In the world of cybersecurity, things move at lightning speed. And so do we at NordLayer. We’re committed to delivering cutting-edge, secure remote network access solutions for our clients. What’s our secret to success? A robust strategy, clear product vision, and insights that help us develop high-quality products.
At NordLayer, we never lose sight of our goals. We continually track our product’s growth, ensuring we always head in the right direction. We aim to provide a remote network access solution that fulfills our promise to all our customers and fosters sustainable progress.

![]() When we look back at the milestones we’ve achieved and those on the horizon, we’re confident about our product lifecycle. Even now, we can see that our developments gained rapid momentum, consistently improving and delivering the best experience for all ways of working.
When we look back at the milestones we’ve achieved and those on the horizon, we’re confident about our product lifecycle. Even now, we can see that our developments gained rapid momentum, consistently improving and delivering the best experience for all ways of working.
This is our epic journey of shaping the cybersecurity landscape and enhancing business security.
Our roadmap for a remote network access solution
Our journey started with an ambitious goal: to enable hybrid and remote work in a user-friendly way. We believe a connected world where all work models are possible needs protected connections, and that’s precisely what we’re crafting.

![]()
Every story has its humble beginnings, and so does NordLayer’s product. Let’s now take a look at our product’s gradual yet significant growth and where our remote network access solution stands now.
Foundation & breakthrough
Our original name was NordVPN Teams. We began as a B2B version of NordVPN (yes, the very VPN that consumers love worldwide). Naturally, it was referred to as a business VPN tool to secure organization connections.
Launched back in 2019, NordLayer started its offering with almost thirty Shared and nearly twenty Private Gateway locations around the globe. Running on three VPN protocols, the tool did a decent job protecting companies on the brink of the pandemic.
It was a time when NordLayer emerged as a virtual private network tool for organizations that needed to protect their teams working remotely and in different settings. Soon, the product capabilities were challenged by the new normal, a.k.a. COVID-19.
Overnight, we faced the task of onboarding hundreds of employees, ensuring secure connections and business continuity. It was a baptism by fire. We embraced and overcame this challenge as a tryout and aspiration to offer protection for businesses around the world.

Elimination of a physical office required new solutions here and now. So, connecting different locations with Site-to-Site functionality and Auto-connect feature were NordLayer’s hatching out of the VPN-only product shell. We quickly realized we had outgrown our shoes and needed to enhance our capabilities to offer an even better solution.
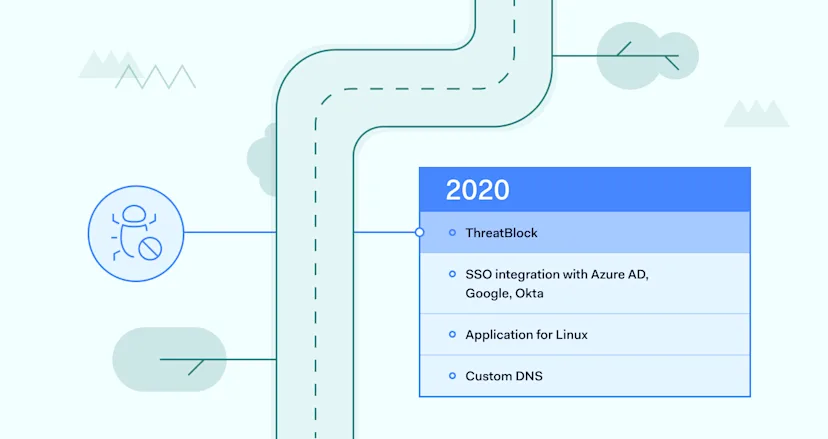
In 2020, ThreatBlock took the spotlight as NordLayer’s flagship release. It was initiated by the business need to secure networks from potential risks. What’s unique about ThreatBlock is that it automatically blocks harmful websites, so no malware or other cyber threats can infect your device.
Followed by identity management enhancements of single sign-on (SSO) integration with major service providers in the market Azure AD, Okta. Also, Google Workspace, the solution soon became available on all major OSs.
The introduction of custom DNS functionality marked the time for something big to evolve.
NordLayer created a sophisticated offering to start establishing its market position. Based on existing features and our future vision, we quickly noticed how prominent NordLayer is in Zero Trust Network Access (ZTNA) and Secure Access Service Edge (SASE) frameworks. Naturally, that led us to focus our development efforts in that direction.
Strategic navigation
The year 2021 started with improving what NordLayer offered its customers in the ZTNA department.
Listening to feedback and adjusting to client business needs, we increased the number of Virtual Private Gateway locations.

We also introduced one more SSO integration with OneLogin, a popular user identity access management service provider, and added biometric authentication for a full range of trusted user authentication options.
But these were just stepping stones compared to the launch of the year, a Smart Remote Access functionality. It was like a network bridge interconnecting devices and creating a virtual LAN, bringing relief to IT administrators and employees and allowing them to work more efficiently wherever they are.

As we navigated through a saturated cybersecurity industry market in 2022, our focus remains on a user-friendly implementation of complex concepts like network security. We also defined our vision and mission, dedicating ourselves to stress-free cybersecurity for our customers, no matter their work setup.
Leaning towards Security Service Edge (SSE), a part of the SASE framework, NordLayer made network security as a service its main strategy. This approach, combined with the ZTNA model, emphasized the performance and convenience of using the tool.
Hence, the NordLynx (WireGuard) protocol was created to drastically increase connection speed compared to other protocols, maintain service quality, and security.
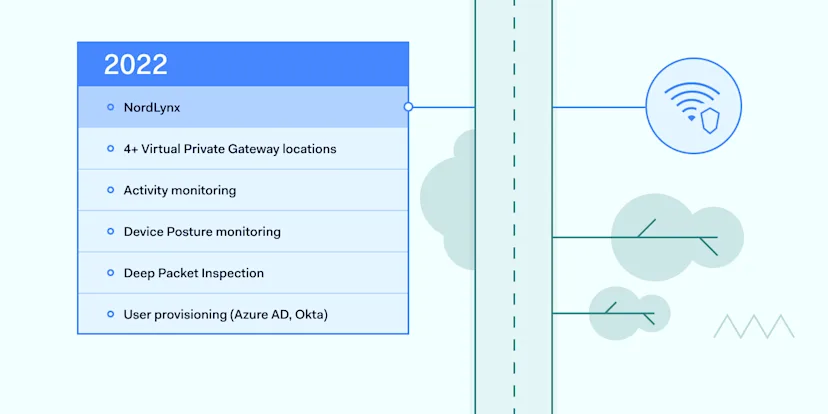
VPNs can slow things down, causing delays. But NordLayer aimed to eliminate this interference so customers forget about the solution running in the background on their computers. And from what we’ve heard, we succeeded in achieving seamless and uninterrupted connections.
So, have you already noticed that we at NordLayer are always up for a challenge? A growing number of Virtual Private Gateways in locations like South Africa and Brazil was a project that led to better service coverage.
Moreover, we added user provisioning functionality with Azure AD and Okta for swift organization onboarding and management to improve the service experience for our customers.
Momentum mastery
The year 2022 also proved to get momentum and turn into a snowballing escalation that only confirmed — buckle up, there’s no way back.
With a focus on Network Access Control and a commitment to meeting compliance requirements, NordLayer introduced Activity monitoring and Device Posture Monitoring for advanced network visibility.
For a more robust and effective Internet Access Security, existing features were accompanied by DNS filtering by category and Deep Packet Inspection (DPI), so the product offers a robust and supportive network management system for our customers.

Automation of processes is the future, and we at NordLayer know it well. That’s why we implemented automated idle session timeouts from the NordLayer application. What’s more, optional enforcement of multi-factor authentication (MFA) and SSO for logging into the Control Panel was added to help ensure advanced security measures for our clients.
In 2023, NordLayer launched a one-of-the-kind Browser Extension to provide more connectivity opportunities to our customers.

A lightweight NordLayer version lets you multitask and secure connections on a browser level. It expanded how users can connect to NordLayer because, unlike the application, it doesn’t need to be OS-compatible and runs only on a browser.
Always On VPN was another big launch for NordLayer. It was dedicated to keeping users connected so organizations could trust that VPN connections stayed active.

To make rolling out NordLayer easier, we introduced the Team Administrator role. This allows admins to share some of their responsibilities in managing team access rights.
For a wider range of third-party service providers, JumpCloud became one of the five options to choose from SSO providers.
Unveiling the next era of NordLayer developments: Cloud Firewall & Device Posture Security
For better network access control, NordLayer is preparing to launch an upgraded Device Posture Security functionality. The already available capability to monitor who and when connects to a company gateway got enhanced with non-compliant device account blocking.
Improved functionality will allow IT admins to create rules, such as defining versions of OS and NordLayer, adding a requirement to have a specific file in a device, seeing if the device is rooted, and, in case of deviations from set rules, blocking the device from entering the network.
Finally, 2023 will be marked with a major product release–Cloud Firewall (FWaaS). The new soon-to-be-released feature will bring NordLayer closer to becoming a unified SSE platform provider. Undoubtedly, it’s a huge upgrade for more granular access control, which allows to deny or allow access based on User/Team, destination, protocol, and port delivered straight from the cloud.
NordLayer’s Cloud Firewall feature will be a great addition to hybrid infrastructures and a relief for legacy organizations that can finally replace expensive and resource-consuming hardware with security deployment in a few clicks.

Simple, intuitive, easy to roll out and use, and efficient, these are the words we often hear from our customers talking about their experience using NordLayer, and it couldn’t make us happier because that’s our goal to strive for.
This encourages the team to work on new and improved product capabilities constantly. We celebrate big launches and get to work even harder to deliver the most stress-free and robust network security solutions.
NordLayer use cases
Product development is an exciting and rewarding process. But without a clear vision and application, all great work can’t be used to its full potential. Thus, NordLayer formulated the main use cases our clients refer to us for help and support.
Internet access security
Modern enterprises, navigating the intricate challenges of internet access security, find themselves at a crossroads—balancing communication demands against rising cyber threats. The transformation in work models—remote, office, and complex hybrid—has introduced unique security challenges.
Threat prevention
NordLayer uses advanced encryption standards to protect data in transit. Whether employees work on-site or remotely, their internet traffic is encrypted, safeguarding company data from threats, potential eavesdroppers, and cyberattacks.
Business VPN
With NordLayer, employees can securely connect to public Wi-Fi networks, such as those in cafes or airports, without the risk of data interception. The VPN shields their connection from potential threats commonly associated with public networks.
Cloud VPN
As businesses increasingly utilize cloud services, NordLayer ensures that access to these resources remains restricted and secure. Whether it’s cloud storage, SaaS applications, or other cloud-based resources, NordLayer’s protective layer ensures seamless and straightforward integration that reduces the risk of data breaches.
Network & resources access management
Companies face the challenge of managing diversified and global teams while embracing a hybrid work model without compromising security. NordLayer, rooted in the Zero Trust model, presents an innovative solution to network and resources access management.
Remote access VPN
A remote access VPN ensures secure connections to company resources, whether in-office or remotely. It encrypts user traffic, safeguarding data from unauthorized interception. With NordLayer, businesses can create dedicated gateways for encrypted access to their network, balancing data availability and security for all workers.
Identity and access management
NordLayer’s Zero Trust approach ensures that only verified users with the right permissions can access specific network resources. This model operates on a trust-no-one-verify-all principle, incorporating strict security measures like 2FA, MFA, SSO, and biometrics to ensure airtight user validation before granting access.
Secure Remote Access
Designed for modern, distributed workforces, NordLayer’s Secure Remote Access application allows teams to connect to company resources from any location. This feature enhances flexibility and maintains a high level of security, ensuring that remote connections are as secure as on-premise ones.
Network segmentation
NordLayer provides organizations with the ability to segment their network through private gateways. This segmentation permits organizations to allocate specific resource access to certain user groups, ensuring that sensitive sections of the network remain insulated and accessible only to those who require it.
Achieving compliance
As regulations intensify and cyber threats amplify, achieving compliance has never been more critical. With staggering statistics revealing the vulnerability of many enterprises, investing in robust cybersecurity mechanisms like NordLayer is essential.
Remote access VPN
NordLayer ensures that connections and all data transfers are encrypted, safeguarding sensitive information from unauthorized access. This is especially crucial for organizations subject to regulations like HIPAA and GDPR, which emphasize the importance of data confidentiality.
NAC and monitoring
NordLayer enforces rigorous access controls, such as single sign-on (SSO), biometrics, and two-factor authentication (2FA). Additionally, it offers 24/7 network activity monitoring, allowing organizations to track secured connections, detect anomalies, and promptly address potential security incidents.
Network segmentation
By implementing network segmentation, NordLayer allows businesses to allocate resource access using private gateways. This heightens overall network security and restricts movement within the network, limiting potential damage from cyber breaches. Such segmentation is essential for compliance with standards that mandate limited and controlled access to specific data sets.
How NordLayer can address your business needs
We cannot emphasize enough how NordLayer outgrew being a simple business VPN and started offering beyond-reaching functionalities. Features we develop unlock a number of different possibilities to secure businesses in many ways:
Protect traveling employees & secure access through public Wi-Fi.
Prevent access to malicious websites while browsing the internet.
Access geo-specific content needed for quality assurance or remote customer support.
Ensure IP address masking.
Monitor VPN usage in the organization and generate reports.
Ensure that employees are connected to a VPN at all times.
Allowlist specific cloud tools with fixed IP addresses.
Segment network access to hybrid-cloud resources by teams.
Restrict access to content categories or specific apps, ports, and protocols.
Monitor and restrict non-compliant devices in the organization’s network by predefined security rules.
Establish a connection between remote devices and a remote connection to on-site networks.
Provide access to company resources on a browser level only.
Looking forward to innovation and growth
Looking towards the future, our primary objective remains the same: ensuring our customers enjoy uninterrupted growth fortified by robust network security. We recognize the evolving dynamics of modern workplaces and are committed to enabling every way of working.

![]()
To achieve this, we’re looking closely into the SSE framework by developing and providing ZTNA, FWaaS, and SWG features. These advanced models allow us to offer a seamless, stress-free security environment, ensuring that our clients can focus on their core operations, confident in the knowledge that their network remains impervious to threats.
Where NordLayer is today, and its direction forward, gives us the confidence to offer our clients a stress-free and user-friendly network access security solution. A product that enables businesses to achieve the best results, improve productivity, and take their technological posture to another level.
For us, it’s all about fulfilling our goals to deliver an effective, secure, and genuine cybersecurity tool for modern companies. If you want to learn more about security solutions, contact our sales team.
In this episode, we dive into:
ChatGPT’s evil twin WormGPT
The Federal Trade Commission (FTC) investigation into OpenAI data leak and ChatGPT’s inaccuracy
A new 4-day rule for disclosing cyberattacks set by the US Securities and Exchange Commission (SEC)
ChatGPT’s evil twin WormGPT
The new tool, WormGPT, is advertised on underground forums as a blackhat alternative to ChatGPT for launching phishing and business email compromise (BEC) attacks. Although, ChatGPT’s natural language abilities can already help hackers write convincing emails, resulting in the obvious signs of malicious emails disappearing.
Tools like ChatGPT and Google’s Bard have some safeguards in place that try to ensure that AI-generated content does not cause harm. However, WormGPT is specifically designed to be fully unrestricted and facilitate criminal activities, so it raises even more questions about the ethical limits of AI.
FTC investigates OpenAI over data leak and ChatGPT’s inaccuracy
Has ChatGPT broken consumer protection laws by risking personal reputations and data? The FTC has opened an investigation into OpenAI, requiring details on how OpenAI gathers and protects data and vets information.
The FTC wants to know how information was used to train its model and how it prevents false claims from being shown to users. Additionally, they are interested in how APIs connect to OpenAI’s systems and how user data is protected, all while the FTC issued multiple warnings that existing consumer protection laws apply to AI.
The 4-day deadline for public companies to report breaches
US companies hit by cyberattacks will face a 4-day deadline for publicly disclosing hacks, under new rules approved by the US Securities and Exchange Commission (SEC). There are mixed feelings about this new requirement. On the one hand, it is praised for encouraging transparency about cybersecurity breaches, as they are considered as important to investors as any other significant operational disruption.
On the other hand, the new rule is being labeled as a controversially short deadline that may not allow companies enough time to put an action plan in place or fix vulnerabilities. Although regulations state that if the SEC is informed in writing of a national security or public safety risk, a delay in breach disclosure of up to 60 days is allowed.
Stay tuned for the next episode of Cyberview.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About NordLayer
NordLayer is an adaptive network access security solution for modern businesses – from the world’s most trusted cybersecurity brand, Nord Security.
The web has become a chaotic space where safety and trust have been compromised by cybercrime and data protection issues. Therefore, our team has a global mission to shape a more trusted and peaceful online future for people everywhere.