
The amplitude of online scams is outraging on the internet. Malicious actors always seek original and convincing ways to catch their victims off-guard. LinkedIn creates a perfect environment for social engineering and other types of fraud, and that’s why scams have populated the platform.
Let’s start from the beginning. The LinkedIn platform is incredibly popular, with over 930 million members globally, making its scams an intriguing topic not only from a consumer perspective but from businesses.
Do only small companies or large enterprises fall victim to LinkedIn threats? Does it depend on a country or organization’s maturity? And what are the most common approaches that get employees’ trust?
To answer these questions and dig deeper into the source of businesses-linked LinkedIn scams, NordLayer researched the fraudulent activity tendencies.
LinkedIn scam — is a fraudulent scheme on the LinkedIn platform that aims to trick people into giving money or personal information, often through a fake job or business opportunities, requests for payment, or impersonation.
These scams usually target individuals. Yet, due to the peculiarity of LinkedIn, they are often connected to organizations the targeted people are employees of. A LinkedIn scam poses personal threats but also puts a company at risk, making it an interesting case from a B2B security point of view.
Research methodology
NordLayer surveyed 500 respondents in Canada, the United Kingdom, and the United States. An external agency conducted the surveys between the 15th–25th of March, 2023.
Respondents (adult population, 18+) of non-governmental organizations were asked what kind of scams they encountered on the LinkedIn social media platform and what aftermath effects it had on their business. Subindustries represented included business management and support services, e-commerce, education, finance and insurance, health care, information and communication, IT, professional and technical services, and consulting.
The survey covered questions about the organization’s cybersecurity maturity level (Beginner, Basic, and Advanced), their cybersecurity solutions, and whether they had an in-house specialist or responsible department.
Companies by size were segmented by:
-
Small companies: 1-10 employees
-
Medium companies: 11-200 employees
-
Large companies: 201+ employees
Typical LinkedIn scams
The professional nature of a LinkedIn platform opens unique opportunities to vary the approach to encounter platform users. With a focus on job and industry topics, LinkedIn is no less than a social networking platform for making connections, communicating, and finding think-alikes.
The primary function of LinkedIn – building a career – introduces one of the most common LinkedIn scams, fake job offers. With 117 job applications submitted per second on the platform, fraudsters have an ideal environment for creating a legitimate-looking job posting to collect personal information or money.
Another popular scam is LinkedIn phishing, where an actor impersonates a well-known company or professional using fake profiles to send unsolicited messages or emails that ask for sensitive information.
Also, receiving an invitation to connect is common on the platform. Fraud actors use this connection culture to start a conversation and share a link with malicious content expecting LinkedIn users will click on it.
The NordLayer research on LinkedIn scams affecting the business sector confirmed the dominating tendencies of fraud types among the respondents, as the leading ones match the general statistics:

It’s safe to assume that most fraud attempts impacting businesses are social engineering based on public or personal information. On the one hand, LinkedIn is an environment where everyone shows their or their organization’s best side.
Yet, politeness, eagerness to sell oneself, and prospect opportunities tend to create an unintentional smoke screen for LinkedIn members leading to the most bizarre scams that might even involve lotteries or romance fraud.
Research findings on LinkedIn scams
Many businesses acknowledge the significance of being present on LinkedIn. 77% of respondents confirmed that their organization has a profile on the platform. Yet, 82% of medium-large companies tend to register more often than 54% of small (up to 10 employees) businesses.

Frequency and scope of LinkedIn scams
According to the research, over half of the respondents encountered a scam attempt or fake account on LinkedIn.

The rest of the respondents (47%) indicated their organization employees are likely to be engaged in a scheme. The trend corresponds with companies with Advanced cybersecurity maturity (46%).
Advanced cyber-maturity and medium-large companies are the first to fall victim to phishing attempts (52%) and fake tech support (45%) scams. It implies that large and mature companies have higher cyber awareness levels and, at the same time, more often outsourced assets like technical help vendors or a vast yet difficult-to-unravel network of colleagues, which brings everyone to an eye of a storm.
It is also worth mentioning that companies of all sizes get a lot of fault-line messages inviting them to connect. The frequency of receiving such requests varies by around 40% of companies.
Offerings to purchase non-existent or fake products or services are more prominent for mid-sized businesses — 34% compared to an average of 26% of such encounters with small and large enterprises. Medium-sized companies also lead fake lotteries (30% compared to 24%) and dating/romance scams (28% compared to 18%).
Target geography of LinkedIn scams

However, the engagement rate of scams is lower in the States than in the other two countries. Only 38% were contacted by a fake LinkedIn profile or attempted to be scammed more than once, compared to 43% in Canada and 44% in the UK.
Looking closer at the tendencies of each surveyed country, the United Kingdom is attacked mainly by fake job offer scams (63%) and fake get-rich-quick offers (43%).
The United States leads in receiving a request to connect with a suspicious link — even 47% of respondents confirmed getting one, and 29% received an invitation to take part in a fake survey.
LinkedIn scams in Canada are focused on offering to buy a non-existing/fake product or service (36%) and getting involved in dating/romance fraud schemes (30%).
Despite the country, results were distributed almost equally for cases of phishing attempts (47%) and fake tech support (38%). It’s also important to note that if one scam is more popular than the other in different countries, it doesn’t mean that companies and their employees are safe from getting attacked or should expect only trending attacks.
The aftermath of LinkedIn scams
The scam attempt effects on organizations vary from harming reputation to imposing physical infrastructure damage. Regardless of the size of the business, they may experience the following:

Medium-sized enterprises have to deal with reputation damage the most (47%), stolen and/or damaged data, and customer contacts (each 43%). Compared to other size businesses, mid-sized organizations are more likely to experience infrastructure damage (25%).

How to avoid falling for a LinkedIn scam?
To avoid falling for a LinkedIn scam, it’s important to be cautious and alert. Start with making sure any job posting or business opportunity you’re interested in is legitimate before you apply or accept an offer. You can do it by researching the company or person offering the opportunity and only providing personal or financial information if you are confident they are not fake.
It’s also essential to protect your privacy on LinkedIn by adjusting your account settings to limit who can see your LinkedIn profile and send you messages. Be careful of unsolicited messages or connection requests from people you don’t know, and always watch out for signs that the message may be a scam, such as poor grammar, spelling mistakes, and overly aggressive or pushy language.
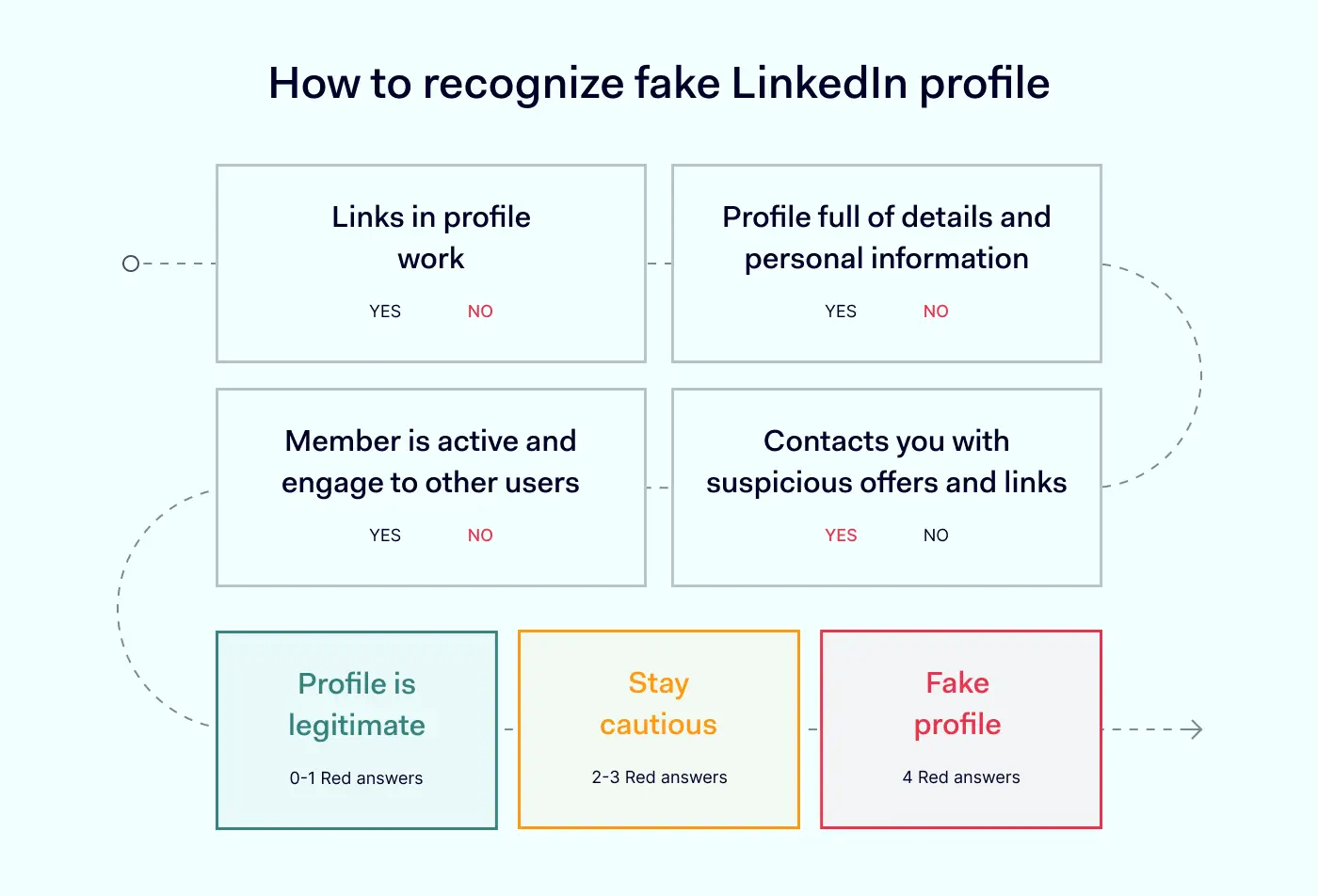
Tips for recognizing fake LinkedIn profiles
-
Check the links present in the profile. Real profiles link to the person’s company website or their professional social media profiles. Be careful of shortened links or links that redirect you to another website, as these may be used to disguise fraudulent websites.
-
Look for inconsistencies or lack of detail in the profile. A legitimate profile usually has a lot of information about the person’s professional history, education, and skills. Fake profiles typically have very little information or no profile picture.
-
Investigate the activity of the LinkedIn profile. If the profile has very little activity or engagement with other users, likely it’s one of the fake LinkedIn accounts. Additionally, suppose the allegedly fake profiles send connection requests to many people, particularly those without connection to the profile. In that case, it may be part of phishing attacks.
-
Be cautious of suspicious or irrelevant job offers, promotions, or messages from the profile. Fake LinkedIn profiles often use these tactics to lure users into scams, identity theft, or other harmful activities.
What to do if you’ve been scammed on LinkedIn?
If you think you’ve been scammed on LinkedIn, don’t panic. The first thing to do is to report the fraud to LinkedIn or the Internet Crime Complaint Center (IC3). Follow the instructions on LinkedIn’s Help Center page to report the scam. You should also contact your bank or credit card company if you have been charged for a fraudulent transaction.
To avoid getting scammed in the future, consider enabling two-factor authentication for your LinkedIn account, checking your account settings regularly, and changing your login details from time to time to ensure your account is secure.
FAQ
Are you worried about scams on LinkedIn? Sadly, LinkedIn is not completely safe from scams like many other online platforms. However, there are things you can do to spot and report scams to protect yourself and others.
How to report a scam on LinkedIn?
If you come across a scam on LinkedIn, first, you should report it to LinkedIn. Here’s how:
-
Go to the profile of the person or company involved in the scam
-
Click the “More” button below their profile picture
-
Select “Report this profile” or “Report this company”
-
Follow the prompts to provide details about the scam and submit your report
LinkedIn’s Trust & Safety team will review the submitted report and take appropriate action, including removing the scammer’s account and preventing them from creating another one.
How to identify a scammer on LinkedIn?
Scammers on LinkedIn may use a variety of tactics to trick people into giving them money or personal information. Some common signs of a scammer include:
-
A profile that appears to be fake or incomplete
-
Unsolicited messages offering a job or business opportunity that seems too good to be true
-
Requests for money, personal information, or account credentials
-
Pressure to act quickly or keep the opportunity secret
If you encounter any of these signs, it’s a good idea to investigate further before engaging with the person. You can also report the profile to LinkedIn as described above.
How can I check if a job offer on LinkedIn is legitimate?
Before accepting a job offer on LinkedIn, it’s a good idea to make sure it’s real. Here are some ways to check:
-
Research the company offering the job. Look for their website and social media profiles to learn more about them.
-
Check the job description for any red flags, such as vague or unrealistic requirements.
-
Ask for more information from the person offering the job. Legitimate employers will likely provide more details about the position and the company.
-
Look for reviews or ratings of the company on LinkedIn or other online platforms.
LinkedIn scams are a reality, but knowing how to recognize and report them can protect yourself and others from harm. If you encounter a scam on LinkedIn, report it to LinkedIn’s Trust & Safety team, and remember to be cautious when engaging with people you don’t know online.
How can NordLayer help?
NordLayer remote network access solution, by its design, protects digital company assets and their employees. By deploying functionalities for secure online browsing, organization administrators can bring more peace of mind in limiting company exposure to external threats.
Organizations can enforce ThreatBlock functionality that lowers the chances of employees potentially landing on malicious websites. This NordLayer feature helps reduce the risk of accessing publicly enlisted phishing sites, making it forbidden to access them.
To make security even stronger, the DNS filtering by category feature allows administrators to block access to the social media category and restrict access to certain websites for the whole organization.
If the blocking is exclusively required only for the LinkedIn site, admins can select and customize Deep Packet Inspection (DPI) Lite functionality for the organization’s network security. DPI Lite blocks specific ports and protocols from accessing when connected to a company network.
If you believe securing a team’s online activity is important for protecting your company, reach out to our team to discuss your options for creating a secure way of working in your organization.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.








