Practical strategies for securing your digital infrastructure beyond human users.
In today’s complex digital environment, machines are often the majority of users accessing systems and data. This presents a new challenge for Chief Information Security Officers (CISOs) and their teams: how to manage and secure these non-human “machine identities.” A failure in this area can lead to costly outages, data breaches, and a lack of control over your infrastructure.
Types of Critical Machine Identities
API Keys and Secrets
These provide programmatic access to services, often bypassing standard security controls. They are a common source of vulnerability if not properly managed, as they can lead to unauthorized access and API security gaps.
Service Accounts
These accounts enable automated operations across systems. They are a significant part of an organization’s identity landscape, and securing them is essential to prevent misuse and credential sprawl.
TLS/SSL Certificates
Certificates secure communication across thousands of endpoints. When they expire or are mismanaged, they can cause major vulnerabilities and disrupt access to critical services. Proper lifecycle management is key to preventing these issues.
Core Strategies for Management
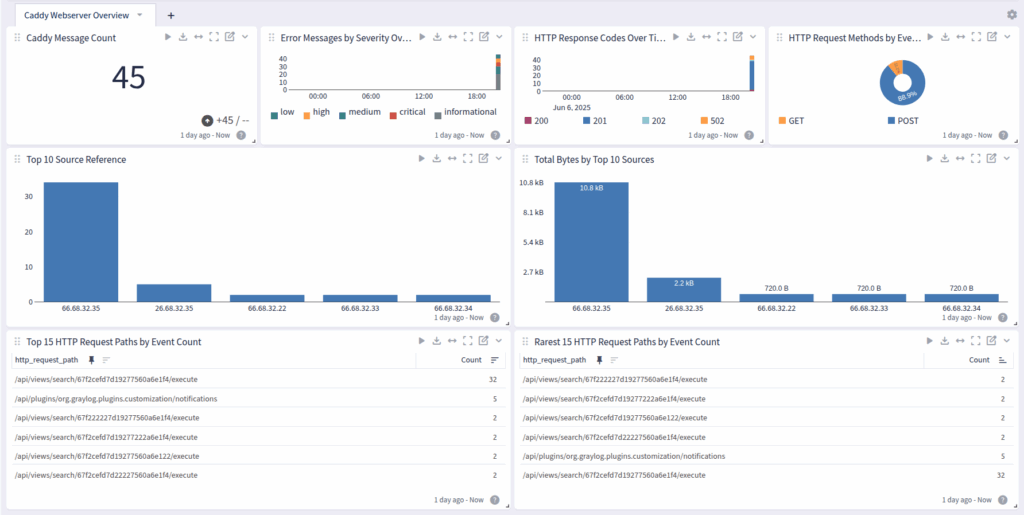
Automated Discovery and Monitoring
You can’t secure what you can’t see. CISOs should deploy automated scanners to discover all machine identities, including forgotten or “shadow” credentials. Continuously monitoring these identities ensures that vulnerabilities are found early.
Lifecycle Management and Ownership
Every machine identity should have a human owner responsible for its lifecycle—from creation to retirement. Automating tasks like dynamic secret generation and automated credential expiration can help scale this process and reduce manual errors.
Integrating Machine Identities into IAM
Machine identities must be a core part of your overall Identity and Access Management (IAM) strategy. By doing so, you gain a unified view and consistent control over both human and non-human access to your most critical systems.
About Segura®
Segura® strive to ensure the sovereignty of companies over actions and privileged information. To this end, we work against data theft through traceability of administrator actions on networks, servers, databases and a multitude of devices. In addition, we pursue compliance with auditing requirements and the most demanding standards, including PCI DSS, Sarbanes-Oxley, ISO 27001 and HIPAA.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.