Third-party resources enhance cloud deployments, allowing businesses to expand their operations and add new services. However, using third parties can also lead to security issues. Installing third-party services correctly is critical if you want to extract maximum benefit.
This article will examine the issue of third-party vendor integration. We will look at why third-party resources bring so many benefits. We will discuss some critical challenges and best practices to achieve successful integrations. The result will be a clear understanding of how to optimize access to third-party resources.
Understanding third-party resource integration
Third-party integrations are cloud resources or services supplied by external providers. The end user or site owner does not own them. However, third parties may still have access to a client’s cloud-hosted data.
For example, Google Maps integrations allow website visitors to locate retail locations. In this case, the Maps infrastructure is located off-site and delivered by a third party.
Third-party resources reduce the workload for cloud users by replacing tools that would otherwise be locally hosted or developed in-house.
Third parties add functionality. Companies can spin up apps or APIs supplied by external vendors. This accelerates development times and allows businesses to serve customers more effectively.
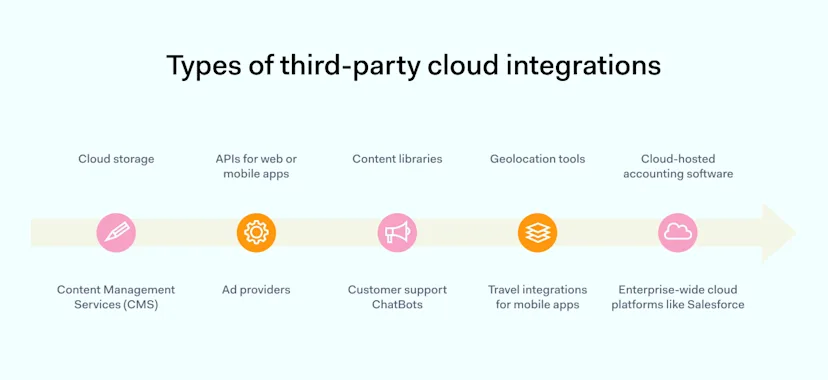
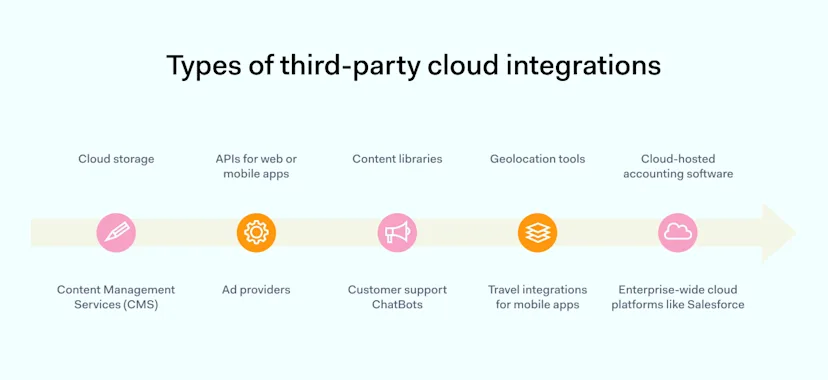
There are many types of third-party cloud integrations. Examples include:
Cloud data storage such as Amazon Web Services (AWS)
Content Management Services (CMS) like Drupal or WordPress
APIs for web or mobile apps
Ad providers like Google Ads
Content libraries for images or product listings
Customer support ChatBots like PipeDrive
Geolocation tools like Google Maps
Travel integrations for mobile apps such as Uber
Cloud-hosted accounting software like Xero
Enterprise-wide cloud platforms like Salesforce
The diagram above shows a typical third-party or Software-as-a-Service (SaaS) cloud integration. Most integrations require regular connectivity between third-party vendors and your organization’s network. This makes managing third-party cloud resource access a critical task for cloud architects.
Incorrect access processes can create openings for cyber attackers. Admins must always secure third-party vendor access. But at the same time, network managers must allow access for partners to carry out their assigned duties. Striking this balance is not easy, and careful planning is essential.
The need for third-party resources in today’s cloud infrastructure
Until recently, many organizations maintained on-premises networks. Workstations or local servers stored apps and data. Organizations purchased licenses to use software developed by others. And that’s where their relationships with third parties ended.
Cloud computing has changed this picture. Software and services developed and managed by third-party vendors are widely used for accounting, customer relationship management, data hosting, payment APIs, and staff collaboration. In-house operations have receded into the background.
Companies tend to incur higher costs when they build websites or virtualized networks on their own. Third-party vendors provide the necessary skills and products.
Vendors provide cross-app support—for instance, Slack links to Google Drive and Gmail. Gmail connects with other cloud integrations like Salesforce. Cloud setups like this involve many access points where third parties interface with your network resources.
Benefits and challenges of third-party integration
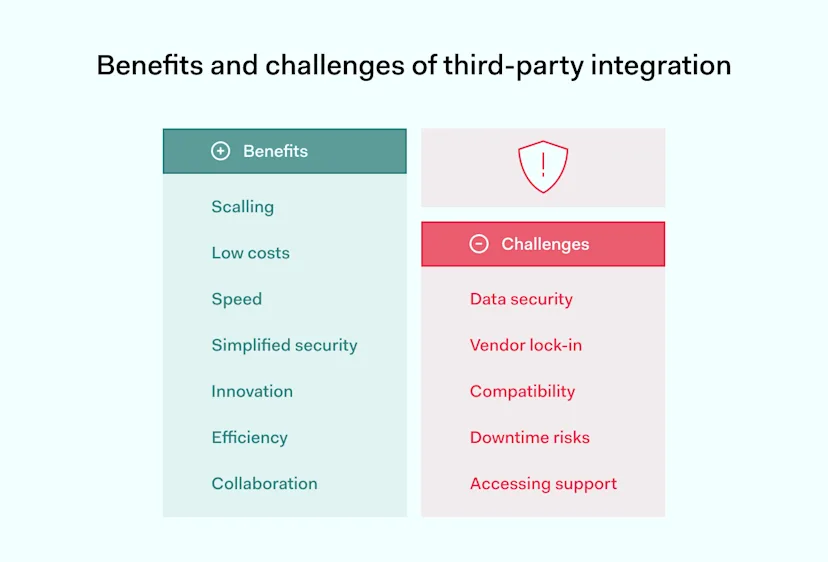
Outsourcing cloud services to third-party vendors has pros and cons. Third parties are not a magic bullet that meets every need of modern businesses. Businesses must consider benefits and challenges when commissioning third-party cloud services.
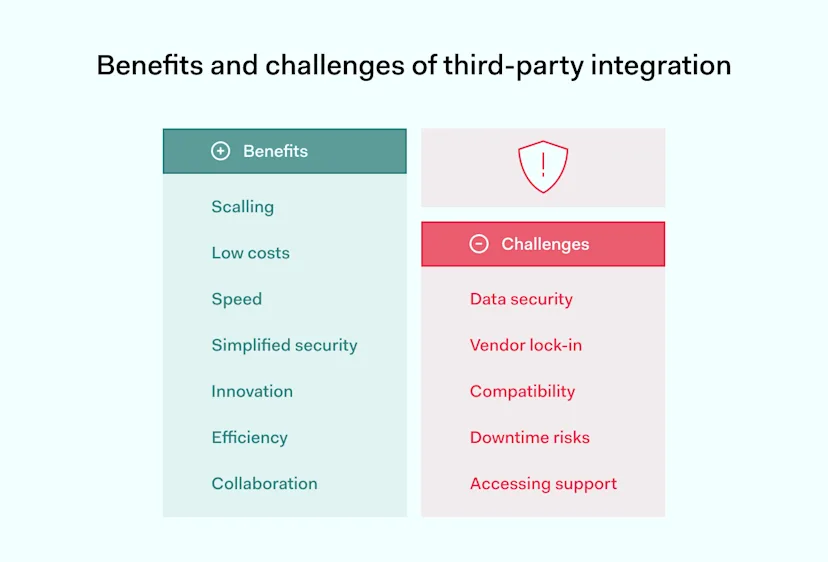
Benefits
Scaling – third-party cloud vendors make it much easier to grow cloud-based enterprises. Companies can increase workloads, knowing cloud providers can handle increased data throughput. There is no need to make huge investments when products succeed. Cloud assets scale smoothly as sales and operations expand.
Low costs – traditional software licenses demand high up-front fees or subscriptions. Up-front billing still applies to many cloud providers. But cloud services also operate pay-as-you-go models where companies pay for the resources they use. This kind of billing-per-usage can result in cost savings.
Speed – many organizations use SaaS tools to expand operations quickly. Time-to-market decreases. And companies can rapidly expand into new geographic markets. They do not need to set up regional offices. Virtualized systems are available almost instantly.
Simplified security – high-quality third-party vendors put in place robust security controls. They meet regulatory standards and secure client data. This reduces the workload on IT managers. Users simply access SaaS resources, and third parties manage security needs.
Innovation – third parties have technical capabilities that clients lack. For instance, they carry out complex data analysis and machine learning to understand the behavior of eCommerce customers. Companies can embrace new technologies without running internal R&D departments.
Efficiency – third parties let companies focus on their critical missions. Organizations don’t need to waste time creating solutions that can be purchased off the shelf. This allows clients to become leaner and more competitive.
Collaboration – cloud services like Slack or Zoom simplify employee communication, allowing information to flow freely. Remote work teams can collaborate on projects regardless of location. Managers can easily monitor project performance.
Challenges
Data security – third parties handle large amounts of private business data. This could include customer financial information or Protected Health Information (PHI). This creates a data breach risk if third-party vendors operate weak private data management and security practices. Ensuring each third party complies with security regulations is challenging. And every extra third party adds another potential data leak source.
Vendor lock-in – vendor lock-in creates problems when you wish to switch to a more capable provider, when business strategy changes, or when the vendor you committed to for years introduces new terms of services or new business models that do not work with your company’s vision.
Compatibility – third-party suppliers must work seamlessly with existing cloud assets. Cloud architects must plan data flows and test apps to ensure smooth operations. This requires expertise that third parties may not possess.
Regulatory risks – using third parties can sometimes contravene industry regulations. For example, healthcare organizations must carefully check third parties to ensure compliance with HIPAA.
Customer support – some cloud service providers offer excellent client support. Others are less efficient. Clients may lack support to handle operational or security issues. They may not possess the internal expertise needed to find solutions.
Common misconceptions about using third-party resources
Using third parties carries significant benefits. But the list of challenges above shows that there is a downside. Many of the potential problems are related to managing:
Methods of third-party access
How much private data is exposed to third parties during integration
Busting these myths about third parties is vital to make the best use of cloud resources. Let’s look at some common issues that confuse companies when they enlist third-party cloud vendors.
Myth #1: Third-party solutions handle every security issue
Cloud security is a shared responsibility. Under the shared responsibility model, third-party providers protect their applications and infrastructure. Vendors must ensure their products are properly configured and safe to use.
Network owners must secure their own cloud platforms and data. Companies need to apply robust access controls to external partners. And IT teams must audit third parties to detect security vulnerabilities.
Myth #2: Third parties always prioritize data privacy
The same rules apply to data privacy as to security. Third parties often have strict privacy policies. These partners don’t extract customer data. They secure private data according to the industry’s best practices. But this isn’t always the case. Check the fine print and read privacy policies before installing any third-party services.
Myth #3: Access controls apply to internal assets, not third-party resources
Companies need to secure their networks with comprehensive access controls. However, access controls should also limit what users can do when accessing third-party resources.
Assigning excessive privileges to users can lead to security incidents. For example, users might share private data with unauthorized Slack users. Controls should apply wherever users can compromise data security. And that includes third-party apps.
Best practices for optimizing access to third-party resources
Organizations need streamlined cloud strategies to achieve optimal performance and adaptability. With that in mind, here are some concise best practices to allow secure third-party resource access.
1. Carry out third-party risk assessments
Assess third parties before commissioning services. Check their security and privacy policies and research their reliability and customer support. And only choose partners that comply with relevant regulations.
Some third parties pose a limited security risk as they process relatively little sensitive data. For example, website ad providers are unlikely to access customer data. However, SaaS accountancy tools could create a data breach risk.
2. Implement privileged access management (PAM) for third parties
Privileged access management systems create a secure interface between third parties and cloud deployments.
PAM avoids direct connections between third parties and network assets. The system screens network requests. It limits what third parties can do and makes damaging cyber-attacks less likely.
Multi-factor authentication (MFA) portals request more than one unique ID before granting access.
Access controls implement Zero Trust Network Access (ZTNA) principles. Users only have access to resources they need and nothing more.
Just-in-time controls provide third parties with access for specified periods and revoke access after that period elapses
PAM integrates with password management systems to enforce strong password policies.
3. Use NordLayer’s data encryption solutions
Always encrypt sensitive data, both at rest and in transit. NordLayer’s security tools encrypt data flows from and to third parties. Users can shield network traffic with our business VPN and keep traffic away from malicious actors.
4. Monitor third-party vendor security
Companies should remain aware of third-party security issues. Subscribe to alerts and vendor notifications. And integrate third-party monitoring into security information and event management (SIEM) solutions.
5. Audit third-party performance
Assess all third-party providers annually. Check for access control violations and security issues—track cloud resource and license usage to detect inefficiencies.
6. Have an exit plan for every third party
Third parties can go out of business or lose customer trust. And when that happens, customers must be prepared to change partners.
For example, you might currently use a certain VPN to protect cloud resources. But if that relationship fails, it makes sense to have a plan to transition to NordLayer or other alternatives.
Plan to migrate data and user activity smoothly. Design contracts to activate the exit plan if partners fail to meet security requirements.
Using VPNs to allow third-party cloud access
As we mentioned earlier, VPNs are a way to engineer secure third-party connections. However, traditional VPNs are a poor fit for third-party cloud access systems.
VPN users may experience slow connection speeds. And slow speeds compromise the performance of third-party services. This can negate the benefits of third-party integrations.
There are security issues on the client side. VPNs grant broad access to network resources. Firewalls are more precise, operating fine-grained access controls. Despite these issues, companies can use virtual private networks to secure cloud vendor connections.
Cloud VPNs represent a potential solution. They encrypt traffic passing between private and public clouds. Also, they create virtualized encrypted networks that protect data moving between SaaS servers and companies.
For example, Salesforce Private Connect defends traffic moving between Salesforce integrations and AWS servers. NordLayer’s cybersecurity solutions offer comprehensive protection for remote teams and cloud deployments.
Cloud VPNs combined with PAM and firewalls provide a robust level of security for third-party integrations. Companies can ensure access while limiting third-party privileges. And they can encrypt data flows in the cloud, hiding the content from malicious actors.
Future trends in third-party resource access
Cloud computing is growing rapidly. In 2023, the market for public cloud services was projected to grow by 21.7%. Companies continue to shift from fixed on-premises setups to agile cloud deployments. And they are embracing third-party cloud integrations on a massive scale.
As a result, third-party resource access will expand and evolve. For instance, Identity-as-a-Service (IDaaS) is becoming mainstream. IDaaS is a cloud-native service that blends the benefits of PAM and VPN tools.
IDaaS provides cloud-native authentication tools that include MFA and single sign-on (SSO) components. Clients can set access policies to implement Zero Trust policies. Tools like Security Assertion Markup Language (SAML) protect user credentials. Self-service portals allow users to change credentials without referring to company IT teams. And data gathering systems make SaaS audits more precise.
In the future, we can expect similar holistic cloud solutions. Tools like IDaaS will allow companies to control access across hybrid clouds. And they will make managing large communities of SaaS vendors easier.
Emerging technologies and their impact
New technologies are reshaping the way third parties connect to client networks. And these technologies go beyond traditional access management.
Machine Learning and AI will make threat detection and third-party monitoring more precise. Behavioral analysis will track suspicious access patterns and deliver instant alerts. Companies will also be able to carry out AI-assisted risk assessments. And they will assess third-party performance in real-time.
Blockchain technology may also contribute to third-party security. Blockchain ledgers can record access requests in tamper-proof formats. This will enhance the integrity of audit trails. And it will make the relationship between clients and third parties more transparent.
Looking forward: how the landscape might change in the next 5 years
Cloud architects should always be a step ahead of potential threats. So, what should we expect in the next few years?
The trend toward hybrid clouds will continue. Companies want easy-to-scale public clouds. They want the speed and flexibility provided by third-party integrations. But they also want secure zones for data storage.
Cloud users will need flexible solutions. They must protect critical data on private clouds while allowing third-party access to the public cloud.
Cloud security threats aren’t going away. Privileged access management will remain a critical security task for cloud engineers. The next 5 years will be an opportunity for companies that adopt secure cloud architecture. However, companies that stick with legacy technologies will struggle.
Conclusion: manage cloud third-party integrations with NordLayer
NordLayer can help you secure third-party resources in the cloud and on-premises. Our security tools enable clients to protect critical data from eavesdropping or leaks whilst browsing on insecure networks. Our virtual private gateways make it much easier to integrate external resources smoothly. Here’s what we offer our clients:
Cloud VPN that protects data and apps. Encrypted tunnels shield north-south traffic. Additional checks and traffic filtering take place in the cloud.
Simplified identity management. NordLayer integrates with industry-leading SSO and SCIM providers to ensure users can authenticate easily and retain access levels and privileges defined in your AD.
Allowlisting tools add extra protection. Set lists of trusted users for the critical resources. Create secure zones for sensitive data. And apply looser controls for less risky traffic flows.
Cloud firewall (FWaaS). Cloud firewall takes traditional firewall protection into the cloud. Companies can use strict firewall rules to set exceptions for third parties, enabling secure access to private data on a very granular level.
Zero Trust solution. NordLayer implements Zero Trust principles for all cloud assets. Users must verify their identity before accessing internal network resources. And they only have access to assets they need, nothing more.
Find the right third-party access solution for your cloud deployment. Contact NordLayer today and discuss your options with our security experts.