Building a cybersecurity strategy is challenging. It requires more than just technical knowledge and managerial skills but also demands financial resources.
Business budgeting tendencies show that cybersecurity investments receive only a small part of the allocated IT budget. Cybersecurity funds must be distributed wisely to ensure valuable outcomes, prove the chosen security direction effective and minimize resources’ waste.
The main challenge is how to achieve effective security spending. How much should businesses allocate to cybersecurity, and what factors like company size or maturity does it depend on?
According to Statista, information security investments in different categories continuously grow. Projections for 2024 indicate worldwide spending on information security will double compared to 2017.
The trend confirms the necessity of considerable cybersecurity funding. To understand it better, let’s dive into research-based data on how businesses of different sizes and cybersecurity maturity distribute their allocated budgets.
Research methodology
NordLayer surveyed 500 non-governmental organizations across Canada, the United Kingdom, and the United States. An external agency conducted the surveys between March 15 and 25, 2023.
Industries and subindustries represented in the research include business management and support services, e-commerce, education, finance and insurance, health care, information and communication, IT, professional and technical services, and consulting.
The survey explored the organizations’ cybersecurity maturity level (Beginner, Basic, and Advanced), their cybersecurity solutions, and the presence of an in-house specialist or responsible department. It also included questions about cyber incident costs and allocated budgeting for IT and security in the period of 2022-2023.
Companies were segmented by size:
-
Small companies: 1-10 employees.
-
Medium companies: 11-200 employees.
-
Large companies: 201+ employees.
Cybersecurity landscape and the importance of budgeting
The mantra “cybersecurity keeps evolving, so do cyber threats” remains relevant today, emphasizing the need for strengthening business protection measures. As the significance of different types of attacks shifts, mitigating one risk at a time is not a practical solution.
For instance, just last year, ransomware attacks held the top position on the threats list, alerting everyone to stay vigilant. This year, according to Statista, the threat outlook for global companies highlights business email compromise and/or account takeovers (33%) as the most prominent cyber risk surpassing ransomware (32%).
Choosing comprehensive cybersecurity tools and solutions helps to achieve the flexibility needed to adapt to dynamic technological and risk change. A sufficient budget is key, so let’s explore how much companies of all sizes invest in building their cybersecurity strategies.
Understanding the context of digital attacks
Data speaks volumes, so let’s begin by analyzing the culprit behind the need for cybersecurity investments. The survey asked companies about any cyber incidents they encountered in 2022.
The list of top 10 cyberattacks starts with phishing (39%) and malware (34%) attacks firmly holding the first two positions. Despite an intense background of cyber incidents, nearly one-fifth of the companies surveyed didn’t encounter any accidents related to digital threats.
 Interestingly, ransomware, one of the most menacing threats recently, appears in the last place (16%) on the list, demonstrating how unpredictable and dynamic the nature of the cybersecurity landscape is. Please note that the frequency of a cyber incident doesn’t necessarily indicate the scale of damage inflicted.
Interestingly, ransomware, one of the most menacing threats recently, appears in the last place (16%) on the list, demonstrating how unpredictable and dynamic the nature of the cybersecurity landscape is. Please note that the frequency of a cyber incident doesn’t necessarily indicate the scale of damage inflicted.
The scope and type of cyber incidents may depend on a company’s size or the cybersecurity maturity of an organization.
Correlation between cyber incidents and company size
Organizational size usually is misinterpreted in evaluating the likelihood of a cyberattack. Small companies tend to argue they lack valuable assets of interest to malicious actors, requiring less protection.
However, from the first glance at the research data, the trend confirms that medium and large companies are exposed to cyber incidents more often. While 42% of small companies claim they didn’t encounter any cyber incidents in 2022, it accounts for less than half of them.
 We observe that insider threats and social engineering attacks are much rarer for small businesses, while data breaches or leaked passwords are more common issues. But phishing attacks (39%) on our list of cyber incidents are equally prevalent across all-sized companies.
We observe that insider threats and social engineering attacks are much rarer for small businesses, while data breaches or leaked passwords are more common issues. But phishing attacks (39%) on our list of cyber incidents are equally prevalent across all-sized companies.
Large enterprises tend to suffer from malware (43%), social engineering (30%), and insider threats (29%). Compared with the other two categories, medium-sized businesses were exposed most to data breaches (34%) and DDos/DoS attacks (27%).
However, identity theft (27%), compromised/leaked passwords (23%), and ransomware (19%) impact companies with either 11 employees or 201+ to a similar extent.
It’s important not to forget that size doesn’t make one immune. Only the form and approach of malicious actors can differ. Frequency is only one of the aspects to consider when analyzing the intensity of attacks but not the overall impact on business continuity.
Cyber preparedness as digital threat prevention
Company size is more of a predetermined factor rather than an easily controllable aspect of the business. Conversely, cyber preparedness is a decision-based measure of whether an organization invests and focuses on cybersecurity awareness.
Interestingly, higher cyber frequency of attacks is recorded for companies with advanced cybersecurity preparedness. Why is that? A few possible reasons explain this trend.
 Cybersecurity maturity is tightly connected with the complexities of creating, providing, and maintaining services and/or products within a company. It also relates to business nature, the processing of sensitive data, and active online presence.
Cybersecurity maturity is tightly connected with the complexities of creating, providing, and maintaining services and/or products within a company. It also relates to business nature, the processing of sensitive data, and active online presence.
Companies with a cybersecurity awareness mindset are more likely to assess the risks they face. To mitigate identified risks, security managers implement solutions to prevent, detect, or proactively hunt threats. Monitoring provides explicit data on cyber events or existing breaches, implying that organizations at the basic and beginner level of cyber maturity are less aware of what’s happening under the hood.
Digital advancements increase the attack surface of a company. Factors such as zero-day vulnerabilities, lack of sufficient resources, and incompatible effectiveness of cybersecurity strategy can lead to a higher frequency of cyber attacks, particularly when outsourced services and vendors introduce third-party dependency.
Adversary motivation is common to most malicious actors. These attacks are often based on financial gain or political ideology, but some attackers simply seek the thrill of a challenge. Less cyber-advanced and protected companies are an easy catch, making them suitable for training grounds for attackers compared to more well-protected and globally known companies.

Taking a closer look at the comparison between organization size, cybersecurity maturity level, and the frequency of cyber incidents reveals no distinct deviations.
The main insights imply a weak correlation between insider threats and cybersecurity preparedness levels, while the size of an organization doesn’t seem to impact the frequency of data breaches and identity theft.
Despite the size or cybersecurity maturity, businesses depend on the industry dynamics and the services and data they operate on. The human factor, whether as an internal threat or attacker motivation, is purely a wild card in the context of the cybersecurity landscape, irrespective of the company’s size or preparedness.
Real-life scenario: damage incurred to LinkedIn scam victim companies
Let’s take a real-life example to see how LinkedIn scams, common online threats, affect businesses. The critical part is assessing the inflicted damage and exploring what measures can help prevent such risks.
A LinkedIn scam or fake profile aims to gain illicit funds, either through direct transactions or by gathering personal information that can be used to build a pretext for receiving money. Naturally, the question is, how much do businesses lose in such attacks?
Comparing the damages suffered according to company size, tendencies show that all companies are at risk. Small businesses are the least affected (12%), and medium-sized and large enterprises have to pay the price more often — 22% and 24%, respectively.
Financial damages vary from losses of up to 5,000 in local currency for 33% of companies to 10,000 in local currency for 16% of surveyed companies. These numbers should be considered high as a fifth of respondents could not disclose information regarding their financial losses.
Regarding cybersecurity maturity level, losses increase accordingly — 15% of beginner-level enterprises suffer from financial damage, while 19% of basic-level and 24% of advanced-level companies have declared experiencing expenses.
Does it mean that the more prominent and cybersecurity-developed company, the more risks it is exposed to? Not necessarily, as cyber-ready companies tend to allocate a portion of their budget to IT, particularly when improving their cybersecurity infrastructure.
Research findings on cybersecurity budgeting
Budgeting is an abstract and not clearly defined practice that could be followed by pre-defined recommendations to guarantee success. But it is an important part of business planning, although seen differently by organizations.
Research on cybersecurity budget allocations revealed insights into how enterprises of various sizes approach the same challenges. The following findings are based on overall data, considering company size, cybersecurity maturity, and country unless indicated otherwise.
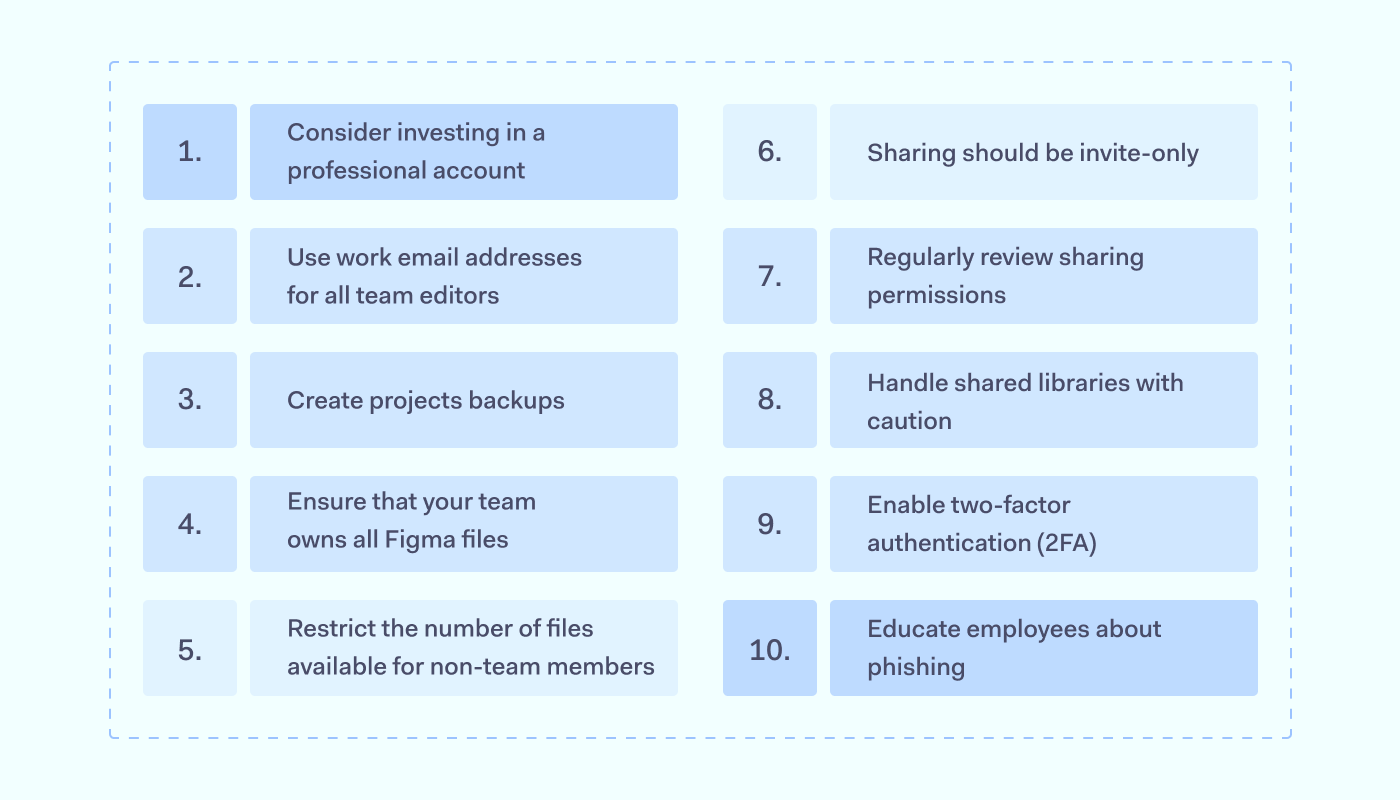
Budget allocation to IT needs and cybersecurity
IT and cybersecurity budgeting are two different segments of financing. The IT covers overall technology investments, including hardware, software, personnel, and cybersecurity. As cybersecurity is just a fraction of the grand scheme, it explains why budgets can be tight and sometimes even non-existent.
In 2022, over 90% of companies distributed some of their budgets to IT needs. Most companies allocated up to 50% of their financial resources, while only 1% of respondents put all their money into IT spending.
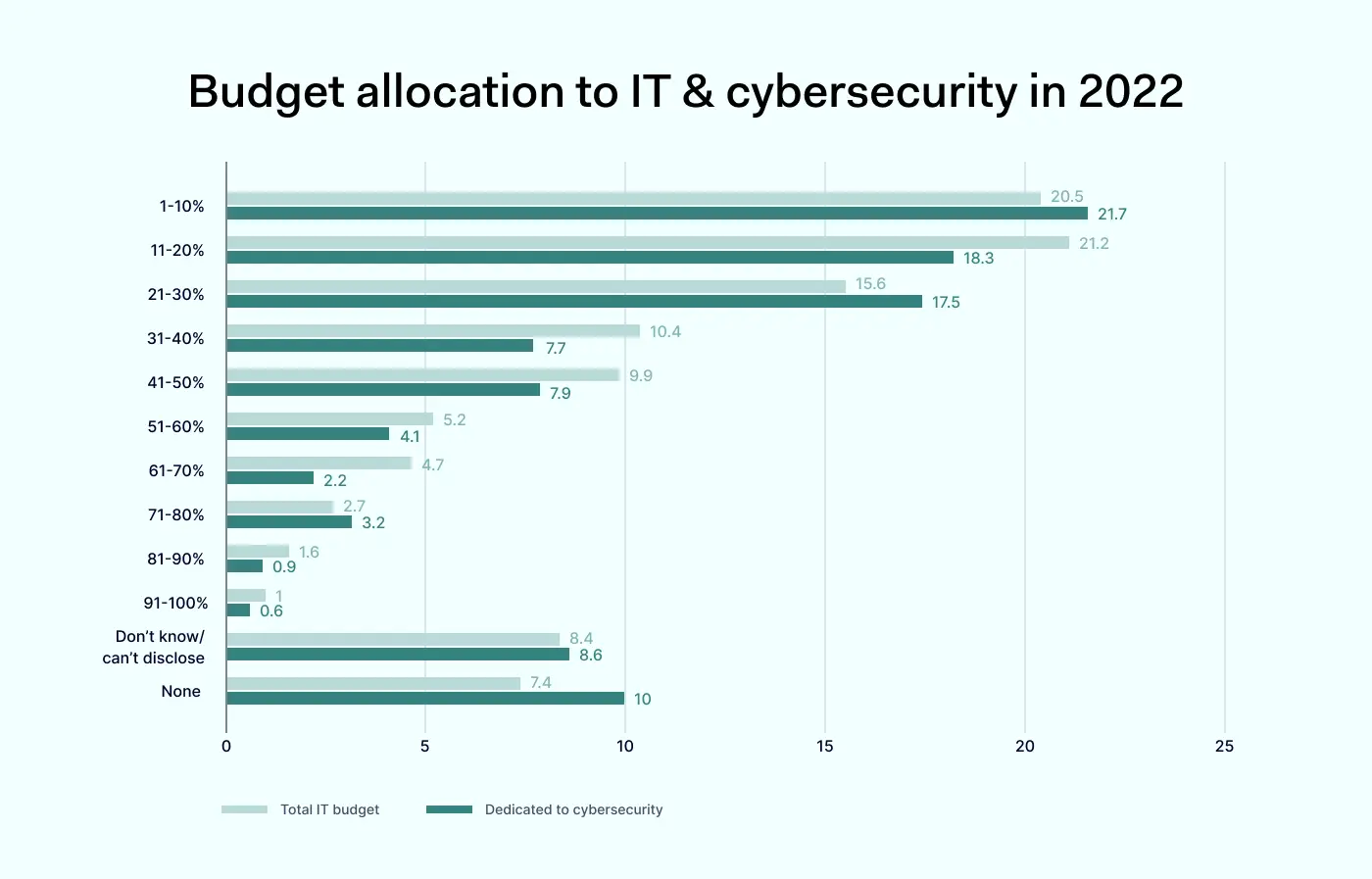
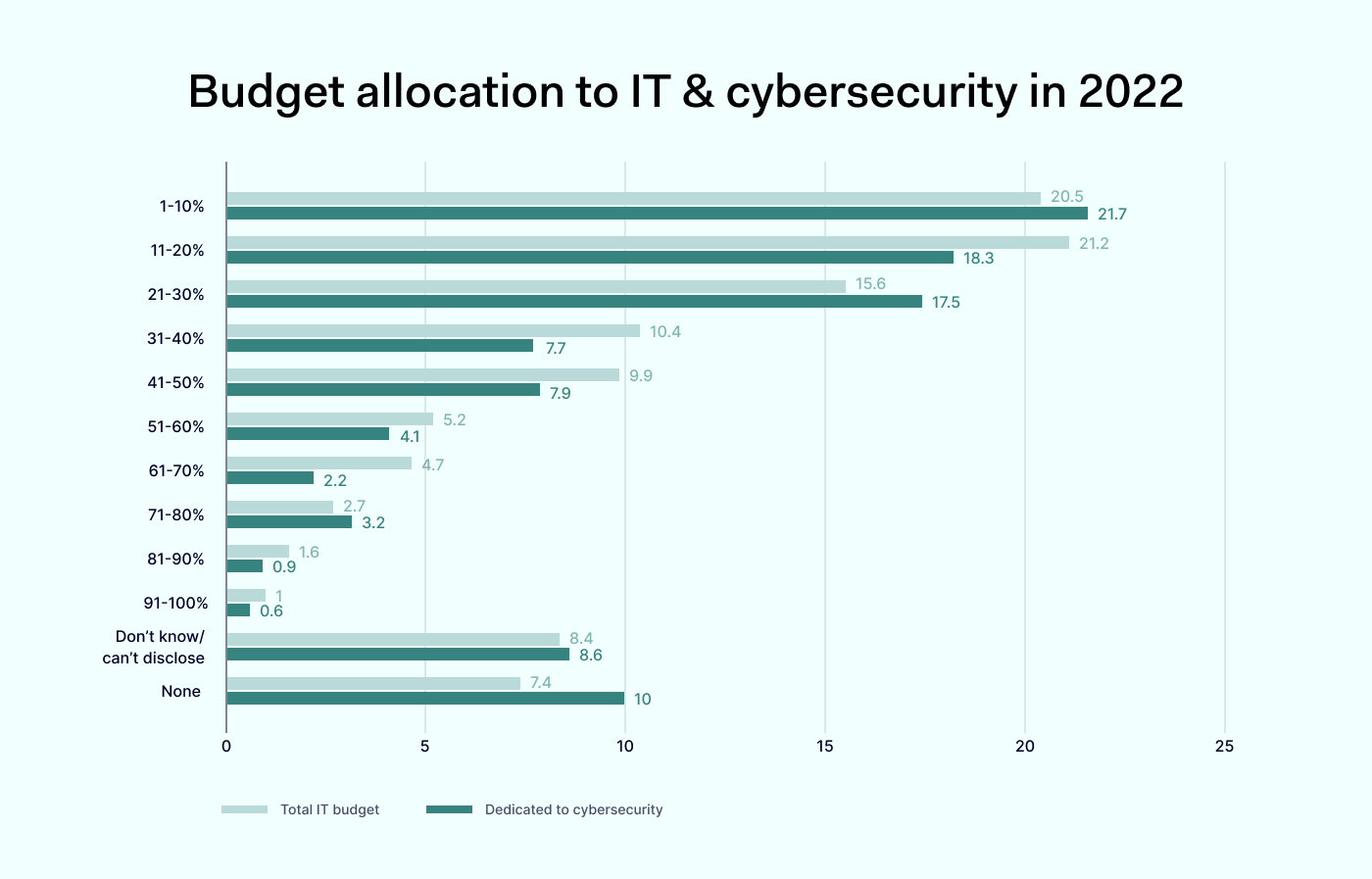
Finances allocated directly to cybersecurity spending (besides hardware and software investments) accounted for 84% of received funds in 2022. However, 10% of companies either didn’t find it relevant or had to shift their investing priorities away from cybersecurity. Nearly one-fifth of organizations allocated up to 30% of their funds to digital security.
Half of the small companies mainly invest up to 20% of their budget in upgrading their IT infrastructure. The same tendency appears for beginner cybersecurity maturity-level companies. 14% of small companies and 18% of beginner cybersecurity maturity level organizations chose not to invest in IT needs, while 26% and 31% of these companies did not invest in cybersecurity at all.
On the other hand, large enterprises and advanced cybersecurity maturity level companies tend to allocate more funds to IT, similar to medium-sized companies and basic cyber preparedness level organizations. Large and medium enterprises tended to allocate at least a portion of their budgets to cybersecurity strategy upgrades during the year.
In 2023, the trend shows that fewer companies (88%) distributed company funds to IT needs. Some organizations redistributed their funds to other departments, excluding IT or cybersecurity.
 Small and beginner-level cybersecurity maturity companies maintain the trend of investing as little as possible in IT and cybersecurity. In 2023, 16% of small-sized businesses and 19% of Beginner-level companies didn’t allocate funds to IT, which is a negative trend compared to 2022. Yet, 23% of small businesses and 28% of beginner-level companies skipped funding cybersecurity, a decrease compared to last year.
Small and beginner-level cybersecurity maturity companies maintain the trend of investing as little as possible in IT and cybersecurity. In 2023, 16% of small-sized businesses and 19% of Beginner-level companies didn’t allocate funds to IT, which is a negative trend compared to 2022. Yet, 23% of small businesses and 28% of beginner-level companies skipped funding cybersecurity, a decrease compared to last year.
This leads to the conclusion that although small and unadvanced companies allocate fewer funds to IT, they prioritize cybersecurity to a greater extent.
Medium-sized companies, on average, spend almost 30% of their available budget on IT in 2022. However, this allocation changed to 23% in 2023. Basic cybersecurity maturity level companies maintained a balance of 21-27% of IT funding in the last two years, with a growing tendency. Similar trends can be observed in cybersecurity investments for the same category of organizations.
Large and advanced cybersecurity maturity companies demonstrate stability, consistently allocating an average of 24% of funds designated to IT or cybersecurity needs in 2022-2023.
Investment trends for cyber threats management
Risk assessments and mitigation dictate the cybersecurity strategy of an organization. The strategy is built on security policies, tools, and solutions to implement measures that address the established business protection needs.
The cybersecurity strategy is a process that needs to be monitored, adjusted, and improved for better results. As mentioned earlier, the necessity for flexibility comes from ever-evolving digital environments.
We asked companies which solutions and services they use and what is their future investment focus in cybersecurity.
 The list of implemented tools and solutions reveals that companies combine different measures to achieve security. Almost 4 out of 5 companies utilize antivirus software (79%). Secure passwords (65%) and file encryption (64%) are the second-highest priority when creating security policies within organizations.
The list of implemented tools and solutions reveals that companies combine different measures to achieve security. Almost 4 out of 5 companies utilize antivirus software (79%). Secure passwords (65%) and file encryption (64%) are the second-highest priority when creating security policies within organizations.
Virtual Private Networks (VPNs) maintain their popularity in securing organization network connections, with over half (59%) of companies using them. Cyber insurance (45%) is a relatively new solution making its way to business cybersecurity, although its focus is on covering the consequences of an incident rather than preventing it.
Spending on cybersecurity solutions, services, and applications will continue to be a priority (59%) in the 2023 budgets. Raising awareness within organizations is as important as companies providing cybersecurity training and increasing dedicated staff for cybersecurity questions.

Compliance plays an important role in the approach to organizational cybersecurity. External audits and preparation for standard information security certifications are equally in focus (37%). However, 17% of respondent companies weren’t able to disclose their plans for cybersecurity budgeting allocation, and 11% said they had no plans for investing in cybersecurity.
It’s concerning to note that 1 out of 10 companies excluded cybersecurity from their budgeting priorities. 34% of those organizations are at the beginner-level of cybersecurity maturity, and 28% of small-sized businesses. Regarding the country, 8% of companies in the United States, 7% of Canada, and 5% of the United Kingdom companies cut their cybersecurity investments for the ongoing year.
Yearly comparison of cybersecurity investments
Plans for 2023 show a slight change but a clear strategy for businesses with advanced cybersecurity maturity. Purchasing security solutions, services, and/or applications is the top priority, accounting for 70% of planned costs. In addition, there is a strong focus on employee education (70%) and increasing staff for cybersecurity questions (63%).
 Attention to organizational preparation for information security certifications grew from 46% in 2022 to 51% in 2023. The data implies that businesses are strengthening their cybersecurity strategies to be more aware and self-sufficient in protecting company assets.
Attention to organizational preparation for information security certifications grew from 46% in 2022 to 51% in 2023. The data implies that businesses are strengthening their cybersecurity strategies to be more aware and self-sufficient in protecting company assets.
Beginner-level cybersecurity maturity companies fluctuate between 20–30% in the same categories. It indicates awareness present with yet too little security spending allocated.
These companies are smaller, thus easier to manage their scale and exposure to digital threats. For sustainable growth and security, the mindset shift is expected to be cyber-ready for driving large-scale organization protection.
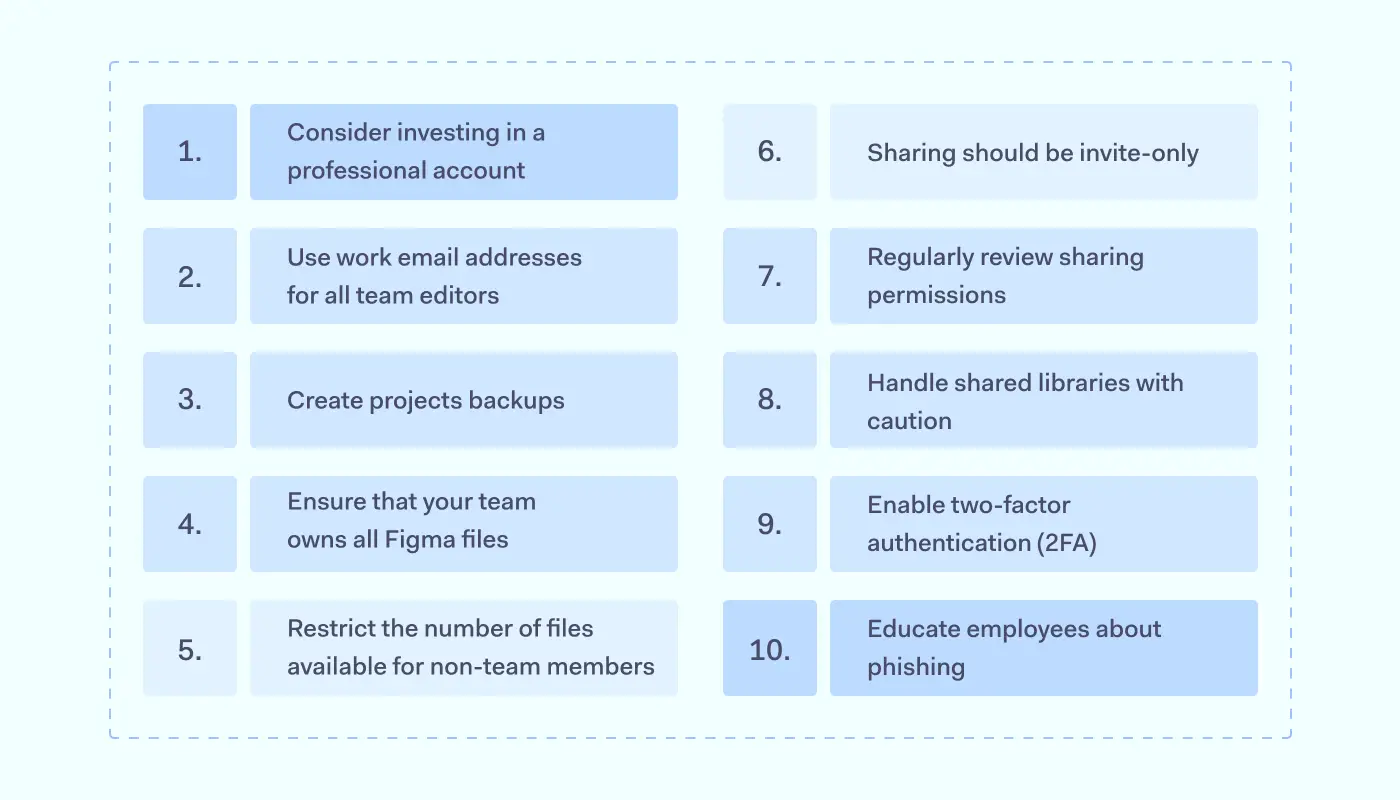
Best practices for developing cybersecurity budgets
Research revealed that cybersecurity spending depends on different factors. It plays a small yet important part in the overall business lifecycle. Investing in cybersecurity is highly recommended to ensure organizational growth and business continuity.
To allocate cybersecurity budgets effectively, evaluate all the components influencing costs, decision-making, and further strategy development. This includes staying vigilant and proactive, planning responsibly, reusing resources (talent, tools, processes) sustainably, and aiming for growth.
Key takeaways: how to identify, estimate, and prioritize security investments
Survey data shows that some companies invest in cybersecurity generously, while others, especially small businesses, tend to refrain from security funding. Naturally, the reason behind it can be related to limited resources, underdeveloped infrastructure and processes, and l time constraints.
Yet poorly protected businesses suffer harder from a cyber incident. Only luck, not size or brand awareness, influences when and how threat actors will target an organization.

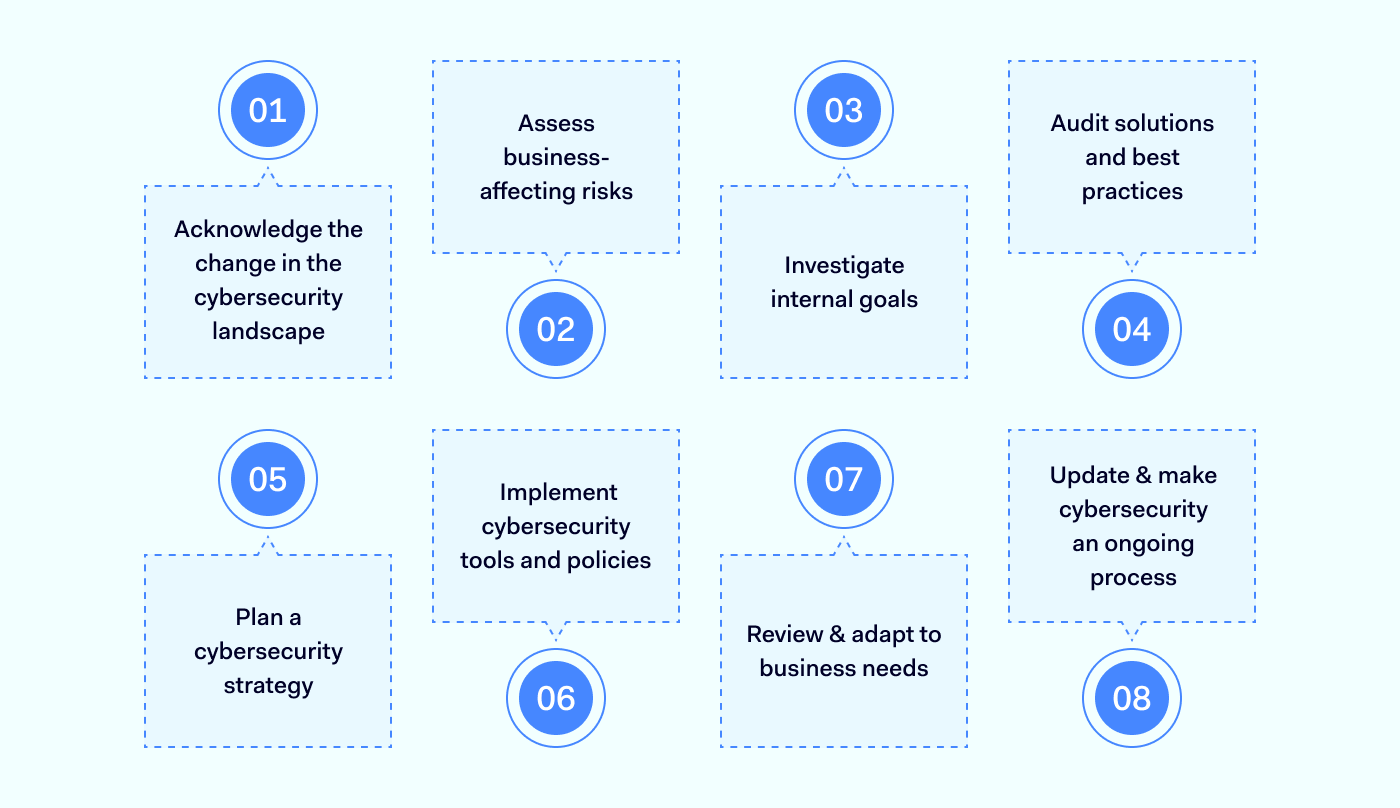
1. Acknowledge the change in the cybersecurity landscape
The first step for all decision-makers in the company, from a Chief Information Security Officer (CISO) to Managing Director, is to be aware of cybersecurity challenges and the vulnerability of their business to cyber threats.
Remember about technology upgrades from hardware to cloud-based environments for more resilience and flexibility. Malicious actors look for security gaps to exploit zero-day vulnerabilities.
2. Assess business-affecting risks
All organizations face the risk of cyber-attacks. Some industries have more red flags than others due to the nature of the data they process. The exposure to cyber threats can vary depending on the type of service or product the organization provides or the company’s maturity.
Understanding what security risks, threats, and scenarios your business is most exposed to is crucial to assess security measures correctly.
3. Investigate internal goals
First, investigate how the company’s budgets are allocated to different needs. What are strategic goals and business development objectives to find the place and role of cybersecurity in the organization?
Examine how the company meets compliance and aligns with stakeholders’ requirements. Are there any plans to seek certification from regulatory compliance providers, such as HIPAA for healthcare providers? Certification is a process that requires dedicated resources and, at the same time, provides guidelines for building a more robust cybersecurity strategy.
4. Audit solutions and best practices
Review your security strategy. To some extent, policies, procedures, and tools should already exist unless it’s the very beginning of a company. See what needs improvement and identify what gaps must be addressed as soon as possible.
Are there any processes that could be consolidated or solutions that aren’t used to the fullest? Companies tend to invest in applications – review what apps are utilized and if they satisfy business and user needs.
5. Plan a cybersecurity strategy
Cybersecurity strategy starts from a mindset within the company. The main elements that require continuous investment planning combine:
-
Tools & solutions.
-
Employee security training and development.
-
Dedicated staff, consultants, and outsourced services.
-
Developing backup plans for different threat scenarios to ensure a stable business lifeline.
6. Implement cybersecurity tools and policies
After evaluating the business needs for security, select solutions and tools that best suit your case. It’s beneficial to have demo calls with vendors and have a trial period to test tool adoption within the organization.
Once chosen, deploy tools, upgrade policies, and onboard the team to the new cybersecurity strategy.
7. Review & adapt to business needs
Implementing a solution and introducing new processes doesn’t end your cybersecurity strategy journey. Test, monitor, and confirm its effectiveness. Ongoing monitoring requires a dedicated team to ensure a smooth transition to a new way of working.
Whether your organization chooses to have an in-house or outsourced dedicated cybersecurity staff, it is important to allocate the necessary investments. It is recommended to choose a solution that is sustainable and easy to manage.
8. Update & make cybersecurity an ongoing process
Work on new and follow-up business initiatives in accordance with your cybersecurity strategy. Investigate what areas need changing, upgrades, and improvements for another implementation cycle.
Coherent tracking and planning help make next year’s cybersecurity budget easier. It is essential to invest in security training, tools, and dedicated employees in the company and view security as continuous learning and growth.
Following recommendations for cybersecurity budgeting
Finances and the effective allocation of limited resources is a sensitive and complex topic for any organization manager responsible for business planning. This research sheds light on the industry trends regarding how companies approach cybersecurity funding, which is ultimately connected to digital threat prevention.
Further investigation and insights are beneficial for informed planning, so explore other materials from NordLayer for a better understanding and planning of the cybersecurity budget:
Cost-benefit analysis of cybersecurity spending
A comprehensive analysis of cybersecurity costs and factors affecting them, benefits of cybersecurity spending, and how to apply it to your organization. In the article, you’ll find more comprehensive information on specific solutions and tools, security spending projections on dedicated cybersecurity staff, and other nuances influencing the cybersecurity strategy.
The study helps better understand the subject and find convincing arguments for discussions with other decision-makers.
Decision Maker’s Kit
This content support platform is dedicated to assisting decision-makers in choosing, explaining, and onboarding their selected cybersecurity solution within their organization. From strategical to explanatory materials, prepared templates, and documentation, the platform provides a better perspective on what’s required and expected when building a cybersecurity strategy for a business.
Projections on security budgeting for 2023
An overview of how much companies plan to allocate to cybersecurity in 2023, considering different factors. The article covers building a budgeting strategy, assessing the expense gap, and exploring investment alternatives such as the cost of a data breach.

 R: For me, it’s balancing the needs of my team with the demands of the business. This can include prioritizing tasks, ensuring everyone is on track to meet deadlines, and effectively communicating changes or updates to the team.
R: For me, it’s balancing the needs of my team with the demands of the business. This can include prioritizing tasks, ensuring everyone is on track to meet deadlines, and effectively communicating changes or updates to the team.