
Default configuration should be what you’re using for a while, at least before familiarizing yourself a bit more intimately with the Tor documentation. However, aside from the GUI-based set up of the browser, I want to try and explain how you would set your Tor browser through the Torrc config file.
I will assume you’re more than familiar with Tor, or have gone through the docs, and that you know what’s the purpose of the Torrc file.
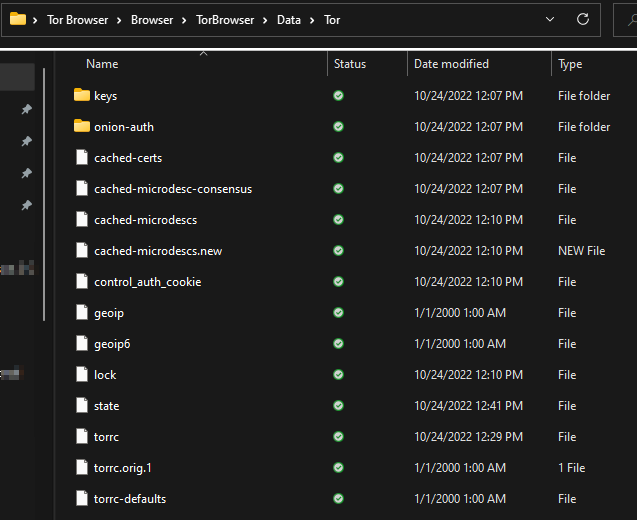
You can find your torrc file in the \Tor Browser\Browser\TorBrowser\Data\Tor path, where Tor Browser is the Tor’s installation folder.
It would look something like this (on a Windows-based machine)
On your Mac, you need to go to the Application and right-click on the Tor browser app icon, selecting the show package contents and navigate to TorBrowser/Data/Tor/Torrc.
On Linux, the file will be in the TorBrowser/Data/Tor path and Tor will also put it into /usr/local/etc/tor/torrc if compiled from source, or in the etc/tor/torrc or etc/torrc if installed as a package.
Check out the manual at this link. You will see a detailed list of options used in the torrc file. You can also do man tor, you can also check out the sample torrc file. This is good to check out since it has a lot of comments.
One of the main things people tend to change are the entry and/or exit nodes – thus changing the geographical location of the said nodes and is a good simple example for us here.
Check ExcludeNodes node,node,…
And you will notice that country codes are 2-letter ISO3166 codes and that they must be enclosed by braces. So, something like {fr} is a valid country code and would set your entry/exit node to France. Note that the country codes are not case-sensitive. And also keep in mind that {??} exists for nodes whose country can’t be identified. More about that can be found at the Tor manual link above.
I’ve now added entry/exit nodes to the torrc file:

As shown in the image above, I want to start the Tor circuit in France, and I want to exit in Great Britain.
I searched for Google.com…

And, as you can see, the change made to the torrc file has been applied. If I click on new circuit for this site:

You will note that the entry and exit nodes stayed on the same countries that were previously specified in the torrc file.
You can also specify actual relays that you want to use. Go to https://metrics.torproject.org/ and and do a relay search (bottom of the page) for a relay of your choosing. (I chose top relays options just to quickly demonstrate how you would add a relay to the torrc file)
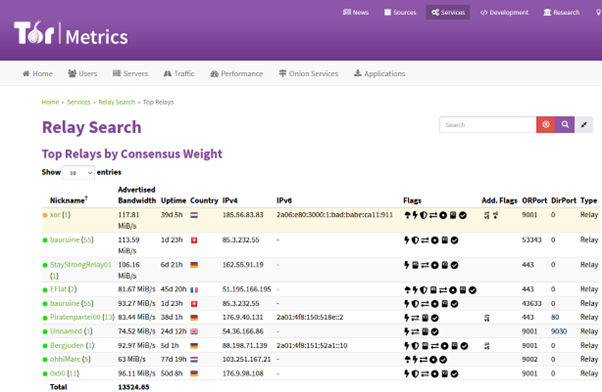
Another important thing are the flags, they will usually tell you what’s the best use of a given relay. If its fast, suitable for entry/exit, if it is validated, and more.
If I were to pick the first relay (xor) I would copy paste the fingerprint into my torrc file


All of this depends on your risks, rather who is your adversary. For example, if they are outside those relays (and you know that) then the relay might help you stay hidden, but nothing is given. If they control the relays… well, then they might be onto you and it’s time to adapt your tactics.
One more thing, unless you’re a seasoned veteran, maybe refrain from manually changing the circuits because this can make you stand out in theory so maybe don’t do that unless you’re sure.
To apply the configuration from the newly-changed torrc file, restart the browser. You can also do pkill -sighup tor on Linux, but it might even be easier (and better) to just restart the browser.
Conclusion
Okay, this was a very short intro to the torrc but I hope you liked it and that you will find the links I shared useful! The saga continues, as I will be publishing another Tor piece shortly…
Stay tuned!
Cover image by Sandeep Swarnkar
#tor_browser #torrc
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About VRX
VRX is a consolidated vulnerability management platform that protects assets in real time. Its rich, integrated features efficiently pinpoint and remediate the largest risks to your cyber infrastructure. Resolve the most pressing threats with efficient automation features and precise contextual analysis.




