Ever wondered why even tech giants like Google approach European internet laws with caution? The answer is the Network and Information Systems (NIS2) Directive, a beacon in the world of internet safety.
The old rules, laid down in 2016 by the NIS Directive, fell short of safeguarding against cyber threats. While they addressed sectors like healthcare and energy, many industries remained uncovered. But now, the tables are turning. The new NIS2 Directive creates a unified EU front against cyber risks, rewriting the rules for this new digital age.
In this piece, we’ll explore how the NIS2 Directive reshapes the cyber security landscape in Europe and what it means for businesses and governments. Learn how to navigate this evolving terrain and stay compliant without incurring penalties.
The need for evolving cyber law in Europe
It’s no secret that online threats have transformed into something far more sinister than we could have imagined. The time has come for Europe to embrace new cybersecurity legislation that will effectively combat the complexities of these threats. This section will explain how online risks have evolved and why new laws are required.
The changing face of cyber threats
In the past, cyber threats were mainly the work of individual cybercriminals. They were like digital graffiti artists, tagging websites and perhaps swiping some data for their bragging rights.
Now, things are more severe. We face organized groups, and sometimes even governments, harnessing the power of cyber attacks. The objective? Stealing vast amounts of data or causing disruption of critical services.
These aren’t just one-off events anymore. Cyber threats have turned into ongoing campaigns targeting sectors like energy or healthcare. With the omnipresence of the internet in everything from our refrigerators to our cars, the risks have infiltrated every nook and cranny of our lives. The cybersecurity landscape has changed, and Europe needs to update its legislative arsenal to counter these digital dangers effectively.
Time for an upgrade: why the old NIS Directive isn’t enough
Back in 2016, the European Union took its first step in the battle for cybersecurity with the Network and Information Systems (NIS) Directive. It was a start, but it soon became evident it had limitations.
For one, it only covered specific sectors, like energy and healthcare. Many other industries that could be vulnerable to cyber-attacks were left out.
Moreover, the directive’s implementation was a patchwork quilt. Each EU country adopted its own interpretation of the rules. This inconsistency meant that while one nation might be doing a great job fortifying its cybersecurity defenses, its neighbor might lag behind.
In short, the old rules weren’t enough, and it was time to bridge the security gaps. This is where the NIS2 Directive stepped in to address them.
Far-reaching impact of the NIS2 on cybersecurity
NIS2: fixing the flaws of its predecessor
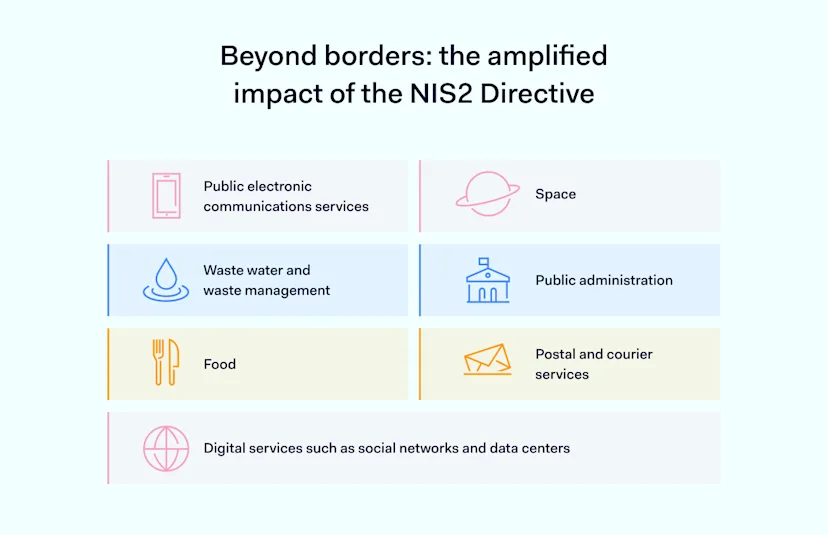
The new and improved NIS2 Directive is Europe’s upgraded plan to make the digital world safer. Unlike the old rules, NIS2 covers a lot more ground. Financial services, public administration, and digital platforms all come under its umbrella.
That means more types of companies have to follow the rules and take measures to safeguard their digital assets. But it’s not just about adding more sectors. NIS2 also brings greater unity among EU countries regarding cybersecurity.
Instead of each country making its own rules, NIS2 established baseline requirements that apply everywhere. This way, the EU can act like one big team in defending against cyber threats, making everyone’s digital life safer.
The NIS2 toolkit: key features for cyber safety
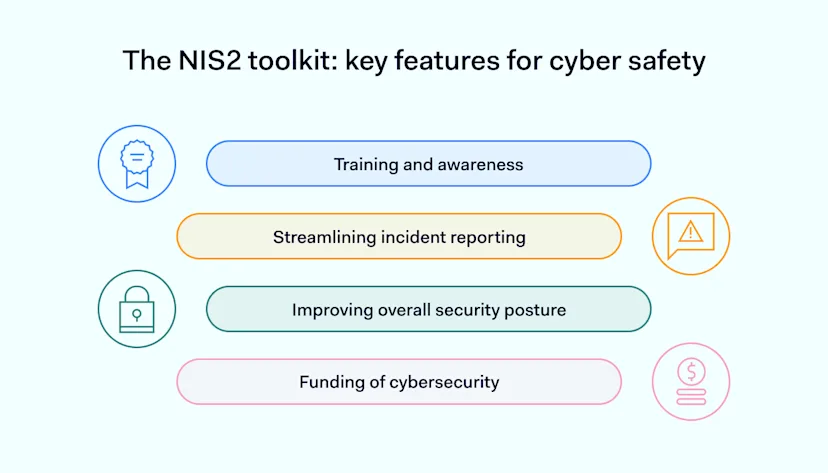
So what’s new in NIS2? First, companies must put in specific security measures that match the cyber risks they face. It’s not a one-size-fits-all solution, but it’s more about adapting to the situation at hand.
Training and awareness
While NIS1 has a nod to raining and awareness-raising, NIS2 takes up a notch, possibly requiring more structured training programs. Organizations must show evidence of ongoing training and be subject to audits to ensure that employees are well-prepared.
Streamlining incident reporting
While NIS1 encouraged incident reporting, the requirements weren’t very specific. Organizations were generally advised to have some form of incident reporting but were given more latitude in implementing it.
But NIS2 steps up its game in incident reporting. It aims to standardize procedures with specific timelines, formats, and more detailed reporting requirements. The goal is to make incident reporting more efficient, ensuring quicker response and better mitigation.
Improving overall security posture
Previously, organizations were encouraged to improve their cybersecurity measures continuously, but the directive wasn’t very prescriptive about how this should be done.
NIS2 pushes organizations to enhance their security posture continuously. This could mean more frequent audits, detailed reporting, and specific milestones to demonstrate progress.
Funding of cybersecurity
While NIS1 hinted at the importance of adequate funding for effective cybersecurity, NIS2 goes further, emphasizing the need for ample financial resources for cybersecurity. Organizations may be required to allocate a specific percentage of their budget to cybersecurity or meet minimum spending requirements.
Plus, NIS2 has stiffer penalties for companies that fall short of compliance. This gives companies a solid reason to take cybersecurity seriously.
Now that we’ve uncovered what NIS2 brings to the table, let’s explore how it impacts businesses and government offices in the next section.
The NIS2 impact: what businesses need to know
The legal framework
The NIS2 Directive isn’t just another set of guidelines, it’s the law. Medium-sized and large enterprises should understand that compliance isn’t an option but a legal requirement. And it’s not just about avoiding penalties. It’s about fortifying your business infrastructure to protect valuable assets and customer data.
Cost of compliance vs. cost of non-compliance
Yes, implementing the NIS2 Directive requires an investment in time, personnel, and resources. But think about it this way: the cost of non-compliance, including legal repercussions and potential loss of consumer trust, can be much more damaging to your bottom line and reputation.
The Directive is designed to create a safer digital environment that can serve as a unique selling proposition for customers who value data privacy.
Long-term gains: beyond just avoiding penalties
NIS2 compliance is an investment in the future. While the initial setup may demand resources, robust cybersecurity measures can significantly reduce the risk of data breaches and cyber-attacks, both financially devastating and detrimental to a company’s reputation.
Maintaining a secure digital ecosystem can become your competitive edge in a world where data leaks or breaches make headlines.
Cybersecurity is a public concern: the NIS2 Directive mandates it
For public administration entities, cyber security isn’t just about protecting sensitive data. It’s about safeguarding the lives and well-being of millions. A cyber-attack on a government body isn’t just a headline, it could lead to a national emergency.
Under the NIS2 Directive, these organizations must improve their cybersecurity to prevent such potential disasters.
Layers of government: everyone is affected
It’s not a one-size-fits-all solution. Public administrations, from central to regional and local levels, must go beyond mere software upgrades. The NIS2 rules demand a comprehensive review and transformation of how these entities manage data, deploy security protocols, and respond to incidents. No matter the size or scope of the government body, compliance with these new measures is essential.
Holistic approach to cybersecurity
Public administration entities must adopt a holistic cybersecurity strategy that addresses risk assessment, preventive measures, and contingency planning. This comprehensive approach ensures that damage can be minimized in the event of an attack, and normal operations can swiftly resume.
Navigating the global landscape
Even if your company is not based in Europe, you can’t ignore Europe’s online safety rules if you’re doing business there. The rules are like a digital handshake, mandatory for anyone offering digital services or handling data in the EU.
Crossing borders: NIS2’s reach beyond Europe
So, what does it mean for global businesses? If your company has its headquarters halfway across the globe, you’re in the spotlight, too. You must follow these new rules when operating in Europe. But don’t worry, it’s a fantastic opportunity. Following these guidelines can signal to European customers that you take security seriously, boosting your appeal. But, word of caution: getting the details right is crucial because the penalties for messing up can be steep.
Global players: future implications and representative requirements
Under NIS2, you can’t simply wing it. If you’re a foreign company doing business in the EU, you need a representative in the EU. They’re your go-to for ensuring all these rules are followed. And it’s not just a formality, it’s a crucial role.
But here is the exciting part: the implications for the future are significant. Global standards like NIS2 might become the norm as the digital world grows. Companies that get it right in Europe now will be a step ahead of the game when similar laws start popping up in other parts of the world.
Now that we’ve covered the new rules and who they apply to, our next section will dive into best practices for organizations to ensure they stay on the right side of the new guidelines.
NordLayer: your NIS2 compliance partner
Navigating the complex world of NIS2 compliance is like solving a puzzle. And while NordLayer may not be the whole solution, it can help you tick off several boxes on your compliance checklist all at once.
NIS 2 legislation, in Article 5, calls for digital service providers to employ suitable technical and organizational measures to secure their networks and information systems. Virtual Private Networks (VPNs) can be particularly helpful in meeting the “appropriate and proportionate” security measures outlined in Article 5.
Specifically, NordLayer offers a secure tunnel between an employee’s device and the corporate network. This ensures that sensitive data, like customer information or intellectual property, is shielded from unauthorized access. This is a powerful step towards managing network and information system security risks, as NIS2 demands.
Article 16 of NIS 2 emphasizes secure data transmission as a core compliance aspect. And here is where VPNs play a crucial role. They encrypt data during transit between different locations or systems. This encryption aligns directly with the article’s requirements to protect against unauthorized access and data tampering. With NordLayer, you’re well on your way to meeting the “technical and organizational measures” stipulated in this article of NIS 2.
In conclusion
We’ve discussed the necessity for Europe to modernize its cybersecurity laws through the NIS2 Directive. This transformation impacts not just IT teams but entire businesses. As the EU unfolds these comprehensive new guidelines, the responsibility falls on organizations to adapt accordingly.
Don’t hesitate to reach out and explore how NordLayer can be a valuable addition to your cybersecurity arsenal, assisting you on your journey toward alignment with the EU’s evolving digital laws.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordPass
NordPass is developed by Nord Security, a company leading the global market of cybersecurity products.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.





)