Advanced tasks: user experience monitoring
In the last century we had very primitive computers and now, at the dawn of a new millennium are we the users who have become primitive !? Want to learn more? Let’s get to know User Experience Monitoring
My first computer, in 1987, was a laptop with a monochrome LCD screen and 16 kilobytes of program memory. They were 15,584 precious bytes and they were read and executed very quickly. When I started to study engineering, it was the turn for that noble artifact to perform approximate integrals and, bam! This is where user experience comes in, when the professor asked me to compare his final result with that of the computer.
Sometimes, depending on the complexity of the formula and the iterations requested, the teacher would finish before the computer. That is why I had to choose those parameters well before starting the calculation, just based on estimation. A decade later, GNU/Linux already existed, the Internet boom began (which has not stopped to this day) and we began to connect by applications that allow us to have a terminal window and thus leave workload calculation to servers dedicated to it.
The experienced user
What we were clear about was that computing power was needed. Decades had gone by where it was delegated to remote terminals and/or dumb terminals and the entire workload was done on a “supercomputer.” Sir Tim Berners-Lee created, de facto, HTML and web pages were like static board ads, changing from time to time. Something called Common Gateway Interface (CGI) was invented to allow them some dynamism. This is how we began to worry about the time it took to solve calculations and results and then present them in a web page template.
Databases evolved: I used MS Access® for small applications and for everything else dBase® and Clipper®. Then Visual Fox Pro® came, with which I was able to handle tens of millions of records on a personal computer.
It was inevitable that databases would pass by without impacting our lives. Later, in this century, PHP language was responsible not only for creating web pages, their HTML code, but we could also custom generate, in several versions, according to different parameters, connecting directly to databases and retrieving data for users in real time.
Brief retrospective
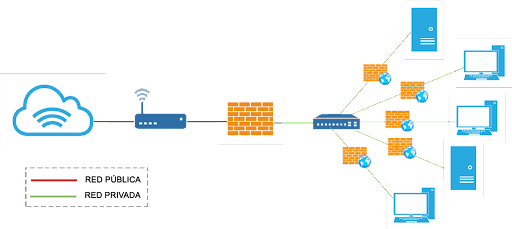
By the beginning of this century, Pandora FMS was born (in 2004, to be precise) and the checking and loading time of a web page, its HTML component, is part of what I consider primitive monitoring. It even has some advanced components, such as text search on the web page or simple login, like the POST type, to take the time it takes to return a result, among other Modules.For Pandora FMS, each measure is called a Module, which are grouped by Agents.
Meanwhile, desktop applications, now known as on premise, were also evolving. In said applications, all their binary code relies on the device where they are executed, and the data is either obtained from a local file or is connected to a database to obtain and edit information, more useful and widely used. They are also known as native applications of each operating system in particular.
Pandora FMS can do remote database checks and we can add operations that a user would generally do. For example, ask for the last seven days of sales, -if the database is online- how long it takes to return this result: if it takes X amount of seconds or more, return a warning on the screen or an alert by mail, SMS, and so on. This gives you a rough idea of the state and operation of a system, but it is not yet user experience monitoring.
Complex applications
As the computing power in servers has always been higher than in our homes or offices, the ingenuity of application programming interface, better known as API, was realized. An API is a set of functions, procedures, and subroutines that provides a “library” to be used by other software. Pandora FMS and many applications have this way of allowing third parties to develop their own interfaces to perform predefined tasks: create a new article in the database? Publish a price list? These tasks are candidates to be performed through an API.
But we are approaching user experience monitoring: if the application created by a third party goes slowly, where is the bottleneck?, in the application?, on the server?, in the communication of the server? Are there other causes for this delay?
Another detail to take into account is our human factor: I have personally had to be told that an application I have made “is going slow”. I took the source code, I changed the background color of the forms, I compiled, installed and received a variety of different responses: what got better, what got worse, etc. That is what is called qualitative reporting, but without figures or facts to support it.
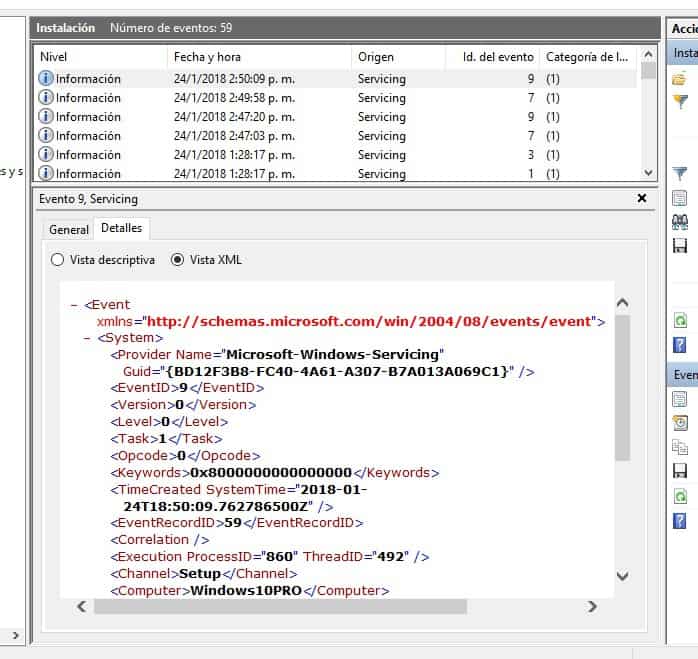
Pandora FMS has real cases of experience monitoring where they reported quantitatively how and when process delays were detected. Thus we are already reaching the present, the applications that we use the most at the time of writing these lines.
Web applications
You can see how the Internet has changed the way we work to reach something that is practically ubiquitous today: web applications. Through a web browser, users are identified and everything is done online, whether the web application connects directly or, through API, to one or more databases.
They have the advantage of being able to quickly change forms for users, but it opens up other problems such as workload sharing between multiple servers and redundancy in data storage. For all this, Pandora FMS has excellent tools, and we can even add our own, that’s how flexible it is!
Said web applications can also be delegated to third parties, and if this is the case, Pandora FMS can monitor the service level agreements (Service Level Agreement or SLA): these scenarios are really complex and they may even need to include user experience monitoring.
Primitive Users
Thus, we have reached the great concern of our times: Is our computer powerful enough to run our favorite web browser? Because, actually, the vast majority only run a web browser and there they read their email, communicate through social networks, carry out their remote work during the pandemic, access their bank accounts, publish on their blog, keep spreadsheets online for different subjects…There are even dozens of tabs open, each one consuming processor and memory cycles by the web browser.
We have become rudimentary and elementary, even our web browser updates automatically. We can acquire a new computer and in a short time have everything working again as we had it since it is completely based on the web browser. I even have Mozilla Firefox and Google Chrome accounts that sync with my other devices like mobile phones and e-book readers: they offer this service to keep everything centralized.
With Pandora FMS and its Software Agent (small application installed in each device and that monitors locally) we can quickly know if these web browsers represent a very large workload for the device, as well as inventory of the software and hardware from all of them.
Have we been monitoring enough with this brief retrospective that I told you? This is where user experience monitoring comes in.
Experience monitoring
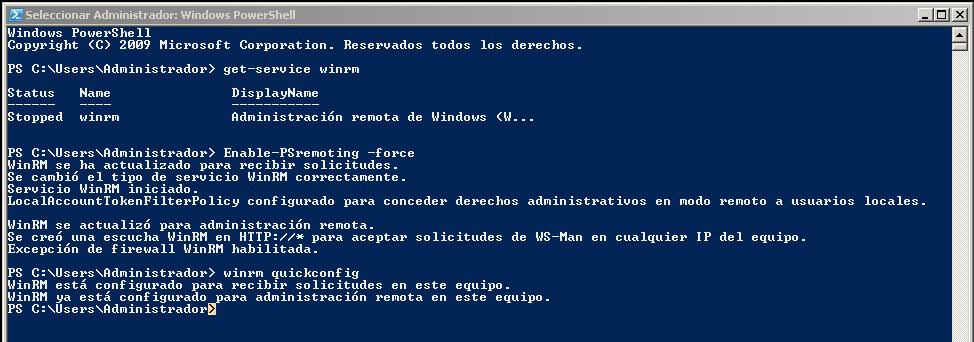
User experience monitoring is like simulating being a user who executes predefined monitoring tasks and whose results are carefully measured, saved and sent to the corresponding Pandora FMS server.
It was invented for all this that I explained you, both web applications and desktop applications.
To be honest, I’m not the first to write on this blog about user experience monitoring:
For web applications, Pandora Web Robot (PWR).
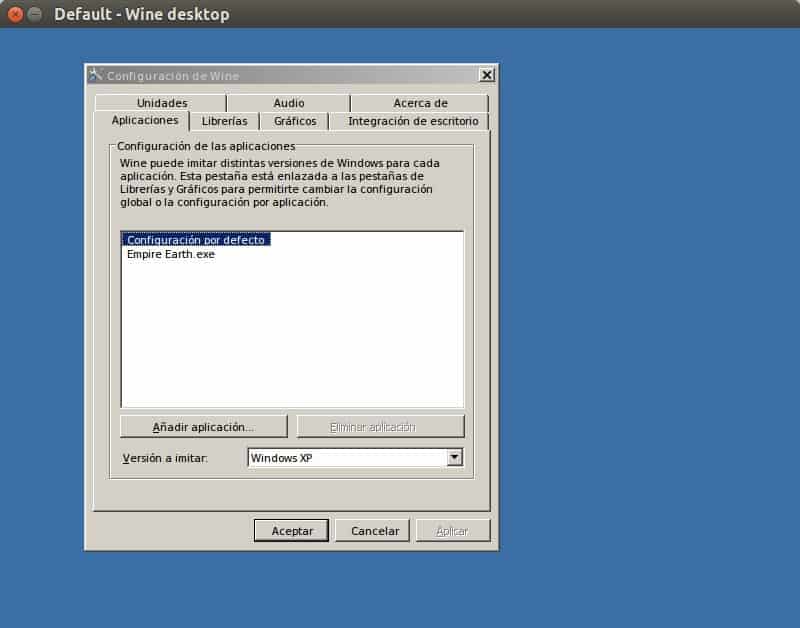
For desktop applications on MS Windows®: Pandora Desktop Robot (PDR).
Essentially, and in both cases, it is about moving and clicking with the mouse and/or pressing the keyboard for each of the application options to be monitored. If you want to know the details in depth, you should undoubtedly click on each of these two articles after finishing your reading here, since there is not much left to finish off.
Progressive web applications
Of course the world is constantly changing. Now web browsers, through the support of each operating system, offer progressive web applications that blur the boundaries between web applications and desktop applications.
They base their technology on HTML, CSS and JavaScript (which works as PHP but on the client side), which is no surprise to us who are used to web applications. The difference is that it uses background processes that are responsible for intercepting our requests to the domain where the web system server resides, but go further using the cache of the web browser. They do not need installation as we know it (if the user consents to its use) and can even make use of their own local databases such as SQLite, for example.
Here monitoring is somewhat complicated, since these progressive applications are capable of working offline with previously saved data: it will be a matter of programming requests with content of random values to avoid this behavior. We can also refine and target our Software Agents to refine our monitoring task. But all of that is enough material for another article.
Before finishing, remember Pandora FMS is a flexible monitoring software, capable of monitoring devices, infrastructures, applications, services and business processes.
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About PandoraFMS
Pandora FMS is a flexible monitoring system, capable of monitoring devices, infrastructures, applications, services and business processes.
Of course, one of the things that Pandora FMS can control is the hard disks of your computers.