2022, the world is the technological paradise you always dreamed of. Space mining, smart cities, 3D printers to make your own Darth Vader mask… Just a little problem, society is based on digitization and communications and you have no idea about the visibility of distributed networks. Something of vital importance considering the rise of cybercrime. Well, don’t worry, we’ll help you.
Do you know everything about distributed network visibility?
Well, the first thing you need to be aware of is the importance of this distributed network visibility. After all, companies around the globe say that the biggest blind spots in their security come from the network, so all their efforts are focused on safeguarding their data by reinforcing this trench. That’s why visibility is key. Even more so if we talk about Managed Service Providers (MSP), the professionals in charge of protecting customer data.
But, what is distributed network visibility?
To put it simply, distributed network visibility supposes having full knowledge of the different components running within your network to be able to analyze, at will, aspects such as traffic, performance, applications, managed resources and many more, which will depend on the capabilities offered by your monitoring tool. In addition to increasing visibility into your customers’ networks, a comprehensive solution can give you more leverage to strategize based on the metrics you’re monitoring.
For example, MSPs can, with a good visibility solution, help improve the security of their customers by revealing signs of network danger or, through better analytics, make more informed and rigorous decisions about data protection.
As we have warned before, cybercrime is our daily bread in this almost science fiction future that we have earned, and blind spots in network security, along with what will become of the cd, is one of our great concerns.
Monitor traffic, look for performance bottlenecks, provide visibility thanks to a good monitoring tool and alert on irregular performance… That’s what we need. In addition, these super important alerts draw attention and notify technicians and system administrators, who will immediately take the appropriate measures to solve our problem.
If you are an MSP in this post-apocalyptic future that we are living in, it is very likely that you use several applications as part of your services, well, another of the obvious advantages of improved visibility is the ability to participate in application supervision. So, for example, when granular network visibility is set, you may get unquestionable insight into how applications are affecting performance and connectivity. Once you are aware of this, you may choose to filter critical app traffic to the right tools and monitor who is using which app and when. You may even make application performance more practical, reducing processor and bandwidth work by ensuring, for example, that email traffic is not sent to non-email gateways.
Some challenges to consider
Not everything is having fun and joking around, rolling on the carpet and having crises saved by your expertise, there are several challenges for MSPs associated with network visibility.
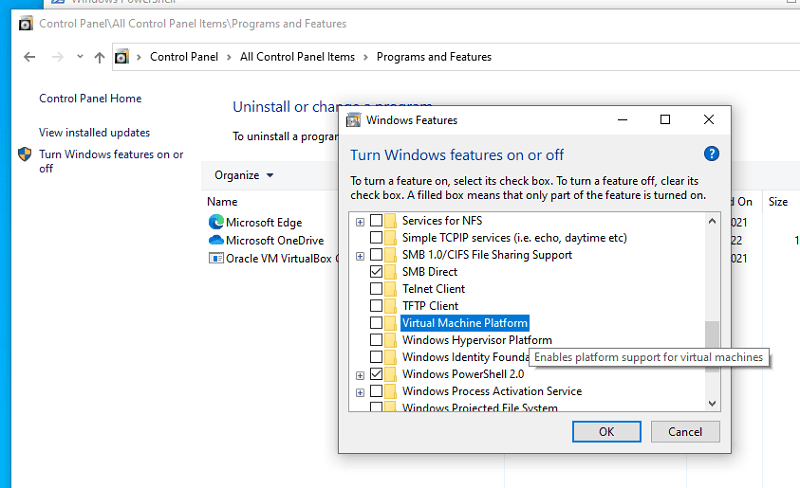
Cloud computing has increased and mobile traffic has increased too, this only adds, to our inconvenience capacity, more blind spots to watch out for as MSP. The end has come for the magnanimous and bucolic days of lying on the grass simply monitoring traffic over MPLS links. We are in the future, and WANs are a deadlock for Internet-based VPNs, Cloud services, MPLS, and mobile users. Something complex that many rudimentary monitoring tools cannot offer full visibility of. There are many components to address. To deal with this Gordian knot and its dense complexity, MSPs must be demanding and rigorous when choosing a monitoring tool to work with.
Another of the great challenges that MSPs may face in this field is the fact that the most traditional monitoring methods are closely linked to on-premise devices. This means that all WAN locations need their own set of applications, and these must have their own sources and be properly maintained. Optionally, all traffic can be retrieved and inspected from a WAN location. This inefficient method can have a performance impact.
Due to this inefficiency, it becomes difficult to apply the traditional approach to distributed network visibility. For enterprises with many applications, networking becomes too obtuse and convoluted, with a variety of individual configurations and policies difficult to support. Additionally, there is the capacity restrictions of the devices, which limit the amount of traffic that can be analyzed without the need to update the hardware. This without noticing that at some point the devices will have to be completely patched or replaced. Damn, even if your company grows, which is what we want, network visibility will quickly be constrained and more security vulnerabilities will go unnoticed.
Conclusions and good wishes
I gave you a very bad prospect. But don’t worry, it was only an adverse in crescendo until reaching the great catharsis: While there are many traditional monitoring tools that cannot address distributed network visibility challenges, there are, thank heavens, other monitoring tools that can. This is the example of Pandora FMS, a monitoring software that is up to the challenges such as those raised and that helps technicians manage complex networks and much more. Pandora FMS allows you to control, manage and customize the tool through a centralized interface. Thanks to its scalability you will be able to manage networks with hundreds of devices and give IT providers what they need to increase security and maximize efficiency. You don’t believe it? Try it now for 30 days for free. You see, not everything was going to be bad in this post apocalyptic future!
About Version 2 Digital
Version 2 Digital is one of the most dynamic IT companies in Asia. The company distributes a wide range of IT products across various areas including cyber security, cloud, data protection, end points, infrastructures, system monitoring, storage, networking, business productivity and communication products.
Through an extensive network of channels, point of sales, resellers, and partnership companies, Version 2 offers quality products and services which are highly acclaimed in the market. Its customers cover a wide spectrum which include Global 1000 enterprises, regional listed companies, different vertical industries, public utilities, Government, a vast number of successful SMEs, and consumers in various Asian cities.
About PandoraFMS
Pandora FMS is a flexible monitoring system, capable of monitoring devices, infrastructures, applications, services and business processes.
Of course, one of the things that Pandora FMS can control is the hard disks of your computers.