As we navigate through the rapidly evolving landscape of cybersecurity in 2024, it’s crucial to recognize the dynamic nature of cyber threats. Gartner forecasts that worldwide end-user spending on security and risk management will reach $215 billion in 2024, a 14.3% growth from 2023. This investment reflects the increasing complexity of digital risks.
We explore the top 10 cybersecurity trends, each of them presents unique challenges and requires nuanced responses from cybersecurity professionals.
Key takeaways
Global cyber conflicts are escalating rapidly.
Data breaches in healthcare are increasing.
Remote work brings new security challenges.
Human error is the main reason for cybersecurity breaches.
Ransomware attacks require better response strategies.
Cyber warfare: an evolving threat in cybersecurity
In 2024, cyber warfare mirrors global tensions, growing in sophistication.
Russian cybercriminals disrupt Ukrainian and European supply chains, impacting aid delivery. A new group, “Cyber Toufan,” believed to be backed by Iran, attacked Israeli companies.
The U.S. grapples with cyber threats from Chinese state-linked threat actors. They have infiltrated about 25 organizations, including U.S. government agencies. Such cyber strikes demonstrate the growing scope of state-sponsored cyber-attacks and emphasize the need for robust cyber defenses.
Impact on the 2024 presidential elections
In the 2024 presidential elections, the shadow of past cyber intrusions looms large. The 2016 election was marred by Russian state-sponsored cyber-attackers who stole and leaked emails from the Democratic National Committee (DNC) and Hillary Clinton’s campaign chairman, John Podesta.
The trend persisted into 2020, when Fancy Bear, the Russian military intelligence-linked unit involved in the 2016 breaches, attempted to gain access to accounts of both Republican and Democratic political consultants, advocacy organizations, and think tanks. Although a specific attack on a Democratic presidential candidate’s advisory firm was thwarted, these incidents signal potential risks for the 2024 elections.
Healthcare sector vulnerabilities
The Health Insurance Portability and Accountability Act (HIPAA), established in 1997, sets strict rules for patient data protection in the healthcare sector. Despite this, healthcare continues to face significant cyber threats.
Recent trends in healthcare cybersecurity show both challenges and progress. The breaches, often due to unauthorized data access, underscore how vulnerable the sector is to cyber-attacks. In 2022, the U.S. healthcare sector saw 344 data breaches. By October 2023, this number decreased to 69 cases, a decline from the peak in 2015.
The consequences of these cyber-attacks are profound. They not only cause financial and reputational damage but also affect patient care. Recent data links ransomware attacks to higher mortality rates and longer hospital stays.
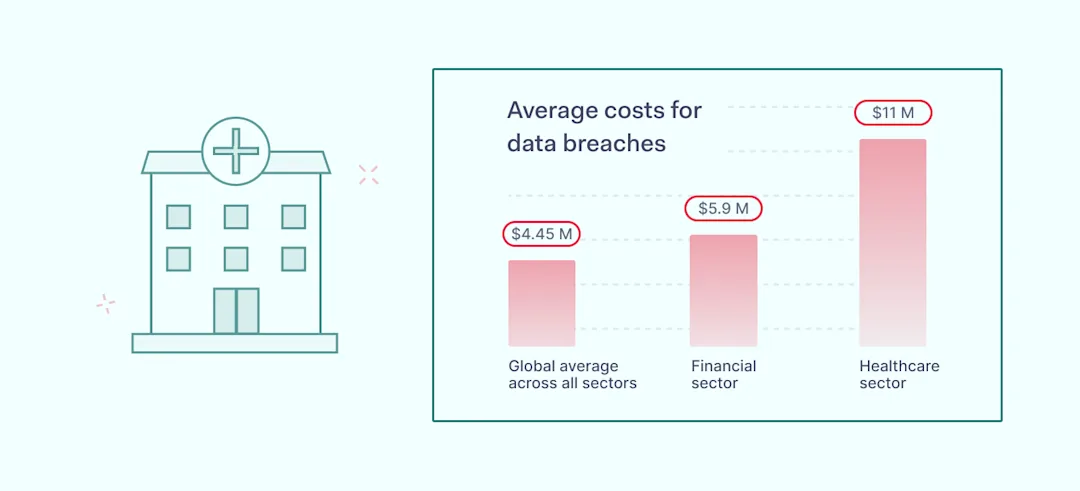
The high cost of health data breaches
From March 2022 to March 2023, the healthcare industry faced the highest costs for data breaches. On average, each breach cost nearly 11 million U.S. dollars. The financial sector ranked second in comparison, averaging 5.9 million U.S. dollars per breach. Across all sectors, the global average data breach cost was 4.45 million U.S. dollars.
![]()
Cybersecurity challenges in the hybrid work environment
In the hybrid work model, several cybersecurity risks are evident. The introduction of various devices and networks expands the potential for cyber threats. Limited control over remote workers and workspaces makes securing devices a challenge. Using public Wi-Fi, especially when traveling, increases exposure to cyber-attacks. Additionally, working across borders can lead to compliance issues with different data privacy laws.
Despite these risks, the shift towards hybrid work persists, making it essential for companies to enhance their cybersecurity strategies to navigate the changing environment.
Generative AI: a new frontier in cyber threats
Generative artificial intelligence, particularly in the form of deepfakes, has emerged as a novel threat in the cyber world.
In August 2023, Mandiant, a cybersecurity firm owned by Google, reported a groundbreaking discovery. They found deepfake video technology being explicitly crafted and marketed for phishing scams. Remarkably, the cost for these deceptive tools was minimal: $20 per minute, $250 for an entire video, or even $200 for a training session.

This development signals a trend in the cybercrime landscape, where advanced artificial intelligence becomes a tool for fraud at surprisingly low prices. This marks a new challenge in cybersecurity.
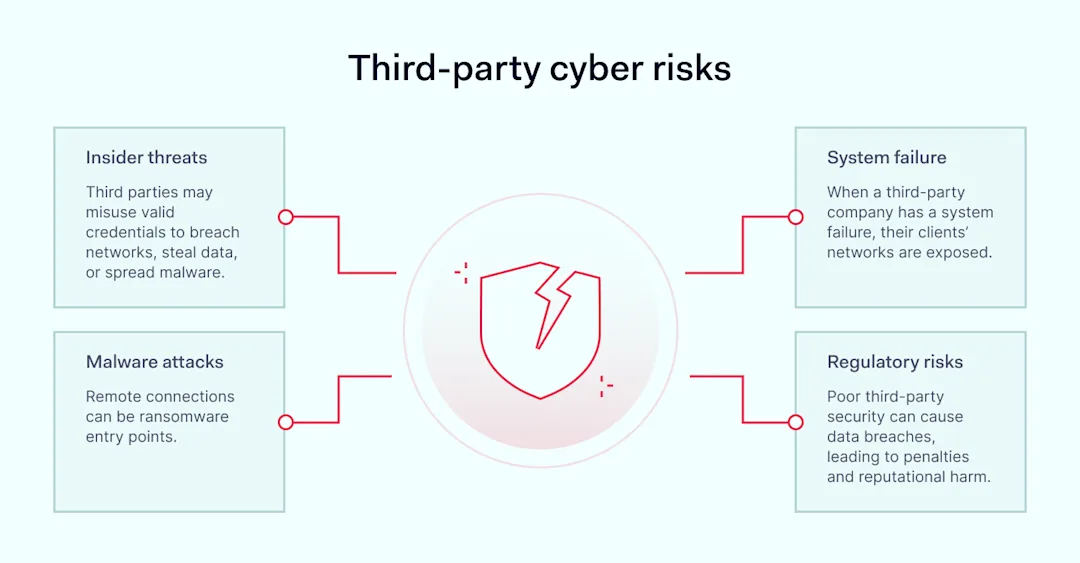
Supply chain attacks: a growing concern
In June 2023, a North Korean cybercriminal group breached JumpCloud, a SaaS provider, targeting cryptocurrency companies. A report by Chainalysis states that North Korean-linked groups stole about $1.7bn in digital cash through multiple attacks last year.
Supply chain attacks have surged, with a 633% increase in 2022 alone, becoming a prominent part of cybersecurity trends. Factors driving this trend include complex, global supply chains and the sophistication of cyber-attacks.
![]()
Cloud security and the threat of cloud jacking
Cloud jacking, where attackers hijack cloud accounts, surged in 2023. Cybercriminals exploited cloud vulnerabilities, used phishing or stolen credentials. Once inside, they could steal data, plant malware, or disrupt services. The growing reliance on cloud services widened the potential for such attacks.
Key trends in 2023 included more frequent attacks on SaaS applications and increased automated scanning for cloud weaknesses. Ransomware became a favored tool, locking organizations out of their own cloud data. In 2022, API security lapses contributed to the risks, with a 286% increase in API threats and 34% of organizations without a strategy to protect APIs, leaving 91% of APIs exposed to data theft.
Double and triple extortion
The trend of double and triple extortion in cybercrime has escalated. Techniques combining encryption, data theft, and DDoS attacks are more frequent. Data exfiltration is on the rise, with an increase from 40% in 2019 to 77% in 2022, with 2023 on course to surpass 2022’s total. With this upward trajectory, 2024 is likely to see a continuation of these cyber extortion tactics.
![]() Social engineering and user privacy: the human factor
Social engineering and user privacy: the human factor
The human element is a significant factor in cybersecurity incidents, with 95% of breaches attributed to human error. This makes it not only a common issue but also a costly and serious one.
In 2023, several major security breaches occurred due to human errors. On January 11, 2023, MailChimp employees fell victim to social engineering by an external party, affecting 133 customers. This incident involved WooCommerce, a widely-used eCommerce plugin for WordPress, leading to the exposure of customer names, store URLs, and email addresses. MailChimp responded by restricting access and informing those affected. They assured that no credit card or password information was compromised. However, the breach highlighted the risk of potential phishing attacks aimed at obtaining credentials or introducing malware.
![]()
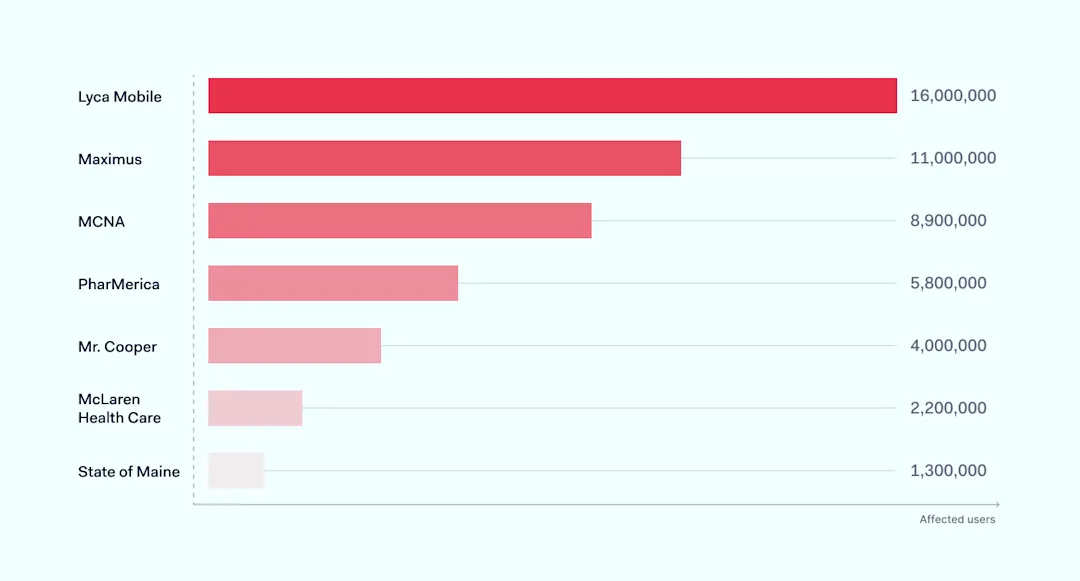
Ransomware threats: evolution and response
In 2023, ransomware attacks continue to threaten organizations, with attackers demanding payment to decrypt critical data. The impact is growing; U.S. healthcare organizations faced an average downtime of 18.71 days due to these attacks, up from 16 days in 2022. This underscores the evolving nature of cybersecurity trends in ransomware.
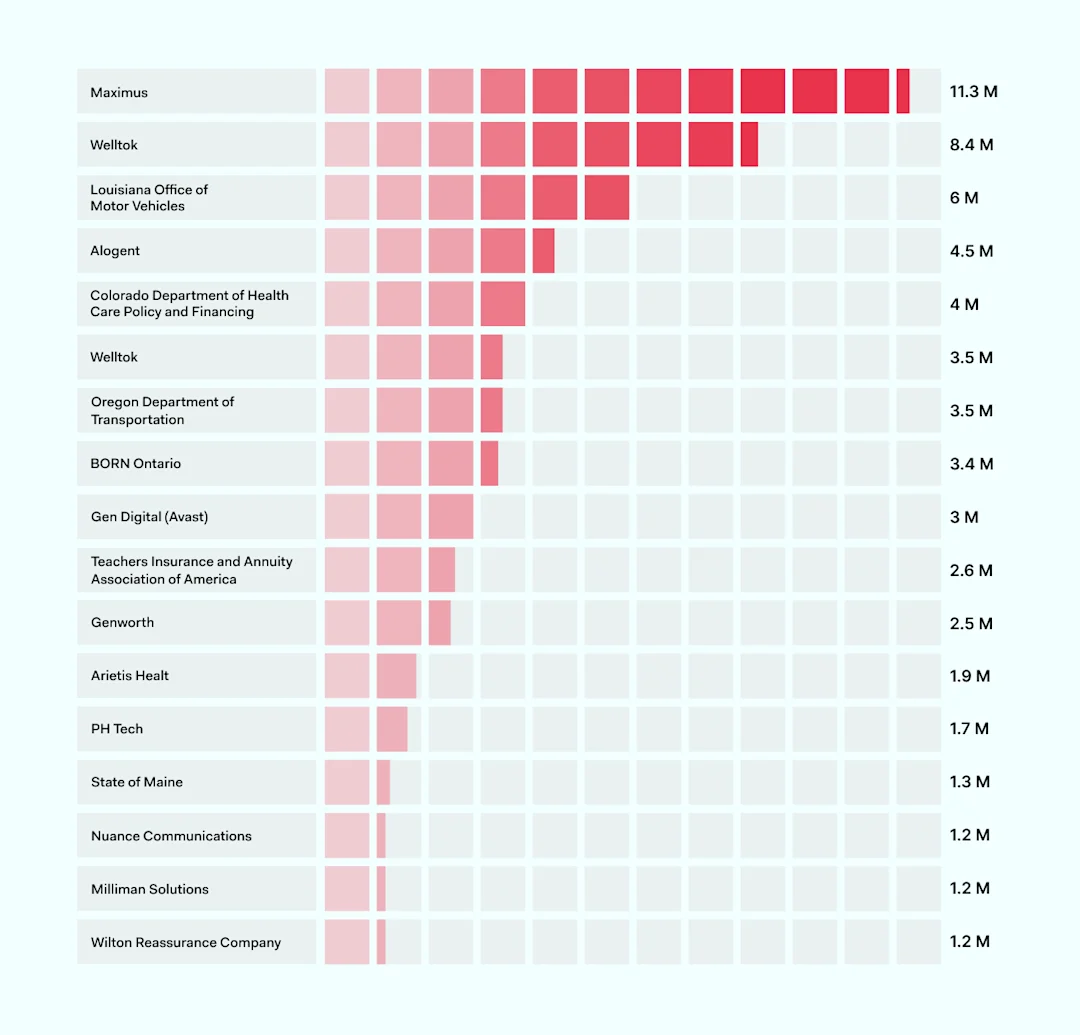
The rise of mass ransomware attacks
This year also witnessed a surge in mass ransomware attacks, with ransom-as-a-service groups exploiting software vulnerabilities to target numerous companies simultaneously. Notable incidents include the MOVEit and GoAnywhere software breaches, affecting hundreds of companies. Such widespread cyber-attacks signal a significant challenge for the cybersecurity and insurance sectors, potentially changing the industry’s approach to risk assessment and claims management.
Advancements in Zero Trust security
In the context of current cybersecurity trends, a positive development is also emerging. Zero Trust security, once a strategic goal, is rapidly becoming standard practice. By 2026, it’s expected that 10% of large enterprises will fully implement mature Zero-Trust programs, a significant rise from less than 1% currently.
Implementing Zero Trust is complex, requiring the integration of various components. The key to success lies in demonstrating its business value. Beginning with a simple, scalable approach allows organizations to progressively understand and adopt the framework, managing its complexity step by step.
Strategies for business safety in 2024
Use multi-factor authentication (MFA) to regulate network access.
Add extra authentication factors for administrative accounts.
Assign minimal user privileges in line with Zero Trust principles.
Secure remote devices with VPNs.
Require strong, regularly-changed passwords.
Encrypt all high-value data.
Use data loss prevention (DLP) tools to track valuable data.
Use intrusion detection systems/intrusion prevention systems (IDS/IPS) to track threats in depth.
Back up data regularly.
Audit backups and threat responses to ensure quick disaster recovery.
Regularly test your security systems.
Risk assess core threats and create response plans.
Train all staff to detect phishing attacks.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.