installation
Simple to monitor with actionable features
Extremely effective with customizable options
User-friendly interface
Straightforward to use
Drawbacks:
Hard for small businesses to negotiate pricing and add features
Limited configurations in the Terraform provider
Implementing network-based rules through code is difficult
Documentation lacks specific, in-depth configurations
Some false positives in traffic blocking, though fixable over time
Slow customer support responses
Limited flexibility in rate-limiting rules for APIs
Load balancing requires an additional license
Disclaimer: This product review is based on information provided on the company’s website, VPN review sites and social networking forums such as Gartner and Reddit, and it assesses customer feedback shared on these platforms, accessed on September 6, 2024.
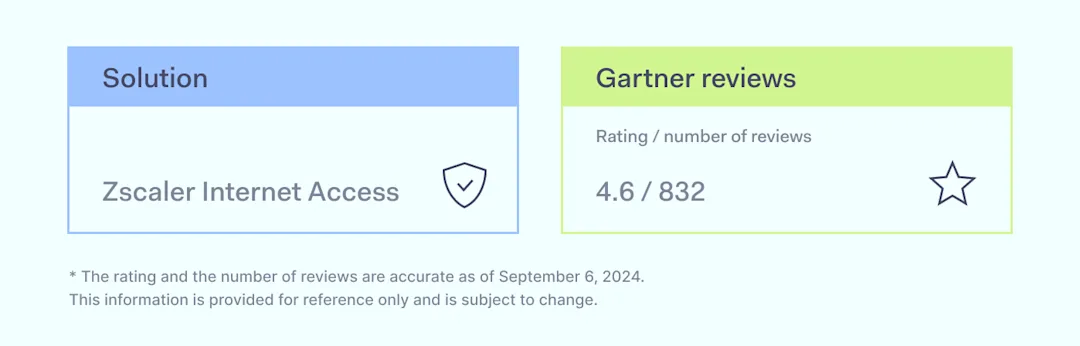
6. ZScaler Internet Access
Established in 2007 and headquartered in California, ZScaler provides a cloud-native Zero Trust Exchange platform that focuses on securing online traffic and controlling access to applications. It offers cloud-based protection against cyber threats and data loss. As for its firewall features, users point out that ZScaler offers a broad range of security tools and flexible options, making it adaptable for cloud-based setups.
Most mentioned overall product benefits:
Scalable
Consistent and stable connectivity
Efficient centralized management for access and security oversight
Robust cloud-native infrastructure
Intuitive interface for users
High-performance security solution
Drawbacks:
Complicated migration from traditional VPN to Zero Trust Network Access
Steep learning curve for new users
URL misclassifications that affect protection measures
Disconnects during brief internet interruptions
Inadequate API documentation
Slow customer service response
Lengthy setup and configuration process
Confusing pricing structure for features and services
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as Gartner and G2, as well as customer feedback shared on these platforms, accessed on September 6, 2024.
7. Appgate SDP
Appgate, founded in 2020 and based in Coral Gables, Florida, provides security solutions for organizations and government agencies. It focuses on Universal Zero Trust Network Access (ZTNA) and fraud protection. As for the firewall functionality, users mention that Appgate SDP is straightforward to manage with helpful troubleshooting documentation.
Most mentioned overall product benefits:
Stable performance
Fast operation
Easy to deploy and manage
Clear documentation for troubleshooting
Real-time updates based on risk metrics
Micro-segmented access to resources
Intuitive user interface
Drawbacks:
Runs on Ubuntu Server, which is not frequently updated
Per-site licensing increases overall costs
Slow connection speeds to remote sites
Occasional resource reduction despite steady internet bandwidth
Complex to configure
Limited log management features
Dashboard is not very helpful for security monitoring
Frequent need to restart due to slow connection despite good internet
Insufficient dashboard information for identifying node connectivity issues
Centralized management lacks efficiency
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as Gartner and G2, as well as customer feedback shared on these platforms, accessed on September 6, 2024.
8. Check Point Harmony SASE (formerly Perimeter 81)
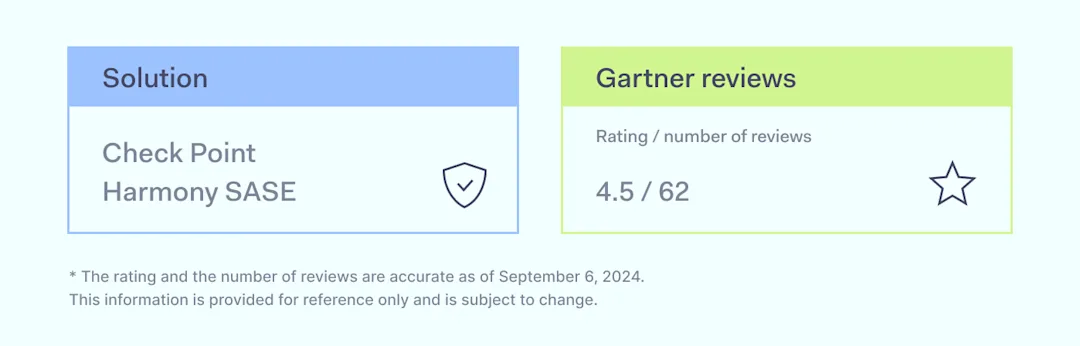
Check Point Software Technologies offers solutions to protect businesses and governments. Founded in 1993, it employs over 6,000 people and protects more than 100,000 organizations. Check Point Harmony SASE, formerly known as Perimeter 81, combines network and endpoint security for a unified approach. As for the firewall capabilities, users note easy troubleshooting due to log visibility and VPN tunnel stability.
Most mentioned overall product benefits:
Smooth migration with easy configuration of necessary features
Smart Console is user-friendly and free of software bugs
Unified platform integrating network and endpoint security
Proactive threat prevention and real-time monitoring
Simplified management with enhanced visibility across the IT environment
Reliable performance
Useful logging activity in the dashboard
Drawbacks:
Unable to establish redundant VPN tunnels with cloud environments
Support failed to detect misconfiguration, leading to significant downtime
Complex initial setup, steep learning curve for new users
Integration challenges with third-party vendors
High pricing structure
Difficulty getting timely technical support
Frustration with poor customer service and unresolved issues
Issues with overbilling and slow responses from the support team
Logging activity is unreliable, with users questioning its accuracy
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as Gartner and G2, as well as customer feedback shared on these platforms, accessed on September 6, 2024.
9. Todyl
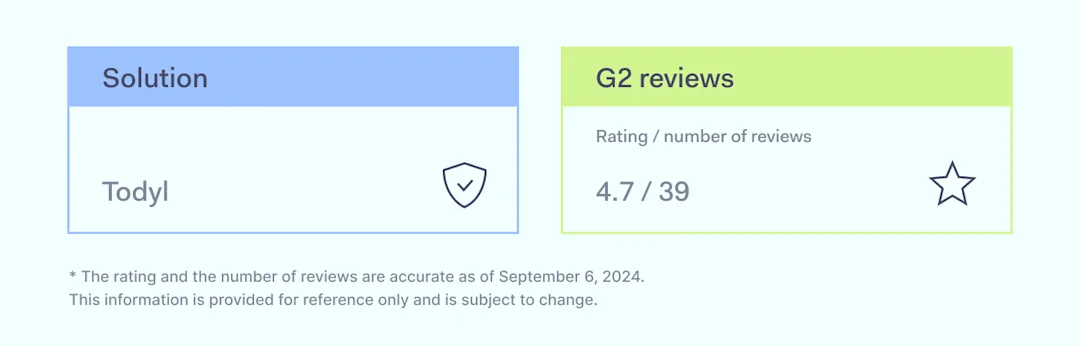
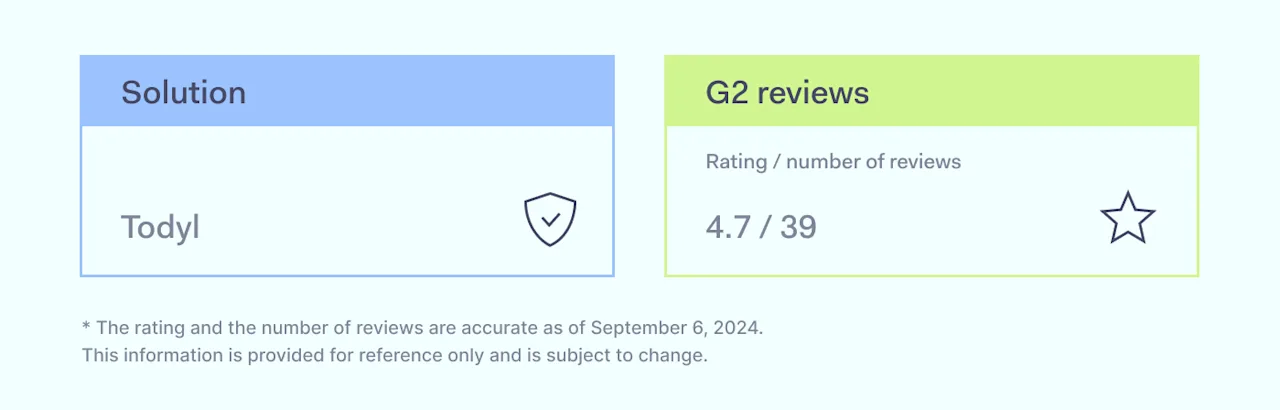
Founded in 2015 and headquartered in Denver, Colorado, Todyl offers a cybersecurity platform designed for MSPs and MSSPs. The platform provides comprehensive security solutions through a single-agent model, allowing businesses to customize capabilities to meet their needs. Users frequently note that Todyl’s integration and ease of deployment stand out as key features.
Most mentioned overall product benefits:
Easy to use
Top-notch support
Intuitive interface
Simple integration and deployment
All-in-one solution for clients
Centralized logs in the SEIM
Flexible licensing options per device and customer
Drawbacks:
Simultaneous use with Defender may cause reporting issues
Lacks custom gauge creation for dashboards
Missing GRC features
Setup can sometimes be tricky
Occasional bugs with the SGN Connect agent disappearing from the system tray
Web filtering can be clumsy
Marketing strategies have upset users
Platform lacks maturity
Connecting to on-premise devices like servers is difficult
Site-to-site connection often disconnects
Hard to cancel the service
Frequent DNS issues and workarounds needed
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as G2 and Reddit, as well as customer feedback shared on these platforms, accessed on September 6, 2024.
10. Banyan Security
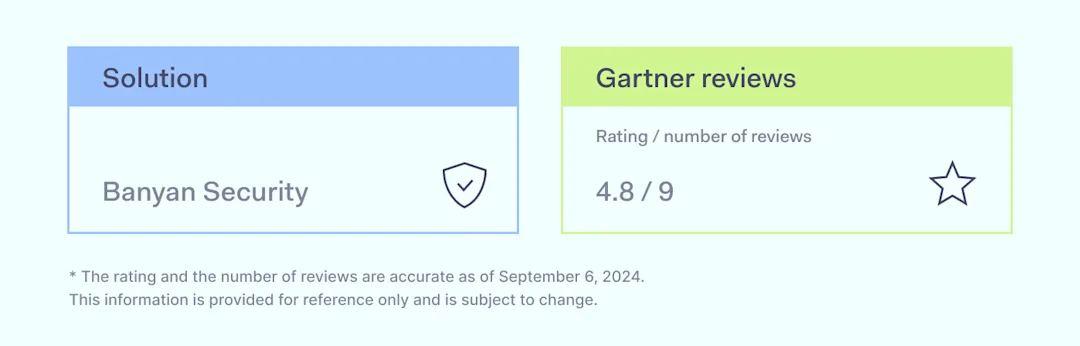
Banyan Security, recently acquired by SonicWall, provides a Zero Trust Network Access (ZTNA) solution focused on securing remote access to applications and resources. It is known for strong visibility and auditing features along with a user-friendly experience.
Most mentioned overall product benefits:
Good visibility and auditing features
Easy to use
More affordable than competitors
Drawbacks:
Integration challenges
Higher costs for some features
False positives in security alerts
Some rough edges in the platform
Disclaimer: This product review is based on information provided on VPN review sites and social networking forums such as Gartner, G2, Capterra and Reddit, as well as customer feedback shared on these platforms, accessed on September 6, 2024.
Key features to look for in a firewall
Focus on features that provide strong network protection while meeting the specific needs of your business. The right firewall solution should offer visibility, easy integration, and scalability to ensure nothing gets misconfigured as your company grows:
Visibility and control. A good firewall solution needs to provide deep insight into your network traffic and applications, especially for businesses needing access control to meet regulations. Next-generation firewalls with strong threat intelligence can help you stay compliant.
Easy integrations. Ensure the firewall provider offers solutions that integrate well with your current systems, like deep packet inspection tools or data centers. It should strengthen your overall network security by fitting smoothly with your other security features.
Updates and maintenance. Choose firewall vendors that provide regular updates and proactive product development. Focus on solutions that are frequently updated, well-maintained, and show consistent growth. Providers should offer public release notes, regular updates, and clear communication with customers. It’s crucial to ensure that security features stay current. Automated updates and clear versioning also reduce manual work for IT teams,
Hybrid network support. If your business operates across both on-premises and cloud setups, choose a firewall solution that supports hybrid infrastructures.
Scalability. As your business grows, your firewall solution should scale without significant cost increases. For example, as your setup becomes more complex, you’ll need more firewall rules. It’s wise to check the number of rules included in each plan before purchasing, as the cost difference between plans can sometimes be steep. This helps maintain strong network protection as your infrastructure expands.
When picking a firewall, focus on features that offer strong security and fit your setup. Prioritize solutions with automation features to reduce manual work. It will save time and help manage security across complex infrastructures.
How to choose the best firewall for your business
When picking the right firewall for your company, you need to weigh several important factors:
Security needs. Start by assessing your network security risks. If you’re a larger organization facing more threats, choose a next-generation firewall with a strong intrusion prevention system, advanced threat intelligence, and encryption to protect sensitive data across all layers. Smaller businesses should focus on essential features like packet filtering, malware defense, and network monitoring without overcomplicating the setup. Make sure the firewall solution aligns with the size and complexity of your network to avoid unnecessary costs or gaps in protection.
Ease of use. The firewall should be easy to deploy and manage, especially if your IT resources are limited. Network firewalls with simple, user-friendly interfaces can reduce the time spent on managing network protection. Opt for solutions that offer automation for tasks like network traffic monitoring, deep packet inspection, and access control to save time.
Support. Reliable customer support is crucial when setting up and maintaining a firewall. A firewall vendor that provides 24/7 support ensures issues are resolved quickly, minimizing downtime. If your business uses data centers or hybrid cloud setups, look for a vendor that offers proactive support to avoid misconfigurations and keep your security features running smoothly.
Cost. While the price is important, consider the long-term value. Cheaper options may lack the scalability and advanced features you’ll need as your business grows. Make sure the solution can scale with your business, especially if you expand your data centers or cloud environments, without incurring hefty costs when upgrading.
Compatibility. Ensure the firewall integrates seamlessly with your existing infrastructure, whether it’s cloud services, VPNs, or identity management systems. A firewall that works well with other security tools, such as intrusion prevention systems and threat management platforms, strengthens your overall network security and prevents integration issues.
Performance and scalability. As your business grows and network traffic increases, your firewall must be able to handle the additional load without sacrificing performance. Whether securing sensitive resources or managing remote access, the firewall should maintain consistent network protection and scale efficiently to meet your evolving needs.
Overall, different firewall solutions suit different business needs. Large options like Fortinet and Palo Alto are ideal for enterprises. Mid-sized businesses may find NordLayer or Perimeter 81 effective, while Todyl targets MSPs and MSSPs. Smaller options like Banyan Security fit smaller budgets. Choose based on your security needs and resources.
Disclaimer: The information in this article is provided for informational purposes only. It is based on publicly available third-party reviews, user feedback, and online sources accessed on September 6, 2024, and should not be considered definitive or permanent. While we strive for accuracy and completeness, Nord Security Inc. and its affiliates make no guarantees regarding the information’s accuracy, completeness, or suitability. We do not undertake, warrant, or represent that any product, or its feature, is or will remain publicly regarded as better or worse than other alternatives, serve any purpose, has mentioned features, benefits, strengths, and limitations for any period of time. Product features, pricing, and other details may change, and we advise readers to verify these directly with vendors. We disclaim any liability to any party for any errors, omissions, or actions taken based on this information. The inclusion of competitor products does not imply affiliation or endorsement, and all trademarks mentioned are the property of their respective owners. Readers should conduct their research and seek independent advice before making purchasing decisions.
:format(avif))







:format(avif))