It is now an undeniable truth: protecting systems, applications, and networks is essential today. A crucial element of cybersecurity, Security Patch Management is the systematic process of identifying, acquiring, testing, and applying software updates—or patches—to fix vulnerabilities within a system.
Security patches are modifications to software systems that correct vulnerabilities potentially exploitable by hackers. They are released by software vendors to fix defects, improve functionality, or enhance security.
By implementing robust patch management practices, organizations can more effectively address vulnerabilities, minimize exposure to cyber threats, safeguard sensitive data, and ensure operational continuity.
Vulnerabilities and Security Patches
A vulnerability is a flaw or weakness in software, hardware, or an IT system that can be exploited to gain unauthorized access, disrupt operations, and cause significant damage.
Vulnerabilities often result from coding errors, misconfigurations, or the absence of adequate security controls. A security patch is a fix or update provided by software vendors to address and mitigate these weaknesses.
The speed at which a patch is released after a vulnerability is discovered has a direct impact on containing and neutralizing the risk of security breaches.
Keeping systems updated with the latest patches is essential to reducing the likelihood of attacks and ensuring strong protection against potential threats.
Security Patch Management Market Size and Trends
The global average cost of a data breach reached $4.88 million in 2024, marking a 10% increase compared to the previous year.
This cost increase is linked to the expenses associated with managing disruptions and customer assistance following a breach. More than half of organizations are passing these costs onto their customers.
However, the application of artificial intelligence (AI) and automation to security system management is opening new possibilities.
Thanks to advanced technologies, organizations can now reduce the time needed to detect and contain a breach, often cutting costs by an average of $2.2 million.
In this context, the development and adoption of security patches play a crucial role. The global Security Patch Management market was already valued at over $660 million in 2022, and this value has since increased further. Forecasts suggest it will continue growing until at least 2030, with an annual growth rate of 10.4%.
This growth is driven by:
- The increasing adoption of third-party applications,
- The growing demand for secure software,
- Greater awareness of cybersecurity among users.
The Importance of Security Patch Management: Key Benefits
As of August 2024, 52,000 new Common Vulnerabilities and Exposures (CVEs) were reported in cybersecurity, a significant increase from 2023’s 29,000 cases.
Hackers exploit vulnerabilities in outdated systems to gain unauthorized access, steal information, or disrupt operations.
Unpatched vulnerabilities are among the leading causes of data breaches. Prioritizing Security Patch Management as part of an overall cybersecurity strategy offers several key advantages:
- Reduced risk of cyberattacks: Regularly applying patches closes security gaps that attackers could exploit, significantly reducing risks from malware, ransomware, and other cyber threats.
- Regulatory compliance: Many industries have strict compliance requirements that mandate regular software updates. Failing to follow proper patching practices can lead to hefty fines and reputational damage.
- Improved system performance: Beyond security, patches often enhance software functionality and efficiency, ensuring systems operate at optimal levels.
- Protection of sensitive data: Preventing costly data breaches helps organizations safeguard sensitive information, maintain privacy, and earn customer trust.
The Role of Automation in Security Patch Management
Manually managing patches across an organization’s IT infrastructure can be costly and complex, especially for large enterprises. This is where automation plays a crucial role.
Automated patch management tools simplify the process by:
- Scanning for vulnerabilities and identifying outdated software,
- Efficiently deploying patches across multiple systems,
- Reducing human errors by ensuring uniform patch application across the entire IT infrastructure.
With automation, IT teams can focus on more strategic initiatives while maintaining strong security defenses.
To maximize these benefits, organizations should select tools that seamlessly integrate with existing systems and align IT governance with business objectives.
Prioritizing Critical Patches
Not all vulnerabilities pose the same level of risk. Some are more critical and require immediate attention.
Prioritizing patches based on severity is fundamental to effective security patch management.
Organizations can use the following strategies to determine which patches to apply first:
- Risk assessment: Analyzing the potential impact of a vulnerability on operations and data security.
- Vendor advisories: Software vendors often provide guidance on the urgency of patches. Organizations should always review these advisories and act accordingly.
- Threat intelligence: Leveraging threat intelligence tools to identify the most actively exploited vulnerabilities.
By focusing on critical patches, organizations can mitigate the most significant risks while ensuring operational continuity.
Balancing Security and Operational Continuity
One of the biggest challenges in security patch management is balancing security with the need for uninterrupted operations. Organizations can achieve this balance by adopting the following practices:
- Scheduled maintenance windows: Planning patch deployments during low-activity periods to minimize disruptions for users and customers.
- Testing patches before deployment: Testing patches in a controlled environment to ensure they don’t introduce new issues or conflicts.
- Gradual rollouts: Deploying patches incrementally across different systems or departments to reduce the risk of widespread disruptions.
- Clear communication with stakeholders: Informing employees and customers about scheduled maintenance to manage expectations and prevent confusion.
By carefully planning and executing patch management processes, organizations can maintain both security and operational efficiency.
Challenges in Security Patch Management
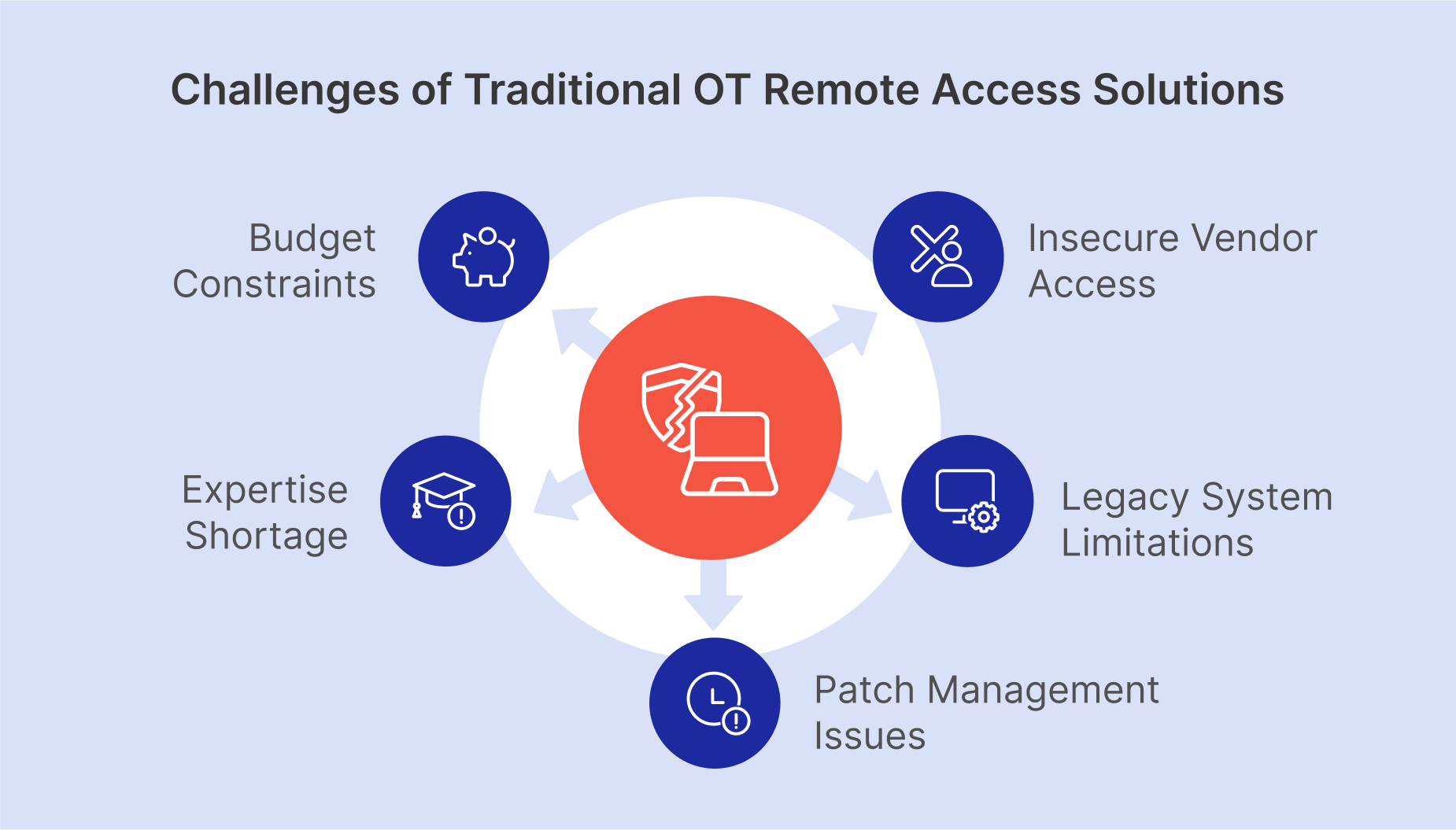
Despite advancements in technology providing more effective solutions, security patch management still faces several challenges. Some of the most common obstacles include:
- Complex IT environments: Modern organizations often manage diverse IT infrastructures, including on-premise systems, cloud platforms, and IoT devices.
- Limited resources: Budget and staffing constraints can hinder an organization’s ability to implement effective patch management, especially for small and medium-sized enterprises.
- Zero-day vulnerabilities: When vulnerabilities are unknown to developers or remain unpatched, organizations must rely on additional security measures, such as intrusion detection systems.
Lack of awareness: Employees may unintentionally delay or ignore updates due to a lack of understanding about their importance.
Best Practices for Security Patch Management
To overcome these challenges and build a robust patch management framework, organizations should adopt the following best practices:
- Establish a clear patch management policy that defines how patches are identified, tested, and deployed, while also assigning roles, responsibilities, and timelines.
- Maintain a comprehensive asset inventory that includes all hardware, software, and devices to ensure no system is overlooked during patching.
- Invest in reliable patch management tools that automate patching processes, provide real-time vulnerability insights, and generate detailed reports.
- Regularly monitor and review the patch management process through frequent audits to identify areas for improvement.
As cyber threats continue to evolve, the importance of Security Patch Management will only grow.
Emerging technologies, such as AI and machine learning, will play a significant role in enhancing patch management processes, predicting vulnerabilities before they are exploited.
The Strategic Importance of Security Patch Management
Security Patch Management is a fundamental component of any organization’s cybersecurity strategy.
By addressing vulnerabilities in a timely and systematic manner, organizations can reduce the risk of cyberattacks, protect sensitive data, and maintain regulatory compliance.
To prioritize critical patches and balance security with operational continuity, an effective Security Patch Management system must be proactive and incorporate advanced automation tools.
We have seen that challenges still exist. However, by adopting the best practices outlined above and staying informed on emerging trends, organizations can establish a strong security patch management framework.
In a world where the cost of a data breach can be catastrophic, investing in robust Security Patch Management processes is not just a good idea—it is an absolute necessity.
FAQs
1. What is Security Patch Management? Security Patch Management is the process of identifying, acquiring, testing, and applying software updates (patches) used to fix vulnerabilities and ensure system security.
2. Why is applying security patches important? Applying security patches reduces the risk of cyberattacks, protects sensitive data, ensures compliance with regulations, and improves the functionality and efficiency of systems.
3. What are the main challenges in Security Patch Management? Challenges include managing complex IT environments, limited resources, zero-day vulnerabilities, and a lack of awareness among employees about the importance of updates.
4. How does automation support Security Patch Management? Automation simplifies vulnerability scanning, patch application, and reduces human errors, allowing IT teams to focus on more strategic tasks.
About EasyVista
EasyVista is a leading IT software provider delivering comprehensive IT solutions, including service management, remote support, IT monitoring, and self-healing technologies. We empower companies to embrace a customer-focused, proactive, and predictive approach to IT service, support, and operations. EasyVista is dedicated to understanding and exceeding customer expectations, ensuring seamless and superior IT experiences. Today, EasyVista supports over 3,000 companies worldwide in accelerating digital transformation, enhancing employee productivity, reducing operating costs, and boosting satisfaction for both employees and customers across various industries, including financial services, healthcare, education, and manufacturing.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.