
All-In-One Solution to Manage
and Secure Workspace
Fast Deployment
- Pre-configured security policies
- Over 1000+ application integration templates
- Ready-to-use within minutes
Zero-Trust Network Architecture

Cutting-edge security measures to safeguard your business by focusing on both user safety and experience
Comprehensive user activities monitoring
Real-time security posture management
Dynamic control to devices and networks
Reduced Management Complexity

All-in-one solution across multiple devices, identities and networks, reducing management effort for all components
One-stop shop for IT management
Centralized platform for security alerts
Easy to configure and get started
Empowering Organizations
Around the World
Identity and Access Management
Integrating directory/IdP services, user role management, access authorization, and account security capabilities into a centralized platform for better identity risk protection.


Centralized Identity Management
Together with the directory services, SealSuite also consolidates data from multiple sources and IdPs (such as Windows AD, LDAP, Workday, etc.) to streamline identity management operations with centralized management platform and strong third-party integration capability.
Comprehensive User Role Management
SealSuite supports segregation among full-time employees, outsourcing partners, part-time contractors, and other identity categories based on departments, personnel, and roles. Static and dynamic role classification facilitates the management of application access, network connections, and other permissions, enabling least privileged access based on identity.


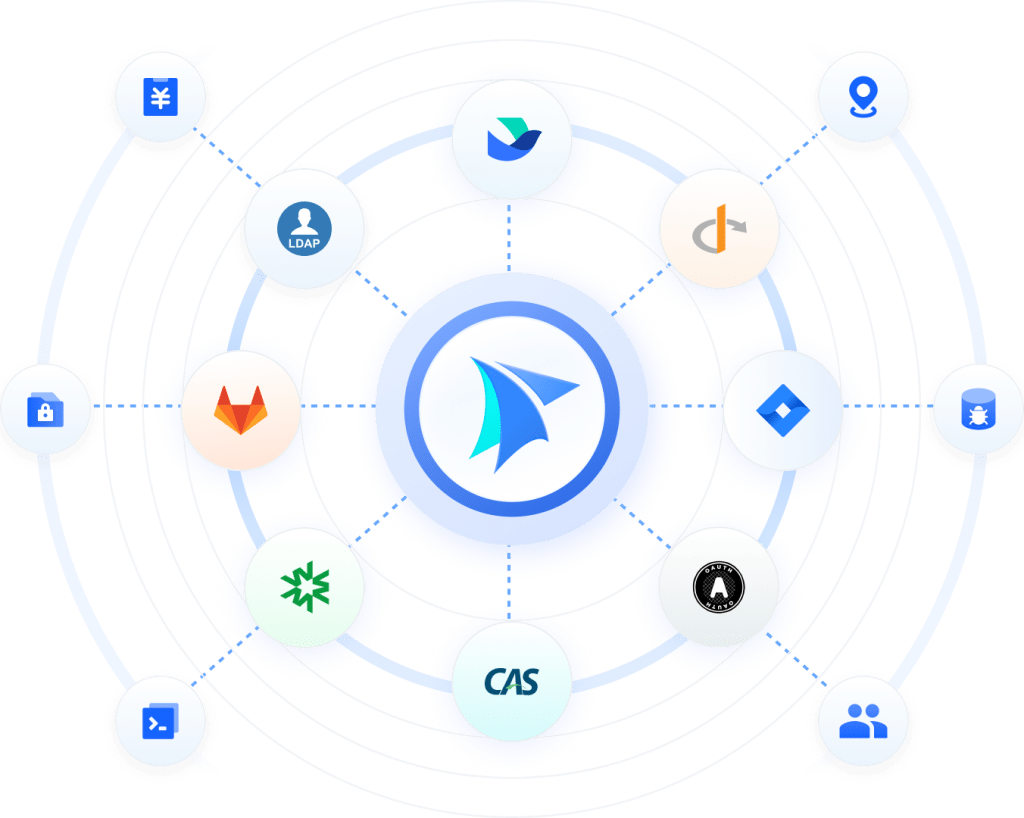
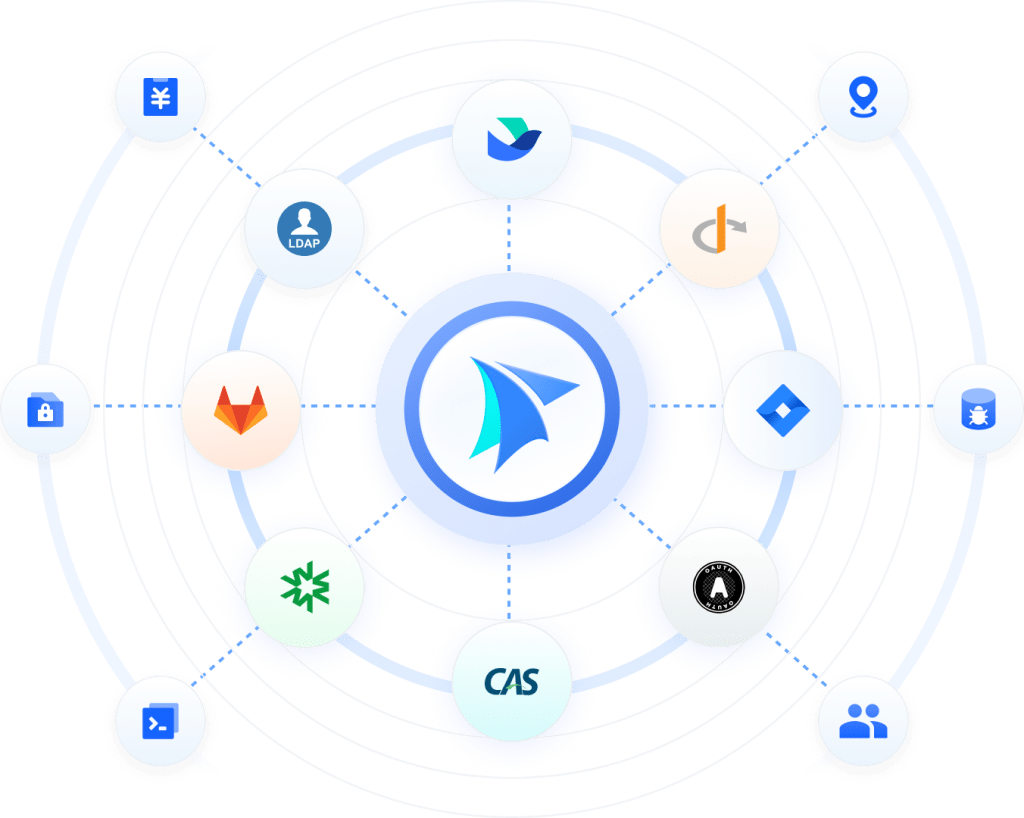
Single sign-on (SSO)
SealSuite offers pre-defined and continuously maintained SSO application marketplace functionality, enabling businesses to reduce onboarding costs with plug-and-play convenience. Additionally, the platform provides standard protocols such as OAuth 2.0, CAS 2.0, SAML, OIDC, accompanied by customized expert support.
Account Authorization and Security
When connecting to the network, or accessing applications, SealSuite enables multi-factor authentication (MFA) to verify employees’ identities, safeguarding accounts against credential theft and fraudulent risks along with other measures such as weak password detection and anti-brute force policies, further enhancing account security.

Endpoint Management and Security


Corporate Digital Asset Management
IT administrators frequently encounter difficulties in gaining transparent insights into user access to both devices and applications. SealSuite offers seamless integration and representation with network details, identity attributes, and behavioral patterns.
Comprehensive Presentation of Security Posture


Customized Risk Remediation Approaches
Network Management and Security
Managing all aspects of office networks and connectivity with solutions such as Virtual Private Network (VPN), Software Defined Network (SD-WAN), and Wi-Fi.


Innovative VPN Management
Leveraging network resource segmentation and identity management capabilities, SealSuite offers enhanced access control capability based on departments, individuals, and dynamic roles. All the traffic is encrypted through dual proxy tunnel (full mode/split mode).
Software-defined wide area network (SD-WAN)
Using virtualized vCPE components, SealSuite enables global SD-WAN interoperability within minutes, facilitating efficient network connections covering headquarters, branches, and data centers.
Additionally, it offers operational analytics capabilities of network bandwidth and routing status to enable high-quality, cost-effective multi-cloud networking solutions.


Wi-Fi and wired network management
SealSuite addresses network access needs from employees and visitors with permission management and multiple authentication methods. Additionally, SealSuite supports and manages numerous switches and routers to ensure seamless integration through proprietary RADIUS technology.
SaaS Protection
Protecting organization’s valuable assets and data in the cloud environment by analyzing user behaviors, device interactions, and access patterns to cloud applications, and offering robust security measures to mitigate potential threats


Secure Application Gateway
SealSuite’s secure application gateway acts as an intermediary server between users and the internet, effectively concealing the true network addresses of users. By rerouting requests through the proxy server, sensitive data remains protected from prying eyes, bolstering confidentiality and integrity. Moreover, reverse proxy feature stands as a formidable barrier against external threats by intercepting incoming traffic before it reaches the internal network.
Application Discovery
SealSuite offers enhanced visibility into employee activities and behaviors through in-depth analysis of user access and utilization of cloud applications. By providing comprehensive insights into uploading and downloading traffic across various applications, SealSuite empowers organizations to implement tailored control measures to fortify their environment against potential threats.


Application Control
Through the establishment of tailored access control policies for cloud applications, organizations can regulate user access by selectively blocking traffic to designated websites and scrutinizing content transmissions to and from user devices.
Additionally, the implementation of data loss prevention (DLP) policies enables organizations to protect confidential data by preventing unauthorized access or transmission, thereby enhancing overall security and compliance efforts within their cloud environment.
Leading the Next-Generation Workforce IT Management
Leveraging the IT infrastructure capabilities and management experience of industry pioneers, SealSuite is pioneering the development of a secure and convenient next-generation digital corporate environment.

SealSuite’s All-in-One solution represents a more
advanced methodology in IT management
It inherently integrates the core IT management systems of identity, network, and endpoints. Without any modifications to the current network architecture, this lightweight solution helps safeguarding existing IT investments by

Secured Access
Enhancing employee identity, authorization governance and least privileged access

Advanced Network Control
Controlling office network access based on user profiles and device conditions

Enhanced Endpoint Security
Improving endpoint asset management, and endpoint security capabilities

Identity authentication and “passwordless” practice
In response to the growing need for enhanced security and user convenience, SealSuite integrates advanced identity authentication methods that go beyond traditional password-based systems.
By leveraging biometric authentication, multi-factor authentication (MFA), or other secure alternatives, we enable a “passwordless” login experience. This approach not only strengthens security by reducing reliance on easily compromised passwords but also enhances user experience by streamlining the authentication process.
Cloud and On-premise Integration
SealSuite seamlessly integrates with various cloud-based and on-premises data center services through a single platform, enabling flexible permission management and dynamic access control at both the network and application layers. Utilizing distributed deployment of Virtual Private Network (VPN) and RADIUS resource nodes, it seamlessly covers a wide range of business applications, providing employees with a unified and secure application login experience.


Office Network Access for Office Branches and Remote Locations
A comprehensive and systematic office network management solution that unifies employee Wi-Fi and Virtual Private Network (VPN) permissions. Combined with endpoint asset management and security detection capabilities, it assists enterprises in achieving comprehensive office network access across all s
Digital transformation of IT policy implementation
Drawing upon the security management practices and insights of industry pioneers, we integrate locking screen passwords, security software installation, and other management requirements into the security baseline. In instances where corporate devices do not meet the baseline criteria, permissions are downgraded or restricted, addressing challenges in implementing management systems effectively.

Reducing Attack through the Zero Trust Solution
Adhering to the principles of zero trust, SealSuite designs secure access rules based on employee roles. Through continuous trust assessment, dynamic access control, multi-factor authentication, traffic decryption and encryption, and audit logs, we effectively mitigate security risks posed by untrusted individuals/devices accessing the network indiscriminately.

Never Trust, Always Verify
With the rise of remote work and cloud applications, enterprise network environments have become increasingly complex. In response, the zero trust principle of continuous verification and dynamic authorization has emerged as a new security paradigm.

Secure Network
Access
Covering Virtual Private Networks (VPN), Wi-Fi, and wired networks, we implement dynamic access control to reduce exposure to security risks in all aspects of networks.

Protecting Various
Business Systems
Whether deployed in public clouds, private clouds, or on-premises data centers, our solution enables seamless and secure access from anywhere.

Balancing Security
and User Experience
With one-click access to internal networks and applications, SealSuite enhances employee office experience while defaulting to secure verification.

Comprehensive Identity-Centric Approach
Zero trust represents a continuously evolving network security paradigm, transforming the traditional network-based trust model into an identity-based trust model. Through identity governance, SealSuite connects comprehensive identity-centricity of entities such as devices, users, and applications and establishes a new security boundary for office networks.
Secure Business Access
Both networks and applications are critical business resources that enterprises need to protect, especially in today’s environment where access requests can originate from any time and place. To mitigate risks and prevent attacks or misuse of business resources, enterprises must implement measures such as least privilege access permissions, encrypted traffic, enforcing identity authentication, and conducting device security checks. These practices help to reduce exposure and safeguard business resources effectively.


Continuous Risk Assessment
Based on identity as the foundation of trust, SealSuite ensures that all access entities (users, devices, environments, etc.) undergo comprehensive and continuous trust verification. This includes multi-factor authentication, baseline checks, endpoint threat detection, data leak detection, and more, enabling real-time insight into internal network security risks.
Dynamic Access Control
By leveraging proprietary engines that respond to enterprise security management policies, SealSuite automates the downgrading or prohibition of network connections and application access permissions for risky devices, thereby preventing the spread of threats. Event alerts and log analysis capabilities aid in auditing the effectiveness of policies, ensuring compliance with regulatory requirements.

Safeguarding your company’s confidential data
Offering comprehensive auditing and control capabilities covering the entire data lifecycle, from collection to processing to storage on corporate networks and devices

Data security is paramount for businesses navigating the digital landscape.
With the increasing digitization of operations and the adoption of cloud storage solutions—be it public, private, or hybrid—ensuring the safeguarding of data through robust measures is imperative to maintain uninterrupted business continuity. SealSuite facilitates this endeavor by offering:

Comprehensive User
Behavior Analytics
Comprehensive capabilities to unveil behavioral risks, enabling the discovery of data and traffic traversing networks and devices.

Advanced Policy
Management
Advanced alert forecasting mechanisms to promptly identify and prevent data breaches, ensuring proactive mitigation.

Enhanced Data
Monitoring
Enhanced monitoring and control of confidential data movement and storage by consolidating identity, networks, and devices, thereby bolstering security measures.

Precise and Efficient Data Discovery Capability
SealSuite maps out sensitive data assets and tracks the entire lifecycle of file and content sharing internally and externally. Data leakage identification covers over 70 file formats such as text, images, code, compressed file, etc. It provides real-time monitoring capability for sensitive operations including but not limited to encryption, modification and sharing outside of the organization of such files.
Robust Security Policy Setting and Risk Alerting Mechanism
SealSuite empowers organizations to establish and enforce stringent security policies tailored to their specific needs, ensuring protection against evolving threats. By implementing advanced risk alerting mechanisms based on various dimensions, such as device, data sensitivity, channels, and file types, organizations can proactively identify and respond to potential security breaches or vulnerabilities in real-time.


Full-fledged Disposition for Identity, Devices and Network
By integrating identity, network, and endpoint control capabilities, we offer enterprises a true one-stop security baseline for data, covering individuals, networks, and endpoints. All connected devices can be linked to user identities, providing end-to-end data circulation records. Through identity authentication, unknown individuals are prevented from accessing highly sensitive data.

All-In-One Solution to Manage
and Secure Workspace
Fast Deployment
- Pre-configured security policies
- Over 1000+ application integration templates
- Ready-to-use within minutes
Zero-Trust Network Architecture

Cutting-edge security measures to safeguard your business by focusing on both user safety and experience
Comprehensive user activities monitoring
Real-time security posture management
Dynamic control to devices and networks
Reduced Management Complexity

All-in-one solution across multiple devices, identities and networks, reducing management effort for all components
One-stop shop for IT management
Centralized platform for security alerts
Easy to configure and get started
Empowering Organizations
Around the World
Identity and Access Management
Integrating directory/IdP services, user role management, access authorization, and account security capabilities into a centralized platform for better identity risk protection.


Centralized Identity Management
Together with the directory services, SealSuite also consolidates data from multiple sources and IdPs (such as Windows AD, LDAP, Workday, etc.) to streamline identity management operations with centralized management platform and strong third-party integration capability.
Comprehensive User Role Management
SealSuite supports segregation among full-time employees, outsourcing partners, part-time contractors, and other identity categories based on departments, personnel, and roles. Static and dynamic role classification facilitates the management of application access, network connections, and other permissions, enabling least privileged access based on identity.


Single sign-on (SSO)
SealSuite offers pre-defined and continuously maintained SSO application marketplace functionality, enabling businesses to reduce onboarding costs with plug-and-play convenience. Additionally, the platform provides standard protocols such as OAuth 2.0, CAS 2.0, SAML, OIDC, accompanied by customized expert support.
Account Authorization and Security
When connecting to the network, or accessing applications, SealSuite enables multi-factor authentication (MFA) to verify employees’ identities, safeguarding accounts against credential theft and fraudulent risks along with other measures such as weak password detection and anti-brute force policies, further enhancing account security.

Endpoint Management and Security


Corporate Digital Asset Management
IT administrators frequently encounter difficulties in gaining transparent insights into user access to both devices and applications. SealSuite offers seamless integration and representation with network details, identity attributes, and behavioral patterns.
Comprehensive Presentation of Security Posture


Customized Risk Remediation Approaches
Network Management and Security
Managing all aspects of office networks and connectivity with solutions such as Virtual Private Network (VPN), Software Defined Network (SD-WAN), and Wi-Fi.


Innovative VPN Management
Leveraging network resource segmentation and identity management capabilities, SealSuite offers enhanced access control capability based on departments, individuals, and dynamic roles. All the traffic is encrypted through dual proxy tunnel (full mode/split mode).
Software-defined wide area network (SD-WAN)
Using virtualized vCPE components, SealSuite enables global SD-WAN interoperability within minutes, facilitating efficient network connections covering headquarters, branches, and data centers.
Additionally, it offers operational analytics capabilities of network bandwidth and routing status to enable high-quality, cost-effective multi-cloud networking solutions.


Wi-Fi and wired network management
SealSuite addresses network access needs from employees and visitors with permission management and multiple authentication methods. Additionally, SealSuite supports and manages numerous switches and routers to ensure seamless integration through proprietary RADIUS technology.
SaaS Protection
Protecting organization’s valuable assets and data in the cloud environment by analyzing user behaviors, device interactions, and access patterns to cloud applications, and offering robust security measures to mitigate potential threats


Secure Application Gateway
SealSuite’s secure application gateway acts as an intermediary server between users and the internet, effectively concealing the true network addresses of users. By rerouting requests through the proxy server, sensitive data remains protected from prying eyes, bolstering confidentiality and integrity. Moreover, reverse proxy feature stands as a formidable barrier against external threats by intercepting incoming traffic before it reaches the internal network.
Application Discovery
SealSuite offers enhanced visibility into employee activities and behaviors through in-depth analysis of user access and utilization of cloud applications. By providing comprehensive insights into uploading and downloading traffic across various applications, SealSuite empowers organizations to implement tailored control measures to fortify their environment against potential threats.


Application Control
Through the establishment of tailored access control policies for cloud applications, organizations can regulate user access by selectively blocking traffic to designated websites and scrutinizing content transmissions to and from user devices.
Additionally, the implementation of data loss prevention (DLP) policies enables organizations to protect confidential data by preventing unauthorized access or transmission, thereby enhancing overall security and compliance efforts within their cloud environment.
Leading the Next-Generation Workforce IT Management
Leveraging the IT infrastructure capabilities and management experience of industry pioneers, SealSuite is pioneering the development of a secure and convenient next-generation digital corporate environment.

SealSuite’s All-in-One solution represents a more
advanced methodology in IT management
It inherently integrates the core IT management systems of identity, network, and endpoints. Without any modifications to the current network architecture, this lightweight solution helps safeguarding existing IT investments by

Secured Access
Enhancing employee identity, authorization governance and least privileged access

Advanced Network Control
Controlling office network access based on user profiles and device conditions

Enhanced Endpoint Security
Improving endpoint asset management, and endpoint security capabilities

Identity authentication and “passwordless” practice
In response to the growing need for enhanced security and user convenience, SealSuite integrates advanced identity authentication methods that go beyond traditional password-based systems.
By leveraging biometric authentication, multi-factor authentication (MFA), or other secure alternatives, we enable a “passwordless” login experience. This approach not only strengthens security by reducing reliance on easily compromised passwords but also enhances user experience by streamlining the authentication process.
Cloud and On-premise Integration
SealSuite seamlessly integrates with various cloud-based and on-premises data center services through a single platform, enabling flexible permission management and dynamic access control at both the network and application layers. Utilizing distributed deployment of Virtual Private Network (VPN) and RADIUS resource nodes, it seamlessly covers a wide range of business applications, providing employees with a unified and secure application login experience.


Office Network Access for Office Branches and Remote Locations
A comprehensive and systematic office network management solution that unifies employee Wi-Fi and Virtual Private Network (VPN) permissions. Combined with endpoint asset management and security detection capabilities, it assists enterprises in achieving comprehensive office network access across all s
Digital transformation of IT policy implementation
Drawing upon the security management practices and insights of industry pioneers, we integrate locking screen passwords, security software installation, and other management requirements into the security baseline. In instances where corporate devices do not meet the baseline criteria, permissions are downgraded or restricted, addressing challenges in implementing management systems effectively.

Reducing Attack through the Zero Trust Solution
Adhering to the principles of zero trust, SealSuite designs secure access rules based on employee roles. Through continuous trust assessment, dynamic access control, multi-factor authentication, traffic decryption and encryption, and audit logs, we effectively mitigate security risks posed by untrusted individuals/devices accessing the network indiscriminately.

Never Trust, Always Verify
With the rise of remote work and cloud applications, enterprise network environments have become increasingly complex. In response, the zero trust principle of continuous verification and dynamic authorization has emerged as a new security paradigm.

Secure Network
Access
Covering Virtual Private Networks (VPN), Wi-Fi, and wired networks, we implement dynamic access control to reduce exposure to security risks in all aspects of networks.

Protecting Various
Business Systems
Whether deployed in public clouds, private clouds, or on-premises data centers, our solution enables seamless and secure access from anywhere.

Balancing Security
and User Experience
With one-click access to internal networks and applications, SealSuite enhances employee office experience while defaulting to secure verification.

Comprehensive Identity-Centric Approach
Zero trust represents a continuously evolving network security paradigm, transforming the traditional network-based trust model into an identity-based trust model. Through identity governance, SealSuite connects comprehensive identity-centricity of entities such as devices, users, and applications and establishes a new security boundary for office networks.
Secure Business Access
Both networks and applications are critical business resources that enterprises need to protect, especially in today’s environment where access requests can originate from any time and place. To mitigate risks and prevent attacks or misuse of business resources, enterprises must implement measures such as least privilege access permissions, encrypted traffic, enforcing identity authentication, and conducting device security checks. These practices help to reduce exposure and safeguard business resources effectively.


Continuous Risk Assessment
Based on identity as the foundation of trust, SealSuite ensures that all access entities (users, devices, environments, etc.) undergo comprehensive and continuous trust verification. This includes multi-factor authentication, baseline checks, endpoint threat detection, data leak detection, and more, enabling real-time insight into internal network security risks.
Dynamic Access Control
By leveraging proprietary engines that respond to enterprise security management policies, SealSuite automates the downgrading or prohibition of network connections and application access permissions for risky devices, thereby preventing the spread of threats. Event alerts and log analysis capabilities aid in auditing the effectiveness of policies, ensuring compliance with regulatory requirements.

Safeguarding your company’s confidential data
Offering comprehensive auditing and control capabilities covering the entire data lifecycle, from collection to processing to storage on corporate networks and devices

Data security is paramount for businesses navigating the digital landscape.
With the increasing digitization of operations and the adoption of cloud storage solutions—be it public, private, or hybrid—ensuring the safeguarding of data through robust measures is imperative to maintain uninterrupted business continuity. SealSuite facilitates this endeavor by offering:

Comprehensive User
Behavior Analytics
Comprehensive capabilities to unveil behavioral risks, enabling the discovery of data and traffic traversing networks and devices.

Advanced Policy
Management
Advanced alert forecasting mechanisms to promptly identify and prevent data breaches, ensuring proactive mitigation.

Enhanced Data
Monitoring
Enhanced monitoring and control of confidential data movement and storage by consolidating identity, networks, and devices, thereby bolstering security measures.

Precise and Efficient Data Discovery Capability
SealSuite maps out sensitive data assets and tracks the entire lifecycle of file and content sharing internally and externally. Data leakage identification covers over 70 file formats such as text, images, code, compressed file, etc. It provides real-time monitoring capability for sensitive operations including but not limited to encryption, modification and sharing outside of the organization of such files.
Robust Security Policy Setting and Risk Alerting Mechanism
SealSuite empowers organizations to establish and enforce stringent security policies tailored to their specific needs, ensuring protection against evolving threats. By implementing advanced risk alerting mechanisms based on various dimensions, such as device, data sensitivity, channels, and file types, organizations can proactively identify and respond to potential security breaches or vulnerabilities in real-time.


Full-fledged Disposition for Identity, Devices and Network
By integrating identity, network, and endpoint control capabilities, we offer enterprises a true one-stop security baseline for data, covering individuals, networks, and endpoints. All connected devices can be linked to user identities, providing end-to-end data circulation records. Through identity authentication, unknown individuals are prevented from accessing highly sensitive data.
產品查詢
電話:(852) 2893 8860
E-mail:sales@version-2.com.hk
產品查詢
電話:(852) 2893 8860
E-mail:sales@version-2.com.hk




















