How has Guardz changed your day-to-day operations and peace of mind?
Guardz has significantly streamlined our operations and provided unparalleled peace of mind. Instead of spending hours filtering through false alarms, I now start my day with a clear list of actual threats. Recently, we connected one of our new clients to Guardz, and it helped us scan their cloud presence, discovering over 800 files shared publicly, some containing sensitive corporate data. With Guardz’s help, we closed a major data leak before it caused any harm. This reliable protection allows me to focus on strategic initiatives like developing a new cloud migration service that has already attracted several new clients. The efficiency and security Guardz offers are truly invaluable.Can you recall a moment when Guardz really proved its worth to you?
Absolutely, I can recall a moment when Guardz truly proved its worth. We faced a highly sophisticated malware attack that slipped past our previous security measures. Guardz detected it almost instantly, neutralizing the threat before it could do any damage. This incident reaffirmed our decision to partner with Guardz and highlighted the critical role it plays in safeguarding our clients’ data. It was a clear demonstration of Guardz’s advanced capabilities and our commitment to maintaining top-tier cybersecurity.How has Guardz impacted your client relationships?
Guardz has significantly enhanced our client relationships by making our proactive efforts more transparent. Its detailed reports clearly show the threats we neutralize, helping clients appreciate the value of our work. For instance, last quarter, we used Guardz’s visual ROI report to present a cyber risk assessment to our manufacturing client. The clear data helped them identify security gaps, leading to a substantial budget increase for additional protective measures. These reports are now crucial for showcasing our value and building stronger, more trusting relationships with our clients.How has Guardz helped you scale your business?
We’ve grown our client base by 20% since implementing Guardz, and we’ve done it without adding to our team.What would you tell other MSPs about Guardz?
To fellow MSPs, I can confidently say that Guardz has revolutionized our cybersecurity offerings. Its AI-driven threat detection is impressively accurate, catching issues that previously went unnoticed. The 24/7 monitoring feels like having an elite security team on duty around the clock. What sets Guardz apart is their exceptional support team, working with us as true partners. Since implementing Guardz, our threat response has become faster and more precise, driving our business growth and keeping us ahead of the competition. If you want to elevate your cybersecurity services, I highly recommend Guardz. It has transformed our business.How do you see your partnership with Guardz evolving in the future?
I envision our partnership with Guardz as a long-term collaboration. Their innovative approach aligns perfectly with our goals, and I’m excited about the potential to grow together. I’m confident that Guardz will continue to push the boundaries of cybersecurity, helping us stay ahead in an ever-evolving landscape.About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About Guardz
Guardz is on a mission to create a safer digital world by empowering Managed Service Providers (MSPs). Their goal is to proactively secure and insure Small and Medium Enterprises (SMEs) against ever-evolving threats while simultaneously creating new revenue streams, all on one unified platform.









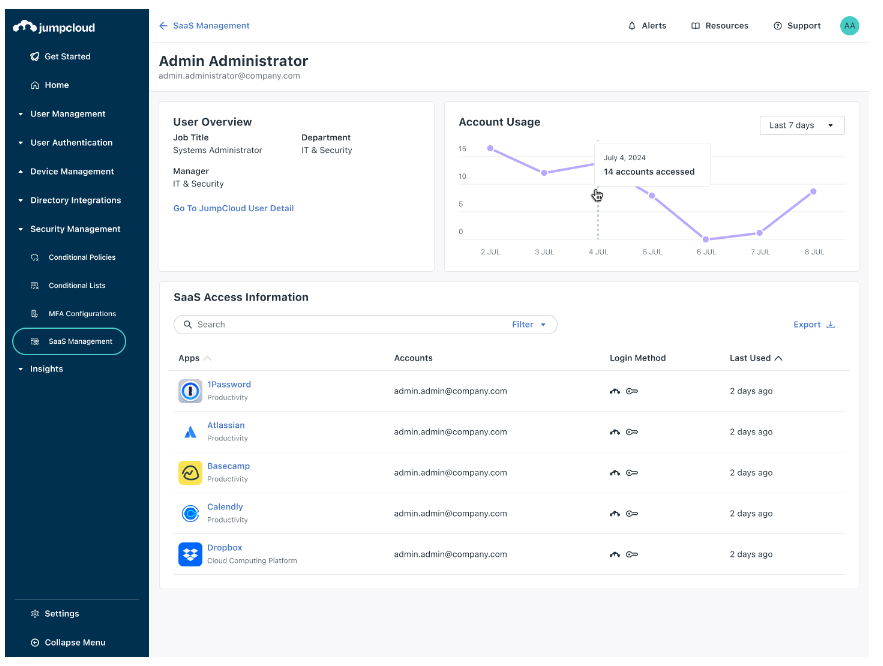
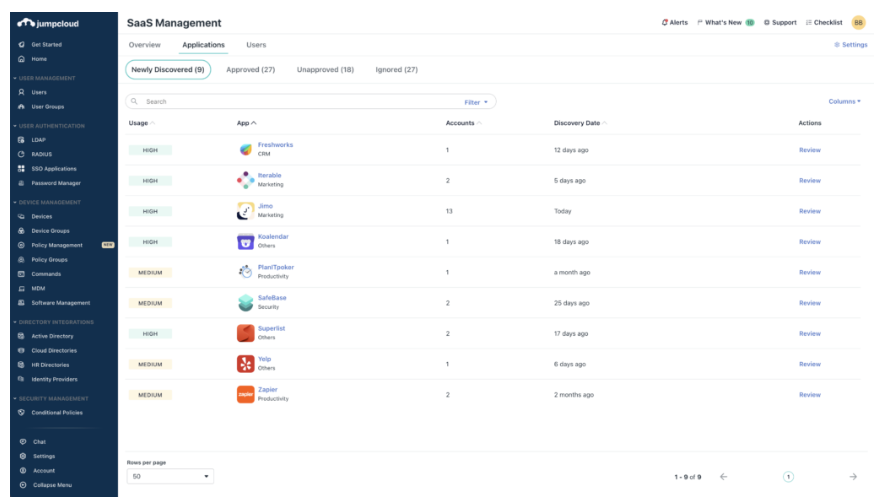 這款新工具能幫助 IT 管理員發現所有受管理設備上使用的 SaaS 應用程式,讓您清楚知道哪些應用被使用,以及使用者是誰。JumpCloud 的 SaaS 管理工具有助於控制 SaaS 增長,防止「影子 IT」,擴大單一登錄(SSO)的覆蓋,降低 SaaS 成本,確保公司企業內部的 SaaS 使用安全、合規並經過優化。
這款新工具能幫助 IT 管理員發現所有受管理設備上使用的 SaaS 應用程式,讓您清楚知道哪些應用被使用,以及使用者是誰。JumpCloud 的 SaaS 管理工具有助於控制 SaaS 增長,防止「影子 IT」,擴大單一登錄(SSO)的覆蓋,降低 SaaS 成本,確保公司企業內部的 SaaS 使用安全、合規並經過優化。 JumpCloud 的 SaaS 管理解決方案使 IT 團隊能夠有效保護和管理公司企業內的 SaaS 應用程式。公司企業可以利用 JumpCloud 簡化 SaaS 應用的發現,防止「影子 IT」,擴展 SSO 覆蓋範圍,並在一個綜合平台上實現合規要求。
JumpCloud 的 SaaS 管理解決方案使 IT 團隊能夠有效保護和管理公司企業內的 SaaS 應用程式。公司企業可以利用 JumpCloud 簡化 SaaS 應用的發現,防止「影子 IT」,擴展 SSO 覆蓋範圍,並在一個綜合平台上實現合規要求。