In the ever-expanding landscape of cybersecurity, organizations are continually challenged to adapt and innovate in the face of evolving threats. As digital transformation accelerates and remote work becomes the norm, the traditional security perimeter is becoming increasingly porous, leaving sensitive data and critical systems vulnerable to advanced attacks.Secure Service Edge (SSE) emerges as a proactive approach to safeguard digital assets while enabling seamless connectivity and productivity.

A recent study posted on Gartner’s Peer Community showed the top three challenges for the future of cybersecurity attack sophistication (56%), greater resources for cyber-attacks (44%), and hybrid work models (43%). In addition, the same group of more than 300 IT/engineering/infosec leaders reported the three emerging cloud security tools they’re most excited about are cloud-native application protection platforms (CNAPP) (39%), SSE (38%), and SaaS management platforms (SMP) (37%).
Another Gartner study calls out the business priorities for Zero Trust, with protecting customer data (63%) topping the list.

Evolution of Secure Service Edge
The traditional network perimeter, once a stalwart defense against cyber threats, has become obsolete in the face of modern challenges such as cloud computing, mobility, and the proliferation of internet-connected devices.
As organizations embrace digital transformation and adopt cloud-based services, the concept of a secure perimeter shifts from a static boundary to a dynamic, distributed model that extends to wherever users and data reside.
This shift in perspective gives rise to the Secure Access Service Edge (SASE) framework, which converges networking and security capabilities into a unified architecture.
SASE combines the scalability and flexibility of cloud-native architectures with the security and performance required to protect modern digital environments.
SASE, in its simplest form, is a combination of software-defined WAN (SD-WAN) and SSE, as shown in the figure below.
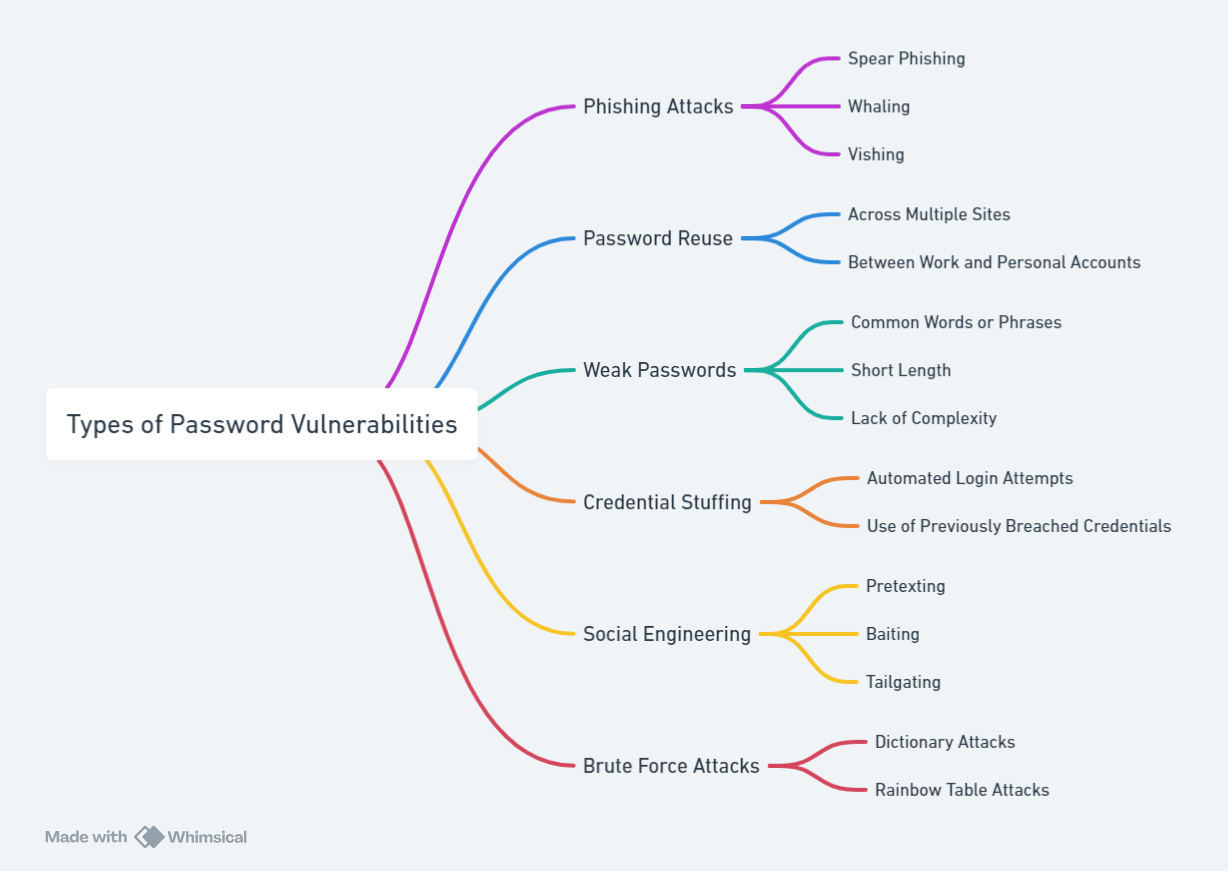
Central to the SASE model is the concept of SSE, which is based on Zero Trust network access (ZTNA), secure web gateways (SWG), cloud access security brokers (CASB), firewall as a service (FWaaS), and remote browser isolation (RBI).
At the heart of the SSE paradigm lies RBI, a ground-breaking technology that promises to revolutionize how organizations defend against web-based threats.
But to appreciate the significance of RBI within the broader context of SSE, it’s essential to understand the journey that led to its emergence and the transformative impact it holds for cybersecurity professionals and businesses alike.
Built ground up on Zero Trust architecture, which means, it assumes that no entity, whether inside or outside the network, should be trusted by default, emphasizing continuous verification and least privilege access.
SASE = SSE + SD-WAN

Remote browser isolation: Foundation of Secure Service Edge
At the core of the SSE architecture is remote browser isolation (RBI), a revolutionary technology that decouples web browsing activity from endpoint devices, effectively isolating potential threats in a secure, remote, and sandboxed environment.
Unlike traditional web security approaches that rely on detecting and blocking malicious content at the endpoint or network perimeter, RBI ensures that web content is executed and rendered in a disposable container outside the corporate network, preventing malware from ever reaching the endpoint.
Key principles of RBI include:
Isolation: RBI creates a secure air-gap barrier between users’ web browsers and potentially malicious content, preventing direct access to corporate resources and sensitive data.
Zero Trust: By treating all web content as untrusted and isolating it in a remote environment, RBI aligns with the Zero Trust model, minimizing the attack surface and mitigating the risk of web-based threats.
Scalability: RBI offers virtually unlimited scalability, allowing organizations to support growing user populations and fluctuating demand without sacrificing performance or security.
Seamless user experience: Despite the robust security measures in place, RBI ensures a seamless and responsive browsing experience for end users, eliminating the need for cumbersome security controls that impede productivity.
The impact of RBI on cybersecurity:
The adoption of RBI as a foundational component of the Secure Service Edge has profound implications for cybersecurity practitioners and organizations seeking to fortify their defenses against web-based threats. It shifts the focus from reactive threat detection to proactive threat prevention.
RBI empowers organizations to:
- Enhance security posture: RBI reduces the risk of web-based attacks such as phishing, ransomware, and drive-by downloads by isolating potentially malicious content away from endpoints and critical assets.
- Improve compliance: With RBI’s ability to enforce granular access controls and prevent unauthorized data exfiltration, organizations can achieve and maintain compliance with regulatory requirements such as GDPR, HIPAA etc.
- Enable secure remote work: As remote work becomes increasingly prevalent, RBI enables organizations to extend robust web security protections to distributed workforces, ensuring consistent protection regardless of users’ locations or devices.
- Optimize resource utilization: By offloading resource-intensive web browsing activities to remote isolation environments, organizations can optimize endpoint performance and reduce the strain on network infrastructure.
The future is brightly secured
As organizations navigate the complex cybersecurity landscape and embrace the principles of Secure Service Edge, remote browser isolation emerges as a cornerstone technology that empowers them to adapt and thrive in an ever-changing threat landscape. By embracing RBI as a proactive defense against web-based threats, organizations can strengthen their security posture, enhance user productivity, and maintain compliance in an increasingly interconnected and dynamic digital world. RBI serves as a one-stop solution for any organization that has an appetite for, and the attack surface, encompassing access, network, and end-point security.
We at Parallels, are constantly striving to collaborate and enable our partners and customers on their journey to a secure future. As a commitment to this vision, we are excited to introduce our own in-house offering, Parallels Browser Isolation (PBI)!
Parallels Browser Isolation: See it in action
Parallels Browser Isolation provides a secure way to access web applications, including Software as a Service (SaaS) and other cloud-based applications, right from your favorite web browser on your laptop or desktop.
Parallels Browser Isolation stands as a beacon of innovation and resilience, guiding organizations towards a future where security and productivity are not mutually exclusive, but rather complementary pillars of success.
This bolsters the Parallels pedigree as a leader in cross-platform solutions spanning, desktop-server-cloud capabilities, all seamlessly integrated. Our solutions provide a seamless plug-and-play experience, combining different Parallels suite of products into one holistic platform, enabling access to on-premises or cloud-based apps and desktops via any device, any browser, or any operating system.