The term ‘sandworm’ might make many people think of the ‘Dune’ movie. Yet, it is also the name of a group actively involved in manipulating elections.
Over the years, Sandworm has meddled with elections to sway outcomes and interrupt political processes. This includes the 2016 US Presidential Election, the 2017 French Presidential Election, and various electoral processes in Ukraine.
Sandworm often begins its attacks with phishing. This technique isn’t just for tricking people into giving away their credit card information on fake websites. It’s a significant threat to businesses and, by extension, to national security, as companies can sometimes be the weaker link.
Learning about phishing is crucial. Let’s discuss it in a way that’s clear, easy to remember, and practical to use.
Key takeaways
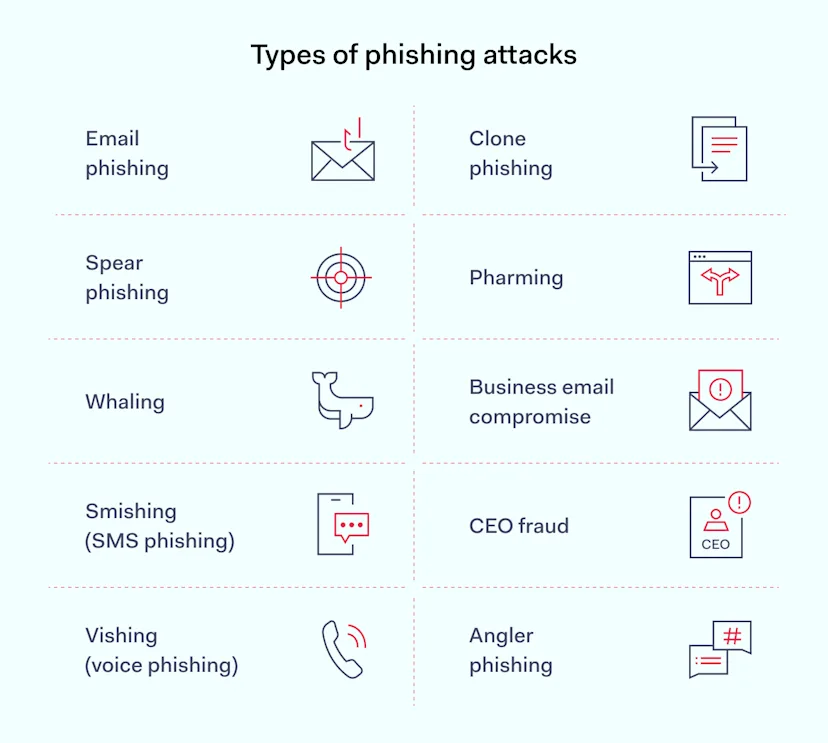
Phishing comes in various forms, such as email phishing, spear phishing, whaling, smishing, and vishing.
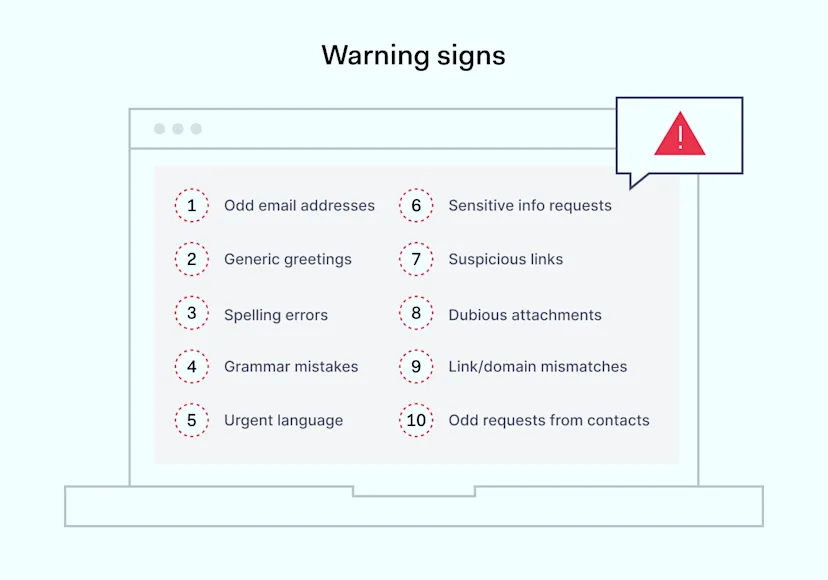
To identify a phishing attempt, look for signs such as suspicious email addresses, generic greetings, spelling and grammar errors, urgent language, requests for sensitive information, and dubious links or attachments.
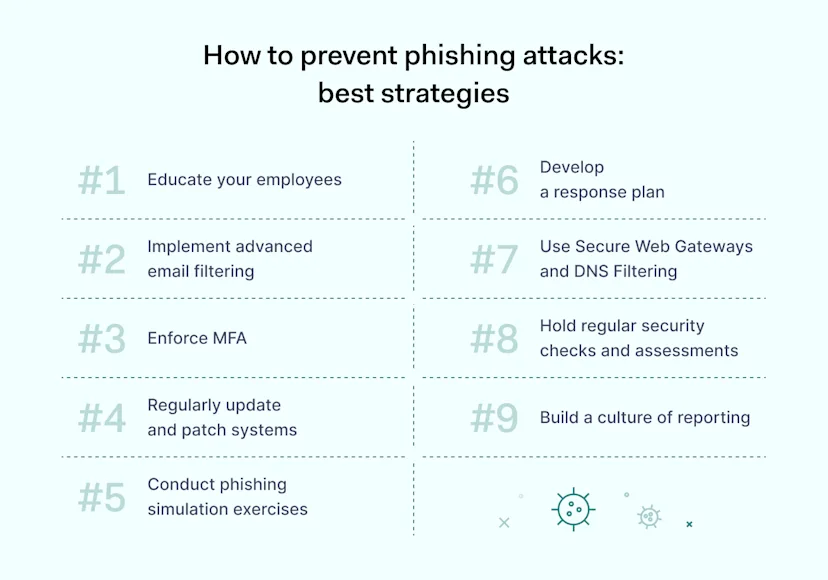
Educating your employees about anti-phishing techniques and promoting a culture of security awareness are crucial steps.
Enforce multi-factor authentication (MFA) to add a layer of security, making stolen credentials insufficient for accessing sensitive data.
Phishing simulation exercises can test your team’s detection skills and significantly improve your anti-phishing defenses.
Develop a response plan that outlines clear steps for reporting phishing attempts.
NordLayer helps mitigate phishing attacks by assisting in implementing the Zero Trust Network Access (ZTNA) framework and offering Threat Prevention features, which strengthen your organization’s defenses against phishing.
Types of phishing attacks
Phishing attacks come in various forms, each with its own tactics to trick victims into sharing sensitive information.
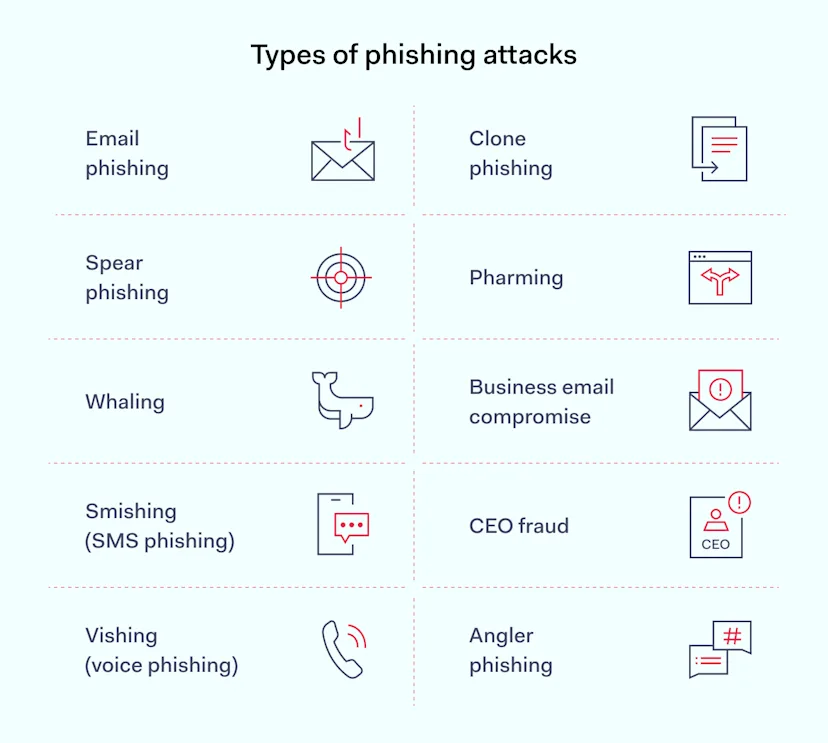
Email phishing is the most common, where attackers send fraudulent emails, mimicking legitimate organizations to steal personal data.
Spear phishing targets specific individuals or companies, using tailored information to seem more convincing.
Whaling focuses on high-profile targets like company executives, using sophisticated social engineering techniques.
Smishing and vishing involve sending text messages and making phone calls, respectively, to lure victims into revealing information or downloading malware.
Real-life examples of phishing
Phishing continues to be a significant problem. Recent studies show that phishing attacks have hit 94% of organizations, and 96% of them experienced negative impacts from the attacks. Adopting strong anti-phishing strategies is still very important.
In June 2023, a North Korean threat actor launched a sophisticated phishing attack on JumpCloud, a platform for identity management. They tricked a software engineer, which led to a security breach. This gave the attacker access to JumpCloud’s systems, which allowed them to interfere with operations. The team quickly noticed the unusual activities and immediately took steps to limit the damage, including changing credentials and rebuilding systems. However, JumpCloud has not shared details about whether any information was leaked from the affected devices.
In February 2023, Reddit showed how to handle a phishing attack effectively. The company was the target of a phishing attempt that fooled employees with fake alerts, leading them to a website designed to look like Reddit’s own intranet. This phishing attempt obtained some employees’ credentials, which gave unauthorized access to Reddit’s internal documents and source code. Quickly reporting the incident by an employee who got phished was key to Reddit’s swift action and investigation. This situation highlights the importance of quickly reporting phishing emails to mitigate phishing attacks. It also shows how spam filters and multi-factor authentication prevent phishing attacks and protect sensitive information.
In 2019, Magellan Health, a company that provides managed care services in the U.S., experienced a phishing attack. This incident exposed the personal and health-related information of about 270,000 people. It seems an employee, without realizing it, gave away their login details to the attackers. This mistake led to unauthorized access and the spread of spam emails. Magellan Health has decided to settle the claims for $1.43 million, although they don’t admit any fault and state there’s no proof that the information was actually misused.
How to identify phishing attacks
The arrival of generative AI has made spotting phishing attempts tougher. These advanced tools create very convincing messages, so staying alert is more important than ever. However, looking out for specific warning signs is still an essential way to guard against phishing attempts.
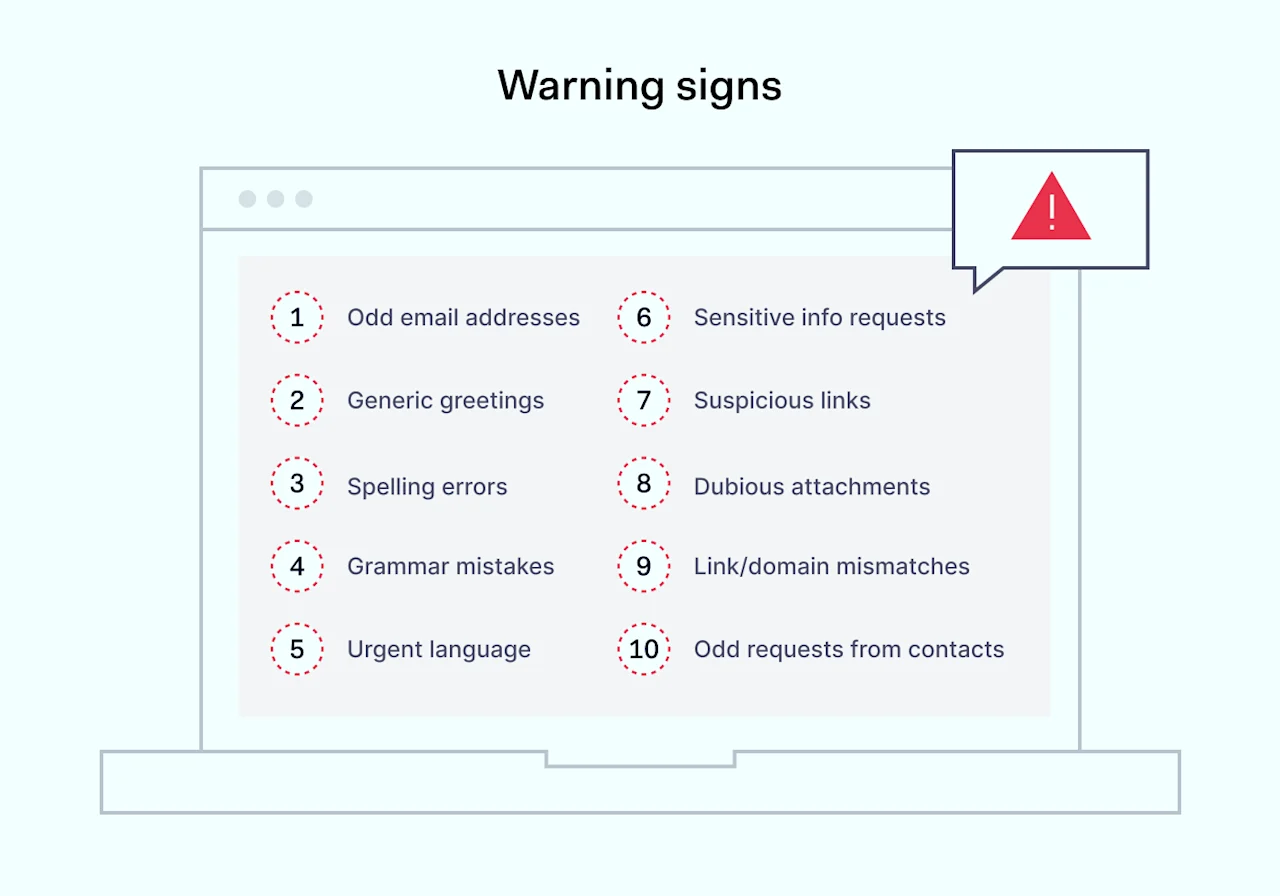
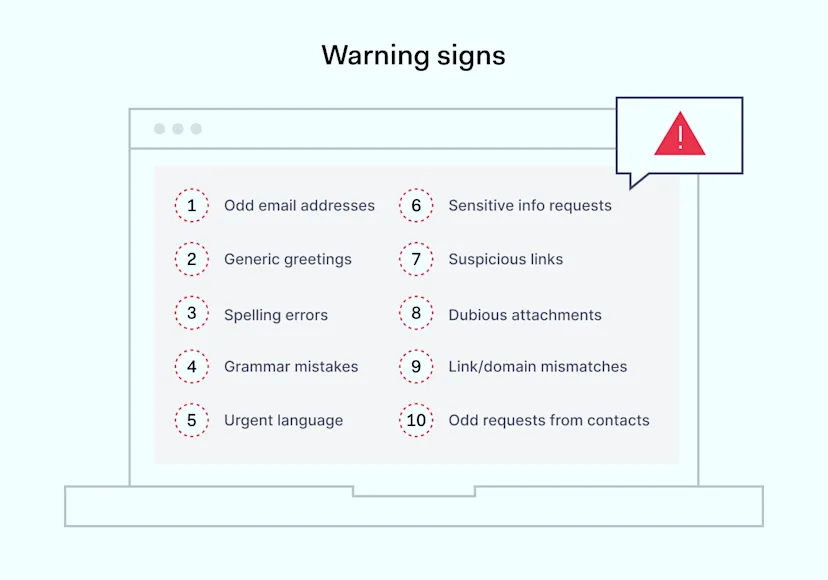
Email addresses that look slightly off are often the first sign of a phishing attack. Attackers mimic legitimate company addresses with small changes that are easy to miss. For example, getting an email from “support@amaz0n.com” instead of “support@amazon.com” is a clear warning sign.
When an email uses a generic greeting like ‘Dear Customer’ instead of your name, it might be a phishing attempt. Real companies know your name and use it to talk to you directly, making communication more personal.
Mistakes in spelling and grammar are telltale signs of phishing emails. Authentic companies make sure their messages are error-free. An email full of errors should make you pause and think. Also, spotting things like ‘[enter the name]’ or typical ChatGPT commands in an email should alert you. These signs can indicate the email may not be trustworthy.
Phishing emails often use urgent language to make you feel panicked. If an email pressures you to act fast to avoid negative consequences, like losing access to your account, be skeptical.
Requests for sensitive information through email should always be a red flag. Genuine organizations won’t ask for your passwords, Social Security numbers, or credit card details in this way.
Be cautious with links and attachments in emails. Checking where a link goes before clicking on it and being careful with unexpected attachments are smart ways to avoid phishing traps.
Differences in links and domain names can expose a phishing email. If these elements don’t match up with the actual company, it’s likely a scam.
If you get an email from someone you know that doesn’t seem right, like asking for odd things, it could mean their email is part of a phishing scam. This is a tactic to catch you off guard.
How to prevent phishing attacks in your organization
Phishing attacks are common yet serious threats to steal organizations’ sensitive information. To protect against these attacks, combining education, technology, and vigilance into a comprehensive strategy is essential.
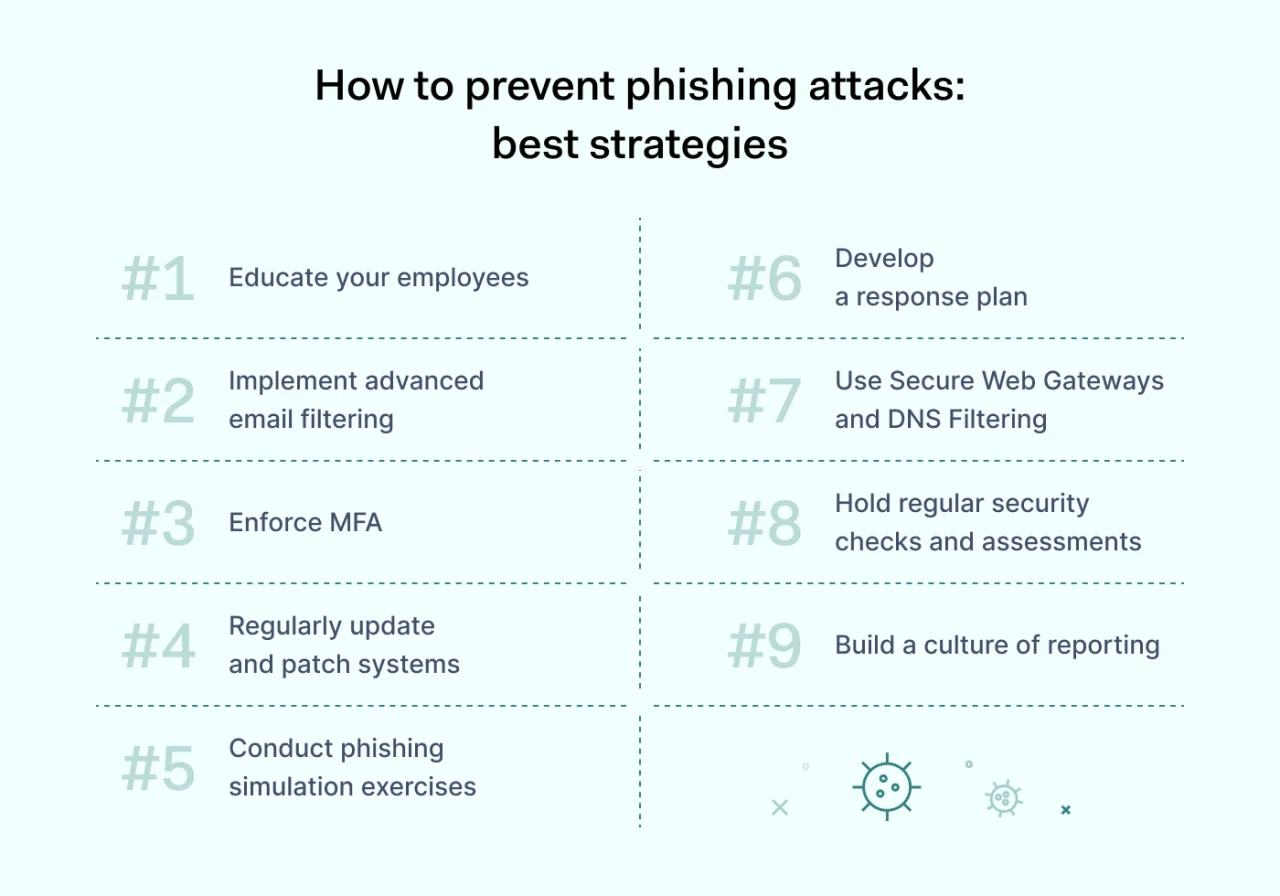
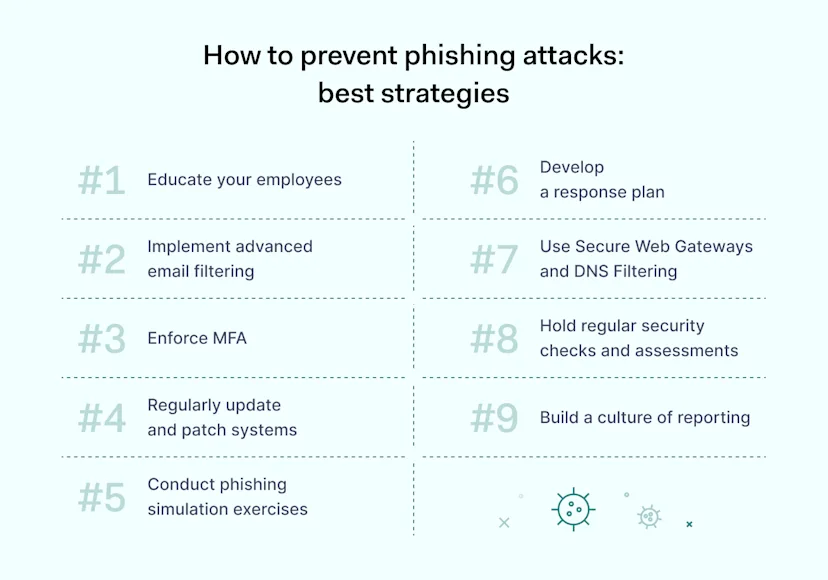
Educate your employees
Teaching your team about phishing techniques is crucial. Stress the importance of checking for email misspellings, the dangers of clicking on unknown links or attachments, and how to report anything suspicious. Building a security-aware culture helps everyone play a part in preventing phishing attacks.
For example, lately, Business Email Compromise (BEC) has become a major cybersecurity concern. This scam involves sending targeted phishing emails to steal money or data from companies. A typical example is CEO fraud, where scammers, pretending to be the company’s CEO, ask employees for urgent money transfers. These requests could be for settling invoices, closing deals, or even buying gift cards, often urging quick action or demanding secrecy.
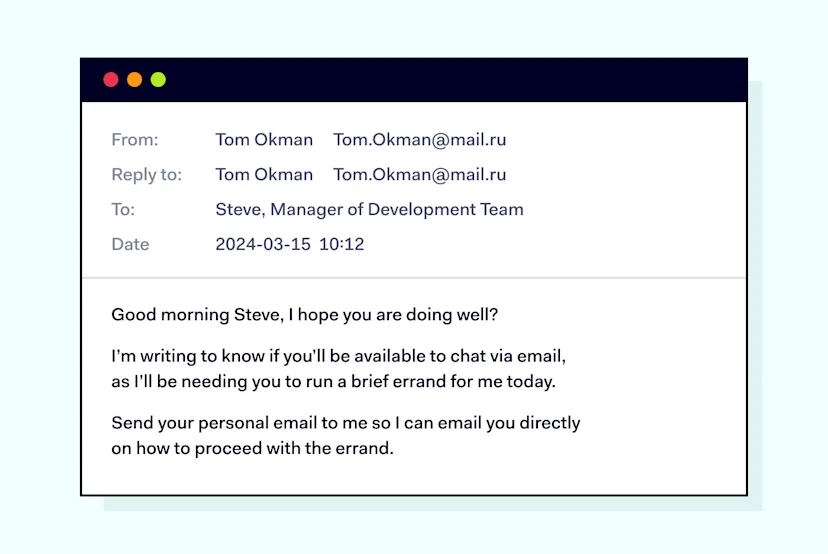
Some BEC attempts are easily recognized, like the one our colleague got:
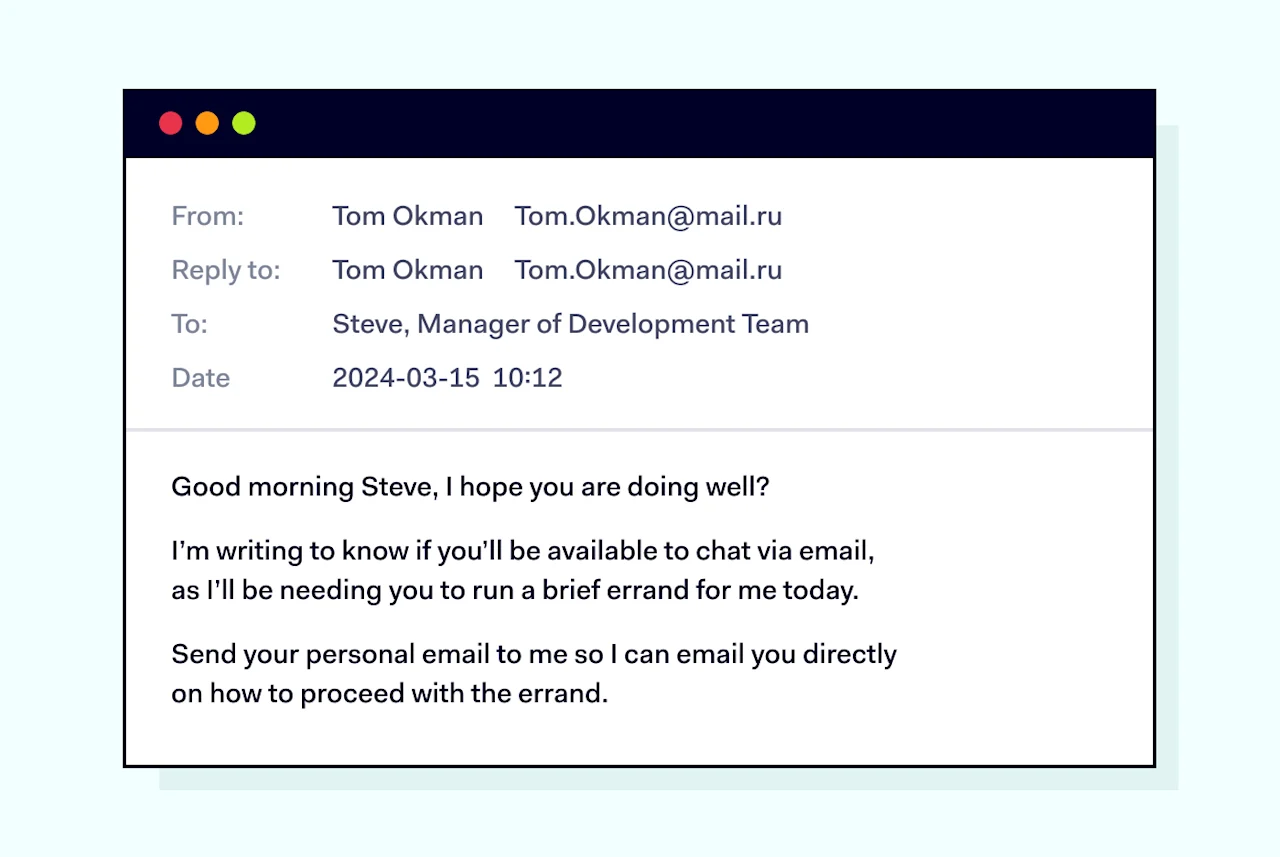
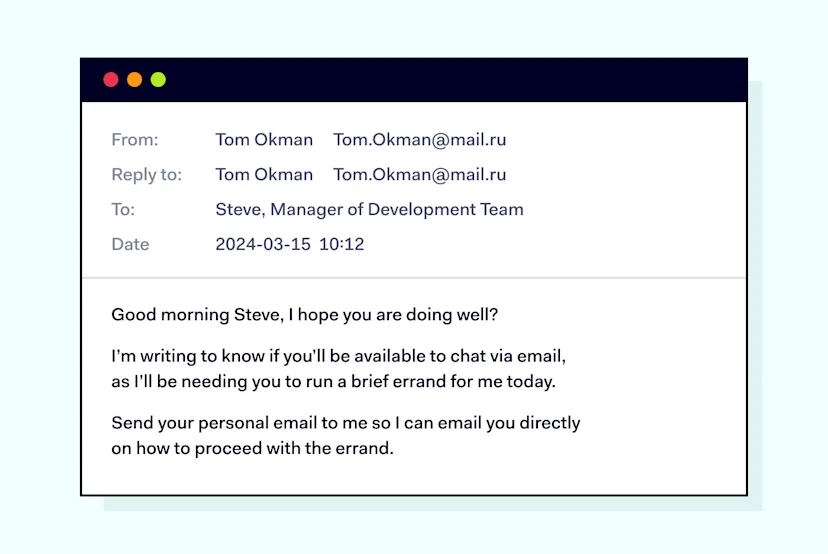
Other attacks can be quite sophisticated. For instance, in 2016, a scam involving a fake CEO of FACC led to a $47 million loss.
Now, the risk is even greater with generative AI, allowing scammers to create realistic deepfake videos or audio of executives. So, remind your employees to be cautious when fending off BEC threats. Encourage people to confirm any urgent requests for money or important information claimed to be from the CEO by directly calling the CEO or messaging them on a different platform.
Implement advanced email filtering
Email filters are crucial in stopping phishing emails before they get to your team. These systems look for clues that an email might be a phishing attempt, and they learn from new threats, greatly reducing the likelihood of a successful attack.
Google has shared that its AI-driven security in Gmail blocks over 99.9% of spam, phishing, and malware, keeping almost 15 billion unwanted emails away from users every day. Keeping these filters up-to-date and properly set up is essential in staying one step ahead of phishers.
Enforce MFA
Multi-factor authentication offers a solid layer of protection, even when other defenses might not work as well. MFA could require something like a code from your phone or your fingerprint. This way, it makes sure that just having stolen credentials isn’t enough to get into your data.
Once, Google aimed to cut down on phishing risks, so they required all their employees to use physical Security Keys, leading to no account takeovers being reported. The company found physical security keys so effective that it introduced its own in 2018. To help with the security of the US election, they also gave out thousands of these keys for free.
Regularly update and patch systems
Updating software is key to phishing prevention. These updates patch security holes that threat actors might use to sneak malware into innocent-looking requests.
They also add new anti-phishing features, like better detection of fake websites, making it harder for phishing attempts to succeed. Plus, keeping software current ensures businesses meet data protection standards and supports the latest defenses against phishing, such as improved email filters and browser warnings.
Conduct phishing simulation exercises
Phishing simulations test how well your team can spot a phishing attempt. For example, Uber tackles cybersecurity risks, including phishing simulations, with a trio of strategies.
Tabletop exercises are like role-playing games for security scenarios, helping leaders practice decision-making and boost their understanding of cybersecurity. Red team operations are more like realistic mock battles, where a team plays the role of attackers to test how well Uber can defend against real threats. Lastly, atomic simulations are bite-sized tests focusing on specific security measures and how quickly the team can respond. Together, these strategies keep the team better prepared for different sorts of cyber challenges.
Develop a response plan
Developing a response plan is essential in the fight against phishing attacks. Start by outlining clear steps that your team should follow when they detect a phishing attempt, including who to notify and how to report the incident. Make sure everyone understands the common phishing techniques and the importance of quick action to minimize damage. Regularly review and update your anti-phishing policies to adapt to new phishing scams. Practice your response plan through drills to ensure that when a real phishing attack occurs, your organization is prepared to act swiftly and effectively.
Use Secure Web Gateways and DNS Filtering
Using Secure Web Gateways (SWG) and DNS filtering is a powerful step in your anti-phishing strategy. These tools act as a first line of defense by blocking access to malicious websites known for phishing attacks before they can do harm. They scan and filter internet traffic to prevent phishing techniques and scams from reaching your network or your team’s devices. Setting up SWG and DNS filtering helps ensure only safe, approved web content gets through, significantly reducing the risk of phishing attempts.
Hold regular security checks and assessments
Regular security checks and assessments help identify vulnerabilities that could be exploited by phishing techniques. By consistently reviewing your security measures, you can stay one step ahead of attackers and adapt to new phishing scams. Incorporating anti-phishing drills and tests into these assessments can strengthen your team’s ability to recognize and respond to threats. Make it a priority to schedule these checks periodically.
Build a culture of reporting
It’s important to make employees feel comfortable reporting any suspected phishing. If people worry they’ll get in trouble or feel embarrassed, they might not report things that could warn you about a phishing threat. Showing that reporting can stop attacks before they happen helps everyone understand why it’s so crucial. Making it easy to report, like having a special email address or a simple button in email programs, encourages reporting. Saying thank you to those who report phishing helps build a culture where everyone wants to keep the organization safe.
How to mitigate phishing attacks with NordLayer
NordLayer offers a straightforward solution to mitigate phishing attacks effectively. It guides businesses in implementing the Zero Trust Network Access (ZTNA) framework smoothly, often without the need for external tech specialists.
ZTNA works on the principle of trusting no one by default, whether they are inside or outside your network. Access is given only after detailed verification, greatly lowering the risk of phishing attacks by making sure only verified users can get into your network resources.
Besides helping with the ZTNA framework, NordLayer has direct features aimed at phishing prevention. The Threat Prevention tool actively spots and stops potential threats, protecting your devices and important data from complex phishing methods and scams.
Using NordLayer’s complete security tools gives your organization strong anti-phishing protection. To find out how NordLayer can help prevent phishing attacks in your organization, feel free to contact sales.