In “The Code Conundrum”, A New Software Hero Emerges To Take Aim at Defeating the Complexity of Container Management and Deliver Stability to Modern IT Edge Environments
INDIANAPOLIS – May 29, 2024 – Scale Computing, the market leader in edge computing, virtualization, and hyperconverged solutions, today announced the publication of the second issue of its EdgeSlayer comic book series. In “The Code Conundrum”, our hero is a software developer named Amy (a reference to AIME for Autonomous Infrastructure Management Engine) who must implement continuous integration and containerized deployment strategies to defeat a rogue AI that’s wreaking havoc on the fictional city of Technopolis. Can Amy conquer the unruly forces with container deployment and restore stability to the edge relying on little else than her smarts and DevOps prowess?
While the characters and the plot of the latest EdgeSlayer comic book might be fantastical, the story’s premise is squarely rooted in the realities of today’s complex edge environments where managing, customizing, and integrating software containers has become an essential yet increasingly challenging task. Employing the metaphor of a high-stakes battle to represent the ongoing struggle of IT professionals, the comic depicts our valiant heroes confronting a relentless enemy: a tangled web of application deployment complexities, ever-evolving cybersecurity threats, and the constant pressure to maintain application uptime.
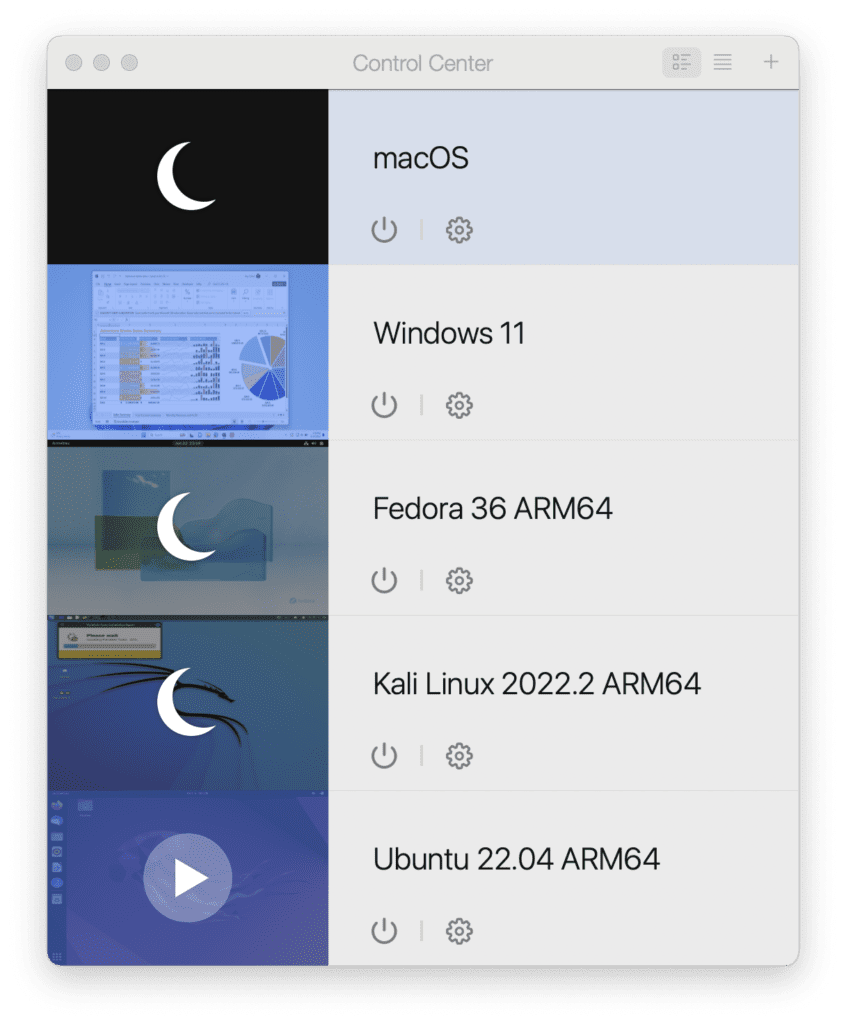
This complexity largely stems from the need for additional tools such as Kubernetes, to manage sprawling container clusters. Kubernetes, while powerful, adds another layer of configuration and learning for already overburdened IT teams. The EdgeSlayer story highlights this struggle, but also offers a path forward. By running containers directly on VMs within SC//HyperCore, redundancy is automatically achieved at the infrastructure level, enabling the real-world heroes of IT to spend less time troubleshooting complex container orchestration and more time focused on strategic initiatives that drive business value.
“We’re seeing more and more customers struggling to deploy containers in a consistent and programmatic fashion at the network edge, which points to a growing need for automated solutions,” said Jeff Ready, CEO and co-founder of Scale Computing. “This burden often falls on the shoulders of IT administrators, the unsung heroes who work tirelessly behind the scenes to keep everything running smoothly, often without the recognition they deserve. Our EdgeSlayer comics are our creative way of celebrating these individuals by showcasing their challenges and triumphs through a superhero lens.”
This new edition of the EdgeSlayer comic can be downloaded here in PDF format for free.
About Scale Computing
Scale Computing is a leader in edge computing, virtualization, and hyperconverged solutions. Using patented HyperCore™ technology, Scale Computing Platform automatically identifies, mitigates, and corrects infrastructure problems in real-time, enabling applications to achieve maximum uptime, even when local IT resources and staff are scarce. Edge Computing is the fastest growing area of IT infrastructure, and industry analysts have named Scale Computing an outperformer and leader in the space, including being named the #1 edge computing vendor by CRN. Scale Computing’s products are sold by thousands of value-added resellers, integrators, and service providers worldwide. When ease-of-use, high availability, and TCO matter, Scale Computing Platform is the ideal infrastructure platform. Read what our customers have to say on Gartner Peer Insights, G2 and TrustRadius.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Scale Computing
Scale Computing is a leader in edge computing, virtualization, and hyperconverged solutions. Scale Computing HC3 software eliminates the need for traditional virtualization software, disaster recovery software, servers, and shared storage, replacing these with a fully integrated, highly available system for running applications. Using patented HyperCore™ technology, the HC3 self-healing platform automatically identifies, mitigates, and corrects infrastructure problems in real-time, enabling applications to achieve maximum uptime. When ease-of-use, high availability, and TCO matter, Scale Computing HC3 is the ideal infrastructure platform. Read what our customers have to say on Gartner Peer Insights, Spiceworks, TechValidate and TrustRadius.










)